0% found this document useful (0 votes)
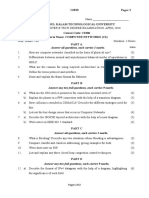
291 views15 pagesComputer Networks Exam Questions 2007-2008
This document contains an exam for a Computer Networks course, assessing knowledge of networking concepts and protocols. It includes:
1) A multiple choice section with questions on topics like network topologies, error detection, IP addressing, and TCP/UDP.
2) Longer answer sections requiring explanation of concepts like the OSI model layers, media access control protocols, routing algorithms, TCP operation, and application layer protocols like SMTP, HTTP, and FTP.
3) Sample questions assess knowledge of network design, addressing, routing protocols, error detection, media access, and transport/application layer protocols in detail. The exam evaluates both conceptual understanding and practical application of computer networking principles.
Uploaded by
Sathyanarayana YogendranCopyright
© Attribution Non-Commercial (BY-NC)
We take content rights seriously. If you suspect this is your content, claim it here.
Available Formats
Download as PDF, TXT or read online on Scribd
0% found this document useful (0 votes)
291 views15 pagesComputer Networks Exam Questions 2007-2008
This document contains an exam for a Computer Networks course, assessing knowledge of networking concepts and protocols. It includes:
1) A multiple choice section with questions on topics like network topologies, error detection, IP addressing, and TCP/UDP.
2) Longer answer sections requiring explanation of concepts like the OSI model layers, media access control protocols, routing algorithms, TCP operation, and application layer protocols like SMTP, HTTP, and FTP.
3) Sample questions assess knowledge of network design, addressing, routing protocols, error detection, media access, and transport/application layer protocols in detail. The exam evaluates both conceptual understanding and practical application of computer networking principles.
Uploaded by
Sathyanarayana YogendranCopyright
© Attribution Non-Commercial (BY-NC)
We take content rights seriously. If you suspect this is your content, claim it here.
Available Formats
Download as PDF, TXT or read online on Scribd