Professional Documents
Culture Documents
Internet Attacks: - Social Engineering - Impersonation - Exploits
Internet Attacks: - Social Engineering - Impersonation - Exploits
Uploaded by
Hossein HomayooniOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Internet Attacks: - Social Engineering - Impersonation - Exploits
Internet Attacks: - Social Engineering - Impersonation - Exploits
Uploaded by
Hossein HomayooniCopyright:
Available Formats
http://www.clark.
net/pub/mjr
Internet Attacks
Types of attacks
Social engineering
Fooling the victim for fun and profit
Impersonation
Stealing access rights of authorized users
Exploits
Exploiting a hole in software or operating systems
2
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
http://www.clark.net/pub/mjr
Types of attacks
Transitive trust
(cont)
Exploiting host-host or network-network trust
Data driven
Trojans, trapdoors, viruses
Infrastructure
Taking advantage of protocol or infrastructure features or bugs
3
Types of Attacks
Denial of service
(cont)
Preventing system from being used
Magic
New things nobody has seen yet
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
http://www.clark.net/pub/mjr
Social engineering
Example #1:
Email sent to users from root to users on large academic network please change your password to fooble Attacker then logs in as user from over network System bugs exploited to gain complete run of system
5
Social engineering
Example #2:
Attacker calls switchboard and impersonates employee this is Dr. XXX trying to reach the data center. Calls data center this is Dr. XXX -- my modem is not working, has the modem pool ## changed? Gets modem pool phone ## and name of system manager from data center operator
6
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
http://www.clark.net/pub/mjr
Social engineering
(cont)
Calls computer room, this is <system manager> - Ive accidentally locked myself out of the Sun, can you do the following on the console for me?... Dials in and logs in
Social engineering
Very hard to protect against How to protect against it:
Educate staff Have well-known mechanisms for problem reporting and handling Identify transactions that must be done in person
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
http://www.clark.net/pub/mjr
Impersonation
Example #1:
User telnets into network from terminal room at a trade show Attacker with network sniffer (tcpdump, nitsniff, etc) at trade show or network captures complete login session Attacker later logs into system with user-id and stolen password
9
Impersonation
Example #2:
College students place RS-232 tap on serial lines between modem closet and computer room Late-night monitoring set up at cross-wired terminal System manager logs in and sets privilege Attacker later logs into system with stolen passwords
10
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
http://www.clark.net/pub/mjr
Impersonation
two factor authentication: something you have + something you know It is hard to steal a physical token over a network or a telephone! Applications may encrypt data to protect traffic (e.g.: encrypted TELNET sessions)
11
Exploits
Example #1:
Sendmail process runs with system privileges Mail to invalid user-id triggers bounce message return-to-sender Attacker sends a message to invalid recipient that appears to have come from a program invocation
12
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
http://www.clark.net/pub/mjr
Exploits
(cont)
Mailer dutifully bounces message to program and executes attackers commands with privileges To: fishlips@target.com From: | /bin/sed 1,/^$/d | sh
13
Exploits
Badly written software is the norm Most software has security added as an afterthought (once its too late to design it right) Too many programs run with excessive privileges Few programs take advantage of systems underlying security features
14
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
http://www.clark.net/pub/mjr
Transitive trust
Example #1:
Entire network set up with .rhosts files so that users can log in from trusted hosts w/o giving a password One user has a .rhosts file that trusts a host on a different network Attacker compromises remote network
15
Transitive trust
(cont)
Attacker scans all user command history files for invocations of the rlogin command and discovers the user who habitually accesses remote network Attacker compromises users account and now has foothold in an entirely new network Attacker island-hops from network to network
16
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
http://www.clark.net/pub/mjr
Transitive trust
Example #2:
Network of workstations share files via NFS Attacker compromises a client workstations administrator account Attacker can create privileged executables on file systems exported from server
17
Transitive trust
(cont)
Attacker creates privileged executable on server then logs in as normal user Attacker executes privileged program and gains privilege on file server
18
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
http://www.clark.net/pub/mjr
Transitive trust
Current software suites do not have adequate mechanisms for trust delegation and containment System admins must carefully map out trust relationships between hosts on networks Consider internal firewalls
19
Data driven attacks
Example #1:
Attacker mails victim user a PostScript file with file operations in it Victim displays it on workstation with a PostScript interpreter PostScript interpreter executes file operations which add attackers host to users .rhosts file Attacker logs into users account
20
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
10
http://www.clark.net/pub/mjr
Data driven attacks
Example #2:
Attacker on IRC (Internet Relay Chat) tells newbie users to obtain a utility program that will help them use system better Users download program and run it Program deletes all users files and emails a copy of password file to attacker
21
Web Pages wed like to see:
Click ClickHere Here to to Infect InfectYour YourMachine Machine
22
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
11
http://www.clark.net/pub/mjr
Data driven attacks
Firewall can help screen out some Restricting services can help reduce potential for attack Educate users about not just executing anything they are given
23
Infrastructure attacks
Example #1: (DNS Spoofing)
Attacker compromises a system that is name server for a network Victim has a host called foo.victimdomain.com in their .rhosts file Attacker sets up a name mapping from the address of one of his systems to foo.victimdomain.com Attacker uses rlogin to gain access
24
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
12
http://www.clark.net/pub/mjr
DNS spoofing
When building a system do not rely on DNS for making security critical decisions Programs like tcp_wrappers do double reverse lookup which makes it harder to mount attack Most firewalls use DNS information only for routing mail and user services
25
Infrastructure attacks
Example #2: (ICMP bombing)
ICMP (Internet Control Message Protocol) is used by routers to notify a host when a destination is unreachable Attacker can knock a machine off the air by sending ICMP to target system telling it that a destination is not available Tools for this are widely available (e.g.: nuke icmpbomb)
26
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
13
http://www.clark.net/pub/mjr
ICMP bombing
Most firewalls block ICMP into and out of network Firewalls that are a single point of connectivity correctly interpret ICMP without letting it through Unfortunately ICMP is also used to legitimate purposes (e.g., ping - ICMP echo request)
27
Infrastructure attacks
Example #3: (Source Routing)
IP protocol specifies that source-routed traffic should return on the reverse route from which it came Attacker selects a trusted host within the target network and knocks it off the air using ICMP bombing Attacker sets address of his system to that of the trusted host
28
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
14
http://www.clark.net/pub/mjr
Infrastructure attacks
(cont)
Attacker uses rlogin or TELNET with source routed packets Target host sees packets coming from trusted machine and may permit better access
29
Source Routing
Attacker on Internet 2: attacker sends traffic as trusted host Target
3: return traffic follows source route
Target Network Trusted host
1: attacker zaps trusted host
30
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
15
http://www.clark.net/pub/mjr
Source Routing
Defeat source routing with firewalls that block and log source routed packets Many routers can block source routed packets Tools like tcp_wrappers detect sourcerouted traffic and trigger alarms
31
Infrastructure attacks
Example #4: (TCP sequence guessing or the Mitnick Attack)
TCP connections rely on an increasing sequence number to correctly order traffic over connection When connection is created, a new semirandom sequence number is used
32
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
16
http://www.clark.net/pub/mjr
Infrastructure attacks
(cont)
If an attacker knows the sequence numbers of a connection stream he can generate correct-looking packets even though the response packets do not reach him In order for attack to work response packets must not reach the correct destination
33
Sample TCP Session
Host A
SYN (initia
Host B
l sequence
# =x) ence # =y)
(i SYN, ACK ACK
nitial sequ
ACK
34
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
17
http://www.clark.net/pub/mjr
TCP Sequence guessing
Phase #1:
Victim is behind a router-based firewall that allows through all traffic originating from victim network Router firewall also permits incoming traffic on SMTP service port to target network Attacker gags trusted host by initiating a number of partial TCP connection requests
35
Sequence guessing: phase #1
Attacker on Internet Router 1.1: attacker masks off trusted host with a sequence of half-open connection requests Target
Target Network Trusted host
36
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
18
http://www.clark.net/pub/mjr
TCP sequence guessing
Phase #2:
Attacker generates a number of connection attempts against target systems SMTP port from an outside machine Attacker notes down sequence numbers of the connections as they are created
37
Sequence guessing: phase #2
Attacker on Internet Router 2.1: attacker makes connection requests and notes down sequence numbers Target Network Trusted host Target
38
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
19
http://www.clark.net/pub/mjr
TCP sequence guessing
Phase #3:
Attacker computes sequence numbers that will be assigned to next connection Attacker generates packets from outside machine with source address of inside trusted machine Generated packets have correct sequence numbers for client side of dialog
39
TCP sequence guessing
(cont)
Target machine thinks it has received an rsh command from trusted inside machine and executes it, adding a line to the password file
40
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
20
http://www.clark.net/pub/mjr
Sequence guessing: phase #3
Attacker on Internet Router 3.1: attacker creates traffic with correct sequence number appearing to originate from trusted host 3.2: router permits traffic because it appears to have originated on target network 3.3: target system executes command because it appears from trusted host
41
Target
appears from trusted host Target Network Trusted host
TCP sequence guessing
Most dual-homed firewalls immune to sequencing since they block all traffic to inside network
Impossible to jam nodes on inside
Correctly configured routers can prevent sequence guessing
Router should not let in traffic claiming to come from inside
42
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
21
http://www.clark.net/pub/mjr
Infrastructure attacks
Example #5: (TCP splicing)
Attacker between networks watches for a legitimate connection Waits until after user has logged in Steals connection and becomes user
Negates protections provided by authentication tokens!
43
TCP splicing
Phase #1:
Attacker between networks identifies a connection to steal Monitors connection until user has logged in Starts recording packet sequence numbers
44
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
22
http://www.clark.net/pub/mjr
TCP splicing: phase #1
Users destination User host
Attacker between networks 1.1: user logs into destination across network 1.2: attacker observes login and records packet sequence numbers
45
TCP splicing
Phase #2:
Attacker jams users machine Users machine closes connection unilaterally User sees his login disconnected
46
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
23
http://www.clark.net/pub/mjr
TCP splicing: phase #2
Users destination User host
Attacker between networks 2.1: attacker jams users machine 2.2: user sees login session hang or die
47
TCP splicing
Phase #3:
Attacker resumes sending packets with correct sequence numbers Remote system does not realize anything has happened and keeps communicating with attacker
48
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
24
http://www.clark.net/pub/mjr
TCP splicing: phase #3
Users destination User host
Attacker between networks 3.1: attacker generates correctly sequenced packets appearing to come from users machine 3.2: users destination keeps sending return packets to users machine which does not see them because it is jammed 3.3: attacker keeps monitoring traffic on stolen session
49
TCP splicing
Application level encryption is effective solution since attacker cannot generate traffic that will decrypt to meaningful data This attack has not been widely seen yet
50
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
25
http://www.clark.net/pub/mjr
Infrastructure attacks
Example #6: (FTP bouncing)
Attacker locates a trusted system that is running an FTP server with upload capability Uploads a file of commands or data Bounces the download to a different system for delivery
This may work through some firewalls!
51
FTP Bouncing
Phase #1:
Attacker locates an FTP server behind a firewall FTP server has a writeable upload area Attacker generates (in this example) an SMTP dialog of a spoofed mail message Attacker uploads the message
52
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
26
http://www.clark.net/pub/mjr
FTP Bouncing: phase #1
Attacker on Internet Router 1.1: attacker identifies an FTP server with writeable upload area
HELO mumble.com MAIL From: president@whitehouse.gov RCPT To: victim DATA Joe, you ignorant splut. Signed, Bill. . QUIT
Target
Target Network FTP Server
1.2: attacker generates an SMTP dialog file and uploads it to the FTP server
53
FTP Bouncing
Phase #2:
Attacker FTPs to the FTP server and sends a PORT command
PORTs IP address is that of the victim system PORTs IP port is the SMTP port
FTP server opens connection to victim system and informs attacker OK
54
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
27
http://www.clark.net/pub/mjr
FTP Bouncing: phase #2
Attacker on Internet Router 2.1: attacker issues a PORT command with the targets address and SMTP port: PORT 16,67,32,1,9,25 2.2: FTP server opens connection to target machine port 25 and informs attacker OK FTP Server Target
55
FTP Bouncing
Phase #3:
Attacker sends a RETR command specifying the data file containing the SMTP dialog FTP server dutifully transmits the file to the previously opened port
Fake Email is sent Email appears to originate on FTP server FTP server logs may not reveal the attack
56
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
28
http://www.clark.net/pub/mjr
FTP Bouncing: phase #3
Attacker on Internet Router 3.1: attacker issues a RETR command filename of SMTP commands uploaded earlier
HELO mumble.com MAIL From: president@whitehouse.gov RCPT To: victim DATA Joe, you ignorant splut. Signed, Bill. . QUIT
Target
3.2: FTP server transmits the file to the target machine, thereby sending a mail message
FTP Server
57
FTP Bouncing
FTP bouncing makes address-based verification difficult
FTP servers may now provide launching points for attack Many Windows/PC based FTP servers can easily be used to issue bounce attacks
Implication: Externally reachable FTP servers must be carefully managed!
58
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
29
http://www.clark.net/pub/mjr
Infrastructure attacks
Example #7: (Racing Authentication)
Authentication systems that rely on a unidirectional dialog may be spoofed by an attacker Attack is based on typing faster than the victim and guessing the last digits/letters of passwords
Defeats many tokens and one-time password schemes
59
Racing Authentication
Phase #1:
Attacker is in a position to sniff user logging in with SecurID, S/Key or similar authentication token Watches user input keystrokes one at a time, duplicating them in a duplicate login attempt
60
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
30
http://www.clark.net/pub/mjr
Racing Auth: phase #1
Users destination User host Login: mjr Password: 1234.. Login: mjr Password: 1234.. Attacker sniffing traffic 1.1: user starts to log in with SecurID 1.2: attacker mirrors users login attempt 1.3: user starts to enter SecurID keycode
61
Racing Authentication
Phase #2:
Attacker waits until user is ready to enter the final digit of their SecurID code Attacker takes a guess and picks a number and enters it first Odds are 1 in 10 that a successful login will be granted to attacker Normal user thinks he just made a typo
62
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
31
http://www.clark.net/pub/mjr
Racing Auth: phase #2
Users destination User host Login: mjr Password: 1234.. ..user is about to type 4 Attacker sniffing traffic
Login: mjr Password: 1234.. attacker guesses and types 4 first!
2.1: attacker waits until user enters second to last digit 2.2: attacker guesses last digit and enters it before user does
One time in 10 attacker gets in!
63
Racing Authentication
Racing authentication does not work on challenge/response or signature based authentication systems Can also be prevented by authentication servers that do not allow a user to be in the process of logging in from more than one terminal simultaneously
64
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
32
http://www.clark.net/pub/mjr
Denial of service attacks
Example #1:
Attacker ICMP bombs router off the network or Attacker ICMP bombs router at service provider off the network
65
Denial of service attacks
Example #2:
Attacker floods network link with garbage packets or Attacker floods mail hub with junk mail
66
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
33
http://www.clark.net/pub/mjr
SYN Flooding
Deny legitimate users service by jamming the target machine with halfopen TCP sessions
Eventually connections may get through but it disrupts service and causes long timeouts Many hacker tools for SYN flooding are now on the net
67
SYN flooding a TCP Session
Host A
SYN (initia l sequence # =x) from bogu s address nitial sequ ence # =y)
Host B
(i SYN, ACK
Attacker never sends rest of connection completion, filling victims queue request connection Legitimate h g u get thro may never
68
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
34
http://www.clark.net/pub/mjr
Syn Flooding
1: attacker issues a flood of SYN packets and ignores responses Attacker on Internet
Target Network 2: legitimate users connection may not get through
www.victim.com
?
69
SYN Flooding
Most responses to SYN flooding are quick and dirty fixes
Increase buffer and queue sizes Generate automatic RST packets to clear jamming
SYN flooding type attacks will always be technically feasible
70
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
35
http://www.clark.net/pub/mjr
Denial of service attacks
Few things network administrator can do to protect against it
Attacker can always attack upstream of point of connection and interrupt service
Internet protocols are designed to withstand single points of failure
Cannot handle active attackers on network that introduce multiple failures
71
Magic attacks
We dont know what these will look like Theyre the attack that someone hasnt thought of yet Attack will be utterly mysterious in origin and will surprise everyone Hopefully it will be easy to fix
72
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
36
http://www.clark.net/pub/mjr
What does the future hold?
Host-based software will continue to be buggy and unreliable from a security standpoint Vendors will continue to add security as an afterthought rather than designing it in from the beginning Encryption will be more widely deployed in spite of government restrictions
73
Summary
Attackers are performing active R&D to figure out how to break into networks Some attacks very technical Some attacks very low tech
74
(C)Copyright, 1997, Marcus J. Ranum. All rights reserved.
37
You might also like
- DMDave Adventure - The Vault of Terror - 13th-LevelDocument13 pagesDMDave Adventure - The Vault of Terror - 13th-LevelJason Bryant50% (2)
- Hacking ExposedDocument202 pagesHacking Exposedبوبيسكو كالينNo ratings yet
- Threats and AttacksDocument21 pagesThreats and AttacksMichaelaNo ratings yet
- DFS40083 - Chapter3 - Network Attacks & Protecting The NetworkDocument74 pagesDFS40083 - Chapter3 - Network Attacks & Protecting The NetworkF2066 MUHAMMAD JOSHWAN BIN MUHD IRWAN JOHNSONNo ratings yet
- Security Networking BasicsDocument46 pagesSecurity Networking Basicsrodriguez.fonte.felipeNo ratings yet
- Silberschatz and Galvin: SecurityDocument16 pagesSilberschatz and Galvin: SecurityFyruz FyFiveNo ratings yet
- Network SecurityDocument58 pagesNetwork SecurityahkowNo ratings yet
- Why Computer Security: - The Past Decade Has Seen An Explosion in The Concern For The Security of InformationDocument93 pagesWhy Computer Security: - The Past Decade Has Seen An Explosion in The Concern For The Security of Informationshabir AhmadNo ratings yet
- 4.2 Network Issues and CommunicationDocument29 pages4.2 Network Issues and CommunicationAryan Khan RobloxNo ratings yet
- Module 01 - CryptographyDocument92 pagesModule 01 - CryptographyMarco CarabuenaNo ratings yet
- Ethic Unit 2Document66 pagesEthic Unit 2Mahtab AnsariNo ratings yet
- Lecture 1Document37 pagesLecture 1melakmubettyNo ratings yet
- BIS 321 Chapter One Part TwoDocument23 pagesBIS 321 Chapter One Part TwoEyob TemesgenNo ratings yet
- 4.2 Network Issues and Communication PDFDocument29 pages4.2 Network Issues and Communication PDFJane ChangNo ratings yet
- Module 4: The Problems: Cyber AntipatternsDocument12 pagesModule 4: The Problems: Cyber Antipatternsshreya n patelNo ratings yet
- Lecture 2Document50 pagesLecture 2Jasbindar SinghNo ratings yet
- Network Security 4Document8 pagesNetwork Security 4rajipharmacy085055No ratings yet
- Ethical Hacking GE4Document23 pagesEthical Hacking GE4muna cliffNo ratings yet
- Network Security - Part 1 企業網絡安全威脅: Enterprise Networks Security ThreatsDocument50 pagesNetwork Security - Part 1 企業網絡安全威脅: Enterprise Networks Security Threatstmx173No ratings yet
- 08 TheoryOfComputation VirusesDocument77 pages08 TheoryOfComputation Viruseskitaabisaaa407No ratings yet
- MIS Ethics Privacy and SecurityDocument5 pagesMIS Ethics Privacy and Securityanon_461820450No ratings yet
- Week3 TutorialDocument21 pagesWeek3 Tutorialnathalieedith20No ratings yet
- Chapter Four CSDocument74 pagesChapter Four CSAschalew AyeleNo ratings yet
- Cyber Security in Power Systems: Matus KormanDocument31 pagesCyber Security in Power Systems: Matus KormanrajimuruganNo ratings yet
- IT ThreatsDocument53 pagesIT ThreatsDiana RoșcaNo ratings yet
- Computer Security: Hackers and Viruses: Theory of Computation Mesfer Alrizq Naif AlrashidiDocument83 pagesComputer Security: Hackers and Viruses: Theory of Computation Mesfer Alrizq Naif AlrashidiGhanshyam SharmaNo ratings yet
- Information Security IssuesDocument24 pagesInformation Security IssueshabteNo ratings yet
- Week6 KillChainDocument17 pagesWeek6 KillChainFrozoneNo ratings yet
- Ethical Hacking Basics: CE33201 Eka Stephani SinambelaDocument26 pagesEthical Hacking Basics: CE33201 Eka Stephani Sinambelayenni juliana sibaraniNo ratings yet
- Slides Training DeceptionIsFreeDocument77 pagesSlides Training DeceptionIsFreeEd NjorogeNo ratings yet
- Cyber Security NotesDocument22 pagesCyber Security NotesJayita GhoraiNo ratings yet
- External Threats Internal ThreatsDocument31 pagesExternal Threats Internal ThreatsVishal AvhadNo ratings yet
- Cybersecurity Challenges and Opportunities: Edward B. TalbotDocument26 pagesCybersecurity Challenges and Opportunities: Edward B. TalbotabcdeNo ratings yet
- Chapter 7 - Part 2 - Network Security Control1Document20 pagesChapter 7 - Part 2 - Network Security Control1priyankaNo ratings yet
- Security: Concept, Threats (User, Data), MeasuresDocument23 pagesSecurity: Concept, Threats (User, Data), Measurespariyal malikNo ratings yet
- Cyber SecurityDocument13 pagesCyber SecurityVinay BharwaniNo ratings yet
- 4.2 Network Issues and CommunicationDocument29 pages4.2 Network Issues and CommunicationMohd RafeeqNo ratings yet
- Cyber Attacks & Hacking: S. R. ShindeDocument70 pagesCyber Attacks & Hacking: S. R. ShindeAkshay GadeNo ratings yet
- Study On Modbus/DNP3 Protocol: Topics CoveredDocument9 pagesStudy On Modbus/DNP3 Protocol: Topics CoveredMandeep SinghNo ratings yet
- 30 Ethical HackingDocument19 pages30 Ethical HackingPraveen MandalNo ratings yet
- What Is Security?: Some Differences Between Traditional Security and Information SecurityDocument8 pagesWhat Is Security?: Some Differences Between Traditional Security and Information SecurityShweta DishwarNo ratings yet
- Honeypots & Honeynets: Tech TalkDocument16 pagesHoneypots & Honeynets: Tech Talkthaidt229No ratings yet
- Computer Security CyberDocument28 pagesComputer Security Cyberkena wendimuNo ratings yet
- Threats, Risk Ge4Document20 pagesThreats, Risk Ge4kassahunNo ratings yet
- Cryptography, Network Security and Cyber Laws Notes 2019-2020Document23 pagesCryptography, Network Security and Cyber Laws Notes 2019-2020Himanshu KumarNo ratings yet
- Threats and Attacks: CSE 4471: Information Security Instructor: Adam C. Champion, PH.DDocument26 pagesThreats and Attacks: CSE 4471: Information Security Instructor: Adam C. Champion, PH.Dswapnil RawatNo ratings yet
- CH2 CS LectureDocument68 pagesCH2 CS LecturepyramidmistreNo ratings yet
- Hacking 1Document65 pagesHacking 1MATHESWARAN PNo ratings yet
- IS Module 1Document19 pagesIS Module 1smit.maldeNo ratings yet
- Lecture 2Document31 pagesLecture 2melakmubettyNo ratings yet
- Class 1Document41 pagesClass 1Shorif Uddin Al MahamudNo ratings yet
- CS2p NeedForSecurityDocument83 pagesCS2p NeedForSecurityjoshuaNo ratings yet
- CS NotesDocument36 pagesCS NotesJ2XNo ratings yet
- COSC 6301 - Computer Security Threats - and - VulnerabilitiesDocument52 pagesCOSC 6301 - Computer Security Threats - and - VulnerabilitiesmailtosiscoNo ratings yet
- Chapter 5Document4 pagesChapter 5Khánh LyNo ratings yet
- Management Information System: Unit-7: Management Challenges - Security, Ethical and Societal ChallengesDocument40 pagesManagement Information System: Unit-7: Management Challenges - Security, Ethical and Societal ChallengesVidhi MaheshwariNo ratings yet
- NS 1Document96 pagesNS 1elitejoker622No ratings yet
- Cloud SecurityDocument15 pagesCloud Securityishugupta0298No ratings yet
- Penetration Testing: A Roadmap To Network SecurityDocument4 pagesPenetration Testing: A Roadmap To Network SecurityYoni sudarmanNo ratings yet
- TUTANESCU I-Anatomy and Types of Attacks Against Computer .Document6 pagesTUTANESCU I-Anatomy and Types of Attacks Against Computer .Jalal BhayoNo ratings yet
- Cyberphobia: Identity, Trust, Security and the InternetFrom EverandCyberphobia: Identity, Trust, Security and the InternetRating: 3.5 out of 5 stars3.5/5 (9)
- 2 - SNG Group Equip & ServicesDocument16 pages2 - SNG Group Equip & Servicesadeelsiddiquepso100% (1)
- Honda Lawn GardenDocument24 pagesHonda Lawn GardenRaza Tanweer100% (1)
- Diode Familiarization Experiment 1Document5 pagesDiode Familiarization Experiment 1Ramon Chito S. PudelananNo ratings yet
- ADSO Scenario in SAP BW HANADocument29 pagesADSO Scenario in SAP BW HANAJH Consulting Solutions100% (2)
- Square Hollow Sections-Cold Formed..BS en 102191997Document4 pagesSquare Hollow Sections-Cold Formed..BS en 102191997Jagdish ChhuganiNo ratings yet
- TS PGECET Environmental Management Syllabus & Exam PatternDocument1 pageTS PGECET Environmental Management Syllabus & Exam PatternpavaniNo ratings yet
- 02 - 05 - Carbide ToolsDocument21 pages02 - 05 - Carbide ToolsEscuela EntrenamientoNo ratings yet
- 2.lab Techniques (Repaired) PDFDocument52 pages2.lab Techniques (Repaired) PDFSomu Yashawant ChaudhariNo ratings yet
- Leister Process Heat Ba Css Easy Css KSR Digital enDocument12 pagesLeister Process Heat Ba Css Easy Css KSR Digital enfourat.zarkounaNo ratings yet
- Steel Windows and Door Frames CatalogueDocument59 pagesSteel Windows and Door Frames CatalogueburimNo ratings yet
- Ersa DIGITAL 2000 A: Lötstation/Soldering StationDocument34 pagesErsa DIGITAL 2000 A: Lötstation/Soldering StationFlorinNo ratings yet
- Petri Nets Refesher: Prof - Dr.ir. Wil Van Der AalstDocument159 pagesPetri Nets Refesher: Prof - Dr.ir. Wil Van Der AalstMariana TanasaNo ratings yet
- Contor SiemensDocument4 pagesContor SiemensVasile CiupituNo ratings yet
- As 2350.7-2006 Methods of Testing Portland Blended and Masonry Cements Determination of Temperature Rise DuriDocument2 pagesAs 2350.7-2006 Methods of Testing Portland Blended and Masonry Cements Determination of Temperature Rise DuriSAI Global - APACNo ratings yet
- 7036 Handheld Engine Oil Pump: Materials: Suitable For: Document RefDocument2 pages7036 Handheld Engine Oil Pump: Materials: Suitable For: Document RefAntonioNo ratings yet
- Silo Fluidizer Mini Disk: Mini Fluidizing Disk Keeps Material Moving in Tight CurvaturesDocument2 pagesSilo Fluidizer Mini Disk: Mini Fluidizing Disk Keeps Material Moving in Tight Curvaturesseeralan_1986No ratings yet
- SadfsdafDocument5 pagesSadfsdafAjeet RajpootNo ratings yet
- Architectural Design-I (150101) : ITM UniversityDocument6 pagesArchitectural Design-I (150101) : ITM Universityanon_891354001No ratings yet
- Pulsar NS160 Single Disc & Twin Disc BSIV - SPCDocument85 pagesPulsar NS160 Single Disc & Twin Disc BSIV - SPCErik R. AraúzNo ratings yet
- Scan 3VWDJ2164EM052486 20190718 1932 54410km 33808miDocument7 pagesScan 3VWDJ2164EM052486 20190718 1932 54410km 33808miWiltney BugdanovizNo ratings yet
- Fortinet Fortigate 60Document2 pagesFortinet Fortigate 60Davor Mendizabal TapiaNo ratings yet
- ASVAB Mechanical Comprehension Practice Test 4Document8 pagesASVAB Mechanical Comprehension Practice Test 4ASVABTestBankNo ratings yet
- ECE 321 Experiment 7 NMOS and PMOS Transistor CircuitsDocument11 pagesECE 321 Experiment 7 NMOS and PMOS Transistor CircuitsgrantdheilemanNo ratings yet
- Advanced Compression WP 12c 1896128 PDFDocument18 pagesAdvanced Compression WP 12c 1896128 PDFBubuNo ratings yet
- CADAM Revised SyllabusDocument2 pagesCADAM Revised SyllabusSreejith S NairNo ratings yet
- Cut Out Fuse: Technology With Better Cost / Benefit!Document8 pagesCut Out Fuse: Technology With Better Cost / Benefit!cilok nangkaNo ratings yet
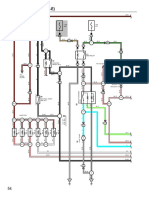
- 1990 ECM WiringDocument8 pages1990 ECM WiringHenry Garro MoraNo ratings yet
- TDS Acronal 7079 PDFDocument3 pagesTDS Acronal 7079 PDFWahid Karol100% (1)
- Critical Imaging Recon IR 100-500 Data SheetDocument2 pagesCritical Imaging Recon IR 100-500 Data SheetSandra CollinsNo ratings yet