Professional Documents
Culture Documents
Ransomware
Uploaded by
Muhammad Adeel0 ratings0% found this document useful (0 votes)
11 views1 pageOriginal Title
ransomware.txt
Copyright
© © All Rights Reserved
Available Formats
TXT, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as TXT, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
11 views1 pageRansomware
Uploaded by
Muhammad AdeelCopyright:
© All Rights Reserved
Available Formats
Download as TXT, PDF, TXT or read online from Scribd
You are on page 1of 1
Block SMB access to the Internet, which runs over TCP ports 137, 139, 445 and UDP
ports 137, 138.
Apply the Microsoft patch for the MS17-010 SMB vulnerability dated March 14, 2017.
Filter and monitor email for phishing attacks, watching for inbound executable and
macro-enabled attachments.
Utilize least privilege by giving users access only to the resources they need to
conduct their jobs to contain damage from a compromised user account.
Reduce and restrict full administrative privileges. Segregate administrative
accounts from system administrators and from the user accounts they use to read
email and surf the web. Also, restrict common administrative access to TCP ports
such as 22, 23, and 3389.
Configure internal access controls to contain infection contagion within the
networks. Block or restrict SMB (TCP ports 137, 139, 445 and UDP ports 137, 138).
Send internal flash bulletins to users regarding this outbreak, warning them to
beware of attachments as well as cautioning them not to bring in possible infected
outside devices (teleworkers, vendors, home computers) to the office network.
Perform and test backups regularly.
You might also like
- Docker NotesDocument1 pageDocker NotesMuhammad AdeelNo ratings yet
- Ransom WareDocument1 pageRansom WareMuhammad AdeelNo ratings yet
- NTS GAT (General) GUIDE BOOK by DOGAR PUBLISHER PDFDocument372 pagesNTS GAT (General) GUIDE BOOK by DOGAR PUBLISHER PDFwaqasahmadz86% (977)
- Computer Science MSQsDocument27 pagesComputer Science MSQsMuhammad AdeelNo ratings yet
- Sebata SLADocument51 pagesSebata SLAMuhammad AdeelNo ratings yet
- ADB Flood Project Application FormDocument1 pageADB Flood Project Application FormMuhammad AdeelNo ratings yet
- Fme Understanding Emotional Intelligence PDFDocument50 pagesFme Understanding Emotional Intelligence PDFrgscribd61No ratings yet
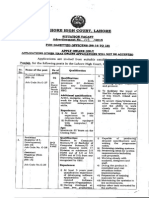
- Advertisement 1Document10 pagesAdvertisement 1Muhammad AdeelNo ratings yet
- Strategic Procurement Plan TemplateDocument9 pagesStrategic Procurement Plan TemplateMuhammad AdeelNo ratings yet
- OrientDocument1 pageOrientMuhammad AdeelNo ratings yet
- AdvtNo10 2015Document3 pagesAdvtNo10 2015Almas KhanNo ratings yet
- Network Management GuideDocument200 pagesNetwork Management GuidePavan NavNo ratings yet
- Cucm Licence BreakingDocument4 pagesCucm Licence BreakingMuhammad Adeel0% (1)
- NTS Book For GAT GeneralDocument142 pagesNTS Book For GAT GeneralMuzaffar AhsanNo ratings yet
- CEH v8 Labs Module 00Document4 pagesCEH v8 Labs Module 00ariesshtNo ratings yet
- CEHv8 BrochureDocument12 pagesCEHv8 BrochurePró EstudoNo ratings yet
- BayanDocument1 pageBayanMuhammad AdeelNo ratings yet
- Clientless SSL VPN (Webvpn) On Cisco Ios Using SDM Configuration ExampleDocument22 pagesClientless SSL VPN (Webvpn) On Cisco Ios Using SDM Configuration ExampleMuhammad AdeelNo ratings yet
- LDA Ad PDFDocument2 pagesLDA Ad PDFMuhammad AdeelNo ratings yet
- Cucm Licence BreakingDocument4 pagesCucm Licence BreakingMuhammad Adeel0% (1)
- CorelDRAW Graphics Suite X5Document1 pageCorelDRAW Graphics Suite X5Muhammad AdeelNo ratings yet
- CS302 Fall 2012 Assignment No. 2: Due DateDocument2 pagesCS302 Fall 2012 Assignment No. 2: Due DateMuhammad AdeelNo ratings yet
- Sap Abap Training MaterialsDocument3 pagesSap Abap Training MaterialsNarayanasamy SubramaniamNo ratings yet
- SPDDocument6 pagesSPDMuhammad AdeelNo ratings yet
- 3C17700DataSheet PDFDocument2 pages3C17700DataSheet PDFMuhammad AdeelNo ratings yet
- Fiberlink (PVT.) LTD: Karachi Lahore Islamabad Multan HyderabadDocument8 pagesFiberlink (PVT.) LTD: Karachi Lahore Islamabad Multan HyderabadMuhammad AdeelNo ratings yet
- 50 Worst of The Worst and Most Common Job Interview MistakesDocument3 pages50 Worst of The Worst and Most Common Job Interview MistakesMuhammad AdeelNo ratings yet
- Cisco 79xx Password ResetDocument6 pagesCisco 79xx Password ResetMuhammad AdeelNo ratings yet
- Ethernet Gersis GMBH DsDocument93 pagesEthernet Gersis GMBH DsMuhammad AdeelNo ratings yet
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)