Professional Documents
Culture Documents
Michael Richo Criminal Complaint
Uploaded by
SoftpediaOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Michael Richo Criminal Complaint
Uploaded by
SoftpediaCopyright:
Available Formats
Case 3:16-mj-00464-SALM Document 1 Filed 10/04/16 Page 1 of 1
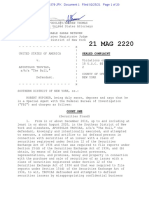
AO 91 (Rev 11111) Criminal Complaint
UNITED STATES DISTRICT COURT
for the
Di.1ric1 J' onnect icut
United States of America
2016 OCT
v.
ll
).
)
)
)
)
)
MICHAEL RICHO
9 YO
tad~ No.
1 _/
3:16-mj- 41,{1'-(SALM)
Defendant(s)
CRIMINAL COMPLAINT
I, the complainant in this case, state that the following is true to the best of my knowledge and belief.
On or about the date(s) of
November 2013 to October 2014
District of
Connecticut
in the
, the defendant(s) violated:
Offense Description
Code Section
18
18
18
18
18
in the county of _ _ New Haven
U.S.C. 1029(a)(2) and (a)(3)
U.S. C. 1030(a)(2) and (a)(4)
u.s.c. 1343
U.S.C. 1028A
U.S.C. 1956(a)(1 )(B)(i)
Access device fraud
Computer fraud
Wire fraud
Aggravated identity theft
Money laundering
This criminal complaint is based on these facts:
See attached Affidavit of FBI Specel Agent Michael Morrison, which is incorporated herein by reference .
~ Continued on the attached sheet.
Printed name and title
Sworn to before me and signed in my presence.
Date:
/s/ Sarah A. L. Merriam
10/03/2016
-~ ~---
Judge 's signature
City and state:
New Haven, CT
lsmah A. L. Merriam, U.S. Magistrate Judge
Printed name and title
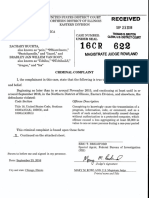
Case 3:16-mj-00464-SALM Document 1-1 Filed 10/04/16 Page 1 of 15
UNDER SEAL
STATE OF CONNECTICUT
ss: New Haven, Connecticut
FlL::::J
u
ArJ
0 Oct
U.~ . i
AFFIDAVTT IN SUPPORT Olt A RIJVON AL
ber 3 2016
MPLAINT AND ARREST WARRANT
I, Michael Morrison, being duly sworn, depose and state as follows:
BACKGROUND OF AFFIANT
1.
I have been employed as a Special Agent for the Federal Bureau of Investigation
("FBI") since 2012. I am currently assigned to the cybercrime squad ofthe New Haven Division.
I have received training and gained experience in, inter alia, arrest procedures, search warrant
applications, the execution of searches and seizures, computer crimes, and computer evidence
identification, seizure and processing. I have personally participated in investigations related to
financial fraud, cybercrimes, and cyber intrusions. In addition to my work experience, I have
received specialized training in the field of computer crime investigation from the FBI and others.
I am an "investigative or law enforcement officer of the United States," within the meaning of 18
U.S.C. 251 0(7), that is, an officer of the United States who is empowered by law to conduct
investigations of and to make arrests for offenses enumerated in 18 U.S.C. 2516.
2.
I make this affidavit in support of a Criminal Complaint and Arrest Warrant
charging Michael Richo ("RICHO"), a 34-year old male born in 1981 and having a social security
number of xxx-xx-0169, with access device fraud, in violation of 18 U.S.C. 1029(a)(2) and
(a)(3), computer fraud, in violation of 18 U.S.C. 1030(a)(2) and (a)(4), wire fraud, in violation
of 18 U.S.C. 1343, aggravated identity theft, in violation of 18 U.S.C. I 028A, and money
laundering, in violation of 18 U.S.C. 1956(a)(l )(B)(i) (collectively, the "TARGET
OFFENSES"). Based on the facts set forth below, I believe there is probable cause to believe, and
Case 3:16-mj-00464-SALM Document 1-1 Filed 10/04/16 Page 2 of 15
I do believe, that RICHO knowingly committed the TARGET OFFENSES in the District of
Connecticut.
3.
The statements contained in this affidavit are based in part on information provided
by other members of local, state, and federal law enforcement, my own investigation to include
personal observations, documents and other investigative materials which I have reviewed, as well
as my training and experience as a Special Agent with the FBI. Since this affidavit is being
submitted for the limited purpose of obtaining a criminal complaint and arrest warrant, I have not
included each and every fact known to me concerning this investigation. I have set forth only the
facts that I believe are necessary to establish probable cause to believe that RICHO committed the
TARGET OFFENSES.
RELEVANT STATUTES
4.
This investigation concerns possible violations of 18 U.S.C. 1029 (access device
fraud), 1030 (computer fraud), 1343 (wire fraud), 1028A (aggravated identity theft), and 1956
(money laundering).
5.
18 U.S.C. 1029(a)(2) prohibits a person from knowingly, and with intent to
defraud, using one or more unauthorized access devices during any one-year period and by such
conduct, obtaining anything of value aggregating $1,000 or more during that period. 18 U.S.C.
I 029(a)(3) further prohibits a person from knowingly, and with intent to defraud, possessing
fifteen or more unauthorized access devices. The term "access device" is defined to mean, among
other things, any card, account number, electronic serial number, personal identification number,
or other means of account access that can be used, alone or in conjunction with another access
device, to obtain money, goods, services, or any other thing of value, or that can be used to initiate
a transfer of funds. The term "unauthorized access device" is defined to mean any access device
Case 3:16-mj-00464-SALM Document 1-1 Filed 10/04/16 Page 3 of 15
that is, among other things, stolen or expired with intent to defraud.
6.
18 U.S.C. 1030(a)(2) (computer fraud) prohibits a person from, among other
things, accessing a computer without authorization, and thereby obtaining information from a
protected computer. 18 U.S.C. 1030(a)( 4) further prohibits a person from knowingly and with
intent to defraud, accessing a protected computer without authorization, and by means of such
conduct furthering the intended fraud and obtaining anything of value, unless the object of the
fraud and the thing obtained consists only of the use of the computer and the value of such use is
not more than $5,000 in any one-year period. The term "protected computer" is defined to include,
among other things, a computer used in or affecting interstate or foreign commerce or
communication.
7.
18 U.S.C. 1343 (wire fraud) prohibits a person who, having devised or intending
to devise any scheme or artifice to defraud, or for obtaining money or property by means of false
or fraudulent pretenses, representations, or promises, transmits or causes to be transmitted by
means of wire, in interstate or foreign commerce, any writings, signs, signals, pictures, or sounds
for the purpose of executing such scheme or artifice.
8.
18 U.S.C. 1028A (aggravated identity theft) prohibits a person, during and in
relation to certain enumerated felonies, from knowingly transferring, possessing, or using, without
lawful authority, a means of identification of another person. The enumerated felonies include
any violations of Chapters 47 and 63, which, in tum, includes violations of 18 U.S.C. 1029
(access device fraud), 1030 (computer fraud), and 1343 (wire fraud).
The term "means of
identification" is defined to include, among other things, any name or number that may be used,
alone or in conjunction with any other information, to identify a specific individual, including,
among other things, a name, social security number, or unique electronic identification number or
Case 3:16-mj-00464-SALM Document 1-1 Filed 10/04/16 Page 4 of 15
address.
The term "means of identification" also includes an "access device" as defined in 18
u.s.c. 1029.
9.
18 U.S.C. 1956(a)(l )(B)(i) prohibits a person from conducting or attempting to
conduct a financial transaction involving proceeds of specified unlawful activity in order to
conceal or disguise the nature, location, source, ownership or control of such proceeds. The term
"conducts" is defined to include initiating, conducting, or participating in initiating, or concluding
a transaction. The term "specified unlawful activity" includes violations of 18 U.S.C. 1029
(access device fraud), 1030 (computer fraud), and 1343 (wire fraud).
BACKGROUND ON BITCOINS
10.
Bitcoins are an anonymous, decentralized form of electronic currency, existing
entirely on the Internet and not in any physical form.
The currency is not issued by any
government, bank, or company, but rather is generated and controlled automatically through
computer software operating on a "peer-to-peer" network. Bitcoin transactions are processed
collectively by the computers composing the network. To acquire bitcoins in the first instance, a
user typically must purchase them from a bitcoin "exchanger," who accepts payments of currency
in conventional form, and exchanges them for bitcoins, based on a fluctuating exchange rate.
Bitcoins are maintained by a user in an electronic "wallet," associated with a bitcoin "address,"
which is analogous to an account number for a bank account. A user can use bitcoins in his wallet
to conduct financial transactions by transferring bitcoins from his bitcoin address to the bitcoin
address of another user. The "address" is analogous to the account number for a bank account,
while the "wallet" is analogous to a bank safe where the money in the account is physically stored.
All bitcoin transactions are maintained on a public ledger known as the "Blockchain," which serves
to prevent a user from spending the same bitcoins more than once. However, the Blockchain only
Case 3:16-mj-00464-SALM Document 1-1 Filed 10/04/16 Page 5 of 15
reflects the movement of funds between anonymous bitcoin addresses and therefore cannot by
itself be used to determine the identities ofthe persons involved in the transactions.
11.
There are a number of online exchanges that allow users to buy and sell bitcoins
for fiat currency, such as U.S. currency. In addition, there are online services that allow users to
exchange their bitcoins directly with other users. One such service is Local Bitcoins, which is
located on the internet at http://localbitcoins.com. According to the Local Bitcoins website,
"LocalBitcoins.com is a person-to-person bitcoin trading site. At LocalBitcoins.com, people from
different countries can exchange their local currency to bitcoins. The site allows users to post
advertisements where they state exchange rate and payment methods for buying or selling
bitcoins."
12.
A bitcoin tumbler is a mixing service which is utilized to help mask the trail of
bitcoins. Since all bitcoin transactions are documented on the Blockchain, a tumbler attempts to
mask the transactional trail by having a person send their bitcoins to this service, often for a
nominal fee, which then will combine them with many other people's bitcoins. The service, over
a period of time and multiple random transactions will send the bitcoins to a new bitcoin address
in the control of the mixing service's client. Based on my training and experience and information
provided to me by others, I am aware that Bitcoin Fog is an online bitcoin tumbling service.
BACKGROUND ON TOR AND THE ''DARK WEB"
13.
"Tor," which is an acronym for "The Onion Router," is a special network of
computers on the Internet, distributed around the world, that is designed to conceal the true IP
addresses 1 of the computers on the network, and, thereby, the identities of the network's users.
1
Every computer device connected to the Internet has an "Internet protocol" or "IP" address
assigned to it, which is used to route Internet traffic to or from the device. A device's IP address
can be used to determine the device's physical location and, thereby, its user.
5
Case 3:16-mj-00464-SALM Document 1-1 Filed 10/04/16 Page 6 of 15
Every communication sent through Tor is bounced through numerous relays within the network,
and wrapped in numerous layers of encryption, such that it is practically impossible to trace the
communication back to its true originating IP address. Tor likewise enables websites to operate
on the network in a way that conceals the true IP addresses of the computer servers hosting the
websites. Such "hidden services" operating on Tor have complex web addresses, generated by a
computer algorithm, ending in ".onion" (rather than ".com" or ".net"). In order to access the Tor
network, anyone can simply download the Tor browser software and use it to access the internet.
Because of the anonymity provided to users and websites on the Tor network, it is sometimes
referred to as the "Dark Web."
14.
Based on my training and expenence, I am aware that criminals have taken
advantage of the Dark Web to create websites with online marketplaces dedicated to the trafficking
of controlled substances and other illicit goods. Many of these online marketplaces further protect
the anonymity of their users by requiring all transactions to be paid for through the use ofbitcoins.
Typically, in order to make purchases of products from these online marketplaces, a user must first
obtain bitcoins and send them to his or her account at the online marketplace. The marketplace
maintains information regarding the balance of bitcoins maintained by each user. After funding
his or her account, the user can then make purchases from the marketplace. When the user
purchases an item on the marketplace, the bitcoin balance of the user is debited by the purchase
price. The purchase price is held in escrow by the marketplace, and after the sale is completed,
the marketplace releases the bitcoins from escrow. Users can withdraw bitcoins from their bitcoin
balances on the marketplace by providing the marketplace with a bitcoin address to which funds
can be transferred. Some marketplaces charge a commission for every transaction conducted by
its users.
Case 3:16-mj-00464-SALM Document 1-1 Filed 10/04/16 Page 7 of 15
THE INVESTIGATION AND PROBABLE CAUSE
15.
In November 2013, the FBI began investigating RICHO in connection with his
involvement with a hidden online marketplace on the Tor network that specialized in the sale of
illegal narcotics, stolen credit cards, and other illicit items.
The FBI subsequently obtained
information that RICHO may have been involved in an online phishing2 scheme whereby RICHO
would obtain people's usernames and passwords in an effort to steal their bitcoins. At the time,
RICHO was living in West Haven, Connecticut.
16.
On November 4, 2014, the Honorable Holly B. Fitzsimmons, United States
Magistrate Judge for the District of Connecticut, issued a federal search and seizure warrant for
RICHO's residence in West Haven. I was the affiant in the application for that search warrant.
17.
FBI agents and other law enforcement officers executed the warrant on November
6, 2014. I was not present during the execution of the warrant, but I have reviewed reports related
to the execution of the warrant.
18.
During the execution of the warrant, FBI agents and other law enforcement officers
located and seized multiple computers, external hard drives, and thumb drives.
/
19.
As the search was being executed, RICHO agreed to an interview with FBI agents
at his residence. During the interview, RICHO admitted, in substance and in part, the following:
a.
RICHO has his own business called MediaPen.
Phishing is an attempt by a person to learn information such as login credentials or account
information of another individual by impersonating a reputable entity or person via emails,
websites, or other communication channels. Often times, a person operating a phishing scheme
will create emails that appear to be from a legitimate entity, such as a bank for example. The email
may ask the recipient to respond with account login credentials, or it may contains links to what
appears to be the entity's website, but in reality, it is a fake website that is designed to capture an
individual's login credentials.
7
Case 3:16-mj-00464-SALM Document 1-1 Filed 10/04/16 Page 8 of 15
b.
RICHO steals bitcoins from users and vendors trying to access online
marketplaces on the Tor network.
c.
RICHO used two types of scams to steal user's login information to these
sites. He would post fake links on forums to these markets which would direct users to a fake login
page hosted on a laptop at his house. The login page would look exactly like the real login pages
for the various market sites. When users would attempt to log in, he would steal their usemames
and passwords.
d.
The other technique RICHO used to steal login credentials involved posting
fake links on forums that when clicked would "port forward" the users through RICHO's computer
server to the actual marketplace site where users would log in. RICHO would keylog 3 all of the
user's traffic including their login information.
e.
Once RICHO had access to a user's account, he would use a program called
"bitcoin monitor" to notify him when a deposit was made into the user's bitcoin wallet. After
receiving notification of a deposit, he would log in to the account and withdraw the bitcoins before
the user could spend them. He would often use "Bitcoin Fog" when transferring the bitcoins to
hide his trail. The bitcoins would then be deposited into his bitcoin wallet with "Local Bitcoins"
where he would sell them in exchange for cash deposits into his Bank of America account, Green
Dot prepaid debit cards, Western Union transfers, or Money Gram transfers. RICHO's usemame
with Local Bitcoins was "bmerc."
f.
RICHO estimated that he had stolen over "six figures" worth ofbitcoins.
Key logging, sometimes referred to as keystroke logging, is the action of recording (logging) the
keys struck on a keyboard, typically covertly, so that the person using the keyboard is unaware
that their actions are being monitored.
8
Case 3:16-mj-00464-SALM Document 1-1 Filed 10/04/16 Page 9 of 15
g.
RICHO stated he had a program on his laptop that stored the stolen
usemames and passwords in a file called "nicefancy.txt." RICHO believed it currently had over
10,000 lines of text.
20.
During the interview, RICHO also advised FBI agents that he had additional
computer hard drives in a safety deposit box at People's United Bank. RICHO signed a consent
to search form allowing the FBI to search and seize the contents of his safety deposit box, and he
provided FBI agents with the key to his safety deposit box. FBI agents subsequently visited
People's United Bank and seized the contents of RICHO's safety deposit box, which contained,
among other things, a hard drive and thumb drives.
21.
FBI computer forensic examiners subsequently examined the computers and hard
drives seized from RICHO's residence and safety deposit box. I have reviewed the files recovered
from the forensic examination. Among the files recovered from RICHO's computers and hard
drives were dozens of files created between November 2013 and October 2014 that contain what
appear to be thousands ofusemames and passwords. I observed numerous files titled "nicefancy"
followed by a date.
For example, one file titled "nicefancy0929.txt" had a created date of
September 29,2014. The file contained what appear to be over 10,000 usemames and passwords.
Based on my training and experience, my investigation to date, and RICHO's statements to law
enforcement officers, I believe these are usemames and passwords belonging to other individuals
that RICHO stole through the methods he described in his interview.
22.
During the forensic examination, FBI computer forensic examiners also recovered
numerous online chats between someone with usemames "fatfreak82828" and "fatfreak82829"
and other individuals. In one of the chats, "fatfreak82828" asks another individual to email him at
"mediapenllc@gmail.com."
In
another
chat,
one
of
the
participants
asks,
Case 3:16-mj-00464-SALM Document 1-1 Filed 10/04/16 Page 10 of 15
"mediapenllc@gmail.com[.] who is?? u?" to which fatfreak82829 replies, "me". As discussed,
RICHO told law enforcement he has a business named Media Pen. I have reviewed online records
from the Connecticut Secretary of State's website indicating that RICHO is the manager of
MediaPen LLC. In addition, I have obtained and reviewed bank records for MediaPen LLC at
Bank of America which lists RICHO as the manager of MediaPen LLC. I have also obtained and
reviewed records from Green Dot Bank for prepaid debit cards registered to RICHO which indicate
he registered one card using an email address mediapenllc@gmail.com. Based on this information,
I believe that "fatfreak82828" and "fatfreak82829" are both RICHO.
23.
In the chats, "fatfreak82828" admits to using a phishing scheme to steal individuals'
login credentials in order to steal their bitcoins, and further admits he is an experienced computer
hacker who has been hacking computers since he was 12 years old. The following are examples
of some of the chat messages sent by "fatfreak82828," who I believe is RICHO, that were
recovered from the forensic examination ofRICHO's computers and hard drives:
a.
On November 30, 2013, "fatfreak82828" wrote "i make my own phishing
sites for darknet .onion drug sites[.] i make $1000 a day[.]"
b.
Later in the same conversation, "fatfreak82828" sent the other chat
participant the usemame, password, and bitcoin address of another individual and wrote "see
those[?] usemame, passwor [sic], pin, balance, and all BTC 4 deposit addresses to a private illegal
site ... when i detect BTC payment there, i login, and withdraw[.] make $1000 day[.] all off 1
phishing site i built myself[.] so i know, how to do this, big time[.] i am prettty big too, but within
TOR network[.]"
BTC is an abbreviation for bitcoin.
10
Case 3:16-mj-00464-SALM Document 1-1 Filed 10/04/16 Page 11 of 15
c.
On December 26, 2013, "fatfreak82828" wrote "i 've been in hacking game
hmm 15 years and before internet 5 years[.] when i was 12 years old i had police called on me for
hacking bbs[.] 5 16 [years old] fbi raided my work iran shellbox in the basement[.]"
d.
Later in the same conversation, "fatfreak82828" wrote "i have 5000 llp's 6
to darknet sites .... i live in a house by myself by the beach drive Mercedes all paid by :) .... i 'd
like to pass my business on and do other work but theres $500,000 a year to be made here[.] im
making $30,000 a month[.] $5,000 a week or so[.]" At another point in the conversation, the other
chat participant asked "fatfreak82828" what he does to make money, and "fatfreak82828"
responded "phish but on darknet websites[.] i set up phish's scam pages for secret web pages[.]"
e.
On December 27, 2013, "fatfreak82828" wrote "i have 5000 lip's to illegal
websites that deal in bitcoin[.] so i write scanners, that beat captcha, and login as each user[.] then
i monitor each adddress and withdraw when they deposit[.] .. made $8700 in 1 minute once[.]"
f.
Later in the same conversation, "fatfreak82828" wrote "i also have much
experience with exploits, scanning, etc, rooting boxes, backdoors[.] i am building a botnet/ for
windows ... last time iran botnet i had 2000 hosts join in 1 day." He further wrote "i do all my
work over TOR[.] most of my attacks are on hidden sites within TOR[.] i run phishing sites that
mimick other TOR sites[.] ... i am writing something new, a botnet, for keylogging, etc."
BBS is an abbreviation for bulletin board system.
Based on my training and experience, I believe "lip" is short for logins and passwords.
Based on my training and experience, I am aware that a botnet is an interconnected network of
computers infected with mal ware without the computer users' knowledge and controlled by
cybercriminals. They are typically used to send spam emails, transmit viruses and engage in
other acts of cybercrimes.
11
Case 3:16-mj-00464-SALM Document 1-1 Filed 10/04/16 Page 12 of 15
24.
In the course of my investigation, I obtained and reviewed records from Local
Bitcoins for the usemame "bmerc" which RICHO stated was his usemame. The records state the
account holder's real name is "Michael Richo" and his email address is mediapenllc@gmail.com.
25.
In my review of the records provided by Local Bitcoins, I observed hundreds of
bitcoin transactions during the period from September 2013 to November 2014, including sales of
bitcoins to other individuals in exchange for U.S. currency. I also obtained and reviewed bank
records for MediaPen LLC at Bank of America and observed numerous deposits of U.S. currency,
some of which correspond to the bitcoin sales I observed in the records from Local Bitcoins. For
example, I observed the following transactions in the records provided by Local Bitcoins and Bank
of America:
a.
On November 5, 2013, there were two bitcoin sale transactions on Local
Bitcoins for $350 and $340. That same day, there were two deposits into the Mediapen's Bank of
America account for $350 and $340 with the description "counter credit."
b.
On November 8, 2013, there were four bitcoin sale transactions on Local
Bitcoins for $200, $350, $999.88, and $1,000. That same day, there were four deposits into the
Mediapen's Bank of America account for $200, $350, $999.88, and $1,000 with the description
"counter credit."
c.
On November 9, 2013, there was a bitcoin sale transaction on Local
Bitcoins for $378. On November 12, 2013, there was a deposit into the Mediapen's Bank of
America account for $378 with the description "counter credit."
d.
On November 12, 2013, there was a bitcoin sale transaction on Local
Bitcoins for $801. That same day, there was a deposit into the Mediapen's Bank of America
account for $801 with the description "counter credit."
12
Case 3:16-mj-00464-SALM Document 1-1 Filed 10/04/16 Page 13 of 15
26.
In total, from November 2013 to October 2014, there were over $100,000 in cash
deposits into Mediapen's Bank of America account, the majority having the description "counter
credit."
27.
Open source records indicate that RICHO currently may be living at an address in
Wallingford, Connecticut. On September 26, 2016, I conducted surveillance of that address and
observed a black Mercedes sedan with a Connecticut license plate parked on the street near the
rear entrance to that address.
According to records provided by the Connecticut Department of
Motor Vehicles ("DMV"), the license plate on the car is registered to a Michael Richo having the
same date ofbirth as the Michael RICHO who is the target of this investigation. The DMV records
list the Wallingford address as RICHO's mailing address. Based on the foregoing information, I
believe RICHO currently resides in Wallingford, Connecticut.
CONCLUSION
28.
Based on the aforementioned information and statements, I believe there is
probable cause that from approximately November 2013 to October 2014, the exact dates being
unknown, in the District of Connecticut, RICHO committed access device fraud, in violation of
18 U.S.C. 1029(a)(3) by possessing fifteen or more unauthorized access devices, namely
usernames and passwords he stole from other individuals through an online phishing scheme, with
intent to defraud. He also committed access device fraud, in violation of 18 U.S.C. 1029(a)(2)
by using one or more of those login credentials to steal more than $1,000 worth of bitcoins from
those other individuals during that period.
29.
Based on the aforementioned information and statements, I further believe there is
probable cause that from approximately November 2013 to October 2014, the exact dates being
unknown, in the District of Connecticut, RICHO committed computer fraud, in violation of 18
13
Case 3:16-mj-00464-SALM Document 1-1 Filed 10/04/16 Page 14 of 15
U.S.C. 1030(a)(2) and (a)(4) by using stolen usemames and passwords to access the bitcoin
accounts of other individuals to obtain more than $5,000 worth of bitcoins during that period.
30.
Based on the aforementioned information and statements, I further believe there is
probable cause that from approximately November 2013 to October 2014, the exact dates being
unknown, in the District of Connecticut, RICHO committed wire fraud, in violation of 18 U.S.C.
1343, by devising and executing a scheme to defraud other individuals and obtain their bitcoins
through materially false representations, namely, using stolen usemames and passwords to login
to their bitcoin accounts via the internet and then transferring the bitcoins to himself and selling
the bitcoins for U.S. currency which was deposited into a bank account he controlled.
31.
Based on the aforementioned information and statements, I further believe there is
probable cause that from approximately November 2013 to October 2014, the exact dates being
unknown, in the District of Connecticut, RICHO committed aggravated identity theft, in violation
of 18 U.S.C. 1028A, by committing access device fraud, computer fraud, and wire fraud, by
using means of identification, that is login credentials, of other individuals.
32.
Finally, based on the aforementioned information and statements, I believe there is
probable cause that from approximately November 2013 to October 2014, the exact dates being
unknown, in the District of Connecticut, RICHO committed money laundering, in violation of 18
U.S.C. 1956(a)(l )(B)(i), by selling the bitcoins he obtained as a result of the aforementioned
violations in exchange for U.S. currency and then causing the currency to be deposited into a bank
account controlled by him in order to conceal or disguise the nature, location, source, ownership
or control of such proceeds.
33.
Therefore, I respectfully request that a criminal complaint be issued to support the
arrest of and to charge RICHO with the TARGET OFFENSES.
14
Case 3:16-mj-00464-SALM Document 1-1 Filed 10/04/16 Page 15 of 15
REQUEST TO SEAL
34.
Because this application pertains to an ongoing criminal investigation, and because
disclosure of the information contained herein as well as disclosure of the arrest warrant and
criminal complaint being requested herein may compromise the investigation, increase the risk of
harm for the law enforcement officers responsible for executing the warrant, and result in the flight
of the target of this investigation, the destruction of evidence, and the tampering with witnesses, I
respectfully request that the criminal complaint and affidavit be ordered sealed until further order
of the Court, except that copies may be provided to other law enforcements agents who are
participating in this investigation, and copies may also be provided to counsel for RICHO
following his arrest and prior to his initial appearance in court.
Subscribed and sworn to before me this
2JC day of October, 2016
/s/ Sarah A. L. Merriam
15
You might also like
- D B: W U W "C " R: ATA Reaches Hat The Nderground Orld of Arding EvealsDocument33 pagesD B: W U W "C " R: ATA Reaches Hat The Nderground Orld of Arding EvealsMalik Tanveer HussainNo ratings yet
- TROVIAS IndictmentDocument20 pagesTROVIAS Indictmentmichaelkan1No ratings yet
- CREDIT CARD Fraud Detection Hidden Markov ModelDocument3 pagesCREDIT CARD Fraud Detection Hidden Markov ModelRameez RashidNo ratings yet
- A Novel Approach To Credit Card Fraud Detection ModelDocument3 pagesA Novel Approach To Credit Card Fraud Detection ModelJournal of ComputingNo ratings yet
- Chimene Hamilton Onyeri IndictmentDocument27 pagesChimene Hamilton Onyeri IndictmentkxanwebteamNo ratings yet
- Ferizi ComplaintDocument40 pagesFerizi ComplaintAdam JanofskyNo ratings yet
- CardConnect Final CC 5Document3 pagesCardConnect Final CC 5Juan Pablo MarinNo ratings yet
- Credit Card Fraud Detection Using Hidden Markov ModelsDocument2 pagesCredit Card Fraud Detection Using Hidden Markov ModelsAbhishek RajNo ratings yet
- Hexaware Annual Report 2014Document140 pagesHexaware Annual Report 2014Kran LinNo ratings yet
- Mobile BankingDocument17 pagesMobile BankingSuchet SinghNo ratings yet
- PayWave IssuerDocument18 pagesPayWave IssuerJagjeet AjmaniNo ratings yet
- Warrants Related To The Charges Against Roanoke City Council Member Robert Jeffrey Jr.Document22 pagesWarrants Related To The Charges Against Roanoke City Council Member Robert Jeffrey Jr.David CrossNo ratings yet
- Deluxe RentAcar's Fraud King and Special Interest's Poster Child For AbuseDocument129 pagesDeluxe RentAcar's Fraud King and Special Interest's Poster Child For Abusetheplatinumlife100% (1)
- 5 6059900569177293719Document76 pages5 6059900569177293719chinna ladduNo ratings yet
- Buchta and Van Rooy Complaint FiledDocument61 pagesBuchta and Van Rooy Complaint FiledSteve WarmbirNo ratings yet
- DoJ Vs RyanMarkGinster Nov 2021Document25 pagesDoJ Vs RyanMarkGinster Nov 2021hyenadogNo ratings yet
- Identity Fraud PresentationDocument6 pagesIdentity Fraud Presentationputi rizna nabilaNo ratings yet
- Statement of Facts - USA Vs Ilya Lichtenstein & Heather Rhiannon MorganDocument20 pagesStatement of Facts - USA Vs Ilya Lichtenstein & Heather Rhiannon MorganhyenadogNo ratings yet
- Business Laws and Company LawsDocument82 pagesBusiness Laws and Company LawsNITISH KUMARNo ratings yet
- Money Mule Recruitment Among University Students in Malaysia Awareness PerspectiveDocument19 pagesMoney Mule Recruitment Among University Students in Malaysia Awareness PerspectiveGlobal Research and Development ServicesNo ratings yet
- Fisco Crypto Exchange V S Binance HoldingDocument33 pagesFisco Crypto Exchange V S Binance HoldingShaurya MalwaNo ratings yet
- PaypalDocument24 pagesPaypalMarine EssenceNo ratings yet
- The Telecheckinternet Check Acceptance and Checks by Phone ServiceDocument1 pageThe Telecheckinternet Check Acceptance and Checks by Phone Serviceaaes2No ratings yet
- Senate Hearing, 109TH Congress - Identity Theft and Data Broker ServicesDocument128 pagesSenate Hearing, 109TH Congress - Identity Theft and Data Broker ServicesScribd Government DocsNo ratings yet
- Credit Card Authorization FormDocument1 pageCredit Card Authorization Formsheshadri_1999No ratings yet
- Charges Against Former Federal Agents in SilkDocument95 pagesCharges Against Former Federal Agents in SilkDeepDotWeb.com100% (1)
- Sonja Emery: Detention Hearing AppealDocument32 pagesSonja Emery: Detention Hearing AppealHLMeditNo ratings yet
- Banks Banking On Security: Bank of AmericaDocument3 pagesBanks Banking On Security: Bank of AmericaJomar MarcillaNo ratings yet
- Cryptocurrency: Presentation: Caib SUBJECT TEACHER: Ma'am Ammara AkramDocument7 pagesCryptocurrency: Presentation: Caib SUBJECT TEACHER: Ma'am Ammara AkramAhmed hassanNo ratings yet
- Hidden Power of The Big Three Passive Index Funds Reconcentration of Corporate Ownership and New Financial RiskDocument29 pagesHidden Power of The Big Three Passive Index Funds Reconcentration of Corporate Ownership and New Financial RiskSteven NguyenNo ratings yet
- Fake Credit Card Number Generator: No, You Can't Really Buy Anything With Them! Nice TryDocument2 pagesFake Credit Card Number Generator: No, You Can't Really Buy Anything With Them! Nice TryEQRFNo ratings yet
- Request For Consultation - Victims ReplyDocument8 pagesRequest For Consultation - Victims ReplyDr. Jonathan Levy, PhDNo ratings yet
- Money: Money Is Any Item or Verifiable Record That Is Generally Accepted As Payment ForDocument13 pagesMoney: Money Is Any Item or Verifiable Record That Is Generally Accepted As Payment ForPat ONo ratings yet
- Payflowgateway GuideDocument256 pagesPayflowgateway GuidejojofunNo ratings yet
- Booter Takedown - Affidavit For Seizure WarrantDocument22 pagesBooter Takedown - Affidavit For Seizure WarrantCatalin Cimpanu [ZDNet]No ratings yet
- Credit CardsDocument26 pagesCredit CardsPranav JadavNo ratings yet
- The Financial Services Fact Book 2013Document263 pagesThe Financial Services Fact Book 2013Jay KabNo ratings yet
- Mosley Cracking Cards ComplaintDocument16 pagesMosley Cracking Cards ComplaintSteve WarmbirNo ratings yet
- Indicators of Suspicious TransactionsDocument3 pagesIndicators of Suspicious TransactionsArtūras CimbalistasNo ratings yet
- WoodfordDocument4 pagesWoodfordDestiny RiveraNo ratings yet
- Distributed Data Mining in Credit Card Fraud DetectionDocument57 pagesDistributed Data Mining in Credit Card Fraud DetectionPankaj GorasiyaNo ratings yet
- US V Wallstreet Market Criminal ComplaintDocument34 pagesUS V Wallstreet Market Criminal ComplaintCalebNo ratings yet
- Honest Mining $HNST White PaperDocument34 pagesHonest Mining $HNST White PaperolentzNo ratings yet
- 10 Merchant BankingDocument68 pages10 Merchant Bankingpoojamacwan67% (3)
- HDFC Credit Card Charge DetailsDocument11 pagesHDFC Credit Card Charge DetailsVarun G ShenoyNo ratings yet
- Bank Fraud: Kes College of Arts & Commerce Fraud in BankDocument49 pagesBank Fraud: Kes College of Arts & Commerce Fraud in BankNehal ShahNo ratings yet
- Credit CardDocument6 pagesCredit Cardredwanur_rahman2002No ratings yet
- India-Russia RelationsDocument12 pagesIndia-Russia Relationspapa mote haiNo ratings yet
- A Blockchain-Based Application System For Product Anti-CounterfeitingDocument11 pagesA Blockchain-Based Application System For Product Anti-Counterfeitingsailesh111@gmail.comNo ratings yet
- United States v. Elton Lee Flenaugh, 11th Cir. (2015)Document5 pagesUnited States v. Elton Lee Flenaugh, 11th Cir. (2015)Scribd Government DocsNo ratings yet
- RFID Payment Card Vulnerabilities Technical ReportDocument6 pagesRFID Payment Card Vulnerabilities Technical Reportgargy2512No ratings yet
- Digital Fraud in Australian Corporate & GovernmentDocument4 pagesDigital Fraud in Australian Corporate & GovernmentArk GroupNo ratings yet
- Prepaid Cards For Transit Agencies 20110212Document38 pagesPrepaid Cards For Transit Agencies 20110212amolnatuNo ratings yet
- E Frauds in BankingDocument5 pagesE Frauds in BankingRajivNo ratings yet
- Lichtenstein and Morgan - Statement of FactsDocument20 pagesLichtenstein and Morgan - Statement of FactsMatt Troutman100% (1)
- OWASPLondon 20180125leigh Anne Galloway TYunusov Buy Hack ATMDocument57 pagesOWASPLondon 20180125leigh Anne Galloway TYunusov Buy Hack ATMBoby JosephNo ratings yet
- Bitcoin Explained: Beginner’s Guide To Understanding BitcoinFrom EverandBitcoin Explained: Beginner’s Guide To Understanding BitcoinNo ratings yet
- ATM Explosive Attacks Surge in Europe For Release To The Media On 14th October 2016Document2 pagesATM Explosive Attacks Surge in Europe For Release To The Media On 14th October 2016SoftpediaNo ratings yet
- Buchta and Van Rooy ComplaintDocument61 pagesBuchta and Van Rooy ComplaintSoftpediaNo ratings yet
- Final GOP Interim Staff Report 7-12-16Document25 pagesFinal GOP Interim Staff Report 7-12-16SoftpediaNo ratings yet
- Boggs Liverman - Complaint Affidavit SignedDocument37 pagesBoggs Liverman - Complaint Affidavit SignedSoftpediaNo ratings yet
- Intel McAfee 1-MainDocument19 pagesIntel McAfee 1-MainJordan NovetNo ratings yet
- Music Industry LawsuitDocument39 pagesMusic Industry LawsuitmashablescribdNo ratings yet
- Hpsci Snowden Review - Unclass Summary - FinalDocument4 pagesHpsci Snowden Review - Unclass Summary - FinalQuintaJurecicNo ratings yet
- US v. Nosal - 9th Circuit July 5, 2016 PDFDocument67 pagesUS v. Nosal - 9th Circuit July 5, 2016 PDFMark JaffeNo ratings yet
- Artem Vaulin KickassTorrents LawsuitDocument50 pagesArtem Vaulin KickassTorrents LawsuitStephanie Dube DwilsonNo ratings yet
- Mobile Advertising Network InMobi Settles FTC Charges It Tracked Hundreds of Millions of Consumers' Locations Without PermissionDocument17 pagesMobile Advertising Network InMobi Settles FTC Charges It Tracked Hundreds of Millions of Consumers' Locations Without PermissionSoftpediaNo ratings yet
- PayPal PatentDocument32 pagesPayPal PatentSoftpediaNo ratings yet
- Iermolovychvadym InformationDocument19 pagesIermolovychvadym InformationSoftpediaNo ratings yet
- Acer Customer Notice Letter - CaliforniaDocument2 pagesAcer Customer Notice Letter - CaliforniaSoftpediaNo ratings yet
- Wire Swiss GMBH v. Quiet Riddle Ventures, LLCDocument10 pagesWire Swiss GMBH v. Quiet Riddle Ventures, LLCSoftpediaNo ratings yet
- A Call For A Temporary Moratorium On "The DAO"Document13 pagesA Call For A Temporary Moratorium On "The DAO"SoftpediaNo ratings yet
- Google - Individual Notification Letter (California) - 0Document4 pagesGoogle - Individual Notification Letter (California) - 0SoftpediaNo ratings yet
- Burr Encryption Bill - Discussion DraftDocument9 pagesBurr Encryption Bill - Discussion DraftCory Bennett13% (8)
- FBI Letter To Senator WydenDocument6 pagesFBI Letter To Senator WydenSoftpediaNo ratings yet
- FBI SmartFarmHackingDocument6 pagesFBI SmartFarmHackingSoftpediaNo ratings yet
- NPM Hydra WormDocument4 pagesNPM Hydra WormSoftpediaNo ratings yet
- CV-02464-GMN-PAL (Affinity Vs Trustwave)Document26 pagesCV-02464-GMN-PAL (Affinity Vs Trustwave)SoftpediaNo ratings yet
- PDF 0090 Fcra 609eDocument2 pagesPDF 0090 Fcra 609eNotarys To GoNo ratings yet
- IRS Form F3949ADocument2 pagesIRS Form F3949APolarik100% (1)
- Evgeniy Mikhailovich Bogachev - FBI Most Wanted HackerDocument2 pagesEvgeniy Mikhailovich Bogachev - FBI Most Wanted Hackerharsha89No ratings yet
- Cyber Crimes: or Computer-Oriented CrimeDocument2 pagesCyber Crimes: or Computer-Oriented CrimeAyanna Grace FrondaNo ratings yet
- Irresponsible Used of Social Media Can Harm Your ChildDocument2 pagesIrresponsible Used of Social Media Can Harm Your ChildGhieya GregorioNo ratings yet
- Financial Cyber CrimeDocument10 pagesFinancial Cyber Crimebehappy_aklprasadNo ratings yet
- Template Scam ReplyDocument3 pagesTemplate Scam ReplyDUTCH551400No ratings yet
- Notification From The Cedar Rapids Community School DistrictDocument8 pagesNotification From The Cedar Rapids Community School DistrictEthan SteinNo ratings yet
- Chapter One 1.1 Background of The StudyDocument18 pagesChapter One 1.1 Background of The StudypeterNo ratings yet
- Detection of Fake Profiles in Social Media: Literature ReviewDocument7 pagesDetection of Fake Profiles in Social Media: Literature ReviewRicha GargNo ratings yet
- Cybersecurity Training:: Safeguarding Our Firm and Client AssetsDocument44 pagesCybersecurity Training:: Safeguarding Our Firm and Client AssetsWisnu AjiNo ratings yet
- Paragraf Tamamlama 003 AKIN DILDocument3 pagesParagraf Tamamlama 003 AKIN DILMurat YamanNo ratings yet
- Beware of Fraud and Scam ArtistsDocument2 pagesBeware of Fraud and Scam ArtistsSelahNo ratings yet
- Gee1 SG5Document5 pagesGee1 SG5Jhasmine CorpuzNo ratings yet
- Credit Fraud Detection: Project ReportDocument22 pagesCredit Fraud Detection: Project ReportForam ThakkarNo ratings yet
- IRS Form W-9Document8 pagesIRS Form W-9SAHASec8No ratings yet
- Hacking and Cyber LawDocument12 pagesHacking and Cyber LawChirag ManchandaNo ratings yet
- MasterCard Debit Card Benefits BrochureDocument7 pagesMasterCard Debit Card Benefits BrochureENUNo ratings yet
- IDENTITY THEFT Is A Crime in Which An Impostor Obtains Key Pieces of Personal IdentifyingDocument3 pagesIDENTITY THEFT Is A Crime in Which An Impostor Obtains Key Pieces of Personal IdentifyingSuper RomeNo ratings yet
- Fraud and Scams in Banking SectorDocument90 pagesFraud and Scams in Banking SectorDdjgirish GavankarNo ratings yet
- Digital RobberyDocument16 pagesDigital RobberyAakrisht GoelNo ratings yet
- All DPS Docs CombinedDocument35 pagesAll DPS Docs Combinedmtrahan5075No ratings yet
- Jose Rizal Memorial State University: Republic of The Philippines Dipolog Campus, Dipolog CityDocument9 pagesJose Rizal Memorial State University: Republic of The Philippines Dipolog Campus, Dipolog CityJen PaezNo ratings yet
- CyberDocument11 pagesCyberMomoh GaiusNo ratings yet
- List of FBI - Interpol ContactsDocument38 pagesList of FBI - Interpol ContactsEyemanProphetNo ratings yet
- LifeLock Presentation - How LifeLock WorksDocument10 pagesLifeLock Presentation - How LifeLock WorksJohn BerkowitzNo ratings yet
- Social Contract Theory AnalysisDocument24 pagesSocial Contract Theory AnalysisGhulamNo ratings yet
- What Is Fair TradeDocument9 pagesWhat Is Fair TradeprofessorchanakyaNo ratings yet
- Identity Theft WebquestDocument2 pagesIdentity Theft Webquestapi-256439505No ratings yet
- Dealing With A Debt Collector Can Be One of LifeDocument25 pagesDealing With A Debt Collector Can Be One of LifeDan Clement100% (1)