Professional Documents
Culture Documents
(An Autonomous Institution) : Page 1 of 1
(An Autonomous Institution) : Page 1 of 1
Uploaded by
kavya0 ratings0% found this document useful (0 votes)
18 views1 pageThis document is an exam for a networking security course, with two parts testing objective and descriptive questions. Part A contains 4 multiple choice or short answer questions worth 1 mark each on the topics of RADIUS, WEP keys, 2G technology drawbacks, and phishing. Part B requires answering 3 of 4 longer questions worth 4 marks each, covering data protection in TKIP, authentication and key agreement in 3G, ARP spoofing, and explaining the GSM network architecture.
Original Description:
Original Title
1st internal.docx
Copyright
© © All Rights Reserved
Available Formats
DOCX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThis document is an exam for a networking security course, with two parts testing objective and descriptive questions. Part A contains 4 multiple choice or short answer questions worth 1 mark each on the topics of RADIUS, WEP keys, 2G technology drawbacks, and phishing. Part B requires answering 3 of 4 longer questions worth 4 marks each, covering data protection in TKIP, authentication and key agreement in 3G, ARP spoofing, and explaining the GSM network architecture.
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
18 views1 page(An Autonomous Institution) : Page 1 of 1
(An Autonomous Institution) : Page 1 of 1
Uploaded by
kavyaThis document is an exam for a networking security course, with two parts testing objective and descriptive questions. Part A contains 4 multiple choice or short answer questions worth 1 mark each on the topics of RADIUS, WEP keys, 2G technology drawbacks, and phishing. Part B requires answering 3 of 4 longer questions worth 4 marks each, covering data protection in TKIP, authentication and key agreement in 3G, ARP spoofing, and explaining the GSM network architecture.
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
You are on page 1of 1
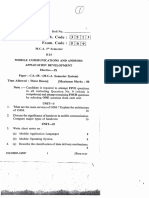
Sreenidhi Institute of Science and Technology
(An Autonomous Institution)
Code No: 5R211
M. TECH. IYear IISemester I InternalExaminations
APPLICATIONS OF NETWORK SECURITY (CNIS)
Time: 2 Hours Max. Marks: 16
Note: No additional answer sheets will be provided.
Part - A (Objective Type)
Max.Marks:4
ANSWER ALL QUESTIONS. EACH QUESTION CARRIES 2&3 MARK.
1. What is the full form of RADIUS? (1M)
2. List out any 3 keys used in WEP? (1M)
3. Drawbacks of 2G Technology? (1M)
4. What is Phishing? (1M)
Part B
Max. Marks: 12
ANSWER ANY THREE QUESTIONS. EACH QUESTION CARRIES 4 MARKS.
1. Describe the Data protection in TKIP.
2. Explain about authentication and Key agreement in UMTS (3G).
3. Describe ARP Spoofing.
4. Draw the architecture of GSM and explain each entity.
-- 00 -- 00
Page 1 of 1
You might also like
- Ict Elective SyllabusDocument52 pagesIct Elective SyllabusAda TechNo ratings yet
- Jntuk M Tech r16 Cse&it Syllabus PDFDocument197 pagesJntuk M Tech r16 Cse&it Syllabus PDFAbhijeet SinghNo ratings yet
- Diploma 6th Sem Model Answer PaperDocument26 pagesDiploma 6th Sem Model Answer Paperommane31200375% (4)
- Sy Comp Sem Iv DCC 22414 QP Model AnswersDocument50 pagesSy Comp Sem Iv DCC 22414 QP Model Answerstanmayghanekar28No ratings yet
- S23 CND 22634Document27 pagesS23 CND 22634harshy0816100% (1)
- CS Question PapersDocument6 pagesCS Question PapersAK BROSNo ratings yet
- Model Answers Summer 2019Document17 pagesModel Answers Summer 2019IF -Nikita GhuleNo ratings yet
- Diploma 6th Sem Model Answer Paper. 22620 - Diploma 6th Sem Model Answer PaperDocument26 pagesDiploma 6th Sem Model Answer Paper. 22620 - Diploma 6th Sem Model Answer PaperVishnu MaskarNo ratings yet
- Case Study Sample 2Document3 pagesCase Study Sample 2kamgangsjbebNo ratings yet
- S23 Model SolutionDocument25 pagesS23 Model Solutiontanupandav333No ratings yet
- Important Instructions To Examiners:: Maharashtra State Board of Technical Education (ISO/IEC - 27001 - 2013 Certified)Document18 pagesImportant Instructions To Examiners:: Maharashtra State Board of Technical Education (ISO/IEC - 27001 - 2013 Certified)Ram PNo ratings yet
- WMN Model Summer-23Document19 pagesWMN Model Summer-23navteshdeore19100% (3)
- 2018 Winter Model Answer PaperDocument14 pages2018 Winter Model Answer Paperharshsuryawanshi2021No ratings yet
- Model Answer Paper Winter 2019Document26 pagesModel Answer Paper Winter 2019Satyam MarotheNo ratings yet
- B.Tech IV Year I Semester (R15) Regular Examinations November/December 2018Document5 pagesB.Tech IV Year I Semester (R15) Regular Examinations November/December 2018pruthviNo ratings yet
- Wa0001.Document2 pagesWa0001.NISHANTH M0% (1)
- 22634-2022-Winter-Model-Answer-Paper (Msbte Study Resources)Document25 pages22634-2022-Winter-Model-Answer-Paper (Msbte Study Resources)ashusonkamble979No ratings yet
- Bca Part 2 Computer Networks LJ 1245 2021Document3 pagesBca Part 2 Computer Networks LJ 1245 2021Hermione's XtacyNo ratings yet
- De ThiDocument2 pagesDe ThihuynhcongthienttttNo ratings yet
- CN Mid Paper Fall 19Document1 pageCN Mid Paper Fall 19Wajid AbbasNo ratings yet
- DCN Winter2019Document27 pagesDCN Winter2019Sanskar NimjeNo ratings yet
- Fundamentals of Networking Assignemnt CDocument1 pageFundamentals of Networking Assignemnt Cabelcreed1994No ratings yet
- Important Instructions To Examiners:: (Autonomous)Document25 pagesImportant Instructions To Examiners:: (Autonomous)Vaibhav BhagwatNo ratings yet
- 10 ICT - English Medium - FinalDocument10 pages10 ICT - English Medium - Finalthusharagomas18No ratings yet
- GEC-R14 Internet of Things: H.T.No. Code No: EC1566 IV B. Tech II Semester Regular Examinations, April 2018Document1 pageGEC-R14 Internet of Things: H.T.No. Code No: EC1566 IV B. Tech II Semester Regular Examinations, April 2018ashleyNo ratings yet
- Cs 2019Document4 pagesCs 2019Durgesh KollaNo ratings yet
- 2019 Summer OrganizedDocument18 pages2019 Summer Organizedsayedshaad02No ratings yet
- Cdma Securit Y: An IntelligenceDocument27 pagesCdma Securit Y: An IntelligenceAshour AlmejrabNo ratings yet
- NR-320502 Computer NetworksDocument6 pagesNR-320502 Computer NetworksSrinivasa Rao G100% (2)
- Cyber Threat and VulnerabilitiesDocument1 pageCyber Threat and VulnerabilitiesMBIEDA NGOMEGNI FRANK GAETANNo ratings yet
- WWW - Manaresults.Co - In: Code: 13A12804Document1 pageWWW - Manaresults.Co - In: Code: 13A12804Chitra Madhuri YashodaNo ratings yet
- 420240-DCC w23, s23, w22, s22, w19, s19Document148 pages420240-DCC w23, s23, w22, s22, w19, s19hackermh862No ratings yet
- MuhamadAzrulbinAmir LabTestSecurity 5ADocument10 pagesMuhamadAzrulbinAmir LabTestSecurity 5Aazrul amir100% (1)
- Important Instructions To Examiners:: Q. No Sub Q.N. Answer Marking SchemeDocument28 pagesImportant Instructions To Examiners:: Q. No Sub Q.N. Answer Marking Schemeavadhutc879100% (1)
- Blue Print IP XII 2023-24Document1 pageBlue Print IP XII 2023-24Naren Kumar0% (1)
- CNS Theory Syllabus PDFDocument3 pagesCNS Theory Syllabus PDFnootiNo ratings yet
- Msbte w22 22417Document21 pagesMsbte w22 22417jacksparrowcom4100% (1)
- ITT420 - Kuiz 2Document5 pagesITT420 - Kuiz 2Hafiz Blm'ersNo ratings yet
- 4 DcoDocument62 pages4 DcoSachin KondawarNo ratings yet
- Model Answer Winter 2019Document22 pagesModel Answer Winter 2019IF21 Minit ChitrodaNo ratings yet
- 6th Sem Pyq'sDocument17 pages6th Sem Pyq'sManeeshMahajanNo ratings yet
- ACN s23Document29 pagesACN s23kalpakpatil2004No ratings yet
- dad87e21EP Mid Sem 2019Document2 pagesdad87e21EP Mid Sem 2019Aayush Kumar SinghNo ratings yet
- 2015 Winter Model Answer PaperDocument31 pages2015 Winter Model Answer PaperVaishnavi KadamNo ratings yet
- DCC Winter 22 Removed OrganizedDocument24 pagesDCC Winter 22 Removed Organizedsayedshaad02No ratings yet
- Wireless Data Encryption & Decryption PPT'S by G.ajay KumarDocument17 pagesWireless Data Encryption & Decryption PPT'S by G.ajay KumarAjay Kumar Gajula0% (1)
- Midterm Exam 467Document2 pagesMidterm Exam 467Faisal ShahbazNo ratings yet
- BCC 301 AssignmentDocument2 pagesBCC 301 Assignmentitsm8011No ratings yet
- r7411206 Information SecurityDocument4 pagesr7411206 Information SecuritysivabharathamurthyNo ratings yet
- Diploma in Computer Application (Second Semester) Examination, February 2019Document3 pagesDiploma in Computer Application (Second Semester) Examination, February 2019Kamta Prasad PatelNo ratings yet
- SRM University Department of Information Technology Lesson PlanDocument4 pagesSRM University Department of Information Technology Lesson PlanRehanNo ratings yet
- Lin Huan - UE SecurityDocument36 pagesLin Huan - UE SecurityFizz FizzNo ratings yet
- 2019 Summer Model Answer Paper (Msbte Study R - 230223 - 195923Document33 pages2019 Summer Model Answer Paper (Msbte Study R - 230223 - 195923Akshay KhaladkarNo ratings yet
- CSEC IT June 2011 Paper 2Document9 pagesCSEC IT June 2011 Paper 2bogobo2689No ratings yet
- DL Mid 2Document1 pageDL Mid 2Vadlamudi DhyanamalikaNo ratings yet
- Mobile CommunicationsDocument12 pagesMobile CommunicationsmohitNo ratings yet
- Keselamatan Teknologi Maklumat Information Technology SecurityDocument9 pagesKeselamatan Teknologi Maklumat Information Technology SecurityKiera ShakiraNo ratings yet
- Introduction To IctDocument1 pageIntroduction To IctBrian musyokiNo ratings yet
- Telecommunications: Present Status and Future TrendsFrom EverandTelecommunications: Present Status and Future TrendsRating: 4.5 out of 5 stars4.5/5 (2)