Professional Documents
Culture Documents
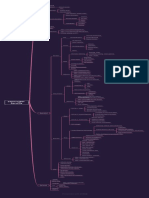
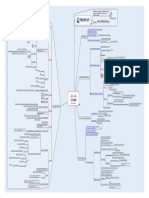
MindCert CISSP Cryptography MindMap
MindCert CISSP Cryptography MindMap
Uploaded by
cpawan_69Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
MindCert CISSP Cryptography MindMap
MindCert CISSP Cryptography MindMap
Uploaded by
cpawan_69Copyright:
Available Formats
X.
509 IDEA RSA
S/MIME
Motivation and Study Techniques to help you learn, remember, and pass your technical exams!
Cisco CISSP CEH More coming soon...
Condentiality Key Exchange
PGP
Visit us
www.mindcert.com
Web of Trust not PKI Between application and transport layers Uses digital certs Hidden to the user Browser support AH ESP WAP WTLS Uses SKIPJACK Escrow Security Layer
SSL/TLS
Cryptography Cryptanalysis
Art relating to encrypting and decrypting information Art relating to converting Ciphertext into plaintext without the secret key Encrypting data on the network IPSec L2TP SSL
IPSec
Link Encryption
Wireless
Misc Security Applications Denitions
End-to-end Encryption Repudiation
Encryption from source to system/Client to Server Non-repudiation
An embedded chip
Denial of sending a message
Key stored in two places
Clipper
Traffic Analysis Traffic Padding Work Factor
Inference of information from analysis of traffic Generation of spurious data units
For government to spy on you! Two identical pads/keys Unbreakable Pads can only be used once relies on physical storage of the pads Distribution a NIGHTMARE Hiding text in a .JPG Hiding data in another format
Effort/Time needed to overcome a protective measure
One time Pad Substitution Ciphers Steganography
Issuing CA SSL For e-mail Replace one letter with another one Monoalphabetic Uses more than one method Transposes the keys Does not follow a common pattern CA Server Personal Symmetric
History
Transposition Ciphers
Encryption Categories Types of Certicates
Algorithmic
Asymmetric Hash
Older Secret algorithm Newer Secrecy is provided by the key Known algorithm Strength of the algorithm
ActiveX Controls
Software Publishers The authenticating agency CA
Fundamentals PKI
Terminology
Systems
Keyed Systems
The end user or device listed in the subject eld of the X.509 certicate A public document containing the rules of the CA
End Entity
Certicate Policy Statement Certication Path RA
CISSP
Cryptography
Encryption Strength
Secrecy of the keys Length of the key
The traceable history of parties who have vouched for this certicate
A trusted body that can verify the authenticity of a person or host Where clients store the Certicate
Uses the same key to encrypt and decrypt
Encrypts data in discrete blocks Data is padded if required Block Block size usually 64 or 128 bytes long Most popular method Encrypts data bit by bit Verication
Certificate Repository
An answer to the symmetric Key Distribution problem Based on Public Keys and Private Key pairs
Only receiver can decrypt it Plain text is encrypted with the receivers public key
Ciphers
Stream
Condentiality Authentication
Fastest Cannot verify stream so not considered as secure as block mode 56 bit Key Industry standard Block Cipher Diffusion and Confusion NIST
Hash provides integrity Encryption with the Private signature provides Authentication
Then encrypted with private key to create a Digital Signature Provided by hashing Combats MITM Attacks 160 Bits Uses SHA
Integrity
DSS
Fast and simple Problems Single key distribution is problematic Can be cracked Cipher Block Chaining Operating Modes Electronic Code Book Cipher Feedback Output Feedback Confusion Spread the inuence of a plain text character P Box Conceals the statistical connection between cipher and plain texts S Box
Uses a shared secret to combine with the hash Faster than using asymmetric with the hash SHA HMAC MD5 HMAC Faster than using the public/private key pair Provides condentiality Variants S/MIME is used for secure emails S/MIME uses session keys to encrypt the message 160 bit HASH 128 bit HASH Based on Factoring two large prime numbers Based on elliptic curve discreet logarithms Faster than RSA movianVPN Great for PDAs ECC IDEA RC4 SHA
Hashed Message Authentication Code (HMAC)
Asymmetric/Public Key Fundamentals
DES
S/MIME
Symmetric/Private Key Fundamentals
Symmetric Algorithms
MD5 RSA Diffusion
Algorithms
3DES
112 or 168 bit DES but with two or three keys
128 bit Variable length 1-448 bit Up to 256 bit 128, 192, or 256 bit
Repeated use of a key makes it easier to crack
Both sender and receiver must have the same key Based on modular arithmetic Can use DH
Blowsh
Key Distribution
Key Distribution and Management Issues
Two Fish
AES
Rijndael Supports smart cards and 32, 64 bit processors NIST competition winner
CISSP Cryptography.mmap - 15/05/2009 - Andrew Mason
You might also like
- CISSP MindMapDocument66 pagesCISSP MindMapJuan Carlos Angarita C.100% (7)
- CISSP Cheat Sheet Domain 3Document1 pageCISSP Cheat Sheet Domain 3Zainulabdin100% (5)
- SSCP / Cissp Notes I Used To PassDocument43 pagesSSCP / Cissp Notes I Used To Passmilo_andy100% (4)
- Cyber Kill Chain ProcessDocument5 pagesCyber Kill Chain ProcessHema LathaNo ratings yet
- 022 Thor-Teaches-study-guide-CISSP-domain-2 - (FreeCourseWeb - Com)Document7 pages022 Thor-Teaches-study-guide-CISSP-domain-2 - (FreeCourseWeb - Com)LinuxPower100% (2)
- Mind Maps 2023 CisspDocument71 pagesMind Maps 2023 CisspRavinder KantNo ratings yet
- CISSP How To Pass TrainingDocument713 pagesCISSP How To Pass TrainingJose RiveraNo ratings yet
- Bluetooth HackingDocument2 pagesBluetooth HackingjayarajanNo ratings yet
- Course Overview: This Course Provides In-Depth Coverage of The Eight Domains Required To Pass The CISSP ExamDocument30 pagesCourse Overview: This Course Provides In-Depth Coverage of The Eight Domains Required To Pass The CISSP ExamAbdul GhaffarNo ratings yet
- CISSP Cheat SheetsDocument1 pageCISSP Cheat SheetsRajaram K.VNo ratings yet
- IT Security Director CISSP in Kansas City Resume David WhippleDocument4 pagesIT Security Director CISSP in Kansas City Resume David WhippleDavidWhipple100% (1)
- CISSP End GameDocument80 pagesCISSP End Gamelidik23489100% (5)
- Asset Attack Vectors: Building Effective Vulnerability Management Strategies to Protect OrganizationsFrom EverandAsset Attack Vectors: Building Effective Vulnerability Management Strategies to Protect OrganizationsNo ratings yet
- CISSP Exam QuestionsDocument57 pagesCISSP Exam Questionshaashim brownNo ratings yet
- MindCert CEH Ethical Hacking MindMapDocument1 pageMindCert CEH Ethical Hacking MindMapgarbett294No ratings yet
- Cybersec First Responder® (Cfr-410) Exam BlueprintDocument20 pagesCybersec First Responder® (Cfr-410) Exam BlueprintOsama KhairyNo ratings yet
- CISM - Cybrary TrainingDocument2 pagesCISM - Cybrary TrainingRAJESH SNo ratings yet
- CISSP Cheat Sheet Domain 8-2 PDFDocument1 pageCISSP Cheat Sheet Domain 8-2 PDFnjNo ratings yet
- CisspDocument16 pagesCisspRyan GlasgowNo ratings yet
- CISSP Exam Prep Questions, Answers & Explanations: 1500+ CISSP Practice Questions with SolutionsFrom EverandCISSP Exam Prep Questions, Answers & Explanations: 1500+ CISSP Practice Questions with SolutionsRating: 3 out of 5 stars3/5 (7)
- Module 1: Security Management: Lesson 1: Confidentiality, Integrity, and AvailabilityDocument7 pagesModule 1: Security Management: Lesson 1: Confidentiality, Integrity, and AvailabilityAntonio BrandãoNo ratings yet
- MindCert CISSP Application Development MindMapDocument1 pageMindCert CISSP Application Development MindMapjayarajanNo ratings yet
- MindCert CISSP Application Development MindMapDocument1 pageMindCert CISSP Application Development MindMapjayarajanNo ratings yet
- CISSP Combined NotesDocument59 pagesCISSP Combined NotesAnonymous 9d1jFv100% (4)
- Thor Teaches Study Guide CISSP Domain 6Document11 pagesThor Teaches Study Guide CISSP Domain 6babyNo ratings yet
- CISSP Cheat Sheet Domain 1-2 PDFDocument1 pageCISSP Cheat Sheet Domain 1-2 PDFnjNo ratings yet
- Crypto Map Version 1.0Document1 pageCrypto Map Version 1.0SylasMendesNo ratings yet
- CISSP Test TemplateDocument37 pagesCISSP Test TemplateRichard WilliamsNo ratings yet
- Mindcert Cissp BCP MindmapDocument1 pageMindcert Cissp BCP MindmapjayarajanNo ratings yet
- Learn Cyber SecurityDocument1 pageLearn Cyber SecurityPHẠM MINH TRÍNo ratings yet
- Key Tables, Charts and Flows For SSCP - CISSPDocument45 pagesKey Tables, Charts and Flows For SSCP - CISSPKevin HuangNo ratings yet
- CEH Quick Review GuideDocument55 pagesCEH Quick Review GuideAnonymous Y6jSgL100% (1)
- 2023+CISSP+Domain+1+Study+Guide+by+ThorTeaches Com+v4 0Document33 pages2023+CISSP+Domain+1+Study+Guide+by+ThorTeaches Com+v4 0somkumar1100% (2)
- Thor Teaches Study Guide CISSP Domain 7Document40 pagesThor Teaches Study Guide CISSP Domain 7babyNo ratings yet
- MindCert Cisco IPsec MindMapDocument1 pageMindCert Cisco IPsec MindMapcpawan_69No ratings yet
- MindCert CISSP Access Control MindMap PDFDocument1 pageMindCert CISSP Access Control MindMap PDFZeeshan RanaNo ratings yet
- Cissp WeekDocument159 pagesCissp Weekrcb023100% (1)
- MindCert CISSP Physical Security MindMapDocument1 pageMindCert CISSP Physical Security MindMapbesmart2000100% (1)
- Mathematics Olympiad For Class 6th 7th 8th Set 1 PDFDocument17 pagesMathematics Olympiad For Class 6th 7th 8th Set 1 PDFRakesh SinghNo ratings yet
- Key Mnemonics To Know - CisspDocument4 pagesKey Mnemonics To Know - CisspSairam R KonalaNo ratings yet
- Top 15 Indicators of CompromiseDocument7 pagesTop 15 Indicators of Compromisenandaanuj100% (1)
- MindCert CISSP Access Control MindMapDocument1 pageMindCert CISSP Access Control MindMapjayarajan100% (1)
- MindCert CISSP Access Control MindMapDocument1 pageMindCert CISSP Access Control MindMapjayarajan100% (1)
- ESP8266 Tutorial - How To Control Anything From The Internet! - DIY HackingDocument8 pagesESP8266 Tutorial - How To Control Anything From The Internet! - DIY HackingjayarajanNo ratings yet
- CISSP ExqsDocument20 pagesCISSP Exqssentoubudo1647No ratings yet
- CISSP CryptographyDocument1 pageCISSP CryptographyonlysubasNo ratings yet
- 2021 CompTIA CySA+ CS0-002 Real DumpsDocument11 pages2021 CompTIA CySA+ CS0-002 Real DumpskaronbillNo ratings yet
- CISSP NotesDocument3 pagesCISSP Noteslidik23489No ratings yet
- My Cissp Success Journey: (Lalit Kumar, CISSP, CISA, ISO 27001 LA, CEH, ITIL, DBA, System Admin)Document2 pagesMy Cissp Success Journey: (Lalit Kumar, CISSP, CISA, ISO 27001 LA, CEH, ITIL, DBA, System Admin)Abdul MalikNo ratings yet
- CISSP Whole Glossary2021Document64 pagesCISSP Whole Glossary2021babuNo ratings yet
- CISSP Mind Maps by Matheus PDF 1638358395Document10 pagesCISSP Mind Maps by Matheus PDF 1638358395Rodrigo Juan100% (1)
- CPTE CourseDocument11 pagesCPTE CourseGudden GuptaNo ratings yet
- How To Crack The CISSPDocument3 pagesHow To Crack The CISSPSayed Ashraf Husaini KaziNo ratings yet
- CCSK Prep Guide V3Document4 pagesCCSK Prep Guide V3satish_networkerNo ratings yet
- Cissp Quiz QuestionsDocument7 pagesCissp Quiz Questionsthejoker2055100% (1)
- Lesson 2 - The RPA Business Analyst - Role, Skills and ChallengesDocument5 pagesLesson 2 - The RPA Business Analyst - Role, Skills and ChallengesjayarajanNo ratings yet
- Ooad Case StudiesDocument21 pagesOoad Case StudiesThanuja Malla100% (4)
- Thor Teaches Study Guide CISSP Domain 8Document30 pagesThor Teaches Study Guide CISSP Domain 8baby100% (1)
- MindCert Cisco IPsec MindMap PDFDocument1 pageMindCert Cisco IPsec MindMap PDFzinzinNo ratings yet
- CISSP Domain One: Security and Risk Management-What You Need To Know For The ExamDocument14 pagesCISSP Domain One: Security and Risk Management-What You Need To Know For The ExamLaptop salesNo ratings yet
- Cysa+ Cs0-002 Exam Topics Notes: 1.0 Threat and Vulnerability ManagementDocument15 pagesCysa+ Cs0-002 Exam Topics Notes: 1.0 Threat and Vulnerability ManagementainzNo ratings yet
- Cybersecurity Training Career Pathways - Final v1.0 Rev 10062020Document2 pagesCybersecurity Training Career Pathways - Final v1.0 Rev 10062020HafizPradanaGemilangNo ratings yet
- Cissp Domain Refresh Webinar SlidesDocument35 pagesCissp Domain Refresh Webinar Slidesuwb_groupNo ratings yet
- Network Segmentation Strategy A Complete Guide - 2020 EditionFrom EverandNetwork Segmentation Strategy A Complete Guide - 2020 EditionNo ratings yet
- Cyberoam CR50 IaDocument2 pagesCyberoam CR50 IaqutbuddinsNo ratings yet
- A Video Encryption and Decryption Using Different TechniquesDocument6 pagesA Video Encryption and Decryption Using Different TechniquesKrishnamoorthy KumarNo ratings yet
- Android Security RoadmapDocument1 pageAndroid Security RoadmappushpeshkarkiNo ratings yet
- UiPath Licensing - Licensing ModelsDocument3 pagesUiPath Licensing - Licensing ModelsjayarajanNo ratings yet
- UiPath Licensing - Platform ComponentsDocument2 pagesUiPath Licensing - Platform ComponentsjayarajanNo ratings yet
- UiPath Licensing - Standalone LicensesDocument2 pagesUiPath Licensing - Standalone LicensesjayarajanNo ratings yet
- Lesson 3 - The RPA Journey and The BA's RoleDocument3 pagesLesson 3 - The RPA Journey and The BA's RolejayarajanNo ratings yet
- Lab Manual 1768Document84 pagesLab Manual 1768jayarajanNo ratings yet
- MindCert CISSP Law MindMap PDFDocument1 pageMindCert CISSP Law MindMap PDFprog_man_0101No ratings yet
- Embedded and Real Time SystemsDocument6 pagesEmbedded and Real Time Systemsjayarajan0% (1)
- Exam PricingDocument1 pageExam PricingjayarajanNo ratings yet
- Sample ExamDocument38 pagesSample ExamjayarajanNo ratings yet
- Cisco SSHDocument1 pageCisco SSHjayarajan100% (1)
- To Disable The Access To USB PortDocument1 pageTo Disable The Access To USB PortjayarajanNo ratings yet
- EC Council BrochureDocument68 pagesEC Council Brochurejayarajan100% (1)
- Sec Sec For Vpns W Ipsec Xe 3s Book PDFDocument108 pagesSec Sec For Vpns W Ipsec Xe 3s Book PDFKishore KumarNo ratings yet
- Secure Key EstablishmenDocument229 pagesSecure Key EstablishmenjetxoNo ratings yet
- CNS C 2Document15 pagesCNS C 2HarithaNo ratings yet
- Cryptography and Network Security: Third Edition by William Stallings Lecture Slides by Lawrie BrownDocument23 pagesCryptography and Network Security: Third Edition by William Stallings Lecture Slides by Lawrie BrownEli PriyatnaNo ratings yet
- SyllabusDocument6 pagesSyllabusAshish RanjanNo ratings yet
- 4 Modes Operations RC4Document37 pages4 Modes Operations RC4Komal BansalNo ratings yet
- Towards Dependable and Trustworthy Outsourced Computing A Comprehensive Survey and TutorialDocument11 pagesTowards Dependable and Trustworthy Outsourced Computing A Comprehensive Survey and Tutorialali rahimiNo ratings yet
- 2018-CE-124 - Lab 6 - CE408Document7 pages2018-CE-124 - Lab 6 - CE408Ashar AslamNo ratings yet
- A Review of Quantum Key Distribution Protocols in The Perspective of Smart Grid Communication SecurityDocument14 pagesA Review of Quantum Key Distribution Protocols in The Perspective of Smart Grid Communication SecurityNati ManNo ratings yet
- Xiaodong Lin, Chenxi Zhang, Theodora Dule Auth., Xuejia Lai, Dawu Gu, Bo Jin, Yongquan Wang, Hui Li Eds. Forensics in Telecommunications, Information, and Multimedia ThirDocument329 pagesXiaodong Lin, Chenxi Zhang, Theodora Dule Auth., Xuejia Lai, Dawu Gu, Bo Jin, Yongquan Wang, Hui Li Eds. Forensics in Telecommunications, Information, and Multimedia ThirsauloNo ratings yet
- Indjcse11 02 04 177 PDFDocument7 pagesIndjcse11 02 04 177 PDFUriel Cedeño AntunezNo ratings yet
- Practical - 1: Aim:-Implement Caesar Cipher Encryption-Decryption. IntroductionDocument4 pagesPractical - 1: Aim:-Implement Caesar Cipher Encryption-Decryption. IntroductionPranav PatelNo ratings yet
- cns19 Lec2 3 4Document86 pagescns19 Lec2 3 4Naveed Ahmad AwanNo ratings yet
- Intermed: An Efficient Interoperable Blockchain Protocol For Electronic Health Record TransferringDocument11 pagesIntermed: An Efficient Interoperable Blockchain Protocol For Electronic Health Record Transferringngocthanhdinh7987No ratings yet
- Secure Hash Algorithm (Sha-256)Document22 pagesSecure Hash Algorithm (Sha-256)sri harshaphaniNo ratings yet
- Kerberos: A Private Key SystemDocument7 pagesKerberos: A Private Key SystemUmesh ThoriyaNo ratings yet
- Sms Crytography SystemDocument43 pagesSms Crytography SystemEzekiel JeremiahNo ratings yet
- 2k20 T.Y.B.com. Com. Sys. and App. 03Document2 pages2k20 T.Y.B.com. Com. Sys. and App. 03shrinath_chauhanNo ratings yet
- QXQ - YLC-Week 8 Summary of Key ConceptsDocument2 pagesQXQ - YLC-Week 8 Summary of Key ConceptsRio CarthiisNo ratings yet
- WhatsApp Chat With NickyDocument3 pagesWhatsApp Chat With Nicky08086978618danNo ratings yet
- Quizz 19Document11 pagesQuizz 19firas.chakrounNo ratings yet
- Password OOPDocument9 pagesPassword OOPYuyun JoeNo ratings yet
- Gujarat Technological University: Page 1 of 6Document6 pagesGujarat Technological University: Page 1 of 6Parshw PatelNo ratings yet
- Community Certificate PDFDocument1 pageCommunity Certificate PDFADSaksoulNo ratings yet
- 254 Cascadable and Reconfigurable Photonic Logic GatesDocument15 pages254 Cascadable and Reconfigurable Photonic Logic Gatesfsd fsdfdsNo ratings yet
- Cryptography Study PlanDocument2 pagesCryptography Study PlanAnonymous RA353CNo ratings yet
- Message Authentication and Hash FunctionsDocument26 pagesMessage Authentication and Hash FunctionsMukeshNo ratings yet
- Transport Layer Security: DescriptionDocument17 pagesTransport Layer Security: DescriptionGiuseppeBorriNo ratings yet
- Communication From Brazilian Plant Protection Organization ConsideringDocument3 pagesCommunication From Brazilian Plant Protection Organization ConsideringjulioNo ratings yet