Professional Documents
Culture Documents
Windows Server 2008 Active Directory Components
Windows Server 2008 Active Directory Components
Uploaded by
shogun7333Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Windows Server 2008 Active Directory Components
Windows Server 2008 Active Directory Components
Uploaded by
shogun7333Copyright:
Available Formats
Acronyms
ACL Access Control List AD Active Directory AD DB Active Directory Database AD DS Active Directory Domain Services AD FS Active Directory Federation Services AD LDS Active Directory Lightweight Directory Services AD RMS Active Directory Rights Management Services CLC Client Licensor Certificate DA Domain Administrator DFS-R Distributed File System Replication DMZ Demilitarized Zone FQDN Fully Qualified Domain Name FRS File Replication Service FS Federation Server FS-A Account Federation Server FS-R Resource Federation Server FSP Federation Server Proxy GNZ GlobalNames Zone GPO Group Policy Object GPOE Group Policy Object Editor GPMC Group Policy Management Console GUID Globally Unique Identifier IIS Internet Information Services IE Internet Explorer IFM Install from Media KDC Key Distribution Center LDAP Lightweight Directory Access Protocol LOB Applications Line of Business Applications MLGPO Multiple Local Group Policy Objects MMC Microsoft Management Console NLA Network Location Awareness OU Organizational Unit RAC Rights Account Certificate RMS Rights Management Services RODC Read-Only Domain Controller SSO Single Sign-on SAML Security Assertion Markup Language SYSVOL System Volume WS Web Server XML Extensible Markup Language XrML Extensible Rights Markup Language
Legend
Product Scenario: Enterprise and Branch Office
Active Directory Lightweight Directory Services
Active Directory Lightweight Directory Services (AD LDS) provides directory services for directory-enabled applications. AD LDS does not require or rely on Active Directory domains or forests. AD LDS was previously known as Active Directory Application Mode (ADAM).
Product Scenario: Security and Policy Enforcement
Active Directory Federation Services
Active Directory Federation Services (AD FS) provides Web single sign-on (SSO) technologies to authenticate a user to multiple Web applications over the life of a single online session. AD FS securely shares digital identity and entitlement rights, or "claims," across security and enterprise boundaries.
Active Directory Rights Management Services
Product Scenario: Security and Policy Enforcement
Active Directory Rights Management Services (AD RMS) is information protection technology that works with AD RMS-enabled applications to safeguard digital information from unauthorized use both online and offline inside and outside of your organizations firewall.
Information Important
AD LDS Usage Scenarios
Application-Specific Directory Services Scenarios Application Development Scenarios Extranet Access Management X.500/LDAP Directory Migration Scenarios Deployment in Datacenters & Perimeter Networks (Branch Offices, DMZs)
AD LDS
AD LDS Users and Groups
AD LDS authenticates the identity of users, who are represented by AD LDS user objects AD LDS allows the use of Windows Security principals from the local machine and AD for access control. Authentication process for these user principals is redirected to the local machine and AD respectively Four default groups: Administrators, Instances, Readers, and Users
ADSchemaAnalyzer Helps migrate the AD schema to AD LDS, from one AD LDS instance to another, or from any LDAP-compliant directory to an AD LDS instance Active Directory to AD LDS Synchronizer Command-line tool that synchronizes data from an AD forest to a configuration set of an AD LDS instance Snapshot Browser Uses LDAP client to bind to VSS snapshot (taken by NTDSUTIL) and view read-only instance of AD LDS database Active Directory Sites and Services Assists in administrating AD LDS replication topology Install from Media (IFM) IFM can also be used to install an AD LDS instance from backup media
AD LDS Tools
Federation Scenarios
Federated Web SSO with Forest Trust Users must authenticate only once to access multiple WebForests located in the DMZ and internal network. A federation based applications. All users are external, and no federation trust is established so accounts in internal forest can access trust exists. Web-based applications in perimeter network (including intranet or Internet access). FS-A/-R AD Internet Forest Trust AD or FS-R AD LDS
Federation Trust
FS-A Client Intranet DMZ AD FSP WS Internet Client WS DMZ Client
Web SSO
Federated Web SSO
Federation trust relationship established between two businesses. FS routes authentication requests from user accounts in adatum to Webbased applications that are located in the treyresearch network. FS-A AD Client FSP-A Internet WS Client Federation Trust DMZ Client treyresearch (online retailer) FS-R AD (Separate SQL server or, for small configurations, SQL on AD RMS server)
AD DC SQL Server
Information Bullet
User
Authenticates users of AD RMS Group expansion for AD RMS Stores AD RMS Service Discovery Location
adatum DMZ Intranet Forest
Configuration Database stores: Data needed to manage account certification, licensing & publishing Primary key pairs for secure rights management
Windows Server 2008 delivers a fully integrated federated enterprise rights management solution. This integration combines Active Directory Federation Services (AD FS) and Active Directory Rights Management Services (AD RMS) to extend AD RMS to external users.
License AD RMS-protected content Enroll servers and users Administer AD RMS functions Software-based key protection is the default for AD RMS. For added protection, AD RMS can store its keys in a hardware security module.
User Groups
Service Account
AD LDS Platform Support
AD LDS is a Windows Server 2008 role
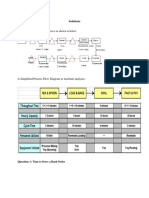
AD FS Authentication Flow
Federation Trust
Extend AD to access resources offered by partners across the Internet
AD RMS Server 7
treyresearch.net (Resource Forest) 8 Federation Server
7 3 2
Federation may also have a client proxy for token requests. Provides UI for browser clients. Web Server Enforce user authentication Create application authorization context from claims
Requires IIS 6.0 or greater Root Certification Server Provides certificates to AD RMS-enabled clients
Client(s)
User Tokens
AD LDS Access Control
AD LDS Replication Replication Overview
AD LDS instances replicate data based on participation in a configuration set
Uses ACLs on directory objects to determine which objects user can access
adatum.com (Account Forest)
Federation Server
Requires IIS V6 or greater
Configuration Set 1
Computer 1 AD LDS Instance Configuration Partition 1 Schema 1 App Partition 1 App Partition 2 Computer 2 AD LDS Instance Configuration Partition 1 Schema 1 App Partition 1 App Partition 2 NOT Hosted
5 Generate token-based
authentication data A configuration set is a group of AD LDS instances that replicate data with each other A single server machine can run multiple AD LDS instances One AD LDS instance can belong to just one configuration set AD DS / AD LDS Authenticate users Map attributes Federation Server Issue tokens Map attribute to claims Manage Trust Policy
Requires IIS 6.0 or greater
Generate token based upon policies in federation server
AD RMS-enabled client installed AD RMS-enabled applications. For example: IE, Office 2003/ 2007, Office SharePoint Server 2007.
3 1
AD RMS is included in Windows Server 2008 as a server role
User Application Wizard
User Credentials Cache
9 5
Active Microsoft Directory Office Outlook User Object
4 Information Author Information Recipient
6 4
Internal Client
10
AD RMS-Protected Content (XrML) (contains usage rules) Each consumer of content receives unique license that enforces rules
The AD LDS instances in a configuration set can host all or a subset of the applications partitions in the configuration set AD LDS replication and schedule is independent from Active Directory
Configuration Set 2
Replication Computer 3 AD LDS Instance Configuration Partition 2 Schema 2 AD LDS Instance Configuration Partition 2 Schema 2 App Partition 3 Not Hosted App Partition 4
1 Author uses AD RMS for the first time - receives Rights Account Certificate (RAC) and Client Licensor Certificate (CLC). Happens once and enables user to publish online or offline and consume rights-protected content. 2 Using AD RMS-enabled application, author creates file and specifies user rights. Policy license containing user policies is generated. 3 Application generates content key, encrypts content with it. Online Publish - Encrypts content key with AD RMS server public key and sends to AD RMS server. Server creates and signs publishing license (PL). Offline Publish - Encrypts content key with CLC public key, encrypts copy of key with AD RMS server public key. Creates PL and signs with CLC private key. Append PL to encrypted content. 4 AD RMS-protected content file sent to Information Recipient. AD RMS-protected content may also be represented by e-mail. 5 Recipient receives file, opens using AD RMS-enabled application or browser. If no account certificate on the current computer, the AD RMS server will issue one (AD RMS document notifies application of the AD RMS server URL). 6 Application sends request for use license to AD RMS server that issued publishing license (if file published offline, send to server that issued the CLC). Request includes RAC and PL for file. 7 AD RMS server confirms recipient is authorized, checks for a named user, and creates use license for the user. Server decrypts content key using private key of server and re-encrypts content key with public key of recipient, then adds encrypted session key to the use license. This means only the intended recipient can access the file. 8 AD RMS server sends use license to information recipients computer. 9 Application examines both the license and the recipients account certificate to determine whether any certificate in either chain of trust requires a revocation list. User granted access as specified by information author.
AD LDS Computer 1 Directory Clients Using Applications
1 Client tries to access Web application in treyresearch.net. Web server requests token for access. 2 Client redirect to Federation Server on treyresearch.net. Federation server has list of partners that have access to the Web application. Refers client to its
adatum.com Federation Server.
Computer Password Credentials Replication Policy Cache
3 Instruct client to get a token from adatum.com Federation Server. 4 Client is member of its domain. Presents user authentication data to adatum.com Federation Server. 5 Based on authentication data, SAML token generated for the client. 6 User obtains SAML token from adatum.com Federation Server for treyresearch.net Federation Server. 7 Redirects client to treyresearch.net Federation Server for claims management. 8 Based on policies for the claims presented by the adatum.com token, a treyresearch.net token for the Web application is generated for the client. Security tokens assert claims Claims Statements authorities make about security principals (e.g., name, identity, key, group, privilege, capability)
App Partition 3 App Partition 4
Directory-enabled Application 3 Directory-enabled Application 4
Central Store Group Policy
AD LDS Computer 2
AD LDS Computer 3
9 The treyresearch.net token is delivered to client.
10 Client can now present treyresearch.net token to Web server to gain access to the application.
Firewall
Active Directory Forest
Product Scenario: Server Management
Group Policy
Active Directory Management
Product Scenario: Server Management
Active Directory Domain Services (AD DS) expands auditing capabilities to track changes in the Active Directory objects. Windows Server 2008 has password policy that removes the restriction of a single password policy per domain. AD DS has the capability to stop and restart the Active Directory Service.
Active Directory Read-Only Domain Controller
Product Scenario: Enterprise and Branch Office
A Read-Only Domain Controller (RODC) allows organizations to easily deploy a DC in locations where physical security cannot be guaranteed. RODC hosts a read-only replica of the database in Active Directory Domain Services (AD DS) for any given domain.
Replication Mechanism
Internet
Group Policy delivers and applies configuration or policy settings to targeted users and computers within an Active Directory environment. Windows Server 2008 supports a Central Store for centralized XML-based template storage, advanced logging, and enhanced Group Policy delivery and enforcement using Network Location Awareness.
RMS Protected Content
Restartable DS
Central Storage for Administrative Templates
Group Policy Central Store
Group Policy Delivery & Enforcement
Workstation / Member Server Delivery
Workstation / Member Server Startup Processed every 90-120 minutes (randomized) Refreshes on NLA notifications (Windows Vista and Windows Server 2008)
Policies + [GUID]
1) Create Central Store on PDC Emulator 2) Central Store created for each domain 3) If Central Store available when administering domainbased GPOs, the central store is used by default (ADMX/ADML available for use with Windows Vista/ Windows Server 2008)
GlobalNames Zone
Resolution of single-label, static, global names for servers using DNS.
Fine-grained password policy removes the restriction of a single password policy per domain.
Set Attributes on PasswordSettings Object: Precedence Password Settings Account Lockout Settings Distinguished Name of Users and/or Groups the settings apply to Requires Windows Server 2008 Domain Mode If multiple policies applied, then lower number precedence wins! Only one set of Password Settings can apply to a user Password Settings Object applied to a user wins above settings applied to a group
RODC GC support for Outlook clients
Except for account passwords, an RODC holds all the AD DS objects and attributes that a writable DC holds. By default, no user/computer passwords are stored on an RODC. RODC performs normal inbound replication for AD DS and DFS changes Read-Only Partial Attribute Set Prevent replication of sensitive information. Requires manual configuration.
RODC
Server/Client Tools
Fine-Grained Password Policies
Advantages of Central Store include reduced SYSVOL size and reduced traffic between DCs
+ ADM
All authoritative DNS servers for a domain must be running Windows Server 2008 to provide GlobalNames support for clients Implemented as a Regular Forward Lookup zone, which must be named GlobalNames GlobalNames zone should be Active Directory integrated and replicated forest-wide The GlobalNames zone is manually configured with CNAME records to redirect from servers host name to Fully Qualified Domain Name Complex Single-forest or Multiple-forest deployments require additional DNS configuration for GlobalNames zone functionality GlobalNames Zone Intranet CNAME server.east.contoso.com east.contoso.com Zone Server A 172.20.1.1 DNS server authoritative for east.contoso.com Authoritative DNS servers, which also have a copy of the GNZ, will first check the GNZ for data to respond
Branch Office
3
Password Replication Policy
AD LDS Server
AD LDS Instance
+ PolicyDefinitions
PolicyDefinitions folder stores all .admx files .adml files stored in language-specific + en-US All folders. For example, en-US for US English
ADMX/ADML replaces ADM files. ADMX and ADML files take advantage of an XML-based format
Hub Site Writable DCs
Writable DC verifies request is coming Password from an RODC and consults Password Replication Replication Policy for RODC
Policy
User Delivery
At user logon Processed approximately every 90-120 minutes (randomized)
SYSVOL
msDS-PasswordSettings Object(s)
Domain Controller Delivery
Domain Controller Startup Processed approximately every 5 minutes
Using Network Location Awareness, Group Policy has access to resource detection and event notification capabilities in the operating system. This allows Group Policy to refresh after detecting the following events: Recovery from hibernation or standby NLA Establishment of VPN sessions Moving in or out of a wireless network Network Location Awareness also: Removes the reliance on the ICMP protocol (PING) for assisting policy application across slow link connections Is used for bandwidth determination (applying GP over slow links)
Network Location Awareness (NLA)
Central Store Benefits Single point of storage Multilingual support Central Store hosted on Windows Server 2000, Windows Server 2003, & Windows Server 2008
PasswordSettings objects stored in ... Password Settings Container cn=Password Settings Container, cn=System, dc=northwind, dc=com
YIELD
Applied to Users and/or Groups
Must be Global Security Groups
GlobalNames Zone Intranet CNAME server.east.contoso.com
Users
Query for server.east.contoso.com
Int ran et. Quer ea y f east.contoso.com st. or con workstation 17 tos 2.2 o.c 0.1 om .1 1
Branch Office
Read-only replica AD DB Unidirectional replication Credential caching Read-only AD-integrated DNS zone
Changes made on a writeable-DC are replicated back to RODC, but not vice versa
Web Server
Web Server Farm
Multiple Local Group Policy Objects
FRS/ DFS-R
Use File Replication Service (FRS) on Windows 2000 and Windows Server 2003 Use Distributed File System Replication (DFS-R) on Windows Server 2008 Forest functional environments
GPO Processing Order
Password Settings override Domain Password Policy
Query for Intranet.west.contoso.com 1 3 172.20.1.1
west.contoso.com workstation Client types intranet into browser. DNS Client appends domain name suffixes to this single-label name. No client DNS suffix changes required
Universal group membership caching automatically enabled for site in which the RODC is deployed
Hub Site
4
Selectively enable password caching. Only passwords for accounts that are in the Allow group are replicated to RODC
Authenticate user and queue request to replicate credentials to RODC if allowed
11 12 1 2 10 9 3 8 4 7 6 5
Domain Controller
DHCP Server
MLGPO
Site
2
Domain
3
OUs
MLGPO Architecture
1 Local Computer Policy
LGPO Computer Configuration LGPO User Configuration Admin OR Non-Admin Group Policy Local User Account Policy
At User Logon and Password Change, check if a Password Settings Object has been assigned to this user
Groups
Delegated Administration for RODC
DNS server authoritative for west.contoso.com
Restartable Active Directory Service
Restarting AD requires membership of the built-in Administrators group on the DC
Active Directory Domain Services (AD DS) in Windows Server 2008 has the capability to start and stop the Active Directory Service via the MMC or command line.
Audit Object Changes
Active Directory (AD DS and AD LDS) in Windows Server 2008 has the capability to log changes made to AD objects.
Move Object Undelete Object
RODC administrators can be different users from domain administrator users. Benefits include: Prevents accidental modifications of directory data existing outside RODC Delegated installation and recovery of RODC
( Note: Steps 1 and 2 are not necessarily performed from the same computer) 1 Pre-Create and Delegate Domain Administrator uses AD Users and Computers MMC snap-in to pre-create RODC Specifies RODCs FQDN and Delegated Administration group 2 Promote RODC Delegated Administrator (non-DA) uses DCPROMO Wizard from server to configure as RODC Replicates over network, with support for secure IFM Reboots as RODC
IFM is complementary to replication over the network, but it does not replace the need for network replication.
RODC contacts writable DC at hub site and requests copy of credentials
Federation Server
BitLocker
Credentials Cache Credentials encrypted with a set of keys AD RMS Server SQL Server
Delegated Installation and Administration Process for RODC
Windows Vista, Windows Server 2008
Group Policy Tools
Group Policy Logging
Windows Logs Applications and Services Log No userenv.log required XML-based event logs Report, filter, and create customized log views Event Viewer Subscription Collect copies of events from multiple remote computers and store them locally
Start Stop
Manage new Windows Vista/Windows Server 2008 Policy Settings Manage Windows 2000, Windows Server 2003, and Windows XP Machine Policy Settings
(GPMC/GPOE)
If another DC cannot be contacted, administrator can log on either by using cached credentials or using the DSRM credentials Reduces time required for offline operations Log attribute values for new objects
Modify Object Log previous and current attribute values
1
Request sent to RODC
Directory Service States Stop/Start DS without Reboot
If the DC is contacted while the DC service is stopped, server acts as member server Another DC is used for logon, and normal Group Policy is applied
Log previous and new locations
Log old and new locations
Old/New password values NOT logged
Branch Office
RODC is advertised as the Key Distribution Center (KDC) for the branch office By default, an RODC will not store user or computer credentials except for its own computer account and a special "krbtgt" account (the account that is used for Kerberos authentication). Each RODC has a unique krbtgt account. RODC can be combined with Windows BitLocker Drive Encryption to provide enhanced data security for branch offices through boot-level hard-drive encryption
Windows 2000, Windows Server 2003, Windows XP Cannot manage new Windows Vista/Windows Server 2008 Policy Settings Manage Windows 2000, Windows Server 2003 and Windows XP Machine Policy Settings
(GPMC/GPOE)
AD DS Started AD DS Stopped (Ntds.dit offline) AD Directory Restore Mode
Audit Controls Global Audit Policy (Audit Active Directory Changes) Security Audit Entry on object Schema Set per attribute to prevent change logging
RODC Deployment Incremental Requirements
Windows Server 2003 Forest Functional Mode Multiple Windows Server 2008 DCs per domain are recommended to load balance RODC replication
Log changes to objects in Security Audit Log
Windows Server 2008 Active Directory Feature Components
This poster is based on a prerelease version of Windows Server 2008. All information herein is subject to change.
2007 Microsoft Corporation. Microsoft, Active Directory, BitLocker, IntelliMirror, Internet Explorer, RemoteApp, SharePoint, Windows, Windows PowerShell, Windows Vista and Windows Server are either registered trademarks or trademarks of Microsoft Corporation in the United States and/or other countries. All rights reserved. Other trademarks or trade names mentioned herein are the property of their respective owners.
Authors: Martin McClean & Astrid McClean (Microsoft Australia)
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5814)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1092)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (845)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (897)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (540)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (348)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (822)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (401)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- PoC For MDMDocument27 pagesPoC For MDMsvmglpNo ratings yet
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- 6th Central Pay Commission Salary CalculatorDocument15 pages6th Central Pay Commission Salary Calculatorrakhonde100% (436)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Asahi Glass Company Limited Swot AnalysisDocument4 pagesAsahi Glass Company Limited Swot Analysis254656No ratings yet
- OCL Quick Reference PDFDocument2 pagesOCL Quick Reference PDFЂурићДарко100% (1)
- Computer Based Fatigue Analysis For Welded Joints TWIDocument4 pagesComputer Based Fatigue Analysis For Welded Joints TWIDele TedNo ratings yet
- Buffalo WZR2-G300N Quick Setup GuideDocument6 pagesBuffalo WZR2-G300N Quick Setup GuideKevin Severud100% (8)
- SFSU Faculty and Staff Alphabetical DirectoryDocument102 pagesSFSU Faculty and Staff Alphabetical DirectoryKevin Severud100% (155)
- Buffalo WZR2-G300N ManualDocument48 pagesBuffalo WZR2-G300N ManualKevin Severud100% (8)
- SFSU Faculty and Staff by Department DirectoryDocument20 pagesSFSU Faculty and Staff by Department DirectoryKevin Severud100% (7)
- Windows Server 2008 Feature ComponentsDocument1 pageWindows Server 2008 Feature ComponentsKevin Severud100% (3)
- Plan Selection Based On Query Clustering: Antara Ghosh Jignashu Parikh Vibhuti S. Sengar Jayant R. HaritsaDocument12 pagesPlan Selection Based On Query Clustering: Antara Ghosh Jignashu Parikh Vibhuti S. Sengar Jayant R. HaritsamiritkaufmanNo ratings yet
- PICME (User Guide)Document22 pagesPICME (User Guide)bing100% (1)
- OpenVision Library Gaussian Mixture Model ImplementationDocument5 pagesOpenVision Library Gaussian Mixture Model Implementationpi194043No ratings yet
- PacketfenceDocument22 pagesPacketfenceLuka O TonyNo ratings yet
- Solutions: The Flow Diagram of The Process Is As Shown As BelowDocument5 pagesSolutions: The Flow Diagram of The Process Is As Shown As BelowMsAlis AlisNo ratings yet
- Requetes SQLDocument3 pagesRequetes SQLabc 123No ratings yet
- Thinkig SphinxDocument283 pagesThinkig Sphinxupender.d100% (1)
- From Punchcard To Big DataDocument35 pagesFrom Punchcard To Big DataFabrice EpelboinNo ratings yet
- Queue Using Array Questions and AnswersDocument11 pagesQueue Using Array Questions and AnswersChotu111No ratings yet
- MorphoManager User Manual PDFDocument154 pagesMorphoManager User Manual PDFcarlosgomescardozoNo ratings yet
- HP x360 PartDocument1 pageHP x360 PartmaulidinbNo ratings yet
- Module 3 Program Development Tools in The tms320f28335 1 PDFDocument47 pagesModule 3 Program Development Tools in The tms320f28335 1 PDFMORARI KINKAR SAMEER KUMARNo ratings yet
- Elastix Without Tears June2010Document299 pagesElastix Without Tears June2010LISNo ratings yet
- Discrete Mathematics ExercisesDocument65 pagesDiscrete Mathematics ExercisesNguyen Phuc Thinh (K16 HCM)No ratings yet
- CV OkiDocument3 pagesCV OkiOky WijayaNo ratings yet
- Java ProgramsDocument30 pagesJava ProgramsashwanileoNo ratings yet
- Gretl User's Guide: Gnu Regression, Econometrics and Time-Series LibraryDocument356 pagesGretl User's Guide: Gnu Regression, Econometrics and Time-Series Librarysandraexplica100% (1)
- Maze EscapeDocument23 pagesMaze EscapeHimansu SahaNo ratings yet
- IRC5 Programming and Operation - 2006 TKTDocument83 pagesIRC5 Programming and Operation - 2006 TKTpit100% (1)
- User Manual DSL605EWDocument116 pagesUser Manual DSL605EWklulaku100% (2)
- Learning Spring Boot 2 0 Microservices 34Document321 pagesLearning Spring Boot 2 0 Microservices 34Rupak Kumar100% (1)
- Matlab Code For Image Compression Using SPIHT AlgorithmDocument19 pagesMatlab Code For Image Compression Using SPIHT AlgorithmArsenalBestlyNo ratings yet
- Desire IAS Economic Handwritten NotesDocument117 pagesDesire IAS Economic Handwritten NotesAbhishek Pratap SinghNo ratings yet
- Projectile Motion With Air ResistanceDocument6 pagesProjectile Motion With Air ResistanceJulio Cesar Galdeano MoralesNo ratings yet
- PLC & HMI Interfacing For AC Servo Drive: Naveen Kumar E T.V.Snehaprabha Senthil KumarDocument5 pagesPLC & HMI Interfacing For AC Servo Drive: Naveen Kumar E T.V.Snehaprabha Senthil KumarNay Ba LaNo ratings yet