Professional Documents
Culture Documents
Encryption Is Described As The Way of Turning Normal Data Into What Is Known As Cipher Text
Uploaded by
Ted RogersOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Encryption Is Described As The Way of Turning Normal Data Into What Is Known As Cipher Text
Uploaded by
Ted RogersCopyright:
Available Formats
Encryption is described as the way of turning normal data into what is known as cipher text.
The
resulting cipher text is attained by using a cipher, which is the algorithm used to transform a
regular text to a format that is un-readable by human or computer through an encryption
program’s cipher. Encryption programs allow businesses to protect their company’s.
Encryption Coding: Refers to management and lifecycle of keys. This includes generating, using,
storing, archiving, and deleting of encryption keys.
1. API: In this method, data is encrypted manually, by hand. The best hands-on example of
API is databases such as Oracle, SQL. Specifically, queries within a column are modified
within the software by hand, using an algorithm, or cipher (eg: 1 is A, 2 is B, etc etc).
Codes are changed frequently.
2. Plug-in method: individual columns are encrypted requiring encryption coding to be
changed less frequently.
3. Transparent data encryption: The most popular method. Encryption of the whole
database. Usually, native to database apps.
Data encryption can happen on a number of levels from columns to groups of files. The more
parts there are the longer it will take to encrypt.
Cell-Level: each cell has a password.
Column-Level: columns are encrypted all together. Could take longer.
Tablespace-Level :allows encryption across tables. Very little impact on performance.
File-Level: scrambling entire document. You can move files into report, or spreadsheet
apps and they will still keep their scrambled protection.
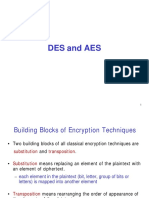
What are symmetric and asymmetric encryption?
Describe relationship between ciphertext(resulting encryption) and decryption keys. Encryption
algorithms can use the following.
Symmetric: In this case, data is encrypted when it is saved to the database and decrypted
when it needs to be viewed. Both Sharing parties require decryption key, and the key is
the same. Most popular. Key can be leaked by a person, leading to leaked data.
Symmetric encryption types are AES, RC4, DES.
Asymmetric: More secure than Symmetric. Need a private and public key. Public key lets
anyone to encrypt data for anyone, but then needs a private key to be read.). Types are
RSA, DSA, and PKCS.
How to businesses know which method to use? (which is most secure)
AES: Advanced Encryption Standard, symmetric algorithm, and is very secure. Encrypts
data in block lengths which are 128, 192, or 256 bits. That’s how many 0’s and 1’s there
are in the key.
RSA: Rivest-Shamir-Adleman is an asymmetric. This method is typically used for
sharing data over an insecure network, which can include database encryption. The key
size is between 1024 and 2048 bits.
3DES: Triple Data Encryption is another block cipher. uses 56-bit keys to encrypt data
three times, finishing in a 168-bit key. Becoming obsolete.
Twofish: Twofish is a symmetric block cipher, keys range from 128 bits to 256 bits.
Javamex. (n.d.). cipher encryption keys. Retrieved January 25, 2020, from
https://www.researchgate.net/figure/Performance-of-symmetric-encryption-algorithms-Javamex-
nd_fig4_325208273
You might also like
- 4 Common Encryption Methods and Use CasesDocument3 pages4 Common Encryption Methods and Use CasesPrabir Kumar MandalNo ratings yet
- No Network Is 100Document7 pagesNo Network Is 100AngelDayanaNo ratings yet
- Encryption and Decryption Algorithms 1Document5 pagesEncryption and Decryption Algorithms 1Jolina Joy B. BayacaNo ratings yet
- Module (Code &Name:Swdba401-Backend Application DevelopmentDocument62 pagesModule (Code &Name:Swdba401-Backend Application Developmentmuganzajesus001No ratings yet
- What is Cryptography? ExplainedDocument9 pagesWhat is Cryptography? ExplainedSagar DixitNo ratings yet
- Encryption Algorithms and Digital SignaturesDocument11 pagesEncryption Algorithms and Digital SignaturesPrateek MahajanNo ratings yet
- WP Encryption En-Lesson 6Document7 pagesWP Encryption En-Lesson 6LDB2No ratings yet
- Encrption: Keywords: Encryption, DES, Blowfish, RSA, AESDocument10 pagesEncrption: Keywords: Encryption, DES, Blowfish, RSA, AESabdul hadiNo ratings yet
- TCIL-IT Ethical Hacker Assignment No. 2Document11 pagesTCIL-IT Ethical Hacker Assignment No. 2anon_611052707No ratings yet
- The CIA Triad & Real-World ApplicationDocument1 pageThe CIA Triad & Real-World ApplicationGesler Pilvan SainNo ratings yet
- Cryptography inDocument97 pagesCryptography inDhanraj DSNo ratings yet
- 8920731afc1f33f15f9ba1311ba02babDocument35 pages8920731afc1f33f15f9ba1311ba02babKamrul HasanNo ratings yet
- Ijaiem 2013 07 17 054Document3 pagesIjaiem 2013 07 17 054International Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Aes FinalDocument134 pagesAes FinalPrasannaNo ratings yet
- Anderson AESDocument7 pagesAnderson AESMiraculous MiracleNo ratings yet
- Cryptography AnswersDocument21 pagesCryptography Answers219 DibyanshuKumarNo ratings yet
- Weak and Semi-Weak Keys in DESDocument10 pagesWeak and Semi-Weak Keys in DESAbdulrahman RadeefNo ratings yet
- PERFORMANCE ANALYSIS OF SYMMETRIC KEY CRYPTOGRAPHY ALGORITHMS: DES, AES and BLOWFISHDocument10 pagesPERFORMANCE ANALYSIS OF SYMMETRIC KEY CRYPTOGRAPHY ALGORITHMS: DES, AES and BLOWFISHResearch Cell: An International Journal of Engineering SciencesNo ratings yet
- Assignment 1Document10 pagesAssignment 1Barney StinsonNo ratings yet
- Implementation of Aes and Blowfish AlgorithmDocument4 pagesImplementation of Aes and Blowfish AlgorithmInternational Journal of Research in Engineering and TechnologyNo ratings yet
- EncryptionDocument14 pagesEncryptionSubhrajyoti MallNo ratings yet
- SecurityDocument78 pagesSecuritypriyeshb13No ratings yet
- UntitledDocument5 pagesUntitledDanirose RionalNo ratings yet
- Open SSLDocument31 pagesOpen SSLDibya SachiNo ratings yet
- Data Encryption StandardDocument37 pagesData Encryption Standardchristian MacNo ratings yet
- Cryptography in Cloud Computing: A Basic Approach To Ensure Security in CloudDocument8 pagesCryptography in Cloud Computing: A Basic Approach To Ensure Security in CloudDinh Van ThaiNo ratings yet
- EncryptionDocument66 pagesEncryptionRoberto RaimondoNo ratings yet
- Public Key InfrastructureDocument23 pagesPublic Key InfrastructureYogesh YadavNo ratings yet
- A Review Paper On AES and DES Cryptographic AlgorithmsDocument6 pagesA Review Paper On AES and DES Cryptographic AlgorithmsFadhil SahibNo ratings yet
- CryptographyDocument8 pagesCryptographySadia Islam ShefaNo ratings yet
- Net Security Chap 2Document20 pagesNet Security Chap 2Asif KoujaganurNo ratings yet
- CryptographyDocument9 pagesCryptographyTom LunaNo ratings yet
- NSC Unit - 2 - 221218 - 100752Document25 pagesNSC Unit - 2 - 221218 - 100752SurenderNo ratings yet
- Final DocumentDocument60 pagesFinal DocumentRitul RaiNo ratings yet
- Cryptography Theory and ObjectivesDocument7 pagesCryptography Theory and ObjectivesZonia NillNo ratings yet
- A Novel Idea On Multimedia Encryption Using Hybrid Crypto ApproachDocument6 pagesA Novel Idea On Multimedia Encryption Using Hybrid Crypto ApproachLeonardo OroscoNo ratings yet
- CryptographyDocument2 pagesCryptographytouk toukNo ratings yet
- Contoh Proposal Usaha WarnetDocument10 pagesContoh Proposal Usaha WarnetRayanQardhafiNo ratings yet
- Decryption:: Encryption DataDocument3 pagesDecryption:: Encryption Dataavinashthegreat9No ratings yet
- A Review On RSA Encryption Algorithm: Shaina Garg, Dr. Mukesh Kumar RanaDocument4 pagesA Review On RSA Encryption Algorithm: Shaina Garg, Dr. Mukesh Kumar RanaPatient ZeroNo ratings yet
- Secure File Storage On Cloud Using Hybrid CryptographyDocument8 pagesSecure File Storage On Cloud Using Hybrid CryptographyVicky VigneshNo ratings yet
- Protect Your Data in Today's World Through CryptographyDocument4 pagesProtect Your Data in Today's World Through CryptographyInnovative Research PublicationsNo ratings yet
- (Delfs and Knebl 2015) : Individual Assignment - Im41103 Network SecurityDocument6 pages(Delfs and Knebl 2015) : Individual Assignment - Im41103 Network SecurityNaue J.No ratings yet
- CNS Imp (Overview)Document23 pagesCNS Imp (Overview)elitepredator1916No ratings yet
- Advanced Encryption Standard (AES) IntroductionDocument67 pagesAdvanced Encryption Standard (AES) IntroductionRama VenkateshNo ratings yet
- Instructor Materials Chapter 4: The Art of Protecting SecretsDocument29 pagesInstructor Materials Chapter 4: The Art of Protecting SecretsDewi Ayu LestariNo ratings yet
- Most Followed Encryption MethodsDocument2 pagesMost Followed Encryption MethodsBernard LayonNo ratings yet
- Confidential Data Storage and DeletionDocument22 pagesConfidential Data Storage and DeletionpoojaNo ratings yet
- Invitation To Computer Science 6Th Edition Schneider Solutions Manual Full Chapter PDFDocument30 pagesInvitation To Computer Science 6Th Edition Schneider Solutions Manual Full Chapter PDFcurtisnathanvjyr100% (9)
- Research Paper On Cryptography AlgorithmDocument4 pagesResearch Paper On Cryptography Algorithmfvfzfa5d100% (1)
- Computer Security: Computer Threats and EncryptionDocument21 pagesComputer Security: Computer Threats and EncryptionPro NebyuNo ratings yet
- Comparative Study of Different Cryptographic Algorithms For Data Security in Cloud ComputingDocument7 pagesComparative Study of Different Cryptographic Algorithms For Data Security in Cloud ComputingPathan MehemudNo ratings yet
- Foundation of Information Assurance Test SolutionsDocument7 pagesFoundation of Information Assurance Test SolutionsAjibade AdedapoNo ratings yet
- Comparative Study of Symmetric Encryption Techniques For Mobile Data Caching in WMNDocument6 pagesComparative Study of Symmetric Encryption Techniques For Mobile Data Caching in WMNtheijesNo ratings yet
- File Encryption, Decryption Using AES Algorithm in Android PhoneDocument6 pagesFile Encryption, Decryption Using AES Algorithm in Android PhoneAnonymous MSmf7l33HYNo ratings yet
- The Use of Elliptic Curves in Cryptography: Aster S Hesis in AthematicsDocument76 pagesThe Use of Elliptic Curves in Cryptography: Aster S Hesis in AthematicsTeodoraNo ratings yet
- What Is Cryptography?Document3 pagesWhat Is Cryptography?Sridhar PNo ratings yet
- Chapter 2 Computer Security1Document10 pagesChapter 2 Computer Security1Yared AyeleNo ratings yet
- Fifthleveloflearningpart2 PDFDocument293 pagesFifthleveloflearningpart2 PDFTed RogersNo ratings yet
- Fifthleveloflearningpart2 PDFDocument293 pagesFifthleveloflearningpart2 PDFTed RogersNo ratings yet
- FOIA Log - Cases Received Between 1/1/2018 and 12/31/2018Document483 pagesFOIA Log - Cases Received Between 1/1/2018 and 12/31/2018Ted RogersNo ratings yet
- Fifthleveloflearningpart 1Document378 pagesFifthleveloflearningpart 1Ted RogersNo ratings yet
- 6th Central Pay Commission Salary CalculatorDocument15 pages6th Central Pay Commission Salary Calculatorrakhonde100% (436)
- 9.0.1.2 Class Activity - Creating CodesDocument3 pages9.0.1.2 Class Activity - Creating CodesAdministratorNo ratings yet
- To Participate in Message-Driven Processing. Application Programs Can CommunicateDocument29 pagesTo Participate in Message-Driven Processing. Application Programs Can Communicateseenu651No ratings yet
- I.T Engg Sem-VIDocument14 pagesI.T Engg Sem-VIMuvin KoshtiNo ratings yet
- Book 2 Ecommerce LawDocument82 pagesBook 2 Ecommerce LawRashmi AminNo ratings yet
- Cryptography, Network Security and Cyber Laws Notes 2019-2020Document23 pagesCryptography, Network Security and Cyber Laws Notes 2019-2020Himanshu KumarNo ratings yet
- An Encryption Protocol For End-To-End Secure Transmission of SMSDocument7 pagesAn Encryption Protocol For End-To-End Secure Transmission of SMSThet Hmue Hay ThiNo ratings yet
- CipherDocument9 pagesCipherAnonymous jpeHV73mLzNo ratings yet
- Slaa 547 ADocument28 pagesSlaa 547 AOlteanu IonelNo ratings yet
- DES and AESDocument81 pagesDES and AESeyasuNo ratings yet
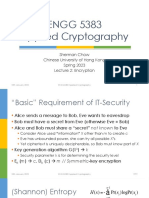
- 5383 23S 2 EncDocument40 pages5383 23S 2 EncTingyang YUNo ratings yet
- Secuirity & Privacy in Vanet Name of Project: JIS College of EngineeringDocument21 pagesSecuirity & Privacy in Vanet Name of Project: JIS College of EngineeringDebojit SenguptaNo ratings yet
- CNS NotesDocument36 pagesCNS NotesAnjanaNo ratings yet
- New Encryption AlgorithmDocument5 pagesNew Encryption AlgorithmcheintNo ratings yet
- Introduction to Smart Cards and Quantum CryptographyDocument11 pagesIntroduction to Smart Cards and Quantum CryptographyayanthakNo ratings yet
- 1 (Ciphers)Document23 pages1 (Ciphers)Anand RajNo ratings yet
- Encryption and Cryptography ExplainedDocument41 pagesEncryption and Cryptography ExplainedSamer SamaraNo ratings yet
- Network-Management-And-SecurityDocument16 pagesNetwork-Management-And-SecurityMuhammad Taha RasoulNo ratings yet
- Digital Signature: Presented by K.ANITHA (19065) T.DIVYA (19074) T.PAVAN (19082) P.Venu Gopal Reddy (19104)Document19 pagesDigital Signature: Presented by K.ANITHA (19065) T.DIVYA (19074) T.PAVAN (19082) P.Venu Gopal Reddy (19104)Divya TammineediNo ratings yet
- Modernblockcipher 170817223658Document26 pagesModernblockcipher 170817223658Rajkamal K GuptaNo ratings yet
- Cryptography CS 555: Topic 10: Block Cipher Security & AESDocument26 pagesCryptography CS 555: Topic 10: Block Cipher Security & AESAswini KnairNo ratings yet
- Cryptanalysis of Classical Ciphers with webcrypt SoftwareDocument40 pagesCryptanalysis of Classical Ciphers with webcrypt SoftwareLeandro TeixeiraNo ratings yet
- 3 - Intro To Modern CryptoDocument61 pages3 - Intro To Modern CryptosamuelNo ratings yet
- CH04 - CryptograpghyDocument95 pagesCH04 - Cryptograpghyangwin sNo ratings yet
- CRY303c PE Solution Spring22Document2 pagesCRY303c PE Solution Spring22Dao Manh Cong (K16HL)No ratings yet
- Introduction To Cryptography: Zahra Sadat Bahri Student No. 98110232 Homework 1 October 8, 2021Document7 pagesIntroduction To Cryptography: Zahra Sadat Bahri Student No. 98110232 Homework 1 October 8, 2021Baran BahriNo ratings yet
- Public-Key Cryptography LabDocument9 pagesPublic-Key Cryptography LabMinh Châu Đặng ĐạiNo ratings yet
- Cryptography: The Science of Secret WritingDocument21 pagesCryptography: The Science of Secret WritingsubashreeNo ratings yet
- Seminar On Information Tecnology Acts: Data Encryption Standard (Des)Document13 pagesSeminar On Information Tecnology Acts: Data Encryption Standard (Des)Vaibhav GuptaNo ratings yet
- Encryption and CryptographyDocument83 pagesEncryption and CryptographyabcNo ratings yet