Professional Documents
Culture Documents
Cop: An Ultra-Lightweight Secure Network Coding Scheme Via Last Forwarder'S Proof
Cop: An Ultra-Lightweight Secure Network Coding Scheme Via Last Forwarder'S Proof
Uploaded by
Sajitha JosephOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Cop: An Ultra-Lightweight Secure Network Coding Scheme Via Last Forwarder'S Proof
Cop: An Ultra-Lightweight Secure Network Coding Scheme Via Last Forwarder'S Proof
Uploaded by
Sajitha JosephCopyright:
Available Formats
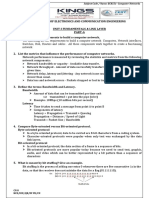
TSINGHUA SCIENCE AND TECHNOLOGY
ISSN ll 1007-0214 ll10/10 llpp599-605
Volume 17, Number 5, October 2012
CoP: An Ultra-Lightweight Secure Network Coding Scheme via Last
Forwarders Proof
+
Wei Ren
1;2;
, Linchen Yu
1
, Liangli Ma
3
1. School of Computer Science, China University of Geosciences, Wuhan 430074, China;
2. Shandong Provincial Key Laboratory of Computer Network, Jinan 250014, China;
3. Department of Computer Engineering, Naval University of Engineering, Wuhan 430033, China
Abstract: Network coding can improve network efciency by extending copy-and-forward paradigm to code-and-
forward paradigm. It thus imposes a security problem called pollution attack that some network coding or forwarding
nodes may intentionally fabricate, modify, forge, or drop packets. Recently, many authentication methods are
proposed to guarantee the correctness of encoding and forwarding results via the verication from receivers. Those
methods include homomorphic hashing, homomorphic message authentication code, and homomorphic signature.
However, those schemes result in expensive computation overhead due to the homomorphic cryptographic
primitives, so that those methods will not be able to work in most applications that confront resource constraints.
In this paper, we propose an ultra-lightweight checking protocol to guarantee the secure network coding without
any homomorphic cryptographic primitives. The extensive analysis proofs that it has following advantages: the
least security assumption for intermediate nodes, the least cryptographic primitive requirement, ultra-lightweight
computation, exible message length with probably proof, and minimal rounds in terms of message exchanging.
Key words: covert network coding; security; pollution attack; secure protocol
Introduction
Network coding technique extends traditional copy-
and-forward paradigm to code-and-forward paradigm
to improve efciency of network by reducing the
total number of forwarding packetsforwarding single
coded packet instead of forwarding multiple individual
packets
[1, 2]
. This technique has been extensively
Received: 2012-07-20; revised: 2012-08-20
+Supported by the Open Research Fund from the Shandong
Provincial Key Laboratory of Computer Networks (No.
SDKLCN-2011-01), the Fundamental Research Funds for
the Central Universities, China University of Geosciences
(Wuhan) (Nos. 110109 and 090109), and the National Natural
Science Foundation of China (No. 61170217)
++To whom correspondence should be addressed.
E-mail: weirencs@cug.edu.cn
applied in numerous applications such as content
distribution
[3]
, wireless video streaming
[4]
, and cloud
computing
[5]
.
As the packets are manipulated by encoding node or
transferred by forwarding node, they may be polluted
by those intermediate nodes. For example, the coding
node or forwarding node may intentionally manipulate,
modify, forge, and delete packets upon encoding or
forwarding. Such problem is called pollution attack
[6, 7]
and is addressed in many research works. However,
these works have extensively relied on attaching an
authentication tag, such as homomorphic hashing
[3, 8, 9]
,
homomorphic signature
[10-12]
, or homomorphic
message authentication code
[13-15]
, onto original
packets at sending nodes. The coding nodes and
forwarding nodes have to verify the correctness of
tags to justify the former operations on packets. It
thus induces expensive computations in intermediate
600 Tsinghua Science and Technology, October 2012, 17(5): 599-605
nodes, especially for each packet. Moreover, some
proposed schemes rely on cryptographic functions
such as modular exponential operations
[6, 9, 10]
or
elliptic curve bilinear pairing
[11, 12]
, which cannot be
applied in devices with resource constraints such as
sensor nodes. Additionally and unfortunately, some
of proposed schemes are proofed to be insecure by
recently conducted rigorous security analysis
[16]
.
Different from all current related works such
as cryptography-based schemes and other coding-
based schemes
[17-19]
, we address the problem from a
different viewpointrelying on nal receivers and last
forwarders. Our scheme does not rely any expensive
homomorphic cryptographic primitives, and thus does
not incur any heavy computations at intermediate
nodes. Hence, our scheme can be applied to any
network that consists of resource constraint devices.
The contributions of this paper are as follows: (1)
we propose a novel checking protocol with ultra-
lightweight computation for defending pollution attack
in general network coding scenarios; (2) we discover
the sufcient security requirement for cryptographic
primitive and proof the necessary condition for protocol
security; (3) we prove that the proposed protocols
induce the least rounds so as to have the best
communication performance. Moreover, our scheme
assume that there exist the most powerful attackers in
the network, for example, intermediate nodes can be
Byzantine or any active attackers.
1 Problem Formulation
1.1 Network model and system model
In typical buttery scenario, we specify the role of
nodes.
(1) SN: Sending Node. It is the node who sends out
original packets;
(2) CN: Coding Node. It is an intermediate node
who encodes the receiving packets and sends encoding
results to next intermediate node.
(3) FN: Forwarding Node. It is an intermediate node
who forwards encoding results to intended receivers.
(4) RN: Receiving Node. It is the node who is
intended to receive the original packets.
The data involved in network coding scenarios has
four types as follows:
(1) SD: Sent Data. It is the original data sent by SN
and coded by CN.
(2) CD: Coded Data. It is the coding result of SD.
(3) FD: Forwarded Data. It is the data forwarded by
FN.
(4) RD: Recovery Data. It is the data recovered by
RN.
We also assume all nodes have computational
resource-constraints. The communication link also has
resource-constraint.
1.2 Attack model, security requirement, and
design goals
CN and FN are assumed to be untrustworthy. CN and
FN may present Byzantine failure. They may also
malfunction or misbehave, such as dropping, arbitrary
coding, or tampering packet. The links between all
nodes are exposed to active or passive attacks, such
as packet fabrication, modication, and eavesdropping.
The only assumption is that SN and RN are assumed
to be trustworthy. Thus, the security assumption is
maintained to the minimum to let proposed scheme be
suitable to more general scenarios. Our security scheme
fullls security requirements as follows:
(1) Authenticity of RD
Data coding correctness at CN: The CD at CN is
indeed the correct coding result of SD.
Data integrity: It includes the integrity of SD, CD,
and FD.
Data source authentication: The source of the SD
must be veriable to conrm that the data indeed comes
from SN.
(2) Data condentiality of FD
It includes the data condentiality at FN, among FNs,
between FN and RN.
The design goal is thus to guarantee above
requirements to defend against pollution attack via an
ultra-lightweight manner.
2 Proposed Schemes and Analysis
In this section, we investigate a family of schemes for
better understanding. Each later scheme improves over
the previous one by addressing some of its limitations.
The available schemes for authentication of SD
largely relies on the homomorphic properties of
cryptographic functions, such as homomorphic hash
functions, homomorphic Message Authentication
Codes (MACs), and homomorphic signatures. Such
kind of cryptographic primitives are generated at
SN sides and veried at FN sides. However, totally
different from current schemes, we tackle the problem
from RN. The motivation is that the operations for
Wei Ren et al.: CoP: An Ultra-Lightweight Secure Network Coding Scheme 601
homomorphic tag generation and verication can all be
avoided.
Figure 1 depicts the typical scenario of network
coding called buttery network.
Suppose SN1s SD is A, and SN2s SD is B. Upon
the receipt of FD from FN, RN1 can recover RD that is
assumed to be B. RN1 can guarantee to have received
correct A, as A is received from SN who is assumed
to be trustworthy, instead of from CN and FN. Hence,
RN1 only needs to verify the correctness of data B. In
contrast, RN2 can guarantee to have received correct
B, and only needs to verify the correctness of data A.
Suppose A and B have the same length L.
We list all major notations used in the remainder of
the paper in Table 1.
2.1 Hash-based checking ProtocolHaP
We rstly propose a basic scheme called HaP to
illustrate our motivation.
We propose a data checking protocol between RN1,
RN2, and FN. As RN1 and RN2 cannot communicate
directly, we needs to rely on intermediate node
FN. RN1 and RN2 are assumed to be trustworthy,
which is the minimal security assumption for network
communication. FN is assumed to be untrustworthy.
Even if FN does not follow the protocol, for example,
presents Byzantine failure, fabricates received packets,
and forwards to others, or even drops packets, we
will prove that FN still cannot fool RNs to accept
unauthenticated data (so that the data authenticity is
protected).
Fig. 1 Typical scenario for network coding.
Table 1 Notations
n Length of A and B in bits
FN Forwarding node
RN Receiving node
m Length of block in bits
H./ Hash function
f./ One-way function
Suppose H./ is a cryptographically secure hash
function.
(1) RN1 sends H.A/ to FN. That is, RN1 FN :
H.A/;
(2) RN2 sends H.B/ to FN. That is, RN2 FN :
H.B/;
(3) FN sends (usually broadcasts) H.A/ H.B/ to
RN1 and RN2. That is,
FN RN1: RN2 : H.A/ H.B/:
Thus, RN1 can obtain H.B/ so as to check whether its
holding B is correct.
Similarly, RN2 can obtain H.A/ so as to check
whether its possessing A is correct.
Regrading the security, as H./ is a cryptographically
secure hash function, FN cannot recover A (or B)
from H.A/ (or H.B/). Regrading the performance,
the computation overhead is only hash function
computation at RN1 and RN2 and exclusive or (namely,
XOR) computation at FN side. The communication
overhead is three messages with length of [H./[.
2.2 One-way-based checking Protocol - OwP
We observe that the requirement of cryptographically
secure hash function H./ can be loosen to any one-
way function. That is, even if H./ is a one-way
function, the protocol is still secure. The requirement
for second pre-image resistance and collision resistance
for hash function can be omitted. Therefore, more
lightweight computation is enough for security and in
implementation more choices can be provided.
The function f :X Y is one-way, if and only if the
following two conditions are satised.
(1) Given Vx X, it is computationally feasible to
compute f.x/.
(2) Given Vy Y; it is computationally infeasible to
nd x X, such that f.x/ = y.
Denition 1 A general model for HaP
protocol The model consists of three parties. One is
untrustworthy, called F, the other two are trustworthy,
called N1 and N2. Each trustworthy party holds two
values, denoted by A and B. One value is guaranteed to
be true. The other value requirs to be veried by proof
from the other party. In other words, the possessed
trustworthy value by one party is coincidentally the
value that the other party wants to check.
More specically, N1 has authenticated A and wants
to check B; N2 has authenticated B and wants to
check A. The untrustworthy party F is an intermediate
party between two trustworthy parties. A and B have to
602 Tsinghua Science and Technology, October 2012, 17(5): 599-605
rely on F to communicate each other. Untrustworthy
parties have no idea of these two values (namely, A
and B), but it can manipulate (and know) the values
upon forwarding, including A B and values in HaP
protocol. We call the stage conducting HaP protocol as
a checking stage.
Our one-way function based checking protocol can
be modeled as follows, called OwP:
N1 F : f.A/;
N2 F : f.B/;
F A.andB/ : f.A/ f.B/;
where f./ is a one-way function.
Denition 2 The security denition of OwP
protocol The security of OwP protocol is dened as
follows:
(1) Condentiality of A and B. After the OwP
protocol, intermediate party almost has no idea of two
values. That is, F almost has no idea about A and B.
(2) Unforgeability of coded values A and B. It
is the major functionality of the proposed protocol.
Untrustworthy party cannot fool trustworthy parties to
regard a fabricated value as a trustworthy value. For
example, suppose F manipulates AB and sends it to
N1, so B is forged with respect to N1. Besides, A B
is also sent to N2, so A is forged with respect to N2.
After the protocol OwP, F cannot fool N1 to believe
her computed B is authenticated, and F cannot fool N2
to believe her computed A is authenticated.
Proposition 1 The condentiality of A and B is
guaranteed.
Proof Before checking stage, F only knows A
B. Thus Pr{A = a[a {0; 1]
n
] = Pr{B =
b[b {0; 1]
n
] = 1=2
n
: That is, A and B have
information-theoretic secrecy. After OwP protocol,
F only knows f.A/ and f.B/. As the one-wayness
of f./, given f.A/ and f.B/, F is computationally
infeasible to nd A and B. F only knows f.A/ for A
and f.B/ for B. Thus Pr{A = a[a {0; 1]
n
; f.a/ =
f.A/] = Pr{B = b[b {0; 1]
n
; f.b/ = f.B/] =
1=.2
n
1/: Besides, Pr{A = a[a {0; 1]
n
; f.a/ =
f.A/]=Pr{B = b[b {0; 1]
n
; f.b/ = f.B/] = 1.
That is, F nds A (or B) only by brute-force search
for x 2
n
such that f.x/ = f.A/ (or f.x/ = f.B/).
Proposition 2 The unforgeability of coded values
A and B are guaranteed.
Proof After OwP protocol, N1 (or N2) can obtain
f.B/ (or f.A/) by letting received f.A/ f.B/
exclusive-or with holding correct f.A/ (or f.B/).
Next, N1 (or N2) checks the correctness of B (or A)
by means of f.B/ (or f.A/), respectively.
We next prove that the following situation is
computationally impossible: F forges A B before
the launching of checking protocol OwP, and then F
successfully forges either (both) f.A/ or (and) f.B/,
which can fool N1 or (both) N2 to deem they receive
correct A B.
F manipulates A B {0; 1]
n
to .A B/
0
{0; 1]
n
and sends it to N1 and N2 before the checking
stage (namely, launching the checking protocol), thus
N1 holds incorrect B
0
and N2 holds incorrect A
0
.
Obviously, A
0
equals partial bit ipping of A; B
0
equals
partial bit ipping of B at the same location. Next,
checking stage starts. F wants to manipulate received
f.A/ and (or) f.B/ so as to fool N1 and (or) N2. As
F is computationally infeasible to compute A and B
from f.A/ and f.B/, F is computationally infeasible
to compute B
0
and A
0
from .A B/
0
. F thus can
only compute f.B
0
/ and f.A
0
/ by random guess with
correct probability 1=2
jf./j
. If [f./[ is large enough,
this value is negligible, as desired. This ends the proof.
Proposition 3 If f./ is not second pre-image
resistant, the protocol is still secure.
Proof f./ is not second pre-image resistant. That
is, given x X, it is computationally feasible to nd
x = x X such that f. x/ = f.x/.
Suppose F manipulates A B to .A B/
0
and
sends it to N1 and N2 before checking stage, thus N1
holds incorrect B
0
and N2 holds incorrect A
0
. A
0
equals
certain bit ipping of A; B
0
equals certain bit ipping
of B. The ipping locations in A
0
and B
0
are exactly the
same. F can fool RN1 or RN2 only if it can generate
correct f.A
0
/ and f.B
0
/. As it is computationally
infeasible for F to compute A and B from f.A/ and
f.B/, as well as A
0
and B
0
. Thus it is computationally
infeasible to compute f.A
0
/ and f.B
0
/.
Next, we proof that the ability of nding second pre-
image cannot improve the chance to compute f.A
0
/ and
f.B
0
/. After F receives f.A/ and f.B/, its additional
ability is thus to nd
A = A and
B = B such that
f.
A/ = f.A/ and f.
B/ = f.B/. (Strictly speaking,
it is not a scenario of second pre-image because pre-
image of f.A/ is not given.) The knowledge of
A and
B does not improve the opportunity to compute
f.A
0
/ and f.B
0
/.
Therefore, the computation of f.A
0
/ and f.B
0
/ only
Wei Ren et al.: CoP: An Ultra-Lightweight Secure Network Coding Scheme 603
relies on random guess, which is 1=2
jf./j
. It is the same
with the situation of one-wayness, as desired.
Proposition 4 If f./ is not collision resistant, the
protocol is still secure.
Proof f./ is not collision resistant. That is, it is
computationally feasible to nd x; x
0
X; x = x
0
, such
that f.x
0
/ = f.x/.
Suppose F manipulates A B to .A B/
0
and
send it to N1 and N2 before checking stage, thus N1
holds incorrect B
0
and N2 holds incorrect A
0
. A
0
equals
certain bit ipping of A; B
0
equals certain bit ipping
of B. The ipping locations in A
0
and B
0
are the exactly
same. F can fool RN1 or RN2 only if it can generate
correct f.A
0
/ and f.B
0
/. As it is computationally
infeasible for F to compute A and B from f.A/ and
f.B/, as well as A
0
and B
0
. Thus it is computationally
infeasible to compute f.A
0
/ and f.B
0
/.
Next, proof the ability of nding collision cannot
improve the chance to compute f.A
0
/ and f.B
0
/.
Even though F can choose two values x and x
0
such
that f.x
0
/ = f.x/ before checking stage, it cannot
manipulate AB to .AB/
0
such that A
0
; B
0
x; x
0
.
Thus F does not improve the possibility to compute
f.A
0
/ and f.B
0
/.
Therefore, the computation of f.A
0
/ and f.B
0
/ only
relies on random guess, which is 1=2
jf./j
. It is the same
with situation of one-wayness, as desired.
From above observations we thereby can draw
the conclusion that one-wayness of f./ is sufcient
condition for protocols security. Next, we will explore
whether it is a necessary condition, in other words,
whether the requirement of one-wayness of f./ can be
further loosened.
2.3 Partial One-way-based checking Protocol
pOwP
We observe that one-wayness of f./ can be further
loosened to partial one-way function, but security
becomes probabilistically secure. We rstly dene t -bit
one-way function as follows:
Denition 3 t-bit (1 t [X[) one-way function
t -bit one-way function is a function f :XY has
following properties:
(1) Given Vx X, it is computationally feasible to
compute f.x/.
(2) Given Vy Y , it is computationally infeasible to
nd t bits of x X, such that f.x/ = y.
The extreme case of t -bit one-way function is 1-bit
one-way function and [X[-bit one-way function.
Proposition 5 If f./ is t -bit one-wayness, OwP
protocol can nd data forgery with probability of 1
1=2
t
.
Proof If f./ is t -bit one-wayness, F cannot nd
full A and B from f.A/ and f.B/ (due to t bits cannot
be conjectured). F has to random guess t bits to obtain
A and B from f.A/ and f.B/. The probability of
successful guess is 1=2
t
. If guess is right, F ips
corresponding bits to compute A
0
and B
0
according to
the knowledge on former manipulation of .A B/
0
.
Finally, compute f.A
0
/ and f.B
0
/ to fool N1 and N2
successfully. Therefore, the probability of successful
forgery avoiding detection is 1=2
t
. In other words,
the successful probability that can nd data forgery by
checking protocol is 1 1=2
t
.
Corollary 1 1-bit one-wayness of f./ is necessary
condition for OwP protocols security.
Proof The security of OwP can be dened as
follows.
Given f.A/, attacker wants to compute f.A
0
/ where
A
0
is certain bit ipping of A and ipping locations are
known by attacker before given f.A/. If the probability
of success is negligible, the protocol OwP is secure.
That is,
Adv
Forge
A
= Pr{Succ
f.A
0
/
[f.A/; {A
0
; A] {0; 1]
n
;
[A[ = [A
0
[ = n; A
0
= BitFlip.A; i
1
; i
2
; ; i
n
/;
1 i
1
; i
2
; ; i
n
n] < .[f./[/;
where ./ is a negligible function with a security
parameter [f./[, Adv
Forge
A
is the advantage of attackers
fool receiving nodes (for example, N1) to regard a
forged data (for example, A) as an authenticated data.
It relies on the possibility of the event computing
correct f.A
0
/ successfully, namely Pr{Succ
f.A
0
/
].
BitFlip.A; i
1
; i
2
; ; i
n
/ is a function that ips A at
location i
1
; ; i
n
bits.
Adv
Forge
A
= Pr{Succ
f.A
0
/
[A f.A/;
A
0
BitFlip.A; i
1
; i
2
; ; i
n
/] Pr{Succ
f.A
0
/
[Guess];
where Guess is the event of randomly guessing correct
value f.A
0
/.
We have
Pr{Succ
f.A
0
/
[A f.A/;
A
0
BitFlip.A; i
1
; i
2
; ; i
n
/] < .[f./[/;
Pr{Succ
f.A
0
/
[Guess] 1=2
jf./j
:
Thus,
Adv
Forge
A
< .[f./[/;
604 Tsinghua Science and Technology, October 2012, 17(5): 599-605
since both .[f./[/ and 1=2
jf./j
are negligible function
in [f./[. It completes the proof.
Next, we further consider whether we can shorten the
length of communication messages in protocol. In other
words, we explore whether it is possible to only transmit
partial information of f.A/ and f.B/ in the protocol
without sacricing security. We propose a revised
protocol with short message length in next section.
2.4 Coding-based checking ProtocolCoP
To further reduce the communication overhead due to
large message length, we thus propose an XOR-based
coding scheme to shorten message length as follows:
(1) N1 sends A
m
=
L
iD.nm/=m
iD0
Trunc.f.A/; 1
i + m; m/ to F, where Trunc.P; Q; R/ is a truncate
function for cutting bit string P from starting point
Q.1 Q [P[ with length R.1 R [P[ Q/.
(2) N2 sends B
m
=
L
iD.nm/=m
iD0
Trunc.f.B/; 1
i + m; m/, to F;
(3) F sends A
m
B
m
to N1 and N2.
We assume m is a system parameter and m[L; .L =
[f.A/[ = [f.B/[/, so that N1 and N2 can send the
message with same length. N1 obtains A
m
B
m
and
compute A
m
by itself so as to obtain B
m
. N1 uses
computed B
m
to check whether its holding B is correct.
Similarly, N2 can obtain A
m
so as to check whether its
possessing A is correct.
If m = n, CoP is the same with OwP. If m = 1, the
message has only one bit.
Proposition 6 CoP can nd the data forgery with
probability of 1 1=2
m
.
Proof As f./ is one-way,
L
iD.nm/=m
iD0
Trunc.f./;
1 i +m; m/ is also one-way. Thus the security of CoP
is guaranteed. As F can manipulate the A
0
or B
0
and
random guess A
m
or B
m
, the probability of successful
guess is 1=2
m
. Thus it can nd the data forgery with
probability of 1 1=2
m
, as desired.
Regrading the performance, the communication
overhead is 3 messages with length of m. The induced
cost is low. More specically, induced computation
overhead is only i = .n m/=m times exclusive or
and function Tranc./ computation on strings of length
m bits at N1 and N2; former computation is one
time exclusive or on string of length L at N1 and
N2. Computation overhead of exclusive or at F also
decreases from length L to length m.
If N1 and N2 assume to send the rst or last chunk
with m-bit of f.A/ or f.B/, exclusive or operation can
be omitted. The probability of nding data forgery by
CoP is 1 1=2
m
.
Corollary 2 If only one bit of f.A/ is sent, for
example, the rst bit or last bit of f.A/, the probability
of nding data forgery of CoP is 1=2.
Proof Straightforward.
Finally, we proof the message rounds in the proposed
protocols (HaP, OwP, and CoP) is minimal.
Proposition 7 CoP protocol has the least rounds in
terms of messages exchanging.
Proof N1 (or N2) needs the others credential of B
(or A) to verify derived B (or A) from received AB.
Thus N2 (or N1) need to send credential of B (or A).
It costs at least two messages. To forward these two
messages to N1 and N2 via F, it will cost at least
two messages without network coding. Using network
coding, it costs at least one message. Therefore, the
minimal number of messages for the secure protocol is
3.
2.5 Extended applicability
In previous section, we discuss the typical network
coding scenariobuttery network. Next, we explore
the applicability of our proposed protocol in extended
scenarios with more than one last-hop forwarding
nodes, depicted in Fig. 2.
Our protocol can be easily extended to above scenario
by forwarding the f.A/ and f.B/ by last-hop node
until to the last common forwarding node, namely FN.
The FN will send f.A/ f.B/ and it is forwarded
through different last-hop nodes until to RN1 and RN2.
Proposition 8 Proposed protocols are secure in the
extended scenarios where there exist multiple last-hop
forwarding nodes.
Proof In extended scenario, nodes in different
Fig. 2 Extended scenario with more than one last-hop
forwarding nodes.
Wei Ren et al.: CoP: An Ultra-Lightweight Secure Network Coding Scheme 605
forwarding paths to RN1 and RN2 are more. As
proposed protocols are secure even though FN is
untrustworthy, the additional nodes have the same
information as FN. Thus even if they are untrustworthy,
the protocol still remain secure.
Next, we explore the applicability of our proposed
protocol in extended scenario where network coding
function is other operations except for exclusive or.
Proposition 9 Proposed protocols are secure in
extended scenarios where network coding function is
not exclusive or but others.
Proof Network coding function only affects the
performance before the checking stage. Checking
protocol veries the network coding result, so it
does not concern underlying concrete network coding
functions. Proposed protocols thus secure in extended
scenarios where network coding function is not
exclusive or. That is, network coding function could
be any function, linear or not.
3 Conclusions
In this paper, we propose several ultra-lightweight
security protocols in network coding context, to
check the correctness of received data yet maintaining
the condentiality of coded original data as well.
HaP is a hash function based checking protocol for
illustrating the motivation. OwP is a one-way function
based checking protocol to loosen the requirement
from cryptographically secure hash function to one-
way function. We proof one-wayness is the sufcient
condition, and 1-bit one-wayness is the necessary
condition for the checking protocol. t -bit one-wayness
function based OwP protocol can nd data forgery
with the probability 1 1=2
t
. It thus loosens the
requirement from one-way function to partial (or t -
bit) one-way function. To further shorten the message
length, we nally propose a one-way function and
coding schemeCoP, which uses simple exclusive-
or operation to code one-way functions result. The
security of CoP relies on the length of coding result (i.e.,
1 1=2
m
, where m is the length). CoP protocol has
the least rounds in terms of messages exchanging. The
proposed protocols are secure in the extended scenarios
where there exist multiple last-hop forwarding nodes,
and network coding function in applications is not
exclusiveor but others.
References
[1] Ahlswede R, Cai N, Li S, Yeung R W. Network informa-
tion ow. IEEE Trans. on Information Theory, 2000, 46(4):
1204-1216.
[2] Jaggi S, Sanders P, Chou P A, Effros M, Egner S, Jain
K, Tolhuizen L. Polynomial time algorithms for multicast
network code construction. IEEE Trans. on Information
Theory, 2005, 51(6): 1973-1982.
[3] Gkantsidis G, Rodriguez P. Cooperative security for
net-work coding le distribution. In: Proc. of IEEE
INFOCOM06, 2006: 1-13.
[4] Lima L, Gheorghiu S, Barros J, Medard M, Toledo
A. Secure network coding for multi-resolution wireless
video streaming. IEEE Journal of Selected Areas in
Communications, 2010, 28(3): 377-388.
[5] Oliveira P, Lima L, Vinhoza T, Barros J, Medard M.
Trusted storage over untrusted networks. In: Proc. of IEEE
Globecom Communication Theory Workshop10, 2010:
1-5.
[6] Yu Z, Wei T, Ramkumar B, Guan Y. An efcient signature-
based scheme for securing network coding against pollution
attacks. In: Proc. of IEEE INFOCOM08, 2008: 1409-1417.
[7] Yu Z, Wei Y, Ramkumar B, Guan Y. An efcient scheme
for securing xor network coding against pollution attacks.
In: Proc. of IEEE INFOCOM09, 2009: 406-414.
[8] Krohn M, Freedman M, Mazieres D. On-the-y verica-
tion of rateless erasure codes for efcient content distribu-
tion. In: Proc. of IEEE Security and Privacy (SP04), 2004:
226-240.
[9] Gennaro R, Katz J, Krawczyk H, Rabin T. Secure network
coding over the integers. In: Proc. of PKC10, LNCS 6056,
2010: 142-160.
[10] Zhao F, Kalker T, Medard M, Han K. Signatures for con-
tent distribution with network coding. In: Proc. of IEEE
ISIT07, 2007: 556-560.
[11] Boneh D, Freeman D, Katz J, Waters B. Signing a linear
subspace: Signature schemes for network coding. In: Proc.
of PKC09, 2009: 68-87.
[12] Czap L, Vajda I. Signatures for multi-source network cod-
ing. IACR 2010/328, 2010.
[13] Agrawal S, Boneh D. Homomorphic macs: Mac-based
integrity for network coding. In: Proc. of ACNS09, 2009:
292-305.
[14] Li Y, Yao H, Chen M, Jaggi S, Rosen A. Ripple authenti-
cation for network coding. In: Proc. of IEEE INFOCOM10,
2010: 1-9.
[15] Oggier F, Fathi H. An authentication code against pollution
attacks in network coding. IEEE/ACM Transactions on
Networking, 2011, 19(6): 1587-1596.
[16] Wang Y. Insecure provably secure network coding and
homomorphic authentication schemes for network coding.
IACR 2010/060, 2010.
[17] Dong J, Curtmola R, Nita-Rotaru C. Practical defenses
against pollution attacks in intra-ow network coding for
wireless mesh networks. In: Proc. of ACM WiSec09, 2009:
111-122.
[18] Kehdi E, Li B. Null keys: Limiting malicious attacks via
null space properties of network coding. In: Proc. of IEEE
INFOCOM09, 2009: 1224-1232.
[19] Zhang P, Jiang Y, Lin C, Fan Y, Shen (Sherman) X.
P-coding: Secure network coding against eavesdropping
attacks. In: Proc. of IEEE INFOCOM10, 2010: 1-9.
You might also like
- On The Security and Efficiency of Content Distribution Via Network CodingDocument12 pagesOn The Security and Efficiency of Content Distribution Via Network CodingArunkumar RakvNo ratings yet
- Performance Comparison of The AODV, SAODV and FLSL Routing Protocols in Mobile Ad Hoc NetworksDocument6 pagesPerformance Comparison of The AODV, SAODV and FLSL Routing Protocols in Mobile Ad Hoc Networksvishwaharnal115No ratings yet
- Rajba 2017Document4 pagesRajba 2017mohdsabithtNo ratings yet
- Enhancement in Elimination of Security Threads Using Trusted Proactive RoutingDocument7 pagesEnhancement in Elimination of Security Threads Using Trusted Proactive RoutingInternational Organization of Scientific Research (IOSR)No ratings yet
- Crypto 1Document12 pagesCrypto 1Vimala PriyaNo ratings yet
- Network Coding-Based Post-Quantum CryptographyDocument27 pagesNetwork Coding-Based Post-Quantum CryptographyTanu PraNo ratings yet
- Secure Routing With Time-Space Cryptography For Mobile Ad-Hoc NetworksDocument6 pagesSecure Routing With Time-Space Cryptography For Mobile Ad-Hoc NetworksarvyrevanthNo ratings yet
- Electronics 12 00559 v2Document16 pagesElectronics 12 00559 v2webmars11No ratings yet
- Packet-Hiding Methods For Preventing Selective Jamming AttacksDocument14 pagesPacket-Hiding Methods For Preventing Selective Jamming Attacksvinodb0No ratings yet
- Ijettcs 2012 10 10 041 PDFDocument4 pagesIjettcs 2012 10 10 041 PDFInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Collaborative Trust-Based Secure Routing Against Colluding Malicious Nodes in Multi-Hop Ad Hoc NetworksDocument8 pagesCollaborative Trust-Based Secure Routing Against Colluding Malicious Nodes in Multi-Hop Ad Hoc Networkssuchi87No ratings yet
- Enhanced MAC - Layer Security Protocol For Mobile Ad Hoc NetworkDocument8 pagesEnhanced MAC - Layer Security Protocol For Mobile Ad Hoc NetworkAbhay KumarNo ratings yet
- Secure Checkpointing Approach For Mobile EnvironmentDocument8 pagesSecure Checkpointing Approach For Mobile EnvironmentidescitationNo ratings yet
- Optical Paper 3Document9 pagesOptical Paper 3Pir Meher Ali Eng DepartmentNo ratings yet
- New Security Algorithm For Mobile Adhoc Networks Using Zonal Routing ProtocolDocument4 pagesNew Security Algorithm For Mobile Adhoc Networks Using Zonal Routing ProtocolSuriyaa SugumarNo ratings yet
- The Security Network Coding System With Physical Layer Key Generation in Two-Way Relay NetworksDocument9 pagesThe Security Network Coding System With Physical Layer Key Generation in Two-Way Relay Networksshirana msNo ratings yet
- Security and Collaborative Enforcement of Firewall Policies in VpnsDocument6 pagesSecurity and Collaborative Enforcement of Firewall Policies in VpnsInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- (IJCT-V2I2P10) Authors :E.Mukundhan, R.VeeramaniDocument4 pages(IJCT-V2I2P10) Authors :E.Mukundhan, R.VeeramaniIjctJournalsNo ratings yet
- Security Protocol For WSNsDocument9 pagesSecurity Protocol For WSNsIrshad UllahNo ratings yet
- 11 - 2022 - Impact of Outdated CSI On The Secure Communication in Untrusted In-Band Full-Duplex Relay NetworksDocument11 pages11 - 2022 - Impact of Outdated CSI On The Secure Communication in Untrusted In-Band Full-Duplex Relay NetworksAdam AlivinoNo ratings yet
- Distributed IntrusionDocument4 pagesDistributed Intrusionbenito agusNo ratings yet
- Towards Secure Quantum Key Distribution Protocol For Wireless Lans: A Hybrid ApproachDocument18 pagesTowards Secure Quantum Key Distribution Protocol For Wireless Lans: A Hybrid ApproachDrMadhuravani PeddiNo ratings yet
- Communication Network EC8551Document43 pagesCommunication Network EC8551Raja Pirian100% (3)
- IEEE Paper Problem StatementsDocument12 pagesIEEE Paper Problem StatementsKeerthiPratheek ReddyNo ratings yet
- Polar Coding For The Multiple Access WiretapDocument19 pagesPolar Coding For The Multiple Access WiretapMehmet KibarNo ratings yet
- Full 7970Document20 pagesFull 7970Cosmin AndreiNo ratings yet
- Project Report SampleDocument61 pagesProject Report SampleVIMALNo ratings yet
- An Enhanced Polynomial-Based Key Establishment Scheme For Wireless Sensor NetworksDocument4 pagesAn Enhanced Polynomial-Based Key Establishment Scheme For Wireless Sensor Networkssathish14singhNo ratings yet
- AQ C - R U A S N C: Uantum Based Hallenge Esponse SER Uthentication Cheme Over Oiseless HannelDocument13 pagesAQ C - R U A S N C: Uantum Based Hallenge Esponse SER Uthentication Cheme Over Oiseless HannelAIRCC - IJNSANo ratings yet
- Route Diversity Based Optimal Path Selection Using Random Key GenerationDocument8 pagesRoute Diversity Based Optimal Path Selection Using Random Key GenerationJournal of Computer ApplicationsNo ratings yet
- We Are Intechopen, The World'S Leading Publisher of Open Access Books Built by Scientists, For ScientistsDocument15 pagesWe Are Intechopen, The World'S Leading Publisher of Open Access Books Built by Scientists, For ScientistsArya ChowdhuryNo ratings yet
- A Novel Acknowledgement Based Intrusion Detection System For ManetsDocument5 pagesA Novel Acknowledgement Based Intrusion Detection System For ManetsIJMERNo ratings yet
- Network Coding Based Reliable Multi-Path Routing in Wireless Sensor NetworkDocument8 pagesNetwork Coding Based Reliable Multi-Path Routing in Wireless Sensor NetworkRahul BhardwajNo ratings yet
- Network-Assisted Mobile Computing With Optimal Uplink Query ProcessingDocument16 pagesNetwork-Assisted Mobile Computing With Optimal Uplink Query ProcessingPonnu ANo ratings yet
- SPREAD: Enhancing Data Confidentiality in Mobile Ad Hoc NetworksDocument10 pagesSPREAD: Enhancing Data Confidentiality in Mobile Ad Hoc NetworksJansi PrasannaNo ratings yet
- A Contribution To Secure The Routing Protocol "Greedy Perimeter Stateless Routing'' Using A Symmetric Signaturebased Aes and MD5 HashDocument9 pagesA Contribution To Secure The Routing Protocol "Greedy Perimeter Stateless Routing'' Using A Symmetric Signaturebased Aes and MD5 HashijdpsNo ratings yet
- Security in Wireless Sensor NetworksDocument12 pagesSecurity in Wireless Sensor Networksghorbani22No ratings yet
- Network CodingDocument24 pagesNetwork CodingChris ChangNo ratings yet
- Ariadne: A Secure On-Demand Routing Protocol For Ad Hoc NetworksDocument12 pagesAriadne: A Secure On-Demand Routing Protocol For Ad Hoc NetworksPablo Velarde AlvaradoNo ratings yet
- CAN Paper Jain Arafin Wang PreprintDocument20 pagesCAN Paper Jain Arafin Wang PreprintYislennier MolinaNo ratings yet
- Ijaiem 2014 10 29 70Document5 pagesIjaiem 2014 10 29 70International Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- ESL2023 randomInterleaverNSDocument4 pagesESL2023 randomInterleaverNSlucianaNo ratings yet
- A Secure Routing Protocol For Ad Hoc NetworksDocument10 pagesA Secure Routing Protocol For Ad Hoc NetworkskhangtmkNo ratings yet
- State of Security in IEC 61850 SubstationsDocument5 pagesState of Security in IEC 61850 SubstationsNikolas UrlaubNo ratings yet
- Viva VoceDocument5 pagesViva VocesathishNo ratings yet
- A Novel Authentication Scheme For Ad Hoc Networks: Lakshmi Venkatraman and Dharma P. AgrawalDocument6 pagesA Novel Authentication Scheme For Ad Hoc Networks: Lakshmi Venkatraman and Dharma P. Agrawalddaffodil2004No ratings yet
- Assignment No 4 (DONE)Document15 pagesAssignment No 4 (DONE)abdullah noorNo ratings yet
- Ijet V3i5p40Document7 pagesIjet V3i5p40International Journal of Engineering and TechniquesNo ratings yet
- ECE - Network - KrantishDocument4 pagesECE - Network - KrantishTJPRC PublicationsNo ratings yet
- An Efficient Secure Zone Based Routing Protocol For Mobile Adhoc NetworkDocument8 pagesAn Efficient Secure Zone Based Routing Protocol For Mobile Adhoc Networkabhintpc09No ratings yet
- IEEE Projects 2012-2013 Network SecurityDocument7 pagesIEEE Projects 2012-2013 Network Securitysathish20059No ratings yet
- EC8551 CN Question BankDocument43 pagesEC8551 CN Question BankRaja Pirian100% (3)
- Reputation Based RoutingDocument12 pagesReputation Based RoutingFlorin AlexNo ratings yet
- Ijnsa 050209Document8 pagesIjnsa 050209AIRCC - IJNSANo ratings yet
- Public Key Based Cryptoschemes For Data Concealment in Wireless Sensor NetworksDocument8 pagesPublic Key Based Cryptoschemes For Data Concealment in Wireless Sensor Networkspoonam pandeyNo ratings yet
- Packet-Hiding Methods For Preventing Selective Jamming AttacksDocument14 pagesPacket-Hiding Methods For Preventing Selective Jamming AttacksYesu BirlaNo ratings yet
- Packet Coding For Strong Anonymity in Ad Hoc NetworksDocument10 pagesPacket Coding For Strong Anonymity in Ad Hoc NetworksAnand TRNo ratings yet
- AMPC A Lightweight Hybrid Cryptographic Algorithm For Wireless Sensor NetworksDocument5 pagesAMPC A Lightweight Hybrid Cryptographic Algorithm For Wireless Sensor NetworksInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Ipv6 ImplDocument26 pagesIpv6 ImplHammad YousafNo ratings yet
- Arp and RarpDocument36 pagesArp and RarpShiva NageswararaoNo ratings yet
- TSB-2010-071-A (Download)Document3 pagesTSB-2010-071-A (Download)david0young_2No ratings yet
- 02 IK IESYS e Introduction To Industrial EthernetDocument32 pages02 IK IESYS e Introduction To Industrial EthernetHernando AlborNo ratings yet
- Ethernet/Ip Programmer'S Guide: Acr Motion ControllersDocument33 pagesEthernet/Ip Programmer'S Guide: Acr Motion ControllersepirikonNo ratings yet
- Topic 1 2 - NETWORK ADMINISTRATIONDocument7 pagesTopic 1 2 - NETWORK ADMINISTRATIONLanz CatamisanNo ratings yet
- Knowledgenet Cisco Ccie Security Student Guide Version 1 1Document1,248 pagesKnowledgenet Cisco Ccie Security Student Guide Version 1 1Pedro PedNo ratings yet
- Q.1 Describe Client-Server Architecture With Suitable DiagramDocument18 pagesQ.1 Describe Client-Server Architecture With Suitable DiagramAbhishekNo ratings yet
- Cross Layer Approach To Enhance TCP PerformanceDocument6 pagesCross Layer Approach To Enhance TCP PerformanceMurali KarthikeyanNo ratings yet
- Sockets and TCP PDFDocument29 pagesSockets and TCP PDFGzim DragushaNo ratings yet
- UMTS Troubleshooting PS Problems 201111Document68 pagesUMTS Troubleshooting PS Problems 201111shindeleNo ratings yet
- WCMC Chapter 6 - Satellite SystemsDocument36 pagesWCMC Chapter 6 - Satellite Systemsይንገስ ጎጃም አድማስNo ratings yet
- Installing Activating and Configuring Your Polycom PVX Videoconferencing Codec OldDocument12 pagesInstalling Activating and Configuring Your Polycom PVX Videoconferencing Codec OldprakashpathakNo ratings yet
- Optical Switching Comprehensive GuideDocument370 pagesOptical Switching Comprehensive GuideSanjay YadavNo ratings yet
- IS1002Document13 pagesIS1002Suvendra SahooNo ratings yet
- Manual Planet FGSW 2620RSDocument38 pagesManual Planet FGSW 2620RSsmigolNo ratings yet
- Ceragon Lineup Nov07 PDFDocument42 pagesCeragon Lineup Nov07 PDFGonzalo GuarachiNo ratings yet
- Google Protocol Buffers For Embedded Iot: Integration in A Medical Device ProjectDocument32 pagesGoogle Protocol Buffers For Embedded Iot: Integration in A Medical Device ProjectNhân Nhậu NhẹtNo ratings yet
- Tems DiscoveryDocument11 pagesTems DiscoveryNgweno MzitoNo ratings yet
- Iptables Tutorial - PsDocument258 pagesIptables Tutorial - Pscatalinalex73No ratings yet
- RPG IV Socket TutorialDocument171 pagesRPG IV Socket TutorialanupgiriNo ratings yet
- Satellite Router: General Description and Installation GuideDocument20 pagesSatellite Router: General Description and Installation GuideSergioFerrufinoFloresNo ratings yet
- Quiz1 at IIT Bombay For Communication NetworksDocument2 pagesQuiz1 at IIT Bombay For Communication NetworksPrakhar KhandelwalNo ratings yet
- An Introduction To SimEventsDocument69 pagesAn Introduction To SimEventsAryo DanielNo ratings yet
- Seminar On Bluetooth: Abinash Ojha Reg. No.-0501206108 Branch-ENTC Ajay-Binay Institute of Technology, CTCDocument22 pagesSeminar On Bluetooth: Abinash Ojha Reg. No.-0501206108 Branch-ENTC Ajay-Binay Institute of Technology, CTCAnnada Prasanna DasNo ratings yet
- Digital Crime InvestigationDocument35 pagesDigital Crime InvestigationMr ViperNo ratings yet
- Uni, Broad, Multi-CastingDocument4 pagesUni, Broad, Multi-CastingQasimShahzadaNo ratings yet
- Layered Approach Using Conditional Random Fields For Intrusion DetectionDocument7 pagesLayered Approach Using Conditional Random Fields For Intrusion DetectionJayaraman AnandanNo ratings yet
- Hyper TransportDocument23 pagesHyper TransportJAYESHTRIV0% (1)