Professional Documents
Culture Documents
ISE Dashboards Overview
Uploaded by
Tanveer AkhtarOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
ISE Dashboards Overview
Uploaded by
Tanveer AkhtarCopyright:
Available Formats
Metrics:
Shows a high-level summary of how many endpoints are active, how many active guests exist,
the profiled endpoints, as well as posture compliance.
System Summary:
Provides a quick overview of all ISE appliances within the deployment. This summary includes
the health status, CPU level, memory usage, and authentication latency for each ISE appliance.
Alarms:
Provides any alarms or anomalous behaviors that have been seen by ISE. A few examples of
alarms may be authentication inactivity, NTP sync issues, or insufficient virtual machine
resources, just to name a few.
1 | P a g e Prepared By Ahmad Ali, Email: ahmadalimsc@gmail.com , Mobile# 0564303717
Authentications:
Provides a 24-hour and 60-minute summary of the ISE passed and failed authentications,
providing a distribution between identity store, identity group, network device, location, and
failure reason (if applicable).
Profiler Activity:
If profiling is enabled, this dashlet provides a 24-hour and 60-minute overview of which
endpoint profile or identity group the endpoints were profiled.
Posture Compliance:
This pane provides the posture status of endpoints, highlighting the distribution based on
profile status as well as operating system.
2 | P a g e Prepared By Ahmad Ali, Email: ahmadalimsc@gmail.com , Mobile# 0564303717
Setup Assistant:
The Setup Assistant link can be used to do an initial configuration of the Cisco ISE. The Setup
Assistant guides through a series of questions to configure the basic functionality of Cisco ISE.
Server Information:
The hostname of the ISE appliance that is currently being viewed. The information given in this
Server Information.
Personas: The active personas on the current ISE appliance.
Role: Whether this ISE is currently in a standalone, primary, or secondary role.
System Time: The current time as seen by the current ISE appliance.
FIPS Mode: If the current ISE node is running in FIPS compliant mode, it is indicated here.
Version: The current version of ISE that is running.
Patch Information: If there is a system patch that has been installed, it is indicated here.
3 | P a g e Prepared By Ahmad Ali, Email: ahmadalimsc@gmail.com , Mobile# 0564303717
Monitoring Node (MnT):
The Monitoring Node is where all the logs are collected and where report generation occurs.
Every event that occurs within the ISE topology is logged to the monitoring node then generate
reports showing the current status of connected devices & unknown devices on your network.
Policy Administration Node (PAN):
The Policy Administration Node is where the administrator logs into to configure policies &
make changes to the entire ISE system. Once configured on the PAN the changes are pushed
out to the policy services nodes. It handles all system related configurations and can be
configured as standalone, primary or secondary. This service provide the GUI of the device.
4 | P a g e Prepared By Ahmad Ali, Email: ahmadalimsc@gmail.com , Mobile# 0564303717
Policy Services Node (PSN):
The Policy Services Node is the contact point into the network. Each switch is configured to
query a radius server to get the policy decision to apply to the network port the radius server is
the PSN. In larger deployments you use multiple PSN’s to spread the load of all the network
requests. The PSN provides network access, posture, guest access, and client provisioning, and
profiling services. There must be at least one PSN in a distributed setup.
5 | P a g e Prepared By Ahmad Ali, Email: ahmadalimsc@gmail.com , Mobile# 0564303717
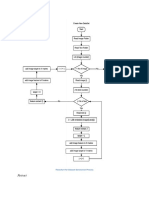
Graphical User Interface of Cisco ISE:
Cisco ISE GUI is divided into three functional components Operations, Policy, & Administration.
Operations:
Operations are those components of ISE that enable administrator to actively monitor, report,
and troubleshoot ongoing authentication and authorization sessions. It is also a place where
the administrator can monitor, report, and troubleshoot those network devices and policies
that are already configured on ISE.
Policy:
Policy functions are those components of ISE that allow the administrator to configure the
security policy. These policy functions include authentication, authorization, profiling, posture,
client provisioning, and security group access policy. As a network device authenticates and
authorizes to ISE, ISE processes the credentials provided by the NAD through this policy,
providing the resulting authorization security policy back to the NAD.
Administration:
Administration focuses on the configuration of the ISE component itself—what, who, and how
users and devices can access ISE. This configuration section of ISE enables the administrator to
define how the ISE deployment behaves, which external identity resources are going to be
used, which devices are allowed to use the ISE security policy, which services ISE will provide to
the user base, and how often ISE will update its device databases.
6 | P a g e Prepared By Ahmad Ali, Email: ahmadalimsc@gmail.com , Mobile# 0564303717
Guest Access:
Guest Access is the New Tabs added to the GUI of ISE 2. Guest Access Tab is something new in
Cisco ISE 2. All Sponsor and Guest portal related settings are available at same place.
7 | P a g e Prepared By Ahmad Ali, Email: ahmadalimsc@gmail.com , Mobile# 0564303717
Work Centers:
The Work Center menu contains all the device administration pages, which acts as a single start
point for ISE administrators. However, pages that are not specific to device administration such
as Users, User Identity Groups, Network Devices, Default Network Devices, Network Device
Groups, Authentication and Authorization Conditions, can still be accessed from their original
menu options, such as Administration.
RADIUS Livelog:
o RADIUS Livelog displays the recent RADIUS authentications.
o Monitor recent RADIUS authentications as they happen.
o Also shows the live session entries corresponding to the events.
o Can drill-down the desired session to view a detailed report to that session.
o The Live Authentications page provides a tabular account of recent RADIUS authentications.
8 | P a g e Prepared By Ahmad Ali, Email: ahmadalimsc@gmail.com , Mobile# 0564303717
Options Description
Time Shows the time that the log was received by the monitoring and
troubleshooting collection agent. This column is required and
cannot be deselected.
Status Shows if the authentication was successful or a failure. This
column is required and cannot be deselected. Green is used to
represent passed authentications. Red is used to represent
failed authentications.
Details Brings up a report when you click the magnifying glass icon,
allowing you to drill down and view more detailed information
on the selected authentication scenario. This column is required
and cannot be deselected.
Repeat Count Shows the number of time the authentication requests were
repeated in last 24 hours.
Identity Shows the username that is associated with the authentication.
Endpoint ID Shows the unique identifier for an endpoint, usually a MAC or IP
address.
Endpoint Profile Shows the type of endpoint that is profiled, for example,
profiled to be an iPhone, Android, MacBook, Xbox, and so on.
Authentication Shows the name of the policy selected for specific
Policy authentication.
Authorization Shows the name of the policy selected for specific authorization.
Policy
Authorization Shows an authorization profile that was used for authentication.
Profiles
IP Address Shows the IP address of the endpoint device.
Network Device Shows the IP address of the Network Access Device.
Device Port Shows the port number at which the endpoint is connected.
Identity Group Shows the identity group that is assigned to the user or
endpoint, for which the log was generated.
Posture Status Shows status of posture validation & details on authentication.
Server Indicates the Policy Service from which the log was generated.
MDM Server Shows the names of the MDM servers.
Name
Event Shows the event status.
Failure Reason Shows a detailed reason for failure, if the authentication failed.
Auth Method Shows authentication method that is used by the RADIUS.
Authentication Shows the authentication protocol used, such as Protected
Protocol Extensible Authentication Protocol (PEAP), EPEAP
Security Group Shows the group that is identified by the authentication log.
Session ID Shows the session ID.
9 | P a g e Prepared By Ahmad Ali, Email: ahmadalimsc@gmail.com , Mobile# 0564303717
Reports:
o Reports is a place to generate reports for ISE functions and sessions.
o Cisco ISE reports are preconfigured and grouped into logical categories.
o Reports includes information related to authentication & session traffic.
o Reports also includes device admin, configuration & administration & troubleshooting.
o The Adaptive Network Control Audit report is based on the RADIUS accounting.
o It displays historical reporting of all network sessions for each endpoint.
o The Administrator Logins report provides an audit trail of all administrator logins.
o The Change Configuration Audit report provides details about configuration changes.
o This report will allow ISE administrators to identify any issues with TACACS Accounting.
o AAA Diagnostics report provides details of all network sessions between Cisco ISE and users.
Troubleshooting Tools:
o Diagnostic tools help you diagnose and troubleshoot problems on a Cisco ISE
o Diagnostic tools provide a detailed instructions on how to resolve problems.
o RADIUS Authentication Troubleshooting Settings allow to identify problems.
o RADIUS Authentication Troubleshooting Settings resolve authentication problems.
o Use to monitor contents of packets on a network interface & troubleshoot problems.
10 | P a g e Prepared By Ahmad Ali, Email: ahmadalimsc@gmail.com , Mobile# 0564303717
Authentication:
o Authentication of Policy provides interface to configure authentication policies.
o Authentication policy defines the rules by which ISE identifies the user.
o Authentication allows you to configure simple and rule-based authentication policies.
11 | P a g e Prepared By Ahmad Ali, Email: ahmadalimsc@gmail.com , Mobile# 0564303717
Authorization:
o Authorization is the process of determining what an endpoint device will have access.
o The Authorization page display, create, duplicate, modify, or delete authorization policies.
Profiling:
o Profiling Policies page displays endpoint-profiling policies with their names.
o Profiling Policies page displays endpoint type, description and the status.
o Cisco ISE includes predefined default profiling policies when Cisco ISE is deployed.
12 | P a g e Prepared By Ahmad Ali, Email: ahmadalimsc@gmail.com , Mobile# 0564303717
Posture:
o ISE is mainly use for posturing & policy compliance checking of hosts.
o Posturing check health of endpoints like antivirus, latest service pack & OS updates.
o Detailed information about the endpoint’s software and hardware configuration.
13 | P a g e Prepared By Ahmad Ali, Email: ahmadalimsc@gmail.com , Mobile# 0564303717
You might also like
- 300-425 Designing Cisco Enterprise Wireless Networks (ENWLSD) Exam QuestionsDocument5 pages300-425 Designing Cisco Enterprise Wireless Networks (ENWLSD) Exam QuestionsMohammed AbdElwhab MadaniNo ratings yet
- Cisco ISE logs authentication of user mydoganDocument3 pagesCisco ISE logs authentication of user mydogangolge_manNo ratings yet
- Firepower Release Notes, Version 6.6.1 and 6.6.3Document88 pagesFirepower Release Notes, Version 6.6.1 and 6.6.3Tim BurchmoreNo ratings yet
- EAP ProtocolDocument7 pagesEAP ProtocolVladianu DanNo ratings yet
- Identity Services Engine (ISE)Document33 pagesIdentity Services Engine (ISE)Vk VNo ratings yet
- Cisco Unified Wireless Network Solution OverviewDocument20 pagesCisco Unified Wireless Network Solution OverviewPaul CherresNo ratings yet
- 02 Network Reference ModelDocument41 pages02 Network Reference ModelnjimeliabdelNo ratings yet
- Configuringme: Configuring Wired 8021x Authentication On Windows Server 2012.pdf Wired 8021x Authentication On Windows Server 2012Document96 pagesConfiguringme: Configuring Wired 8021x Authentication On Windows Server 2012.pdf Wired 8021x Authentication On Windows Server 2012simoo2010No ratings yet
- HP Wifi Controller Configuration Guide PDFDocument635 pagesHP Wifi Controller Configuration Guide PDFEnis Byci100% (1)
- Brkapp 3003Document98 pagesBrkapp 3003aarnulfoNo ratings yet
- Proven Network Administrator with Over 5 Years ExperienceDocument4 pagesProven Network Administrator with Over 5 Years ExperienceBharath PolineniNo ratings yet
- Ace TroubleshootingDocument182 pagesAce TroubleshootingjtfoleyNo ratings yet
- Cisco WLC Configuration Best Practices GuideDocument64 pagesCisco WLC Configuration Best Practices Guideleandroj8No ratings yet
- Cisco Nexus 3548 SwitchDocument166 pagesCisco Nexus 3548 Switchsales634No ratings yet
- (Cisco) Deploying 802.1X For Lan Security (2003) (PPT)Document70 pages(Cisco) Deploying 802.1X For Lan Security (2003) (PPT)Sudhir KuradeNo ratings yet
- Configurar o Gns3Document12 pagesConfigurar o Gns3adilsoncrenteNo ratings yet
- Cisco Nexus 5000 Series Guide - Enhanced vPC OverviewDocument22 pagesCisco Nexus 5000 Series Guide - Enhanced vPC OverviewCrazyBoSSNo ratings yet
- Cyberforce Overview PresentationDocument21 pagesCyberforce Overview Presentationandreko11No ratings yet
- Lab-Day2 - Lab3&4Document25 pagesLab-Day2 - Lab3&4AARNAV pandeyNo ratings yet
- B Ise Upgrade Guide 3 1 PDFDocument58 pagesB Ise Upgrade Guide 3 1 PDFSimenaNo ratings yet
- Alte On 1 Training AgendaDocument6 pagesAlte On 1 Training AgendaVijay SainiNo ratings yet
- CP R77 Gaia AdminGuideDocument281 pagesCP R77 Gaia AdminGuidejanaksundhar85No ratings yet
- NEXUS LACP Configuration FryguyDocument14 pagesNEXUS LACP Configuration Fryguyculebras69No ratings yet
- Cisco Nexus7000 Fundamentals Config Guide 8xDocument190 pagesCisco Nexus7000 Fundamentals Config Guide 8xrhisyamNo ratings yet
- Deployment Guide PDFDocument10 pagesDeployment Guide PDFMiguel LopezNo ratings yet
- Network Engineering Manager or Network Manager or IT Manager orDocument4 pagesNetwork Engineering Manager or Network Manager or IT Manager orapi-79087400No ratings yet
- Ssl/Tls Trends, Practices, and Futures: Brian A. Mchenry, Security Solutions Architect @bamchenryDocument34 pagesSsl/Tls Trends, Practices, and Futures: Brian A. Mchenry, Security Solutions Architect @bamchenryDhananjai SinghNo ratings yet
- Palo-Alto-Networks Certkiller PCNSE - v2018-04-16 by - Olga - 56q PDFDocument38 pagesPalo-Alto-Networks Certkiller PCNSE - v2018-04-16 by - Olga - 56q PDFSomya SinghNo ratings yet
- 90028-VPC Peer Switch Deployment OptionsDocument12 pages90028-VPC Peer Switch Deployment OptionsaliNo ratings yet
- Cisco Call Manager Express Example ConfigDocument23 pagesCisco Call Manager Express Example ConfigBrendon Bell100% (1)
- PCNSE Prepaway Premium Exam 167qDocument65 pagesPCNSE Prepaway Premium Exam 167qPak ChannNo ratings yet
- SW Ch01Document33 pagesSW Ch01Fabio QuintanaNo ratings yet
- Brownfield To ACI Migration Deployment Guide: First Published: August, 2015Document22 pagesBrownfield To ACI Migration Deployment Guide: First Published: August, 2015srinivas gavaraNo ratings yet
- Ccnpv7.1 Switch Lab 10-1 Securing Layer2 StudentDocument37 pagesCcnpv7.1 Switch Lab 10-1 Securing Layer2 StudentAlcaldia Valle De San JuanNo ratings yet
- Palo Alto Networks - Premium.pcnse - by.VCEplus.163qDocument96 pagesPalo Alto Networks - Premium.pcnse - by.VCEplus.163qWess WessNo ratings yet
- Ipsec On Huawei Ar Router PDFDocument5 pagesIpsec On Huawei Ar Router PDFHussein DhafanNo ratings yet
- 26.1.4 Lab - Configure Local and Server-Based AAA Authentication - ILMDocument21 pages26.1.4 Lab - Configure Local and Server-Based AAA Authentication - ILMTRYST CHAMA0% (1)
- PAN9 EDU210 Lab 12Document29 pagesPAN9 EDU210 Lab 12GenestapowerNo ratings yet
- CUCM Smart Licensing Version 12.XDocument5 pagesCUCM Smart Licensing Version 12.XGeo ThomasNo ratings yet
- Lab-Day3 - Lab5&6Document16 pagesLab-Day3 - Lab5&6AARNAV pandeyNo ratings yet
- Cisco Wireless LAN Controller Command Reference, Release 8.0Document1,972 pagesCisco Wireless LAN Controller Command Reference, Release 8.0islandguy43452100% (1)
- Advanced IEEE 802.1x PDFDocument105 pagesAdvanced IEEE 802.1x PDFAnonymous cRxoHJ32QvNo ratings yet
- FortiWeb 5 5 Administration Guide Revision1 PDFDocument859 pagesFortiWeb 5 5 Administration Guide Revision1 PDFPablo AimarNo ratings yet
- CCIE Enterprise - Syllabus PDFDocument12 pagesCCIE Enterprise - Syllabus PDFNETWORKERS HOMENo ratings yet
- Firepower RoadmapDocument18 pagesFirepower RoadmapMichael O'ConnellNo ratings yet
- WSA 7.0.0 UserGuideDocument784 pagesWSA 7.0.0 UserGuideLuis JimenezNo ratings yet
- Cisco UCS Central 1-4 v1 Demo GuideDocument109 pagesCisco UCS Central 1-4 v1 Demo GuideNethaji Thirusangu100% (1)
- 5.1 Cnse Study GuideDocument145 pages5.1 Cnse Study GuideKORATE BOYNo ratings yet
- Network Security v1.0 - Module 5Document26 pagesNetwork Security v1.0 - Module 5Ernesto Silverio FloresNo ratings yet
- Cisco Collaboration 9.x Solution Reference Network DesignsDocument1,230 pagesCisco Collaboration 9.x Solution Reference Network Designs전승원No ratings yet
- Adding Cisco Ios XRV Image To Eve-Ng LabDocument2 pagesAdding Cisco Ios XRV Image To Eve-Ng LabYogesh KhollamNo ratings yet
- 300 101Document484 pages300 101Diego Suarez0% (1)
- Vyatta VPNRef R6.1 v02Document321 pagesVyatta VPNRef R6.1 v02BlaiseMoroseNo ratings yet
- Ixia Solutions BrochureDocument48 pagesIxia Solutions BrochureGS MeenaNo ratings yet
- Cisco IOS ListDocument33 pagesCisco IOS ListAnonymous eTVLLaZ3yNo ratings yet
- CCN Lab Manual FullDocument39 pagesCCN Lab Manual FullfaizaNo ratings yet
- AP Discovery of WLCDocument2 pagesAP Discovery of WLCLucija Fioretti100% (1)
- Ragavan Kasturirangan Sir SpeechDocument16 pagesRagavan Kasturirangan Sir SpeechAlex KaloustNo ratings yet
- Packet Capture On Windows MachineDocument2 pagesPacket Capture On Windows MachineTanveer AkhtarNo ratings yet
- Norwegian Embassy Tourist Visa ChecklistDocument2 pagesNorwegian Embassy Tourist Visa ChecklistTanveer AkhtarNo ratings yet
- IJCS-23-0170 Proof HiDocument33 pagesIJCS-23-0170 Proof HiTanveer AkhtarNo ratings yet
- Technical Implementation DocumentDocument10 pagesTechnical Implementation DocumentTanveer AkhtarNo ratings yet
- Math's Full Notes.Document95 pagesMath's Full Notes.Tanveer AkhtarNo ratings yet
- F5 GTM Course ContentDocument4 pagesF5 GTM Course ContentTanveer AkhtarNo ratings yet
- HSRPDocument1 pageHSRPTanveer AkhtarNo ratings yet
- BGP TroubleshootDocument1 pageBGP TroubleshootTanveer AkhtarNo ratings yet
- Peplink Balance v5.4 User ManualDocument207 pagesPeplink Balance v5.4 User ManualNatalia Valeria Bonifaz MNo ratings yet
- Global Protect VPNDocument234 pagesGlobal Protect VPNTanveer AkhtarNo ratings yet
- Threatintethandbook PDFDocument140 pagesThreatintethandbook PDFMunwwarHussainSheliaNo ratings yet
- AlienVault Deployment Documents Most WantedDocument537 pagesAlienVault Deployment Documents Most WantedTanveer AkhtarNo ratings yet
- Slashnext Threat Intelligence Integration Guide MinemeldDocument8 pagesSlashnext Threat Intelligence Integration Guide MinemeldTanveer AkhtarNo ratings yet
- What Is Avalanche EffectDocument6 pagesWhat Is Avalanche EffectTanveer AkhtarNo ratings yet
- Kro Focus On YouDocument190 pagesKro Focus On YouTanveer AkhtarNo ratings yet
- AAA New Model On RouterDocument1 pageAAA New Model On RouterTanveer AkhtarNo ratings yet
- Employment Application Form: (Academic)Document3 pagesEmployment Application Form: (Academic)amy frostNo ratings yet
- Miner Node MinemeldDocument6 pagesMiner Node MinemeldTanveer AkhtarNo ratings yet
- LIVEcommunity - Manually Install MineMeld On Ubuntu 16.04 - LIVEcommunity - 253336Document23 pagesLIVEcommunity - Manually Install MineMeld On Ubuntu 16.04 - LIVEcommunity - 253336Tanveer AkhtarNo ratings yet
- Qasim Saeed: ContactDocument6 pagesQasim Saeed: ContactTanveer AkhtarNo ratings yet
- Internet ArchDocument1 pageInternet ArchTanveer AkhtarNo ratings yet
- FExtract ResultDocument6 pagesFExtract ResultTanveer AkhtarNo ratings yet
- Hawaid Khan Network Engineer CVDocument4 pagesHawaid Khan Network Engineer CVTanveer AkhtarNo ratings yet
- MethodologyDocument2 pagesMethodologyTanveer AkhtarNo ratings yet
- Best IT Resume Format TemplateDocument3 pagesBest IT Resume Format TemplateKmaniKanda PrabhuNo ratings yet
- DHA Suffa University: Faculty Employment Application FormDocument5 pagesDHA Suffa University: Faculty Employment Application FormTanveer AkhtarNo ratings yet
- Muhammad Shaheer (Network Engineer)Document2 pagesMuhammad Shaheer (Network Engineer)Tanveer AkhtarNo ratings yet
- Flowchart for Dataset GenerationDocument5 pagesFlowchart for Dataset GenerationTanveer AkhtarNo ratings yet
- Configure Inter VLAN RoutingDocument6 pagesConfigure Inter VLAN RoutingTanveer AkhtarNo ratings yet
- Waqas KhanDocument4 pagesWaqas KhanTanveer AkhtarNo ratings yet
- Efficient VLSM Subnetting SchemeDocument17 pagesEfficient VLSM Subnetting SchemeYousif Algulaidi100% (1)
- SG Certified Platform App Builder TransitionDocument9 pagesSG Certified Platform App Builder TransitionAntonymousNo ratings yet
- Item BarcodeDocument473 pagesItem BarcodemanjunathNo ratings yet
- C++ FastDocument31 pagesC++ Fastkshitij_gaur13No ratings yet
- RGB and Hexadecimal Color CodesDocument7 pagesRGB and Hexadecimal Color CodesArce LeagueNo ratings yet
- Yash SrsDocument40 pagesYash SrsMeet ChhetaNo ratings yet
- Captivate Reference PDFDocument707 pagesCaptivate Reference PDFReno PhilipNo ratings yet
- Ai CheatSheet Windows PDFDocument1 pageAi CheatSheet Windows PDFariniNo ratings yet
- ApplicationNotes Skype'ForBusinessInterworkingDocument50 pagesApplicationNotes Skype'ForBusinessInterworkingkathiNo ratings yet
- Manual BeckoffDocument62 pagesManual BeckoffJavier Relaño Orasio100% (2)
- Acro NGLLogDocument28 pagesAcro NGLLogRaghu KNo ratings yet
- Chapter 5Document41 pagesChapter 5Muhammad HazmanNo ratings yet
- Book of Nero 7 CD and DVD Burning Made Easy PDFDocument271 pagesBook of Nero 7 CD and DVD Burning Made Easy PDFDhaif LazharNo ratings yet
- Software Test EstimationDocument4 pagesSoftware Test EstimationHari NairNo ratings yet
- Qx3440 Rta Um enDocument97 pagesQx3440 Rta Um enAntonio Fernandez GonzalezNo ratings yet
- Advanced Compliance Reporting - HANADocument133 pagesAdvanced Compliance Reporting - HANAZORRO50% (4)
- ISO 27001 Statement of Applicability Template LMDocument4 pagesISO 27001 Statement of Applicability Template LMVathasil VasasiriNo ratings yet
- Tread: Owner's ManualDocument80 pagesTread: Owner's ManualemmaNo ratings yet
- Basic File OperationDocument4 pagesBasic File OperationTech force hindi100% (2)
- SANBlaze FC Emulation Datasheet PDFDocument2 pagesSANBlaze FC Emulation Datasheet PDFYilmer ZorrillaNo ratings yet
- 3D Deep Learning With Python - MaDocument236 pages3D Deep Learning With Python - MaJuan Rodriguez80% (5)
- HP Printer ProjectDocument55 pagesHP Printer ProjectMahesh Kumar100% (2)
- Week-3 Verilog Assignment QuestionsDocument3 pagesWeek-3 Verilog Assignment QuestionsAshish SuraNo ratings yet
- Lab 01 - Examine Seismic Data 2Document6 pagesLab 01 - Examine Seismic Data 2api-323770220No ratings yet
- AWE Overview: Paul GryfakisDocument38 pagesAWE Overview: Paul GryfakisssanjayrajNo ratings yet
- MscitDocument55 pagesMscitHardik PatelNo ratings yet
- Peoplebook Student Records 9.0Document1,508 pagesPeoplebook Student Records 9.0Vincent DewaNo ratings yet
- Olmedo Alexis Ipv6Document61 pagesOlmedo Alexis Ipv6Alexis MarceloNo ratings yet
- Trillion Network Operations Center Incident Management PolicyDocument6 pagesTrillion Network Operations Center Incident Management Policys_singh321No ratings yet
- Ir 2004 - 2204N Series Brochure PDFDocument4 pagesIr 2004 - 2204N Series Brochure PDFChristian Shaun DavidNo ratings yet