100% found this document useful (3 votes)
1K views40 pagesJavaScript in Phishing Attacks
This document outlines a lecture on phishing and malicious JavaScript. It discusses how phishing uses deception through web technology to steal identities for profit in an underground economy. It also examines how JavaScript can be used for mischief by accessing local state like the clipboard or browsing history, customizing page displays, probing networks through port scanning or timing attacks, and communicating data back to servers. The document provides examples of these techniques and discusses trends in web attacks.
Uploaded by
vschauhanCopyright
© Attribution Non-Commercial (BY-NC)
We take content rights seriously. If you suspect this is your content, claim it here.
Available Formats
Download as PPT, PDF, TXT or read online on Scribd
100% found this document useful (3 votes)
1K views40 pagesJavaScript in Phishing Attacks
This document outlines a lecture on phishing and malicious JavaScript. It discusses how phishing uses deception through web technology to steal identities for profit in an underground economy. It also examines how JavaScript can be used for mischief by accessing local state like the clipboard or browsing history, customizing page displays, probing networks through port scanning or timing attacks, and communicating data back to servers. The document provides examples of these techniques and discusses trends in web attacks.
Uploaded by
vschauhanCopyright
© Attribution Non-Commercial (BY-NC)
We take content rights seriously. If you suspect this is your content, claim it here.
Available Formats
Download as PPT, PDF, TXT or read online on Scribd
- Introduction: Introduces the topic of phishing and malicious JavaScript, setting the stage for detailed discussions.
- Outline: Provides an outline of the topics covered in the presentation related to phishing and online threats.
- Trends: Analyses trends in vulnerabilities and security threats over the years, highlighting the increasing incidents.
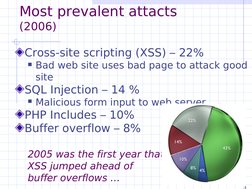
- Common Attacks: Details the most prevalent attacks in 2006, emphasizing the rise of cross-site scripting vulnerabilities.
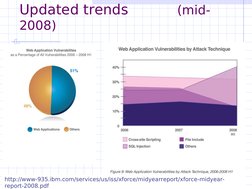
- Updated Trends: Discusses the updated security trends of mid-2008, focusing on web application vulnerabilities.
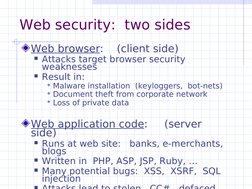
- Web Security: Explores web security from both client and server sides, highlighting potential weaknesses.
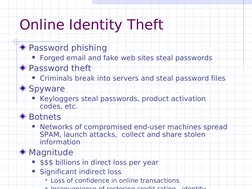
- Online Identity Theft: Examines the methods and impacts of online identity theft including phishing and botnets.
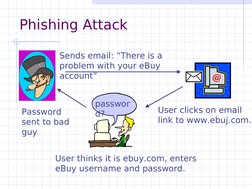
- Phishing Attack Example: Explains a typical phishing attack scenario with a visual example focusing on email scams.
- Spear-Phishing: Provides insights into spear-phishing tactics and how they target specific individuals or organizations.
- Underground Economy: Describes the underground economy around spam services and botnet rentals.
- Exploitation Cases: Highlights real-world cases of exploitation using phished accounts, focusing on financial damage caused.
- HTML and JavaScript: Covers the role of HTML and JavaScript in facilitating online threats, focusing on security vulnerabilities.
- Port Scanning: Explores how JavaScript can be used for port scanning and network probing.
- Remote Scripting: Discusses how remote scripting techniques are used to exploit web applications.
- Conclusion: Summarizes the key points discussed in the presentation regarding phishing and malicious JavaScript.
- Reading Recommendations: Provides reading recommendations for further study on phishing and related attacks.