Professional Documents
Culture Documents
1.1 Current Situation: Cloud Computing Compliance Controls Catalogue (C5)
Uploaded by
SNFK20180 ratings0% found this document useful (0 votes)
48 views1 pageOriginal Title
C510
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
48 views1 page1.1 Current Situation: Cloud Computing Compliance Controls Catalogue (C5)
Uploaded by
SNFK2018Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 1
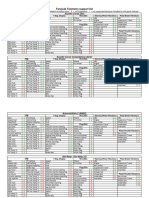
Cloud Computing ComplianCe Controls Catalogue (C5) | introduCtion
1 Introduction
1.1 Current situation There are different standards and certifications on
the market which are used and maintained in par-
Cloud computing is a new paradigm in ICT (infor- allel with great effort by many cloud providers. It
mation and communication technology). It con- is difficult for customers, however, to keep up an
sists of IT services being adjusted dynamically to overview of the large number of different certifi-
the customer needs and made available through cations. The present cloud computing compliance
a network in a billable manner. These services are controls catalogue (hereafter referred to as “C5”) is
offered and used by means of technical interfaces intended to be an aid for the customer providing
and protocols. Moreover, the definition of cloud a better overview for a higher level of security and
computing of the Federal Office for Information avoiding redundant audits.
Security (Bundesamt für Sicherheit in der Infor-
mationstechnik – BSI) (and the differentiation
from IT outsourcing) applies as it is described on
the BSI website1. 1.2 Uniform requirements based
on existing standards
Cloud computing is based on a high level of
standardisation of the hard- and software as well The BSI uses C5 to present its current view of the
as on the services build on it, details of which the mentioned informal consensus, and particularly
customer is usually not very familiar with. As a to also facilitate an in-depth technical discussion.
consequence, a particularly high degree of trust in The requirements were, wherever possible, taken
the cloud service provider is required, which has from known security standards and specified if
to be developed first. necessary. They were supplemented by the BSI’s
own requirements only to the extent needed. The
A possible solution is combining the high origin of the requirements is documented in a
standardisation of cloud computing with a high transparent manner so that the cloud provider is
standardisation of information security. There able to easily perform a comparison with his own
is no lack of available information security security level.
standards in the context of cloud computing.
Examples include the ISO/IEC 27001 and ISO/ In cases considered appropriate, additional
IEC 27017 standards, the rules of the CSA Cloud requirements were included in C5 for certain
Controls Matrix and the BSI products like the basic requirements. It’s BSI’s professional point
IT-Grundschutz Catalogues and security profiles of view that the basic requirements shall always
for software as a service (SaaS). be met for secure cloud computing. Moreover,
it is up to the cloud customer to decide for their
Among security experts and cloud service pro- specific use case whether these basic requirements
viders exists an informal consensus about the are sufficient or additional, optional requirements
requirements that have to be met for secure cloud have to be met by the cloud provider. For this
computing. A generally recognised requirements purpose, the additional requirements of C5 serve
(or controls) catalogue on this, however, is not as a useful starting point.
available yet.
It remains the challenge to prove the cloud
customer that the requirements of C5 are fulfilled
by means of a transparent audit performed by an
independent, trusted third party. As for the basic
1 https://www.bsi.bund.de/EN/Topics/CloudComput-
requirements found in this catalogue, this audit
ing/Basics/Basics_node.html
10
You might also like
- Cloud: Get All The Support And Guidance You Need To Be A Success At Using The CLOUDFrom EverandCloud: Get All The Support And Guidance You Need To Be A Success At Using The CLOUDNo ratings yet
- An Introduction to SDN Intent Based NetworkingFrom EverandAn Introduction to SDN Intent Based NetworkingRating: 5 out of 5 stars5/5 (1)
- 2 Structure and Contents of C5Document1 page2 Structure and Contents of C5SNFK2018No ratings yet
- Am Cloud Connect Operation Overview 8AL91354ENAA 6 enDocument19 pagesAm Cloud Connect Operation Overview 8AL91354ENAA 6 enlocuras34No ratings yet
- ISO 27017 OverviewDocument4 pagesISO 27017 OverviewRajesh VNo ratings yet
- Cloud Adoption Assessment: Vincent Damen RE CISADocument6 pagesCloud Adoption Assessment: Vincent Damen RE CISAtodebarshiNo ratings yet
- 5adb0 NTT Case Study Transforming CX Through Multi Cloud For India S Largest Private Bank 2021Document2 pages5adb0 NTT Case Study Transforming CX Through Multi Cloud For India S Largest Private Bank 2021chandraNo ratings yet
- Cloud Office InfrastructureDocument6 pagesCloud Office InfrastructureDavid KasambaNo ratings yet
- Cloud Computing Security Policy and StandardDocument15 pagesCloud Computing Security Policy and StandardghaurimuhammadNo ratings yet
- Guide to Cloud Procurement RoadmapDocument16 pagesGuide to Cloud Procurement RoadmapMN Abu BakarNo ratings yet
- Am Cloud Connect Operation Overview 8AL91354ENAA 5 enDocument21 pagesAm Cloud Connect Operation Overview 8AL91354ENAA 5 enK Mei.No ratings yet
- Validating Cloud Infrastructure Changes by Cloud AuditsDocument8 pagesValidating Cloud Infrastructure Changes by Cloud AuditsAdrian BladesNo ratings yet
- An Outline of The Problems and Potential Solutions For Cloud Computing SecurityDocument13 pagesAn Outline of The Problems and Potential Solutions For Cloud Computing SecurityInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Deriving A Distributed Cloud Proxy Architecture For Managed Cloud Computing ServiceDocument5 pagesDeriving A Distributed Cloud Proxy Architecture For Managed Cloud Computing ServiceVIVA-TECH IJRINo ratings yet
- ICC Cloud Policy StatementDocument9 pagesICC Cloud Policy StatementICC BASISNo ratings yet
- Cloud ComputingDocument26 pagesCloud ComputingHusnain AliNo ratings yet
- 5g Core Guide Ci CDDocument12 pages5g Core Guide Ci CDHong FangNo ratings yet
- Cloud Cybersecurity ControlsDocument48 pagesCloud Cybersecurity ControlsKaran Ojha100% (2)
- Trusted Cloud ComputingDocument8 pagesTrusted Cloud ComputingAli JumaaNo ratings yet
- CCSK QuestionsDocument4 pagesCCSK Questionsrams2hkNo ratings yet
- Security and Privacy (Final)Document7 pagesSecurity and Privacy (Final)Abin Varkey VargheseNo ratings yet
- Cloud Based Banking Software Solutions: Information Technology For ManagementDocument12 pagesCloud Based Banking Software Solutions: Information Technology For ManagementneerajNo ratings yet
- Zentera CoIP SSO Use Case 15mar2016Document3 pagesZentera CoIP SSO Use Case 15mar2016Adam MernerNo ratings yet
- Offer Description For: Connected Mobile Experiences Cloud (CMX Cloud)Document9 pagesOffer Description For: Connected Mobile Experiences Cloud (CMX Cloud)Ed NunezNo ratings yet
- CLD SecDocument12 pagesCLD SecAman KumarNo ratings yet
- Cloud Security IssuesDocument4 pagesCloud Security IssuesAdi AshkenaziNo ratings yet
- What Is Cloud?: Unit 1: Introduction To Cloud ComputingDocument14 pagesWhat Is Cloud?: Unit 1: Introduction To Cloud Computingkashinath.kbNo ratings yet
- IJIRAE:: A Novel Approach For SLA Compliance Monitoring in Cloud ComputingDocument6 pagesIJIRAE:: A Novel Approach For SLA Compliance Monitoring in Cloud ComputingIJIRAE- International Journal of Innovative Research in Advanced EngineeringNo ratings yet
- Expansion of Payment Services On Cloud RevisedDocument17 pagesExpansion of Payment Services On Cloud RevisednehaNo ratings yet
- Cloud Security Standards Landscape FinalDocument24 pagesCloud Security Standards Landscape FinalArmando RibeiroNo ratings yet
- Quantitative Reasoning About Cloud Security Using Service Level AgreementsDocument15 pagesQuantitative Reasoning About Cloud Security Using Service Level AgreementsSachin GosaviNo ratings yet
- Fintech - Choosing A Clous Services ProviderDocument9 pagesFintech - Choosing A Clous Services ProviderDivya Kumar Gautam PGP 2022-24No ratings yet
- CloudBytes - STAR Certification V1Document56 pagesCloudBytes - STAR Certification V1CloudSANYNo ratings yet
- Cloud Computing Policy Jun17Document7 pagesCloud Computing Policy Jun17Paul LenarkeNo ratings yet
- IDC Analyst Brief Private Cloud Requirements For Datacenter Network Automation and Virtualization US47697221Document5 pagesIDC Analyst Brief Private Cloud Requirements For Datacenter Network Automation and Virtualization US47697221allanhmooreNo ratings yet
- Cloud Computing For Financial Institutions: Vivek KejriwalDocument9 pagesCloud Computing For Financial Institutions: Vivek KejriwalPriyanka DhawanNo ratings yet
- Identity-Based Cryptography For Cloud Security: Abstract-Cloud Computing Is A Style of Computing inDocument9 pagesIdentity-Based Cryptography For Cloud Security: Abstract-Cloud Computing Is A Style of Computing inBibehAria BebNo ratings yet
- Cloud Enabled Data Center Adoption Pattern: Cloud Service Lifecycle: AcquisitionDocument7 pagesCloud Enabled Data Center Adoption Pattern: Cloud Service Lifecycle: AcquisitionGeeta DesaiNo ratings yet
- Microsoft Cloud - Checklist For Financial Institutions in CanadaDocument74 pagesMicrosoft Cloud - Checklist For Financial Institutions in Canadapaladin777No ratings yet
- Cloud Security GuidanceDocument22 pagesCloud Security GuidanceDuncan NgachaNo ratings yet
- Mohammed Kareem HusseinDocument7 pagesMohammed Kareem HusseinOmar AbooshNo ratings yet
- Whitepaper-VMware Bluelock Security in The Hybrid CloudDocument10 pagesWhitepaper-VMware Bluelock Security in The Hybrid CloudJagruti BorasteNo ratings yet
- NGMN Cloud Native ManifestoDocument14 pagesNGMN Cloud Native Manifestobogdan_rustiNo ratings yet
- How Cloud Is UtilisedDocument5 pagesHow Cloud Is Utilisedsophiawright2278No ratings yet
- Cloud computing security challenges and standardsDocument6 pagesCloud computing security challenges and standardsVaziel IvansNo ratings yet
- SHR Infra Sec Op Fwork 2020 v1 0Document29 pagesSHR Infra Sec Op Fwork 2020 v1 0Parameswaran LakshmynarayananNo ratings yet
- MVISION Cloud Architecture Guide - Final 1.1Document20 pagesMVISION Cloud Architecture Guide - Final 1.1Valentin Stefan TalpeanuNo ratings yet
- 3Rd International Conference On Internet of Things & Connected Technologies (Iciotct), 2018Document6 pages3Rd International Conference On Internet of Things & Connected Technologies (Iciotct), 2018Pav TechnicalsNo ratings yet
- Cisco Data Center Certifications: ArticleDocument2 pagesCisco Data Center Certifications: ArticlevasilejimanNo ratings yet
- Visvesvaraya Technological University Belgaum: A Seminar Report On Cloud ComputingDocument13 pagesVisvesvaraya Technological University Belgaum: A Seminar Report On Cloud ComputingNeha TiwariNo ratings yet
- CICD in 5GDocument14 pagesCICD in 5GcarlosrroffeNo ratings yet
- Sécurité dans le Cloud 1-139Document139 pagesSécurité dans le Cloud 1-139z.essiddiqiNo ratings yet
- Multifactor Biometric Authentication For Cloud Computing: Abstract-Cloud Computing Is A Fast-Growing TechnologyDocument7 pagesMultifactor Biometric Authentication For Cloud Computing: Abstract-Cloud Computing Is A Fast-Growing TechnologyMartin Cardenas MorenoNo ratings yet
- Mutual Protection in A Cloud Computing EnvironmentDocument6 pagesMutual Protection in A Cloud Computing Environmentkapil kaleNo ratings yet
- Kandu Kuri 2009Document4 pagesKandu Kuri 2009shivangi aggarwalNo ratings yet
- Cloud Computing PaperDocument22 pagesCloud Computing Papertkdseattle1976No ratings yet
- Security For Cloud Computing: 10 Steps To Ensure Success Version 3.0Document48 pagesSecurity For Cloud Computing: 10 Steps To Ensure Success Version 3.0Brian JonesNo ratings yet
- Cloud Computing Lecture#1Document18 pagesCloud Computing Lecture#1Syeda Insharah RiazNo ratings yet
- Sample Test 281Document3 pagesSample Test 281jvgnrNo ratings yet
- Auditing Cloud Computing: A Security and Privacy GuideFrom EverandAuditing Cloud Computing: A Security and Privacy GuideRating: 3 out of 5 stars3/5 (2)
- Cloud Computing Compliance Catalogue Table of ContentsDocument1 pageCloud Computing Compliance Catalogue Table of ContentsSNFK2018No ratings yet
- Cloud Computing Compliance Controls Catalogue (C5) : - Table of ContentDocument1 pageCloud Computing Compliance Controls Catalogue (C5) : - Table of ContentSNFK2018No ratings yet
- Cloud Computing Compliance Controls Catalogue (C5) : - Table of ContentDocument1 pageCloud Computing Compliance Controls Catalogue (C5) : - Table of ContentSNFK2018No ratings yet
- Cloud Computing Compliance Controls Catalogue (C5) : - Table of ContentDocument1 pageCloud Computing Compliance Controls Catalogue (C5) : - Table of ContentSNFK2018No ratings yet
- Cloud Computing Compliance Controls Catalogue (C5) : - Table of ContentDocument1 pageCloud Computing Compliance Controls Catalogue (C5) : - Table of ContentSNFK2018No ratings yet
- Cloud Computing Compliance Controls Catalogue (C5) : - Table of ContentDocument1 pageCloud Computing Compliance Controls Catalogue (C5) : - Table of ContentSNFK2018No ratings yet
- Cloud Computing Compliance Controls Catalogue (C5) : - Table of ContentDocument1 pageCloud Computing Compliance Controls Catalogue (C5) : - Table of ContentSNFK2018No ratings yet
- Cloud Computing Compliance Controls Catalogue (C5) : - Table of ContentDocument1 pageCloud Computing Compliance Controls Catalogue (C5) : - Table of ContentSNFK2018No ratings yet
- Cloud Computing Compliance Controls Catalogue (C5) : - Table of ContentDocument1 pageCloud Computing Compliance Controls Catalogue (C5) : - Table of ContentSNFK2018No ratings yet
- Cloud Computing Compliance Controls Catalogue (C5) : - Table of ContentDocument1 pageCloud Computing Compliance Controls Catalogue (C5) : - Table of ContentSNFK2018No ratings yet
- Cloud Computing Compliance Catalogue Table of ContentsDocument1 pageCloud Computing Compliance Catalogue Table of ContentsSNFK2018No ratings yet
- Cloud Computing Compliance Catalogue Table of ContentsDocument1 pageCloud Computing Compliance Catalogue Table of ContentsSNFK2018No ratings yet
- Cloud Computing Compliance Controls Catalogue (C5) : - Table of ContentDocument1 pageCloud Computing Compliance Controls Catalogue (C5) : - Table of ContentSNFK2018No ratings yet
- Cloud Computing Compliance Catalogue C5 Table of ContentsDocument1 pageCloud Computing Compliance Catalogue C5 Table of ContentsSNFK2018No ratings yet
- Cloud Computing Compliance Controls Catalogue (C5) : - Table of ContentDocument1 pageCloud Computing Compliance Controls Catalogue (C5) : - Table of ContentSNFK2018No ratings yet
- Cloud Computing Compliance Controls Catalogue (C5) : - Table of ContentDocument1 pageCloud Computing Compliance Controls Catalogue (C5) : - Table of ContentSNFK2018No ratings yet
- Cloud Computing Compliance Controls Catalogue (C5) : - Table of ContentDocument1 pageCloud Computing Compliance Controls Catalogue (C5) : - Table of ContentSNFK2018No ratings yet
- Cloud Computing Compliance Catalogue Table of ContentsDocument1 pageCloud Computing Compliance Catalogue Table of ContentsSNFK2018No ratings yet
- Cloud Computing Compliance Catalogue Table of ContentsDocument1 pageCloud Computing Compliance Catalogue Table of ContentsSNFK2018No ratings yet
- Cloud Computing Compliance Catalogue Table of ContentsDocument1 pageCloud Computing Compliance Catalogue Table of ContentsSNFK2018No ratings yet
- Cloud Computing Compliance Controls Catalogue (C5) : - Table of ContentDocument1 pageCloud Computing Compliance Controls Catalogue (C5) : - Table of ContentSNFK2018No ratings yet
- Cloud Computing Compliance Controls Catalogue (C5) : - Table of ContentDocument1 pageCloud Computing Compliance Controls Catalogue (C5) : - Table of ContentSNFK2018No ratings yet
- Cloud Computing Compliance Catalogue Table of ContentsDocument1 pageCloud Computing Compliance Catalogue Table of ContentsSNFK2018No ratings yet
- Cloud Computing Compliance Catalogue Table of ContentsDocument1 pageCloud Computing Compliance Catalogue Table of ContentsSNFK2018No ratings yet
- Cloud Computing Compliance Catalogue Table of ContentsDocument1 pageCloud Computing Compliance Catalogue Table of ContentsSNFK2018No ratings yet
- Cloud Computing Compliance Controls Catalogue (C5) : - Table of ContentDocument1 pageCloud Computing Compliance Controls Catalogue (C5) : - Table of ContentSNFK2018No ratings yet
- Cloud Computing Compliance Controls Catalogue (C5) : - Table of ContentDocument1 pageCloud Computing Compliance Controls Catalogue (C5) : - Table of ContentSNFK2018No ratings yet
- Cloud Computing Compliance Controls Catalogue (C5) : - Table of ContentDocument1 pageCloud Computing Compliance Controls Catalogue (C5) : - Table of ContentSNFK2018No ratings yet
- Cloud Computing Compliance Controls Catalogue (C5) : - Table of ContentDocument1 pageCloud Computing Compliance Controls Catalogue (C5) : - Table of ContentSNFK2018No ratings yet
- Cloud Computing Compliance Controls Catalogue (C5) : - Table of ContentDocument1 pageCloud Computing Compliance Controls Catalogue (C5) : - Table of ContentSNFK2018No ratings yet
- 001 - Understanding Convergence in An Autodesk Nastran In-CAD Nonlinear Analysis - Nastran - Autodesk Knowledge NetworkDocument12 pages001 - Understanding Convergence in An Autodesk Nastran In-CAD Nonlinear Analysis - Nastran - Autodesk Knowledge NetworkEquitus EngNo ratings yet
- Rotary Actuator and Gripper Selection GuideDocument63 pagesRotary Actuator and Gripper Selection GuideAlexandre DomingosNo ratings yet
- Shantui SG17-B6 Motor Grader enDocument2 pagesShantui SG17-B6 Motor Grader enFranco SartoriNo ratings yet
- Ayurveda ReportDocument75 pagesAyurveda ReportPrince GargNo ratings yet
- Georeferencing Topo Sheets and Scanned Maps (QGIS3) - QGIS Tutorials and TipsDocument19 pagesGeoreferencing Topo Sheets and Scanned Maps (QGIS3) - QGIS Tutorials and Tipsmp dcNo ratings yet
- ¿Qué Son Los Object Pronouns y para Qué Sirven?Document17 pages¿Qué Son Los Object Pronouns y para Qué Sirven?Valeria FrancoNo ratings yet
- Practical File Xii ItDocument4 pagesPractical File Xii ItDiya Biswas100% (1)
- ID-3LA-LP ID-12LA-LP ID-20LA-LP RFID Reader Modules Low Power - Micro Power 125khz LFDocument20 pagesID-3LA-LP ID-12LA-LP ID-20LA-LP RFID Reader Modules Low Power - Micro Power 125khz LFAbleIDLtdNo ratings yet
- Help YourselfDocument68 pagesHelp YourselfSubh RaoNo ratings yet
- Forklift Driver Warehouse Worker ResumeDocument6 pagesForklift Driver Warehouse Worker Resumebcqta9j6100% (2)
- Standard Thermal Store Dec 21Document2 pagesStandard Thermal Store Dec 21ErikNo ratings yet
- Scheduling, Preemption and Eviction - KubernetesDocument66 pagesScheduling, Preemption and Eviction - KubernetesFantahun FkadieNo ratings yet
- 42KHD005N16 High Performance Smart Flat Panel Air ConditionerDocument4 pages42KHD005N16 High Performance Smart Flat Panel Air ConditionerIrvan RamadhaniNo ratings yet
- Huawei Concentric Cell OptimizationDocument45 pagesHuawei Concentric Cell OptimizationWassim Nostra100% (1)
- Testing of Magnetic Flow Meters in Nonideal Conditions: Conference PaperDocument13 pagesTesting of Magnetic Flow Meters in Nonideal Conditions: Conference PaperpinkcityNo ratings yet
- ELSAP11DDocument1 pageELSAP11DJhonny RinconesNo ratings yet
- Ecom Midterm 2018Document5 pagesEcom Midterm 2018BRIAN INCOGNITONo ratings yet
- Final ppt-1Document20 pagesFinal ppt-1jhonnyNo ratings yet
- STP (200kld) - Technical Datasheet 17.02.23Document150 pagesSTP (200kld) - Technical Datasheet 17.02.23Rajender Chamoli100% (1)
- Vertiv Ups Range Competitive Comparison TableDocument1 pageVertiv Ups Range Competitive Comparison TableDaniel DoradoNo ratings yet
- Baja Sae Fox Racing ProgramDocument8 pagesBaja Sae Fox Racing ProgramChristian MavarezNo ratings yet
- Chemometrics in ChromatographyDocument1 pageChemometrics in Chromatographyjeremy mahNo ratings yet
- Datasheet of DS-2AE4225TI-D (C) 3.44 20180403 PDFDocument4 pagesDatasheet of DS-2AE4225TI-D (C) 3.44 20180403 PDFRamon Segarra ClaraNo ratings yet
- Honda Company BackgroundDocument6 pagesHonda Company BackgroundDilawar Aheer100% (1)
- FanaLab Telemetry Support ListDocument8 pagesFanaLab Telemetry Support ListRidasNo ratings yet
- Planta 1500 KvaDocument6 pagesPlanta 1500 Kvawilrojo1983No ratings yet
- PIM2 Fuel Injection Controller KitDocument4 pagesPIM2 Fuel Injection Controller KitmondorolaNo ratings yet
- IL-NT firmware and input/output configuration reportDocument3 pagesIL-NT firmware and input/output configuration reportBGP10No ratings yet
- Flutter SyllabusDocument4 pagesFlutter Syllabussiddhant.batasNo ratings yet
- 2D Animation-2nd Q-W8Document6 pages2D Animation-2nd Q-W8RUFINO MEDICONo ratings yet