Professional Documents
Culture Documents
Draft Ietf Tls Https 03
Uploaded by
JendiHardonoOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Draft Ietf Tls Https 03
Uploaded by
JendiHardonoCopyright:
Available Formats
E.
Rescorla
INTERNET-DRAFT RTFM, Inc.
<draft-ietf-tls-https-03.txt> September 1999 (Expires March-00)
HTTP Over TLS
Status of this Memo
This document is an Internet-Draft and is in full conformance with
all provisions of Section 10 of RFC2026. Internet-Drafts are wor ing
documents of the Internet Engineering Tas Force (IETF), its areas,
and its wor ing groups. Note that other groups may also distribute
wor ing documents as Internet-Drafts.
Internet-Drafts are draft documents valid for a maximum of six months
and may be updated, replaced, or obsoleted by other documents at any
time. It is inappropriate to use Internet-Drafts as reference mate-
rial or to cite them other than as ``wor in progress.''
The list of current Internet-Drafts can be accessed at
http://www.ietf.org/ietf/1id-abstracts.txt
The list of Internet-Draft Shadow Directories can be accessed at
http://www.ietf.org/shadow.html.
To learn the current status of any Internet-Draft, please chec the
``1id-abstracts.txt'' listing contained in the Internet-Drafts Shadow
Directories on ftp.is.co.za (Africa), nic.nordu.net (Europe),
munnari.oz.au (Pacific Rim), ds.internic.net (US East Coast), or
ftp.isi.edu (US West Coast).
Abstract
This memo describes how to use TLS to secure HTTP connections over
the Internet. Current practice is to layer HTTP over SSL (the prede-
cessor to TLS), distinguishing secured traffic from insecure traffic
by the use of a different server port. This document documents that
practice using TLS. A companion document describes a method for using
HTTP/TLS over the same port as normal HTTP.
1. Introduction
HTTP [RFC2616] was originally used in the clear on the Internet.
However, increased use of HTTP for sensitive applications has
required security measures. SSL, and its successor TLS [TLS] were
designed to provide channel-oriented security. This document
describes how to use HTTP over TLS.
1.1. Discussion of this Draft
This draft is being discussed on the "ietf-apps-tls" mailing list. To
subscribe, send a message to:
ietf-apps-tls-request@imc.org
Rescorla [Page 1]
Internet-Draft HTTP Over TLS
with the single word
subscribe
in the body of the message. There is a Web site for the mailing list at
<http://www.imc.org/ietf-apps-tls/>.
1.2. Requirements Terminology
Keywords "MUST", "MUST NOT", "REQUIRED", "SHOULD", "SHOULD NOT" and
"MAY" that appear in this document are to be interpreted as described
in [RFC2119].
2. HTTP Over TLS
Conceptually, HTTP/TLS is very simple. Simply use HTTP over TLS pre-
cisely as you would use HTTP over TCP.
2.1. Connection Initiation
The agent acting as the HTTP client should also act as the TLS
client. It should initiate a connection to the server on the appro-
priate port and then send the TLS ClientHello to begin the TLS hand-
sha e. When the TLS handsha e has finished. The client may then ini-
tiate the first HTTP request. All HTTP data MUST be sentas TLS
"application data". Normal HTTP behavior, including retained connec-
tions should be followed.
2.2. Connection Closure
TLS provides a facility for secure connection closure. When a valid
closure alert is received, an implementation can be assured that no
further data will be received on that connection. TLS implementa-
tions MUST initiate an exchange of closure alerts before closing a
connection. A TLS implementation MAY, after sending a closure alert,
close the connection without waiting for the peer to send its closure
alert, generating an "incomplete close". Note that an implementation
which does this MAY choose to reuse the session. This SHOULD only be
done when the application nows (typically through detecting HTTP
message boundaries) that it has received all the message data that it
cares about.
As specified in [TLS], any implementation which receives a connection
close without first receiving a valid closure alert (a "premature
close") MUST NOT reuse that session. Note that a premature close
does not call into question the security of the data already
received, but simply indicates that subsequent data might have been
truncated. Because TLS is oblivious to HTTP request/response
Rescorla [Page 2]
Internet-Draft HTTP Over TLS
boundaries, it is necessary to examine the HTTP data itself (specifi-
cally the Content-Length header) to determine whether the truncation
occurred inside a message or between messages.
2.2.1. Client Behavior
Because HTTP uses connection closure to signal end of server data,
client implementations MUST treat any premature closes as errors and
the data received as potentially truncated. Two cases in particular
deserve special note:
A HTTP response without a Content-Length header. Since data length in
this situation is signalled by connection close a premature close
generated by the server cannot be distinguished from a spurious
close generated by an attac er.
A HTTP response with a valid Content-Length header closed before
all data has been read. Because TLS does not provide document
oriented protection, it is impossible to determine whether the
server has miscomputed the Content-Length or an attac er has
truncated the connection.
When encountering a premature close, a client SHOULD treat as com-
pleted all requests for which it has received as much data as speci-
fied in the Content-Length header.
A client detecting an incomplete close SHOULD recover gracefully. It
MAY resume a TLS session closed in this fashion.
Clients MUST send a closure alert before closing the connection.
Clients which are unprepared to receive any more data MAY choose not
to wait for the server's closure alert and simply close the connec-
tion, thus generating an incomplete close on the server side.
2.2.2. Server Behavior
RFC2068 permits an HTTP client to close the connection at any time,
and requires servers to recover gracefully. In particular, servers
SHOULD be prepared to receive an incomplete close from the client,
since the client can often determine when the end of server data is.
Servers SHOULD be willing to resume TLS sessions closed in this fash-
ion.
Implementation note: In HTTP implementations which do not use persis-
tent connections, the server ordinarily expects to be able to signal
end of data by closing the connection. When Content-Length is used,
however, the client may have already sent the closure alert and
Rescorla [Page 3]
Internet-Draft HTTP Over TLS
dropped the connection.
Servers MUST attempt to initiate an exchange of closure alerts with
the client before closing the connection. Servers MAY close the con-
nection after sending the closure alert, thus generating an incom-
plete close on the client side.
2.3. Port Number
The first data that an HTTP server expects to receive from the client
is the Request-Line production. The first data that a TLS server (and
hence an HTTP/TLS server) expects to receive is the ClientHello. Con-
sequently, common practice has been to run HTTP/TLS over a separate
port in order to distinguish which protocol is being used. When
HTTP/TLS is being run over a TCP/IP connection, the default port is
443. This does not preclude HTTP/TLS from being run over another
transport. TLS only presumes a reliable connection-oriented data
stream.
2.4. URI Format
HTTP/TLS is differentiated from HTTP URIs by using the 'https' proto-
col identifier in place of the 'http' protocol identifier. An example
URI specifying HTTP/TLS is:
https://www.example.com/~smith/home.html
3. Endpoint Identification
3.1. Server Identity
In general, HTTP/TLS requests are generated by dereferencing a URI.
As a consequence, the hostname for the server is nown to the client.
If the hostname is available, the client MUST chec it against the
server's identity as presented in the server's Certificate message,
in order to prevent man-in-the-middle attac s.
If the client has external information as to the expected identity of
the server, the hostname chec MAY be omitted. (For instance, a
client may be connecting to a machine whose address and hostname are
dynamic but the client nows the certificate that the server will
present.) In such cases, it is important to narrow the scope of
acceptable certificates as much as possible in order to prevent man
in the middle attac s. In special cases, it may be appropriate for
the client to simply ignore the server's identity, but it must be
understood that this leaves the connection open to active attac .
Rescorla [Page 4]
Internet-Draft HTTP Over TLS
If a subjectAltName extension of type dNSName is present, that MUST
be used as the identity. Otherwise, the (most specific) Common Name
field in the Subject field of the certificate MUST be used. Although
the use of the Common Name is existing practice, it is deprecated and
Certification Authorities are encouraged to use the dNSName instead.
Matching is performed using the matching rules specified by [PKIX].
If more than one identity of a given type is present in the certifi-
cate (e.g. more than one dNSName name, a match in any one of the set
is considered acceptable.) Names may contain the wildcard character *
which is considered to match any single domain name component or com-
ponent fragment. E.g. *.a.com matches foo.a.com but not
bar.foo.a.com. f*.com matches foo.com but not bar.com.
If the hostname does not match the identity in the certificate, user
oriented clients MUST either notify the user (clients MAY give the
user the opportunity to continue with the connection in any case) or
terminate the connection with a bad certificate error. Automated
clients MUST log the error to an appropriate audit log (if available)
and SHOULD terminate the connection (with a bad certificate error).
Automated clients MAY provide a configuration setting that disables
this chec , but MUST provide a setting which enables it.
Note that in many cases the URI itself comes from an untrusted
source. The above-described chec provides no protection against
attac s where this source is compromised. For example, if the URI was
obtained by clic ing on an HTML page which was itself obtained with-
out using HTTP/TLS, a man in the middle could have replaced the URI.
In order to prevent this form of attac , users should carefully exam-
ine the certificate presented by the server to determine if it meets
their expectations.
3.2. Client Identity
Typically, the server has no external nowledge of what the client's
identity ought to be and so chec s (other than that the client has a
certificate chain rooted in an appropriate CA) are not possible. If a
server has such nowledge (typically from some source external to
HTTP or TLS) it SHOULD chec the identity as described above.
Rescorla [Page 5]
Internet-Draft HTTP Over TLS
References
[PKIX] Housley, R., Ford, W., Pol , W. and D. Solo, "Internet
Public Key Infrastructure: Part I: X.509 Certificate and CRL
Profile", RFC 2459, January 1999.
[RFC-2616] Fielding, R., Gettys, J., Mogul, J., Frysty , H.,
Masinter, L., Leach, P. and T. Berners-Lee, "Hypertext
Transfer Protocol, HTTP/1.1" RFC 2616, June 1999.
[RFC2119] Bradner, S., "Key Words for use in RFCs to indicate
Requirement Levels", RFC2119, March 1997.
[TLS] Dier s, T., Allen, C., "The TLS Protocol", RFC2246, January 1999.
Security Considerations
This entire document is about security.
Author's Address
Eric Rescorla <e r@rtfm.com>
RTFM, Inc.
30 Newell Road, #16
East Palo Alto, CA 94303
Phone: (650) 328-8631
Rescorla [Page 6]
Internet-Draft HTTP Over TLS
Table of Contents
1. Introduction . . . . . . . . . . . . . . . . . . . . . . . . . . 1
1.1. Discussion of this Draft . . . . . . . . . . . . . . . . . . . 1
1.2. Requirements Terminology . . . . . . . . . . . . . . . . . . . 2
2. HTTP Over TLS . . . . . . . . . . . . . . . . . . . . . . . . . . 2
2.1. Connection Initiation . . . . . . . . . . . . . . . . . . . . . 2
2.2. Connection Closure . . . . . . . . . . . . . . . . . . . . . . 2
2.2.1. Client Behavior . . . . . . . . . . . . . . . . . . . . . . . 3
2.2.2. Server Behavior . . . . . . . . . . . . . . . . . . . . . . . 3
2.3. Port Number . . . . . . . . . . . . . . . . . . . . . . . . . . 4
2.4. URI Format . . . . . . . . . . . . . . . . . . . . . . . . . . 4
3. Endpoint Identification . . . . . . . . . . . . . . . . . . . . . 4
3.1. Server Identity . . . . . . . . . . . . . . . . . . . . . . . . 4
3.2. Client Identity . . . . . . . . . . . . . . . . . . . . . . . . 5
References . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6
Security Considerations . . . . . . . . . . . . . . . . . . . . . . 6
Author's Address . . . . . . . . . . . . . . . . . . . . . . . . . . 6
You might also like
- SSL Tls HttpsDocument32 pagesSSL Tls HttpsShivansh PundirNo ratings yet
- HTTP The Protocol Every Web Developer Must Know - Part 2Document10 pagesHTTP The Protocol Every Web Developer Must Know - Part 2David Lee100% (1)
- Telnet HTTP FTPDocument11 pagesTelnet HTTP FTPRohit VermaNo ratings yet
- In Introduction To HTTP BasicsDocument21 pagesIn Introduction To HTTP BasicsAlice StateNo ratings yet
- Chapter 2 QuestionsDocument12 pagesChapter 2 Questionsahmed zuhdNo ratings yet
- SSL and TLS: Privacy & IntegrityDocument4 pagesSSL and TLS: Privacy & IntegrityVishesh TripathiNo ratings yet
- Unit1 NotesDocument2 pagesUnit1 NotesSufiyan MoterwalaNo ratings yet
- Self - Request - Stack: 2.3.2. Program StackingDocument9 pagesSelf - Request - Stack: 2.3.2. Program StackingSignia DiseñoNo ratings yet
- HTTP BasicDocument1 pageHTTP BasicÍiĨiì Vô TâmNo ratings yet
- Introduction to HTTP and HTTPS ProtocolsDocument12 pagesIntroduction to HTTP and HTTPS ProtocolsAhmadSalmanNo ratings yet
- Lab 2Document7 pagesLab 2Pebo GreenNo ratings yet
- HTTP Secure (HTTPS) - Encrypted Communication ProtocolDocument6 pagesHTTP Secure (HTTPS) - Encrypted Communication ProtocolFRANCESCO222No ratings yet
- Hyper Text Transfer ProtocolDocument15 pagesHyper Text Transfer ProtocolNeeti Saurav PahujaNo ratings yet
- Unit VIIDocument8 pagesUnit VIIabdul jawadNo ratings yet
- HTTPSDocument19 pagesHTTPSmalabaranjaNo ratings yet
- File Transfer ProtocolDocument7 pagesFile Transfer Protocoljayan_SikarwarNo ratings yet
- Curl Protocols - Everything CurlDocument5 pagesCurl Protocols - Everything Curlnot hereNo ratings yet
- CSE4108 Lab-3Document3 pagesCSE4108 Lab-3Ariful HaqueNo ratings yet
- HTTP Vs HttpsDocument6 pagesHTTP Vs HttpsEduardo MarquesNo ratings yet
- Surf Jacking: "HTTPS Will Not Save You"Document11 pagesSurf Jacking: "HTTPS Will Not Save You"ArondeParon100% (1)
- The Design and Implementation of A SSL Proxy For Content SwitchDocument4 pagesThe Design and Implementation of A SSL Proxy For Content SwitchTania MitkovaNo ratings yet
- Network Fault Finding and Wireshark: - Analysing SSL/TLSDocument7 pagesNetwork Fault Finding and Wireshark: - Analysing SSL/TLSAlexHera89No ratings yet
- HTTP Desync AttackDocument18 pagesHTTP Desync Attacksetyahangga3No ratings yet
- HTTP Protocol FundamentalsDocument5 pagesHTTP Protocol Fundamentalsvatesh945No ratings yet
- HTTP and HttpsDocument24 pagesHTTP and Httpskhalid_saeed1025867No ratings yet
- Networking 101Document17 pagesNetworking 101Gusti Made Arya WijayaNo ratings yet
- Name Any Three Client Applications To Connect With FTP ServerDocument5 pagesName Any Three Client Applications To Connect With FTP ServerI2414 Hafiz Muhammad Zeeshan E1No ratings yet
- Secure Communication Channels: Secure Sockets Layer (SSL)Document5 pagesSecure Communication Channels: Secure Sockets Layer (SSL)Mani ShankarNo ratings yet
- Differences between SSL, TLS, TCP and UDP protocolsDocument10 pagesDifferences between SSL, TLS, TCP and UDP protocolsLILIAN KOMBANo ratings yet
- Troytech 70088 MCSE Study Guide Proxy2Document24 pagesTroytech 70088 MCSE Study Guide Proxy2abison_835688100% (2)
- WWW HTTP DNSDocument45 pagesWWW HTTP DNSMohd Shifan100% (1)
- Pop3s & SMTPSDocument9 pagesPop3s & SMTPSKolawole OgundareNo ratings yet
- Chapter02 SGDocument18 pagesChapter02 SGxheti21No ratings yet
- NSM 1st UtDocument13 pagesNSM 1st UtGeethaNo ratings yet
- HTTP 2 White PaperDocument26 pagesHTTP 2 White PaperFrancesco PapalucaNo ratings yet
- Internet and Web Lecture 6Document21 pagesInternet and Web Lecture 6Rakib MiaNo ratings yet
- WT Full NotesDocument232 pagesWT Full NotesLathaNo ratings yet
- Pop3s & SMTPSDocument6 pagesPop3s & SMTPSKolawole OgundareNo ratings yet
- Study Application Layer Protocols with WiresharkDocument5 pagesStudy Application Layer Protocols with WiresharkSALIM TADVINo ratings yet
- Protocols DevicesDocument3 pagesProtocols DevicesRoshan RaviNo ratings yet
- Protocols Devices STDDocument18 pagesProtocols Devices STDRavi RoshanNo ratings yet
- Ibrahiem Elbarki FTPDocument18 pagesIbrahiem Elbarki FTPAhmed AboubakrNo ratings yet
- Unit 2 Application LayerDocument15 pagesUnit 2 Application LayerPRATHAM DHARMANINo ratings yet
- HTTP ProtocolDocument8 pagesHTTP ProtocolAmr Mahmoud MorsyNo ratings yet
- Unit3 Part2Document4 pagesUnit3 Part2ENGINEERING EXTRACTSNo ratings yet
- Overview of the World Wide WebDocument19 pagesOverview of the World Wide WebM Joshua AlfredNo ratings yet
- HTTP Request ResponseDocument35 pagesHTTP Request ResponseD19DCS154 ARTH SONINo ratings yet
- NetworkingDocument4 pagesNetworkingNitesh JajuNo ratings yet
- Load BalancerDocument7 pagesLoad BalancermaheshNo ratings yet
- Pages from DOC-20240401-WA0009.Document5 pagesPages from DOC-20240401-WA0009.PILLARISETTY KARTHIK 2021-CSE UGNo ratings yet
- To Understand E-Mail,: Application LayerDocument14 pagesTo Understand E-Mail,: Application LayerKarthik KeyanNo ratings yet
- Sockets Layer (SSL) and The Follow-On (Subsequent) Internet Standard ofDocument8 pagesSockets Layer (SSL) and The Follow-On (Subsequent) Internet Standard ofFazeelur RahmanNo ratings yet
- Hypertext Transfer ProtocolDocument20 pagesHypertext Transfer ProtocolDani BobNo ratings yet
- Lesson 04: The Web and HTTP: Learning OutcomeDocument5 pagesLesson 04: The Web and HTTP: Learning OutcomeThilan NawagamuwaNo ratings yet
- Introduction: The Hypertext Transfer Protocol: Set Up An HTTP ProxyDocument4 pagesIntroduction: The Hypertext Transfer Protocol: Set Up An HTTP ProxyTahreer Jaber100% (1)
- TlsDocument18 pagesTlsasd666dsaNo ratings yet
- Lab SSLDocument7 pagesLab SSLJacinto BenaventeNo ratings yet
- Transport Layer SecurityDocument33 pagesTransport Layer SecurityFelix Enrique ParedesNo ratings yet
- Landsberg 1989Document13 pagesLandsberg 1989aldoNo ratings yet
- Euro FirefighterDocument2 pagesEuro FirefighterGustavo VydraNo ratings yet
- Voice PortalDocument8 pagesVoice PortalthegownuproosterNo ratings yet
- Accedian Networks EtherNID MetroNID 2pg FINAL 083112 PDFDocument2 pagesAccedian Networks EtherNID MetroNID 2pg FINAL 083112 PDFMark LamondNo ratings yet
- 1724 Albany, Ferndale, MI - Updated, Spacious BungalowDocument8 pages1724 Albany, Ferndale, MI - Updated, Spacious BungalowTodd Waller Real EstateNo ratings yet
- Field Symbols:: Type AnyDocument3 pagesField Symbols:: Type AnyRajesh YadavNo ratings yet
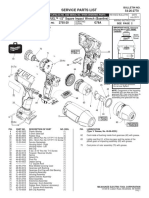
- 2755 22 (G78A) Milwaukee PBDocument2 pages2755 22 (G78A) Milwaukee PBZeckNo ratings yet
- Comment To RTDocument32 pagesComment To RTLim Wee BengNo ratings yet
- Pengaruh Penggunaan Kapur Sebagai Bahan Pengisi (Filler) Terhadap Karakteristik Campuran Beton Aspal Lapis Aus (Ac-Wc)Document18 pagesPengaruh Penggunaan Kapur Sebagai Bahan Pengisi (Filler) Terhadap Karakteristik Campuran Beton Aspal Lapis Aus (Ac-Wc)Nabillsya LoiseNo ratings yet
- Weather and Aviation PDFDocument10 pagesWeather and Aviation PDFSergio GasparriNo ratings yet
- Computer Software Testing TerminologyDocument99 pagesComputer Software Testing TerminologyoluninjaaNo ratings yet
- Foundation Practice Exam Questions 5Document11 pagesFoundation Practice Exam Questions 5Dr CoolzNo ratings yet
- Adobe 2017 Download LinksDocument4 pagesAdobe 2017 Download LinksDaśhīñg ÆžīNo ratings yet
- Zit 64 BVDocument12 pagesZit 64 BVVT86No ratings yet
- Acoustic Emission-Based Monitoring Approach For Friction Stir Welding of Aluminum Alloy AA6063-T6 With Different Tool Pin ProfilesDocument10 pagesAcoustic Emission-Based Monitoring Approach For Friction Stir Welding of Aluminum Alloy AA6063-T6 With Different Tool Pin ProfileslarryNo ratings yet
- Tensile Test AnalysisDocument8 pagesTensile Test AnalysisNazmul HasanNo ratings yet
- Accuret-A20: Electrical SpecificationsDocument2 pagesAccuret-A20: Electrical SpecificationsClaudio CalabreseNo ratings yet
- Project 1 Fettuccini Truss Bridge ReportDocument23 pagesProject 1 Fettuccini Truss Bridge ReportKah LeongNo ratings yet
- Et200s Im151 1 Standard Manual en-US en-USDocument66 pagesEt200s Im151 1 Standard Manual en-US en-USJesús Zacarías ZapataNo ratings yet
- Basics of GD&T TrainingDocument3 pagesBasics of GD&T TrainingShajil SNo ratings yet
- Hands-On Exercise Oracle 10g PL SQL - v1 0Document24 pagesHands-On Exercise Oracle 10g PL SQL - v1 0pavanNo ratings yet
- Acer Aspire 4735z 4736z 4935z 4936z - COMPAL LA-5272P KALG1 - REV 0.1secDocument46 pagesAcer Aspire 4735z 4736z 4935z 4936z - COMPAL LA-5272P KALG1 - REV 0.1secIhsan Yusoff IhsanNo ratings yet
- MAP Demo ExercisesDocument34 pagesMAP Demo ExercisesNancy HernandezNo ratings yet
- Hawker TOLD CardsDocument20 pagesHawker TOLD Cardsapi-3803613100% (1)
- RK-2001 Operation ManualDocument11 pagesRK-2001 Operation Manuale-ComfortUSANo ratings yet
- KfloppyDocument17 pagesKfloppyBhanuNo ratings yet
- PackagesDocument2 pagesPackagesSteven MirandaNo ratings yet
- An Experimental Comparative Review - PK NanavatiDocument9 pagesAn Experimental Comparative Review - PK NanavatiPurvesh NanavatiNo ratings yet
- 11 - Desain, Prototipe Dan KonstruksiDocument46 pages11 - Desain, Prototipe Dan KonstruksiUtari Via VivianNo ratings yet
- Lean & Environment ToolkitDocument96 pagesLean & Environment Toolkittinyplankton100% (7)