Professional Documents
Culture Documents
Distinguish CISC and RISC.: Client Server Architecture BT0052
Uploaded by
dharmendraalone93Original Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Distinguish CISC and RISC.: Client Server Architecture BT0052
Uploaded by
dharmendraalone93Copyright:
Available Formats
Client Server Architecture BT0052
SET-1
1. Distinguish CISC and RISC.
Ans: CISC
Pronounced sisk, and stands for Complex Instruction Set Computer. Most PC's use
CPU based on this architecture. For instance Intel and AMD CPU's are based on
CISC architectures.
Typically CISC chips have a large amount of different and complex instructions. The
philosophy behind it is that hardware is always faster than software, therefore one
should make a powerful instruction set, which provides programmers with assembly
instructions to do a lot with short programs.
In common CISC chips are relatively slow (compared to RISC chips) per instruction,
but use little (less than RISC) instructions.
RISC
Pronounced risk, and stands for Reduced Instruction Set Computer. RISC chips
evolved around the mid-1980 as a reaction at CISC chips. The philosophy behind it
is that almost no one uses complex assembly language instructions as used by
CISC, and people mostly use compilers which never use complex instructions. Apple
for instance uses RISC chips.
Therefore fewer, simpler and faster instructions would be better, than the large,
complex and slower CISC instructions. However, more instructions are needed to
accomplish a task.
An other advantage of RISC is that - in theory - because of the more simple
instructions, RISC chips require fewer transistors, which makes them easier to
design and cheaper to produce.
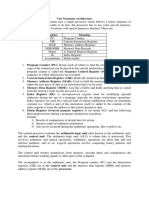
CISC RISC
stands for Complex Instruction Set stands for Reduced Instruction Set
Compute Computer
In CISC, software developers no need to RISC puts a greater burden on the
write more lines for the same tasks software. Software developers need to
write more lines for the same tasks
CISC processors cannot have a large Large number of registers, most of which
number of registers. can be used as general purpose
registers
CISC processor executes microcode RISC processor has a number of
instructions hardwired instructions.
2. Write a short note on Asynchronous Transfer Mode of transmission..
Cybotech Campus Page 1
Client Server Architecture BT0052
Ans: ATM is cell and multiplexing technology that combines the
benefits of dedicated circuits (invariant transmission delay and
guaranteed capacity) with those of packet switching (flexibility and
efficiency for intermittent traffic). The fixed length of ATM’s cells(53
bytes—48 bytes for the “payload” and 5 bytes for headers)facilitates
high speed implementation that can support isochronous (time critical)
application such as video and telephony with constant flow rates, in
addition to more conventional data communications between
computers where fluctuation in packet arrival rates typically not
problematic (7). ATM standards define a board range of bandwidths –
from 1.5 mbps (via t1 or DS1) to 622 mbps (OC -12) and above – but
most commercially available ATM products currently provide 155.52
mbps (OC—3 ) or 100 mbps (TAXI). ATM is currently implemented over
fiber connections to and various twisted pair wiring alternatives.
All devices in an ATM network attach directly to an
ATM switch. Multiple ATM switches can be combined in a fabric
sometimes called an “ATM cloud” and virtual circuits can be
dynamically created between any two nodes on one or more ATM
switches so long as the switch can handle the aggregate cell transfer
rate, additional connections to the switch can be made.
3. Explain various client/server applications using Java.
Ans:
4. How will you develop a simple web client in Java using Sockets?
Ans: import java.io.*;
Import java.net.*;
Public class webc
{
try
{
Socket cSock1=new Socket (“cecasum.utc.edu”, 80);
System.out.println(“Client1: “ + csock1);
getPage(csock1);
}
Catch (UnknownHostException e)
{
System.out.println(“UnknownHostException : “ + e);
}
Catch (IOException e)
{
System.err.println(“IOException: “ + e);
}
}
Public static void getPage(Socket csock)
{
Cybotech Campus Page 2
Client Server Architecture BT0052
try
{
DataOutputStream outbound=new
DataOutputStream(cSock.getOutputStream());
DataInputStream inbound=new DataInputStream(cSock.getInputStream());
Outbound.writeBytes(“Get /~cslab/cpsc591/test.htmHTTP/1.0\r\n\r\n”);
String responseLine;
while((responseLine=inbound.readLine()) !=null)
{
System.out.println(responseLine);
If(responseLine.indexOf(“</HTML>”) !=-1)
Break;
}
outbound.close();
inbound.close();
cSock.close();
}
Catch(IOException ioe)
{
System.out.println(“IOException: “ + ioe);
}
}
}
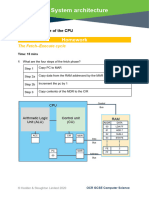
5. Explain TCP/IP Protocol in detail.
Ans: TCP, an acronym for Transmission Control Protocol, corresponds to the fourth
layer of OSI reference model. IP corresponds to the third layer of the same model.
Each of these protocols has the following features:
TCP: It provides a connection type services. That is a logical connection must be
established prior to communication. Because of this, continuous transmission of
large amount of data is possible. It ensures a highly reliable data transmission for
upper layer using IP protocol. This is possible because TCP uses positive
acknowledgement to confirm the sender about the proper reception of data.
Data Segment 1
Time
Acknowledgment 1
Data Segment 2
Acknowledgement 2
Cybotech Campus Page 3
Client Server Architecture BT0052
A B
TCP establishes virtual circuits
A negative acknowledgement implies that the failed data segment needs to be
retransmitted.
The TCP header includes both source and destination port fields for identifying the
applications for which the connection is established. The sequence and
acknowledgement Number fields underlie the positive acknowledgement and
retransmission techniques. Integrity checks are accommodated using the checksum
field.
Source Port Destination
Port
Sequence Number
Acknowledgement Number
Header
Length Preserved Code Bits
Window
Checksum Urgent
Pointer
Option (if any)
Padding
The data segment format of the TCP protocol
IP: It is connectionless type service and operates at third layer of OSI reference
model. That is, prior to transmission of data. No logical connection is needed. This
type of protocol is suitable for the sporadic transmission of data to a number of
destinations. This has no functions like sequence control, error recovery and control,
flow control but this identifies, the connection with the port number.
6. Explain Remote Procedure Call in detail.
Ans: Remote Procedure Call (RPC) is a client/server infrastructure that increases the
interoperability, portability, and flexibility of an application by allowing the application
to be distributed over multiple heterogeneous platforms. It reduces the complexity of
Cybotech Campus Page 4
Client Server Architecture BT0052
developing application that span multiple operating systems and network protocols
by insulating the application developer from the details of the various operating
system and network interfaces-function calls are the programmer’s interface when
using RPC.
To access the remote server portion of an application, special function calls, RPCs,
are embedded, within the client portion of the client/server application program.
Because they are embedded, RPC do not stand alone as a discreet middleware
layer.
RPC increases the flexibility of an architecture by allowing a client component of an
application to employ a function call to access a server on remote system. RPC
allows the remote component to be accessed without knowledge of the network
address or any other lower-level information. Most RPCs use a synchronous,
request-reply (sometimes referred to as “call/wait”) protocol which involves blocking
of the client until the server fulfils its request. Asynchronous (“call/wait”)
implementations are available but are currently the exception.
In two ways RPC can be implemented:
1. Within a broader, more encompassing propriety product
2. By a programmer using a proprietary tool to create client/server RPC stubs.
RPC is appropriate for client/server applications in which the client can issue a
request and wait for the server’s response before continuing its own processing.
Because most RPC implementations do not support peer-to-peer, or asynchronous,
client/server interaction, RPC is not well-suited for applications involving distributed
objects or object-oriented programming.
Asynchronous and synchronous mechanisms each have strength and weaknesses
that should be considered when designing any specific application. In contrast to
asynchronous mechanisms employed by Message-Oriented Middleware, the use of
a synchronous request-reply mechanism in RPC requires that the client and server
are always available and functioning. In order to allow a client/server application to
recover from a blocked condition, an implementation of a RPC is required to provide
mechanisms such as error, messages, request timer, retransmission, or redirection
to an alternate server. The complexity of the application using a RPC is dependent
on the sophistication of the specific RPC implementation. RPCs that implement
asynchronous mechanisms are very few and are difficult to implement.
Cybotech Campus Page 5
Client Server Architecture BT0052
Cybotech Campus Page 6
You might also like
- Socket ProgrammingDocument16 pagesSocket ProgrammingVivek kumarNo ratings yet
- Cs P52 Computer Networks Laboratory Manual (JUNE 2018-NOVEMBER 2018) V SemesterDocument11 pagesCs P52 Computer Networks Laboratory Manual (JUNE 2018-NOVEMBER 2018) V SemesterAnonymous oyWoNqVNo ratings yet
- CN Lab ManualDocument131 pagesCN Lab ManualDHARSHINI SNo ratings yet
- CS 50 Software Design and Implementation Socket Programming: GoalsDocument20 pagesCS 50 Software Design and Implementation Socket Programming: GoalsUtsav DubeyNo ratings yet
- Internet Technology and Web Design: Chapter: 2.3 Internet Protocols Topic: 2.3.1 Introduction To Internet ProtocolsDocument15 pagesInternet Technology and Web Design: Chapter: 2.3 Internet Protocols Topic: 2.3.1 Introduction To Internet ProtocolsETL LABSNo ratings yet
- acknowledgments, Sequencing, and Flow Control Are Characteristics of Which OSI Layer?Document9 pagesacknowledgments, Sequencing, and Flow Control Are Characteristics of Which OSI Layer?Desmond KcNo ratings yet
- Pptonsixmonthtraining 180427093146Document24 pagesPptonsixmonthtraining 180427093146Diwakar DiwakarNo ratings yet
- Final PPT of CCSDS TC SystemDocument38 pagesFinal PPT of CCSDS TC SystemNavakanth Bydeti0% (1)
- Implementing intent-based networking in a campus infrastructureDocument44 pagesImplementing intent-based networking in a campus infrastructureKelvin FlorianNo ratings yet
- Advanced Computer Networks - CoSc-6111-Lecture-4Document80 pagesAdvanced Computer Networks - CoSc-6111-Lecture-4AhmedNo ratings yet
- VST Case StudyDocument9 pagesVST Case StudyBobby NelsonNo ratings yet
- Mossinger 2016Document6 pagesMossinger 2016M VijayalakshmiNo ratings yet
- Practice FinalDocument17 pagesPractice Finalawan kNo ratings yet
- UNIT-4: Computer NetworkDocument12 pagesUNIT-4: Computer NetworkPranav KumarNo ratings yet
- Multi-Threaded Client Server Final Project Project Report Operating System (Cse2005)Document16 pagesMulti-Threaded Client Server Final Project Project Report Operating System (Cse2005)pavan saiNo ratings yet
- Multithreading ProjectDocument16 pagesMultithreading ProjectSATYA AAKASHNo ratings yet
- Study of Socket Programming and Client SDocument4 pagesStudy of Socket Programming and Client Snkprannesh12No ratings yet
- 1.1. Background: Datagram CommunicationDocument8 pages1.1. Background: Datagram CommunicationPrithwish GhoshNo ratings yet
- Hct6000 Tcpip OptionDocument14 pagesHct6000 Tcpip OptionGerman DfrNo ratings yet
- Sysnet Notes: Basic CCNA Interview Questions AND AnswersDocument8 pagesSysnet Notes: Basic CCNA Interview Questions AND AnswersReddy SumanthNo ratings yet
- Communication in Distributed Systems: REK's Adaptation of Tanenbaum's Distributed SystemsDocument24 pagesCommunication in Distributed Systems: REK's Adaptation of Tanenbaum's Distributed SystemsDeepika DasNo ratings yet
- CN Lab Manuals 2019 (1) - Converted-1Document114 pagesCN Lab Manuals 2019 (1) - Converted-142 Subulakshmi V.No ratings yet
- Intro - Slides Systemc SCVDocument28 pagesIntro - Slides Systemc SCVShaikAzharNo ratings yet
- Computer Networks (CS425) : Unix Socket ProgrammingDocument4 pagesComputer Networks (CS425) : Unix Socket ProgrammingAnish VeettiyankalNo ratings yet
- Port Scanner: Guided By: Group MembersDocument17 pagesPort Scanner: Guided By: Group MembersAnshuman SinghNo ratings yet
- TCP Socket Programming GuideDocument24 pagesTCP Socket Programming GuideAbhishekNo ratings yet
- Feb2009 SolvedDocument4 pagesFeb2009 Solvedhj43usNo ratings yet
- NP Lab ManualDocument81 pagesNP Lab ManualRooparam ChoudharyNo ratings yet
- Data Communications and Networking 4 Midterms To FinalsDocument7 pagesData Communications and Networking 4 Midterms To FinalsCanatoy, Christian G.No ratings yet
- Transport Layer - ADocument17 pagesTransport Layer - ADinesh LalwaniNo ratings yet
- HP Course Structure 80 HoursDocument3 pagesHP Course Structure 80 Hourssumitsahu009No ratings yet
- Question Bank Advanced Computer Networks: Q.1 What Do You Mean by Subnet Masking?Document6 pagesQuestion Bank Advanced Computer Networks: Q.1 What Do You Mean by Subnet Masking?Abhishek JainNo ratings yet
- 2 MarksDocument11 pages2 MarksSid VibhorNo ratings yet
- Notes On Computer Networks Unit4Document12 pagesNotes On Computer Networks Unit4Rohit Chaudhary67% (3)
- TCP/IP Concepts and Internet ProtocolsDocument71 pagesTCP/IP Concepts and Internet ProtocolsHans MortenNo ratings yet
- EE353 Lab 4: Network Programming Using PythonDocument19 pagesEE353 Lab 4: Network Programming Using PythonBama DamaNo ratings yet
- CCNA 1 v5.0 R&S ITN Final Exam Answers 2014Document22 pagesCCNA 1 v5.0 R&S ITN Final Exam Answers 2014jonmicNo ratings yet
- Fault-Resilient Pcie Bus With Real-Time Error Detection and CorrectionDocument7 pagesFault-Resilient Pcie Bus With Real-Time Error Detection and CorrectionMohamed AlahmadyNo ratings yet
- Department of Computer Science and Engineering: PREPARED BY: Mr. D. Ramkumar - A.P-CSEDocument38 pagesDepartment of Computer Science and Engineering: PREPARED BY: Mr. D. Ramkumar - A.P-CSEanish.t.pNo ratings yet
- CCNA 1 v60 Study Material Chapter 9 Transport LayerDocument9 pagesCCNA 1 v60 Study Material Chapter 9 Transport LayerRazaqNo ratings yet
- Cisco AssignmentDocument22 pagesCisco AssignmentJiawei TanNo ratings yet
- Lab 11.2.4 Protocol Inspector, TCP and HTTPDocument3 pagesLab 11.2.4 Protocol Inspector, TCP and HTTPamna mukhtarNo ratings yet
- ACL Solution for Finance Web Server AccessDocument14 pagesACL Solution for Finance Web Server AccessRami SweilehNo ratings yet
- CCNA 1+2+3+4 v5Document87 pagesCCNA 1+2+3+4 v5Ajmal QalaNo ratings yet
- Presentation On TCP-IP VulnerabilitiesDocument34 pagesPresentation On TCP-IP Vulnerabilitiesmohit_kohli6739100% (1)
- Assignment - 3Document8 pagesAssignment - 3Shivam SharmaNo ratings yet
- 4 - Local Area NetworkDocument28 pages4 - Local Area NetworkD'Bagas SaputraNo ratings yet
- CCNA 1 Final Exam AnswersDocument80 pagesCCNA 1 Final Exam AnswersTatenda BizureNo ratings yet
- Cisco Real-Exams 300-101 v2019-03-23 by Barbra 469qDocument243 pagesCisco Real-Exams 300-101 v2019-03-23 by Barbra 469qJorge ArmasNo ratings yet
- Abbreviations Advanced RCS 1Document8 pagesAbbreviations Advanced RCS 1seba paezNo ratings yet
- 8cs5a Unps Lab Manual 1Document64 pages8cs5a Unps Lab Manual 1Rooparam ChoudharyNo ratings yet
- CN Lab Manual 2018Document121 pagesCN Lab Manual 2018Suresh RamanujamNo ratings yet
- Abstract On Socket ProgrammingDocument33 pagesAbstract On Socket Programmingyogesh_yadav2012100% (2)
- Computer Networks (CS425) : Unix Socket ProgrammingDocument4 pagesComputer Networks (CS425) : Unix Socket ProgrammingPiuNo ratings yet
- Introduction To VIP With PCI Express Tec PDFDocument4 pagesIntroduction To VIP With PCI Express Tec PDFmaniNo ratings yet
- Take Asse Ssment - Enetwork Chapter 4 - Ccna Exploration: Network Fundamentals (Version 4.0)Document4 pagesTake Asse Ssment - Enetwork Chapter 4 - Ccna Exploration: Network Fundamentals (Version 4.0)IschmisNo ratings yet
- AssgB8 - TCP SocketDocument7 pagesAssgB8 - TCP Socketshravan kumbharNo ratings yet
- CISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkFrom EverandCISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkNo ratings yet
- Books ID: B0020 1. How Will You Add Styles To A Document?: Cybotech CampusDocument7 pagesBooks ID: B0020 1. How Will You Add Styles To A Document?: Cybotech Campusdharmendraalone93No ratings yet
- Define Process. Which Is The Command Used To Find Out Currently Executing Process in UNIX?Document4 pagesDefine Process. Which Is The Command Used To Find Out Currently Executing Process in UNIX?dharmendraalone93No ratings yet
- Java ProgrammingDocument6 pagesJava Programmingdharmendraalone93No ratings yet
- Distinguish CISC and RISC.: Client Server Architecture BT0052Document6 pagesDistinguish CISC and RISC.: Client Server Architecture BT0052dharmendraalone93No ratings yet
- Books ID: B0020 1. How Will You Add Styles To A Document?: Cybotech CampusDocument7 pagesBooks ID: B0020 1. How Will You Add Styles To A Document?: Cybotech Campusdharmendraalone93No ratings yet
- What Are The Difficulties and or Issues of E-Commerce? ExplainDocument13 pagesWhat Are The Difficulties and or Issues of E-Commerce? Explaindharmendraalone93No ratings yet
- Define Process. Which Is The Command Used To Find Out Currently Executing Process in UNIX?Document4 pagesDefine Process. Which Is The Command Used To Find Out Currently Executing Process in UNIX?dharmendraalone93No ratings yet
- Java ProgrammingDocument6 pagesJava Programmingdharmendraalone93No ratings yet
- What Are The Difficulties and or Issues of E-Commerce? ExplainDocument13 pagesWhat Are The Difficulties and or Issues of E-Commerce? Explaindharmendraalone93No ratings yet
- Lecture 02 Introduction To ARM7 ProcessorDocument29 pagesLecture 02 Introduction To ARM7 ProcessorDhruv GuptaNo ratings yet
- Co Unit1 Part4Document10 pagesCo Unit1 Part4Manjushree N.SNo ratings yet
- Chapter 10 - Code GenerationDocument31 pagesChapter 10 - Code Generationbekalu alemayehuNo ratings yet
- Sample Library For Instructions-V16 DOC v1 05 S7BasPro enDocument21 pagesSample Library For Instructions-V16 DOC v1 05 S7BasPro enSergNo ratings yet
- Implementation of Real-Time Applications On ARM MicrocontrollerDocument6 pagesImplementation of Real-Time Applications On ARM MicrocontrollerVAISHAKA N RAJNo ratings yet
- Chapter - 3Document46 pagesChapter - 3Himakshi SandalNo ratings yet
- Register Involved in Computer ProcessDocument3 pagesRegister Involved in Computer ProcessMuhammad Husnain KhalidNo ratings yet
- Benchmarking Tinyml Systems - Challenges and DirectionDocument8 pagesBenchmarking Tinyml Systems - Challenges and DirectionIoan ChirilaNo ratings yet
- How To Draw Timing DiagramDocument6 pagesHow To Draw Timing DiagramMurughesh MurughesanNo ratings yet
- Manasa Hanakere Krishnappa - ResumeDocument3 pagesManasa Hanakere Krishnappa - ResumesanjuNo ratings yet
- 01 Final ES PresentationDocument67 pages01 Final ES PresentationDeepakNo ratings yet
- Ec8552-Cao Unit 5Document72 pagesEc8552-Cao Unit 5Anonymous c75J3yX33No ratings yet
- Von Neumann Architecture ExplainedDocument8 pagesVon Neumann Architecture ExplainedDinesh KumarNo ratings yet
- Computer Architecture I: Digital DesignDocument56 pagesComputer Architecture I: Digital DesignHari K Priya TirumalarajuNo ratings yet
- Detailed Course OutlineDocument34 pagesDetailed Course OutlineMuhammad MuniruddinNo ratings yet
- Instruction Codes and Computer Registers in Basic Computer OrganizationDocument84 pagesInstruction Codes and Computer Registers in Basic Computer OrganizationKulwinder Jeet SinghNo ratings yet
- Introduction To ProgrammingDocument17 pagesIntroduction To ProgrammingVarun AroraNo ratings yet
- 1.1.1 Lesson 4 HomeworkDocument3 pages1.1.1 Lesson 4 HomeworkTom O'BrienNo ratings yet
- Assembler Syntax: Lui $at, 4096 Addu $at, $at, $a1 LW $a0, 8 ($at)Document35 pagesAssembler Syntax: Lui $at, 4096 Addu $at, $at, $a1 LW $a0, 8 ($at)GonzaloDominguezNo ratings yet
- HCS12 Controller-2Document20 pagesHCS12 Controller-2HaxfNo ratings yet
- CAQA5e ch3Document45 pagesCAQA5e ch3Jameem AhamedNo ratings yet
- CachesDocument56 pagesCachesAasma KhalidNo ratings yet
- Building An LLVM BackendDocument65 pagesBuilding An LLVM BackendfranNo ratings yet
- CrackingCodeZXSpectrum PDFDocument270 pagesCrackingCodeZXSpectrum PDFManolo GarciaNo ratings yet
- Adding 16-bit Hexadecimal Numbers with CarryDocument4 pagesAdding 16-bit Hexadecimal Numbers with CarrySudhanshu ShekharNo ratings yet
- Chapter 4 Processors and Memory Hierarchy: Module-2Document31 pagesChapter 4 Processors and Memory Hierarchy: Module-2Rahul RajNo ratings yet
- Design Ideas Book For The CDP1802Document122 pagesDesign Ideas Book For The CDP1802Jean GrégoireNo ratings yet
- Systemsoftwarenotes 100929171256 Phpapp02Document201 pagesSystemsoftwarenotes 100929171256 Phpapp02Shruthi PatilNo ratings yet
- MPMC 2marks (Unit 1 To 5) (Q & A)Document32 pagesMPMC 2marks (Unit 1 To 5) (Q & A)Ganapathy Ramadoss100% (2)
- Basic ComputerDocument3 pagesBasic ComputerDreime Estandarte-DecretoNo ratings yet