Professional Documents
Culture Documents
Russia Influence Warning Letter From NSA Members
Uploaded by
Yahoo NewsOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Russia Influence Warning Letter From NSA Members
Uploaded by
Yahoo NewsCopyright:
Available Formats
October
6, 2016
We are concerned that an ongoing Russian influence operation is targeting the 2016
U.S. election. This is a serious national security issue that transcends partisan
politics.
For this reason, we urge our colleagues in the press and our fellow citizens to be
cautious in the use of allegedly leaked information. The free flow of information
and ideas is what makes Americas political discourse so vibrant, but we now know
that our enemies are using this part of our system against us.
Private cybersecurity firms, independent experts, and senior U.S. intelligence and
law enforcement officials, all link Guccifer 2.0 to Russia and identify Russian cyber
intelligence agents as the likely perpetrator of the hack of political institutions like
the DNC and the DCCC. In this election, private documents and emails stolen by
Guccifer 2.0 have already made their way into the public discourse.
The hackers themselves have told us more are coming.
While we cannot rule out the possibility of isolated cyber attacks on US voting
systems on Election Day, it is imperative that we focus on the broad disinformation
campaign that is already underway.
What is taking place in the United States follows a well-known Russian playbook:
First leak compelling and truthful information to gain credibility. The next step:
release fake documents that look the same. This leaves a discredited actor in the
position of denying the authenticity in the merciless court of public opinion, just
weeks before an election. When this tactic is successful, opinions change and the
foreign actor proves its ability to manipulate perceptions and likely votes.
Disinformation and influence operations like these are a formal part of Russian
military doctrine and intelligence operations. These operations most often target
Russias near neighbors, like Estonia, Georgia, and Ukraine. But the Russians have
also used cyber tools to influence elections in the Netherlands and spread false
stories through the media in Germany and here in the United States.
Thus far, Democratic candidates and staff, as well as former Republican Secretaries
of State, have been targeted with information obtained in the hack on the DNC. In
the instances when they have been given the opportunity, those attacked have
validated that the documents are genuine. The process has begun and stage has
been set for the introduction of false information.
As national security professionals, we hope to empower our fellow citizens to
understand the risks and dangers of disinformation. Altering stolen documents and
introducing them to the public is not the stuff of spy movies. It is a proven tactic of
Russian intelligence, and we expect it will happen here.
We urge our fellow citizens and members of the media to stay engaged and to think
critically about the facts they consume and disseminate. Only through collective
vigilance can we demonstrate that American opinions will not be manipulated by
malign foreign powers.
If it becomes apparent that foreign governments can covertly influence public
opinionand possibly even the outcome of electionsin the United States through
these types of actions, all future U.S. elections could become targets of foreign
intelligence operations. Our debates on critical national security issues will be
targeted in an effort to sway public opinion away from our national interests.
There is no amount of short-term partisan gain or perceived media scoop that could
justify that outcome. The only recourse is our vigilance and our vote.
Jeremy Bash, former Chief of Staff at the Department of Defense
Dan Benjamin, former State Department Coordinator for Counterterrorism
Max Boot, Senior Fellow at the Council on Foreign Relations
Michael Chertoff, former Secretary of Homeland Security
Derek Chollet, former Assistant Secretary of Defense for International Security Affairs
Richard Clarke, former National Coordinator for Security, Infrastructure Protection, and
Counter-terrorism
Mieke Eoyang, Vice President of the National Security Program at Third Way
Robert Kagan, Senior Fellow at the Brookings Institute
Brian Katulis, Senior Fellow at the Center for American Progress
Juliette Kayyem, former Assistant Secretary for Intergovernmental Affairs, Department
of Homeland Security
Carl Levin, former United States Senator from Michigan
Jim Miller, former Undersecretary of Defense for Policy
Julianne Smith, former Deputy National Security Advisor to the Vice President
Ken Sofer, Senior Policy Adviser at the Center for American Progress
Tara Sonenshine, former Undersecretary of State for Public Affairs and Public
Diplomacy
Moira Whelan, former Deputy Assistant Secretary of State for Public Affairs and Digital
Strategy
You might also like
- The U.S. and Its National SecurityDocument7 pagesThe U.S. and Its National SecurityJimmy HartmannNo ratings yet
- Attempts to Impeach Donald Trump: Declassified Government Documents, Investigation of Russian Election Interference & Legislative ProceduresFrom EverandAttempts to Impeach Donald Trump: Declassified Government Documents, Investigation of Russian Election Interference & Legislative ProceduresNo ratings yet
- Simpson House Intel TransDocument165 pagesSimpson House Intel TransCNBC.com100% (38)
- Summary of Unchecked By Rachael Bade: The Untold Story Behind Congress's Botched Impeachments of Donald TrumpFrom EverandSummary of Unchecked By Rachael Bade: The Untold Story Behind Congress's Botched Impeachments of Donald TrumpNo ratings yet
- Trump Presidency 40 - July 25th, 2018 To August 5th, 2018Document515 pagesTrump Presidency 40 - July 25th, 2018 To August 5th, 2018FW0400% (1)
- DCAT - Stephen Bannon - FBI Complaint MemoDocument1 pageDCAT - Stephen Bannon - FBI Complaint MemoGrant Stern75% (4)
- CERL Barr ReportDocument267 pagesCERL Barr ReportLaw&CrimeNo ratings yet
- Hillarys Espionage Far More Grave Than Anyone Realizes!!!Document102 pagesHillarys Espionage Far More Grave Than Anyone Realizes!!!bigleakerNo ratings yet
- White House Letter To Speaker Pelosi, Et Al. 10.08.2019Document8 pagesWhite House Letter To Speaker Pelosi, Et Al. 10.08.2019blc8897% (35)
- The Grizzly Steppe Report (Unmasking the Russian Cyber Activity): Official Joint Analysis Report: Tools and Hacking Techniques Used to Interfere the U.S. ElectionsFrom EverandThe Grizzly Steppe Report (Unmasking the Russian Cyber Activity): Official Joint Analysis Report: Tools and Hacking Techniques Used to Interfere the U.S. ElectionsNo ratings yet
- Sunrise Election Action GuideDocument15 pagesSunrise Election Action GuideExpose SunriseNo ratings yet
- Clinton 4Document531 pagesClinton 4MagaNWNo ratings yet
- Spygate: The Attempted Sabotage of Donald J. TrumpFrom EverandSpygate: The Attempted Sabotage of Donald J. TrumpRating: 4 out of 5 stars4/5 (21)
- Democrat Memo Charge and ResponseDocument5 pagesDemocrat Memo Charge and ResponseScott Johnson75% (4)
- Russian Cyber Attack - Grizzly Steppe Report & The Rules of Cyber Warfare: Hacking Techniques Used to Interfere the U.S. Election and to Exploit Government & Private Sectors, Recommended Mitigation Strategies and International Cyber-Conflict LawFrom EverandRussian Cyber Attack - Grizzly Steppe Report & The Rules of Cyber Warfare: Hacking Techniques Used to Interfere the U.S. Election and to Exploit Government & Private Sectors, Recommended Mitigation Strategies and International Cyber-Conflict LawNo ratings yet
- ELECTION FRAUD Adj The 2016 Media PreNarrative For 2020Document51 pagesELECTION FRAUD Adj The 2016 Media PreNarrative For 2020DGB DGBNo ratings yet
- Tyrants on Twitter: Protecting Democracies from Information WarfareFrom EverandTyrants on Twitter: Protecting Democracies from Information WarfareNo ratings yet
- Felix Satter Email Chain Shows Trump Family Met About His Felony PastDocument4 pagesFelix Satter Email Chain Shows Trump Family Met About His Felony PastGrant Stern100% (3)
- Russian Cyber Activity – The Grizzly Steppe Report: Strategy and Hacking Techniques Used to Interfere the U.S. Elections and to exploit Government and Private SectorsFrom EverandRussian Cyber Activity – The Grizzly Steppe Report: Strategy and Hacking Techniques Used to Interfere the U.S. Elections and to exploit Government and Private SectorsNo ratings yet
- CHINAGATE - Senate RPT Vol. IVDocument313 pagesCHINAGATE - Senate RPT Vol. IVNoFilter PoliticsNo ratings yet
- Russian Cyber Attack: The Rules of Cyber Warfare & Grizzly Steppe ReportFrom EverandRussian Cyber Attack: The Rules of Cyber Warfare & Grizzly Steppe ReportNo ratings yet
- NLPC Complaint With Office of Public Responsibility Against Aaron ZelinskyDocument18 pagesNLPC Complaint With Office of Public Responsibility Against Aaron ZelinskyJim HoftNo ratings yet
- Permit For "Million MAGA March"Document8 pagesPermit For "Million MAGA March"Washingtonian MagazineNo ratings yet
- Disrupt, Discredit, and Divide: How the New FBI Damages DemocracyFrom EverandDisrupt, Discredit, and Divide: How the New FBI Damages DemocracyRating: 5 out of 5 stars5/5 (1)
- Taylor Opening StatementDocument16 pagesTaylor Opening Statementacohnthehill100% (4)
- The Plot to Hack America: How Putin's Cyberspies and WikiLeaks Tried to Steal the 2016 ElectionFrom EverandThe Plot to Hack America: How Putin's Cyberspies and WikiLeaks Tried to Steal the 2016 ElectionRating: 4 out of 5 stars4/5 (35)
- Trump Appeals Colorado Insurrection FindingDocument15 pagesTrump Appeals Colorado Insurrection FindingRobert GouveiaNo ratings yet
- Power Lord Help Us All EmailDocument2 pagesPower Lord Help Us All EmailJohnSolomon92% (25)
- Ivana Trump Says She Is 'First Lady'Document1 pageIvana Trump Says She Is 'First Lady'ivon0% (1)
- 2022 03 24 Trump V Clinton Doc 1 COMPLAINT Case No 2 22 CV 14102 XXXX 108 Pgs FLDC 2022 Filed Mar 24 2022Document113 pages2022 03 24 Trump V Clinton Doc 1 COMPLAINT Case No 2 22 CV 14102 XXXX 108 Pgs FLDC 2022 Filed Mar 24 2022ΧΡΗΣΤΟΣ ΒΛΑΧΟΣNo ratings yet
- Alabama GOP ResolutionDocument2 pagesAlabama GOP ResolutionFox News67% (6)
- WISCONSIN VOTERS ALLIANCE V PENCEDocument7 pagesWISCONSIN VOTERS ALLIANCE V PENCERawStoryNo ratings yet
- List Order Source Politifact Snopes RatingDocument19 pagesList Order Source Politifact Snopes RatingJim Hoft0% (1)
- Final Michigan Notice of Supplemental AuthorityDocument42 pagesFinal Michigan Notice of Supplemental AuthorityMaurA Dowling100% (1)
- Trump Presidency 19 - December 20, 2017 To January 10, 2018Document511 pagesTrump Presidency 19 - December 20, 2017 To January 10, 2018FW040No ratings yet
- 2022-2-15.BGT Letter To Mastriano - Cover Letter and Schedule - RedactedDocument2 pages2022-2-15.BGT Letter To Mastriano - Cover Letter and Schedule - RedactedGeorge StockburgerNo ratings yet
- Chris Krebs Sues Trump and NewsmaxDocument73 pagesChris Krebs Sues Trump and NewsmaxGMG EditorialNo ratings yet
- Tweet 10282020 TypoDeLite: Do ALL Dem Roads Lead To CHINA?Document4 pagesTweet 10282020 TypoDeLite: Do ALL Dem Roads Lead To CHINA?DGB DGBNo ratings yet
- JW V State Benghazi Salafi 01733Document5 pagesJW V State Benghazi Salafi 01733fredvlucasNo ratings yet
- Lloyd Lee Welch TimelineDocument1 pageLloyd Lee Welch TimelineDavid LohrNo ratings yet
- DIG PDF - Seth Rich Info Dive 05252020Document21 pagesDIG PDF - Seth Rich Info Dive 05252020DGB DGBNo ratings yet
- Russian Hackers Targeting Conservative ... Icrosoft Says - US News - The GuardianDocument3 pagesRussian Hackers Targeting Conservative ... Icrosoft Says - US News - The GuardianAgustín GonzálezNo ratings yet
- Building A MonsterDocument13 pagesBuilding A MonsterAnonymous GMasIrX0No ratings yet
- Carter Page Letter To DoJ Re Election FraudDocument37 pagesCarter Page Letter To DoJ Re Election FraudBrett LoGiurato100% (2)
- DHS Intelligence ReportDocument6 pagesDHS Intelligence ReportAustine ObadoNo ratings yet
- The InterceptDocument18 pagesThe InterceptJose LuisNo ratings yet
- Intel Vets Challenge Russia Hack' Evidence - ConsortiumnewsDocument11 pagesIntel Vets Challenge Russia Hack' Evidence - ConsortiumnewsNektarios Del.No ratings yet
- Nance, Malcolm - The Plot To Destroy Democracy: How Putin and His Spies Are Undermining America and Dismantling The WestDocument345 pagesNance, Malcolm - The Plot To Destroy Democracy: How Putin and His Spies Are Undermining America and Dismantling The WestMallat50% (2)
- Conspiracy Denial in The U.S. Media: Journal of 9/11 StudiesDocument3 pagesConspiracy Denial in The U.S. Media: Journal of 9/11 StudiesJohn NadaNo ratings yet
- Equally Weird Data Mining 2ACDocument5 pagesEqually Weird Data Mining 2ACmarcusNo ratings yet
- Mueller Report SummariesDocument18 pagesMueller Report SummariesDan Evon93% (29)
- McCabe Statement For Record, SJC 11-10-20Document3 pagesMcCabe Statement For Record, SJC 11-10-20Herridge100% (3)
- The Russian White PaperDocument46 pagesThe Russian White PaperThe White Paper Project88% (33)
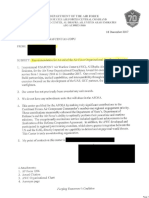
- AFCENTDocument4 pagesAFCENTYahoo News50% (2)
- Brett Kavanaugh Monica Lewinsky Memo 8.15.98Document2 pagesBrett Kavanaugh Monica Lewinsky Memo 8.15.98Rebecca HarringtonNo ratings yet
- Whistleblower Complaint Against President TrumpDocument9 pagesWhistleblower Complaint Against President TrumpYahoo News90% (84)
- Partially Redacted PDFDocument1 pagePartially Redacted PDFYahoo NewsNo ratings yet
- Letter From Secretary James MattisDocument2 pagesLetter From Secretary James MattisYahoo NewsNo ratings yet
- American - Made: Learn MoreDocument1 pageAmerican - Made: Learn MoreYahoo NewsNo ratings yet
- Partially Redacted PDFDocument1 pagePartially Redacted PDFYahoo NewsNo ratings yet
- Heart of Texas: SponsoredDocument1 pageHeart of Texas: SponsoredYahoo NewsNo ratings yet
- American - Veterans: Learn MoreDocument1 pageAmerican - Veterans: Learn MoreYahoo NewsNo ratings yet
- Mr. Hunter Walker Washington, D.C.: Barack ObamaDocument1 pageMr. Hunter Walker Washington, D.C.: Barack ObamaYahoo News100% (4)
- Redacted PDFDocument1 pageRedacted PDFYahoo NewsNo ratings yet
- Manafort IndictmentDocument31 pagesManafort IndictmentKatie Pavlich100% (5)
- Email FR: Shelbi Lewark - Subject: JASTADocument1 pageEmail FR: Shelbi Lewark - Subject: JASTAYahoo NewsNo ratings yet
- Chemical Attack QuestionDocument1 pageChemical Attack QuestionYahoo NewsNo ratings yet
- Manafort IndictmentDocument31 pagesManafort IndictmentKatie Pavlich100% (5)
- Stone Opening Statement FINALDocument47 pagesStone Opening Statement FINALYahoo News100% (2)
- James B. Comey StatementDocument7 pagesJames B. Comey StatementYahoo News100% (6)
- Letter To FacebookDocument2 pagesLetter To FacebookYahoo NewsNo ratings yet
- DJT - Russia Letter 03-06-2017Document1 pageDJT - Russia Letter 03-06-2017Katie PavlichNo ratings yet
- Comey Firing LettersDocument6 pagesComey Firing LettersYahoo News100% (5)
- Fara Complaint 20170329Document17 pagesFara Complaint 20170329Yahoo News100% (1)
- Media Accountability SurveyDocument7 pagesMedia Accountability SurveyYahoo News33% (3)
- LAI ContractDocument2 pagesLAI ContractYahoo NewsNo ratings yet
- Documents On Flynn Payment Sources and AmountsDocument4 pagesDocuments On Flynn Payment Sources and AmountsYahoo News0% (1)
- Updated Travel Ban - March 6Document18 pagesUpdated Travel Ban - March 6Yahoo NewsNo ratings yet
- 30 Barcelona V BarcelonaDocument2 pages30 Barcelona V BarcelonaJuan Samuel IsmaelNo ratings yet
- SpaDocument2 pagesSpaSheila Gutierrez QuijanoNo ratings yet
- Deed of Sale - Motor VehicleDocument4 pagesDeed of Sale - Motor Vehiclekyle domingoNo ratings yet
- Legal ResearchDocument27 pagesLegal ResearchPaul ValerosNo ratings yet
- Chapter 5commercial ArbitrationDocument8 pagesChapter 5commercial ArbitrationMa. Princess CongzonNo ratings yet
- Apostille (Blank)Document4 pagesApostille (Blank)crazybuttful100% (2)
- Do Board Gender Quotas Affect Firm Value? Evidence From California Senate Bill No. 826Document2 pagesDo Board Gender Quotas Affect Firm Value? Evidence From California Senate Bill No. 826Cato InstituteNo ratings yet
- Anti-Suffragists Student MaterialsDocument4 pagesAnti-Suffragists Student MaterialsKaren IdkNo ratings yet
- Project Spear & SABC Counter-Application 18092013Document6 pagesProject Spear & SABC Counter-Application 18092013Sylvia VollenhovenNo ratings yet
- Fimreite-Laegreid 2007 Sepcialization and Coordination - Multilevel SystemDocument31 pagesFimreite-Laegreid 2007 Sepcialization and Coordination - Multilevel SystemargosmexicanoNo ratings yet
- Equal Remuneration ActDocument10 pagesEqual Remuneration ActMG MaheshBabuNo ratings yet
- Pre-Trial brief-BPIvsasuncion-collection-metc Mkti 63Document6 pagesPre-Trial brief-BPIvsasuncion-collection-metc Mkti 63George MelitsNo ratings yet
- Origin and Development of IHLDocument38 pagesOrigin and Development of IHLMoniruzzaman Juror100% (1)
- Foreign Policy Vs DiplomacyDocument1 pageForeign Policy Vs DiplomacyJames RobertsNo ratings yet
- Padilla V DizonDocument5 pagesPadilla V DizonJulius ManaloNo ratings yet
- Important Provisions Under RA 9139Document2 pagesImportant Provisions Under RA 9139Myn Mirafuentes Sta Ana0% (1)
- Edith (R192153V) BuzLaw Assignment 2020Document5 pagesEdith (R192153V) BuzLaw Assignment 2020Tsy DeeNo ratings yet
- IE Mumbai 08 - 080520135224Document15 pagesIE Mumbai 08 - 080520135224TomNo ratings yet
- Berrien County, Michigan August 2, 2022 - UNOFFICIAL Candidate ListDocument6 pagesBerrien County, Michigan August 2, 2022 - UNOFFICIAL Candidate ListWXMINo ratings yet
- Student Branch Chapter Formation Petition 2015Document4 pagesStudent Branch Chapter Formation Petition 2015Andrea Mena LaraNo ratings yet
- Kgaf 2020 Stall FormDocument7 pagesKgaf 2020 Stall FormAmit JainNo ratings yet
- Penny v. Little 3 Scam. 301, 1841 WL 3322 Scam ErrorDocument5 pagesPenny v. Little 3 Scam. 301, 1841 WL 3322 Scam ErrorThalia SandersNo ratings yet
- Anushka Admit Card FirDocument1 pageAnushka Admit Card FirRahul KumarNo ratings yet
- 1 Bachrach V Siefert DIGESTDocument1 page1 Bachrach V Siefert DIGESTGieann BustamanteNo ratings yet
- Aral Pan 7 Sinaunang Kabihasnan Sa Asya (Pagsasanay Sa Mag-Aaral)Document7 pagesAral Pan 7 Sinaunang Kabihasnan Sa Asya (Pagsasanay Sa Mag-Aaral)Ailea Jeanne Gonzales Castellano100% (1)
- Characteristics of Marine InsuranceDocument11 pagesCharacteristics of Marine Insurancerahul50% (2)
- Unclaimed Property Rules FINAL (1) - 0Document10 pagesUnclaimed Property Rules FINAL (1) - 0Stacia SmithNo ratings yet
- ANU - The 2006 Military Takeover in Fiji A Coup To End All Coups - Fraenkel and Firth and Lal EdsDocument486 pagesANU - The 2006 Military Takeover in Fiji A Coup To End All Coups - Fraenkel and Firth and Lal EdsIntelligentsiya HqNo ratings yet
- 9 First Philippine Industrial Corporation Vs Court of AppealsDocument2 pages9 First Philippine Industrial Corporation Vs Court of AppealsKaryl Eric BardelasNo ratings yet
- Presley - Complaint Statement of Facts 0Document8 pagesPresley - Complaint Statement of Facts 0Anonymous GF8PPILW5No ratings yet
- Son of Hamas: A Gripping Account of Terror, Betrayal, Political Intrigue, and Unthinkable ChoicesFrom EverandSon of Hamas: A Gripping Account of Terror, Betrayal, Political Intrigue, and Unthinkable ChoicesRating: 4.5 out of 5 stars4.5/5 (501)
- For Love of Country: Leave the Democrat Party BehindFrom EverandFor Love of Country: Leave the Democrat Party BehindRating: 4.5 out of 5 stars4.5/5 (3)
- The War after the War: A New History of ReconstructionFrom EverandThe War after the War: A New History of ReconstructionRating: 5 out of 5 stars5/5 (2)
- An Unfinished Love Story: A Personal History of the 1960sFrom EverandAn Unfinished Love Story: A Personal History of the 1960sRating: 5 out of 5 stars5/5 (3)
- Broken Money: Why Our Financial System Is Failing Us and How We Can Make It BetterFrom EverandBroken Money: Why Our Financial System Is Failing Us and How We Can Make It BetterRating: 5 out of 5 stars5/5 (3)
- Age of Revolutions: Progress and Backlash from 1600 to the PresentFrom EverandAge of Revolutions: Progress and Backlash from 1600 to the PresentRating: 4.5 out of 5 stars4.5/5 (7)
- Pagan America: The Decline of Christianity and the Dark Age to ComeFrom EverandPagan America: The Decline of Christianity and the Dark Age to ComeRating: 5 out of 5 stars5/5 (2)
- Prisoners of Geography: Ten Maps That Explain Everything About the WorldFrom EverandPrisoners of Geography: Ten Maps That Explain Everything About the WorldRating: 4.5 out of 5 stars4.5/5 (1145)
- Financial Literacy for All: Disrupting Struggle, Advancing Financial Freedom, and Building a New American Middle ClassFrom EverandFinancial Literacy for All: Disrupting Struggle, Advancing Financial Freedom, and Building a New American Middle ClassNo ratings yet
- The Russia Hoax: The Illicit Scheme to Clear Hillary Clinton and Frame Donald TrumpFrom EverandThe Russia Hoax: The Illicit Scheme to Clear Hillary Clinton and Frame Donald TrumpRating: 4.5 out of 5 stars4.5/5 (11)
- How States Think: The Rationality of Foreign PolicyFrom EverandHow States Think: The Rationality of Foreign PolicyRating: 5 out of 5 stars5/5 (7)
- The Exvangelicals: Loving, Living, and Leaving the White Evangelical ChurchFrom EverandThe Exvangelicals: Loving, Living, and Leaving the White Evangelical ChurchRating: 4.5 out of 5 stars4.5/5 (13)
- Darkest Hour: How Churchill Brought England Back from the BrinkFrom EverandDarkest Hour: How Churchill Brought England Back from the BrinkRating: 4 out of 5 stars4/5 (31)
- Compromised: Counterintelligence and the Threat of Donald J. TrumpFrom EverandCompromised: Counterintelligence and the Threat of Donald J. TrumpRating: 4 out of 5 stars4/5 (18)
- The Smear: How Shady Political Operatives and Fake News Control What You See, What You Think, and How You VoteFrom EverandThe Smear: How Shady Political Operatives and Fake News Control What You See, What You Think, and How You VoteRating: 4.5 out of 5 stars4.5/5 (16)
- Franklin & Washington: The Founding PartnershipFrom EverandFranklin & Washington: The Founding PartnershipRating: 3.5 out of 5 stars3.5/5 (14)
- Bind, Torture, Kill: The Inside Story of BTK, the Serial Killer Next DoorFrom EverandBind, Torture, Kill: The Inside Story of BTK, the Serial Killer Next DoorRating: 3.5 out of 5 stars3.5/5 (77)
- You Can't Joke About That: Why Everything Is Funny, Nothing Is Sacred, and We're All in This TogetherFrom EverandYou Can't Joke About That: Why Everything Is Funny, Nothing Is Sacred, and We're All in This TogetherNo ratings yet
- The Return of George Washington: Uniting the States, 1783–1789From EverandThe Return of George Washington: Uniting the States, 1783–1789Rating: 4 out of 5 stars4/5 (22)
- Heretic: Why Islam Needs a Reformation NowFrom EverandHeretic: Why Islam Needs a Reformation NowRating: 4 out of 5 stars4/5 (57)
- Thomas Jefferson: Author of AmericaFrom EverandThomas Jefferson: Author of AmericaRating: 4 out of 5 stars4/5 (107)
- Jesus and the Powers: Christian Political Witness in an Age of Totalitarian Terror and Dysfunctional DemocraciesFrom EverandJesus and the Powers: Christian Political Witness in an Age of Totalitarian Terror and Dysfunctional DemocraciesRating: 4.5 out of 5 stars4.5/5 (7)