Professional Documents
Culture Documents
State of Cybersecurity 2019: Part 1: Current Trends in Workforce Development
Uploaded by
Viriato LeaoOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
State of Cybersecurity 2019: Part 1: Current Trends in Workforce Development
Uploaded by
Viriato LeaoCopyright:
Available Formats
State of Cybersecurity 2019
Part 1: Current Trends in Workforce Development
Abstract
State of Cybersecurity 2019 reports the results of the annual ISACA global State of Cybersecurity Survey, conducted
in November 2018. While some findings pointed to unforeseen trends, many survey results reinforce previous
years’ findings—specifically that the need for trained and experienced cybersecurity professionals vastly outweighs
the supply. State of Cybersecurity 2019 provides a distinctive view of cybersecurity from the perspective of those
who define the field—cybersecurity managers and practitioners. This is the first report based on the survey, which
focuses on the current trends in cybersecurity workforce development, staffing, budget and gender diversity.
© 2019 ISACA. All Rights Reserved.
Personal Copy of Viriato Leao/Lopes De Souza (ISACA ID: 180411)
STATE OF CYBERSECURITY 2019: CURRENT TRENDS IN WORKFORCE DEVELOPMENT
CONTENTS
3 Executive Summary
3 / Key Findings
4 Survey Methodology
4 Technically Proficient Cybersecurity Professionals Continue to Be in Short Supply
4 / Filling Positions
7 / Unqualified and Insufficient Technical Applicants
9 / More Business Acumen Needed
11 Retaining Cybersecurity Professionals Is Exceptionally Difficult
11 / Retention Issues From a Seller’s Market
12 / Strategies to Combat Loss
13 / Perception of Under-Preparedness
14 Gender Diversity Programs Are Declining, and Their Effectivity Is Directionally Lower
14 / Gender Diversity and Disparity
15 / Gender Gap Mitigation
16 / Enterprise Implications
17 Cybersecurity Budget Increases Are Expected to Slow Slightly
18 Conclusion: Current Trends Present Opportunities for the Bold
19 Acknowledgments
© 2019 ISACA. All Rights Reserved. 2
Personal Copy of Viriato Leao/Lopes De Souza (ISACA ID: 180411)
STATE OF CYBERSECURITY 2019: CURRENT TRENDS IN WORKFORCE DEVELOPMENT
Executive Summary
This year’s global State of Cybersecurity Survey the field is business acumen. Currently, the most-
identifies several challenges in the maturing prized hire in a cybersecurity team is a technically
cybersecurity field. This white paper analyzes the proficient individual who also understands business
survey findings regarding cybersecurity workforce operations and how cybersecurity fits into the
development, staffing, retention, budget implications greater needs of the enterprise.
and gender diversity. In a second white paper, ISACA
• Retaining cybersecurity professionals is
examines the survey results relating to cyberattacks,
exceptionally difficult, and the current
cybersecurity awareness training programs, and
enticement of employer-paid training and
organizational cybersecurity and governance.
certification are not ensuring retention.
Cybersecurity personnel are leaving most often
Key Findings for greater pay, career advancement and perceived
Because enterprises continue to struggle with healthier work environments.
cybersecurity staffing, it is important to analyze in
• Gender diversity programs may be declining, and
detail the factors contributing to the skills gap. This
their effectivity is directionally lower. Less than
year, ISACA research identifies missing talent and
half of the survey-respondent enterprises have a
expertise and pinpoints potential contributing factors.
gender diversity program. The perception of their
The truism “good help is hard to find” is exemplified effectiveness, when compared to previous years, is
in the cybersecurity field. This fact continues to be trending downwards.
reinforced by ISACA’s research and other third-party • Cybersecurity budget increases are expected to
research and analysis. slow slightly. Most survey respondents continue to
expect cybersecurity budgets to increase, but not
The following are key findings relating to the
as much as in the previous year.
cybersecurity workforce:
• Technically proficient cybersecurity professionals The struggle to fill open cybersecurity positions,
continue to be in short supply and difficult to especially technical roles, remains great. Additionally,
find. This fact is compounded when coupled with retention of qualified individuals is proving to be difficult,
the realization that the greatest skill needed in with traditional retention tactics seemingly less effective.
“While the number of high-profile cyberattacks are on the ascent on one side, so are the number
of cybersecurity vacancies going unfilled. The creation of industry and academic programs to
introduce the latest industry, technology, process and effective use of automation to address
the shortage of skilled resources will have to be taken on war-footing.”
RENJU VARGHESE, FELLOW & CHIEF ARCHITECT, CYBERSECURITY & GRC, HCL TECHNOLOGIES
© 2019 ISACA. All Rights Reserved. 3
Personal Copy of Viriato Leao/Lopes De Souza (ISACA ID: 180411)
STATE OF CYBERSECURITY 2019: CURRENT TRENDS IN WORKFORCE DEVELOPMENT
Survey Methodology
In the final quarter of 2018, ISACA sent survey invitations • Cyberattacks and Threats
to a global population of cybersecurity professionals who
• Cyberawareness Training Programs
hold ISACA’s Certified Information Security Manager®
(CISM®) and/or Cybersecurity Nexus Practitioner™ (CSX • Organizational Cybersecurity and Governance
Practitioner™) designations and individuals in information
Due to the nature of the survey, the targeted population
security positions. The survey data were collected
consists of individuals who have cybersecurity job
anonymously via SurveyMonkey. A total of 1,576
responsibilities. Of the 1,576 respondents, 1,020
respondents completed the survey and their responses
indicate that their primary professional area of
are included in the results.1
responsibility is cybersecurity. Figure 1 shows
The survey, which used multiple-choice and Likert scale additional survey-respondent demographic norms.
formats, was organized into six major sections:
It is important to note some characteristics that
• Hiring and Skills reflect the survey population’s diversity. Among those
• Diversity in Cybersecurity surveyed, respondents hailed from over 17 industries
(figure 2).
• Cybersecurity Budgets
Technically Proficient Cybersecurity
Professionals Continue to Be in Short Supply
Filling Positions positions (figure 3). This reflects a one percentage point
decrease from last year’s survey findings2 (59 percent),
In a constantly changing, ever connected threat
indicating that, although the need may have decreased,
landscape, staffing cybersecurity positions appropriately
the actual change is minuscule.
and efficiently becomes one of the most important
objectives to any enterprise. Ensuring that business Furthermore, it is taking longer, on average, for
operations remain secure, functional and predictable enterprises to find and hire qualified cybersecurity
is a hallmark of an appropriately staffed and trained professionals. Enterprises that are languishing at least
cybersecurity organization. Like previous years, however, six months before they are able to fill open cybersecurity
a large hiring gap remains in the cybersecurity field. positions increased six percentage points, from 26
Specifically, 58 percent of survey respondents report percent last year3 to 32 percent this year (figure 4).
that their enterprises have unfilled cybersecurity Compounding the issue, 30 percent of this year’s survey
1 Certain questions included the option to choose “Don’t know” from the list of answers. Where appropriate, “Don’t know” responses were removed from the calculation of findings. Result
percentages are rounded to the nearest integer.
2 ISACA, State of Cybersecurity 2018, Part 1: Workforce Development, April 2018, https://cybersecurity.isaca.org/state-of-cybersecurity#0-part-1-april
3 Ibid.
© 2019 ISACA. All Rights Reserved. 4
Personal Copy of Viriato Leao/Lopes De Souza (ISACA ID: 180411)
STATE OF CYBERSECURITY 2019: CURRENT TRENDS IN WORKFORCE DEVELOPMENT
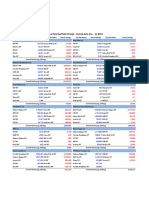
FIGURE 1—RESPONDENT DEMOGRAPHICS
REGIONS
NORTH
94% A M E R I CA EUROPE ASIA
IS ACA
M EM BER
43% 25% 17%
INDUSTRIES
3%
3%
MIDDLE
28 % L AT I N
EAST
A M E R I CA A F R I CA
5% 5%
OCE ANIA
T EC H N O LOGY
S ERV IC E S/C O NS U LT ING
MAIN AREA OF RESPONSIBILITY
20 %
46 % CY BER S EC U R I T Y
M A N AGEM EN T
66%
FIN A N CI A L /BA N K ING
25%
EM PLOY ED IN
A N EN T ER PR IS E
WITH
AT L E A S T
10
I T R IS K
%
1,500
M A N AGEM EN T,
19% AU DI T,
GOV ER N A N C E,
GOV ER N M EN T/MIL I TA RY— CY BER S EC U R I T Y C O M PL I A N C E E M PLOY E E S
N AT IO N A L /S TAT E /LO CA L PR ACT I T IO N ER
© 2019 ISACA. All Rights Reserved. 5
Personal Copy of Viriato Leao/Lopes De Souza (ISACA ID: 180411)
STATE OF CYBERSECURITY 2019: CURRENT TRENDS IN WORKFORCE DEVELOPMENT
FIGURE 2—INDUSTRY SECTORS
In which industry are you employed?
Technology Services/
28%
Consulting
Financial/Banking 20%
Government/Military–
10%
National/State/Local
Other 6%
Manufacturing/Engineering 6%
Health Care/Medical 6%
Insurance 5%
Telecommunications/
5%
Communications
Education/Student 3%
Utilities 2%
Retail/Wholesale/
2%
Distribution
Mining/Construction/ 2%
Petroleum/Agriculture
Transportation 1%
Aerospace 1%
Advertising/Marketing/ 1%
Media
Public Accounting 1%
Pharmaceutical < 1%
Legal/Law/Real Estate < 1%
0% 10% 20% 30% 40% 50% 60% 70% 80% 90% 100%
© 2019 ISACA. All Rights Reserved. 6
Personal Copy of Viriato Leao/Lopes De Souza (ISACA ID: 180411)
STATE OF CYBERSECURITY 2019: CURRENT TRENDS IN WORKFORCE DEVELOPMENT
respondents indicate that cybersecurity positions remain Unqualified and Insufficient
open at least three months before they are filled—
Technical Applicants
representing a five percentage point increase from last
year (figure 4). Analyzing this data holistically, over 60 One of the causes of cybersecurity roles remaining
percent of respondent organizations experience at least unfilled for many months is the lack of qualified
three months of unfilled cybersecurity positions when professionals applying to open positions. Specifically,
hiring new staff. when asked, almost 60 percent of survey respondents
indicate that only 50 percent or less of the applicants
applying to open cybersecurity positions are qualified
(figure 5). Compounding this discovery, 29 percent of
FIGURE 3—ORGANIZATIONS REPORTING UNFILLED CYBERSECURITY POSITIONS
Does your organization have unfilled (open) cybersecurity positions?
Yes 58%
No 35%
Don’t know 7%
0% 10% 20% 30% 40% 50% 60% 70% 80% 90% 100%
FIGURE 4—TIME TO FILL A CYBERSECURITY POSITION
On average, how long does it take your organization to fill a cybersecurity position with a qualified candidate?
< 2 weeks 1%
1 month 5%
2 months 11%
3 months 30%
6 months or more 32%
Cannot fill open positions 3%
Not applicable 5%
Don't know 12%
0% 10% 20% 30% 40% 50% 60% 70% 80% 90% 100%
© 2019 ISACA. All Rights Reserved. 7
Personal Copy of Viriato Leao/Lopes De Souza (ISACA ID: 180411)
STATE OF CYBERSECURITY 2019: CURRENT TRENDS IN WORKFORCE DEVELOPMENT
the survey respondents note that less than one quarter Examining the makeup of these types of unfilled
of applicants have the sufficient qualifications to be cybersecurity positions aids in identifying the type of
considered for open cybersecurity positions (figure 5). talent which is missing within the cybersecurity field
Compared to data from last year’s survey, these overall. The majority of survey respondents report
statistics are basically unchanged and indicate a static that most vacancies are in technical cybersecurity
state of struggle in attracting qualified applicants. positions—52 percent of respondents indicate that
FIGURE 5—PERCENTAGE OF CYBERSECURITY APPLICANTS WHO ARE WELL QUALIFIED
On average, how many cybersecurity applicants are well qualified for the position for which they are applying?
Less than 25% 29%
25 - 50% 30%
50 - 75% 16%
75 - 100% 4%
0% 10% 20% 30% 40% 50% 60% 70% 80% 90% 100%
FIGURE 6—PERCENTAGES OF UNFILLED POSITIONS AT GIVEN ORGANIZATIONAL LEVELS
How many of your unfilled (open) cybersecurity positions are at the following levels?
8%
Individual contributor/ 30%
Technical cybersecurity 52%
10%
25%
Individual contributor/ 53%
Nontechnical cybersecurity 20%
3%
37%
47%
Cybersecurity manager
13%
3%
53%
Senior manager/Director 36%
of cybersecurity 8%
2%
72%
Executive or C-suite 20%
Cybersecurity (e.g., CISO) 5%
2%
0% 10% 20% 30% 40% 50% 60% 70% 80% 90% 100%
None Few Most All
© 2019 ISACA. All Rights Reserved. 8
Personal Copy of Viriato Leao/Lopes De Souza (ISACA ID: 180411)
STATE OF CYBERSECURITY 2019: CURRENT TRENDS IN WORKFORCE DEVELOPMENT
most cybersecurity open positions at their enterprises cybersecurity technical personnel is still strong and
are technical cybersecurity positions at the individual growing across enterprises.
contributor level (figure 6). Conversely, few cybersecurity
executive or C-suite positions are unfilled—72 percent of More Business Acumen Needed
respondents indicate that their enterprises have no Although the cybersecurity field has a great need for
cybersecurity executive position openings (figure 6). technical competence and qualifications, it also suffers
from a lack of business comprehension. Specifically, the
Adding to these hiring needs, 75 percent of survey
biggest skill gap in the average cybersecurity
respondents expect an increase in hiring demand for
professional that survey respondents identified is the
technical professionals, with no specific role or level
ability to understand the business. Forty-nine percent of
experiencing a noteworthy decline in demand (figure 7).
respondents identify this ability as the biggest skill gap,
This is relatively inline with the 77 percent response
and 34 percent report that the biggest skill gap is
from last year’s survey, showing a minimal change.
technical skills (figure 8). This data, combined with the
Comparing this year’s survey responses to the previous
large need for technically skilled individuals, helps to
year’s data for the same question reveals negligible
determine the ideal cybersecurity professional in today’s
changes in trends, indicating that the need for
FIGURE 7—HIRING DEMAND PER ORGANIZATIONAL LEVEL
In the next year, which of these levels do you see the hiring demand increasing, decreasing or remaining the same?
75%
Individual contributor/ 23%
Technical cybersecurity
2%
44%
Individual contributor/ 51%
Nontechnical cybersecurity
5%
42%
Cybersecurity manager 55%
3%
29%
Senior manager/ 67%
Director of cybersecurity
4%
21%
Executive or C-suite 75%
cybersecurity ( e.g., Ciso)
4%
0% 10% 20% 30% 40% 50% 60% 70% 80% 90% 100%
Increase No change Decrease
© 2019 ISACA. All Rights Reserved. 9
Personal Copy of Viriato Leao/Lopes De Souza (ISACA ID: 180411)
STATE OF CYBERSECURITY 2019: CURRENT TRENDS IN WORKFORCE DEVELOPMENT
FIGURE 8—BIGGEST SKILL GAP
What is the biggest skill gap you see in today’s cybersecurity professionals?
Ability to understand
49%
the business
Technical skills 34%
Communication skills 17%
0% 10% 20% 30% 40% 50% 60% 70% 80% 90% 100%
environment—a technically proficient cybersecurity that recent university graduates in cybersecurity are
professional who is able to understand an enterprise’s well prepared for challenges within an enterprise;
business strategy. Indeed, an individual who can 39 percent of respondents disagree or strongly
successfully apply his or her technical cybersecurity disagree; and 38 percent neither agree nor disagree
skillset to effectively enhance business goals and who (figure 9). Analysis of this data can create multiple
can articulate that connection to counterparts at multiple interpretations. First, like many fields of study, formal
organizational levels has a bright future in the field. education alone does not necessarily provide turn-
key-ready professionals. Second, although some
Discovering and hiring individuals to meet this great academic institutions are implementing successful
need within the cybersecurity field has received some technical programs, most are still perceived as
help from more traditional academic institutions; training cybersecurity in abstraction, rather than
however, additional work is required. Twenty-four training it as a technical, hands-on field, which, by its
percent of survey respondents agree or strongly agree very nature, requires some business intelligence.
FIGURE 9—DEGREE TO WHICH UNIVERSITY GRADUATES ARE WELL PREPARED FOR
CYBERSECURITY CHALLENGES
To what extent do you agree or disagree that recent university graduates in cybersecurity are well prepared for the
cybersecurity challenges in your organization?
Strongly agree 2%
Agree 22%
Neither agree nor disagree 38%
Disagree 30%
Strongly disagree 9%
0% 10% 20% 30% 40% 50% 60% 70% 80% 90% 100%
© 2019 ISACA. All Rights Reserved. 10
Personal Copy of Viriato Leao/Lopes De Souza (ISACA ID: 180411)
STATE OF CYBERSECURITY 2019: CURRENT TRENDS IN WORKFORCE DEVELOPMENT
Retaining Cybersecurity Professionals
Is Exceptionally Difficult
Retention Issues From a Seller’s Market respondents indicate that most cybersecurity
professionals left their organizations for better financial
The environment of need in the cybersecurity field
incentives, such as salaries or bonuses, at other
has led to a strong seller’s market for cybersecurity
organizations. Over half of respondents also accredit
professionals, creating a retention problem for
promotion and development opportunities as
enterprises. When asked if their organization has
contributing to retention struggles, and nearly half
experienced difficulties retaining qualified cybersecurity
of respondents indicate that individuals left their
professionals, 64 percent of survey respondents replied
organization for a better work culture or environment
affirmatively. An overwhelming 82 percent of survey
(figure 10).
FIGURE 10—WHY CYBERSECURITY PROFESSIONALS LEAVE THEIR JOBS
Which of the following factors do you feel are causing cybersecurity professionals to leave their job roles?
Better financial incentives 82%
(e.g., salaries or bonuses)
Promotion and 57%
development opportunities
Better work culture/ 46%
environment
Flexible work policies 37%
Opportunities to work with 35%
latest technologies (e.g., AI)
Remote work possibilities 33%
Lower work stress levels 30%
Family situation changes 18%
(e.g., children born, marriage)
Chance to work in 16%
new industry
Other reasons 9%
More diverse workplace 8%
Retirement 8%
Switching careers (e.g., leaving 8%
cybersecurity entirely)
0% 10% 20% 30% 40% 50% 60% 70% 80% 90% 100%
© 2019 ISACA. All Rights Reserved. 11
Personal Copy of Viriato Leao/Lopes De Souza (ISACA ID: 180411)
STATE OF CYBERSECURITY 2019: CURRENT TRENDS IN WORKFORCE DEVELOPMENT
These findings indicate that a seller’s market currently some organizations mitigate the retention issue by
exits in the cybersecurity field. Enterprises are offering requiring training agreements that include post-training
higher pay, career advancement and appealing work term requirements, ensuring that employees do not
environments to lure proven cybersecurity talent away leave immediately after receiving training; otherwise,
from other enterprises. These incentives are impactful they experience stiff financial penalties.
for any work field; however, in the context of the large
skill and capability gap in the cybersecurity field, it is Other retention efforts utilized by respondents include
understandable that the contributing factors are more increased use of contract employees and outside
prevalent when compared to other professions’ trends consultants (36 percent) and increased reliance on
in retaining skilled staff. certification to attest to actual skill mastery (23
percent) (figure 11). These methods are also proven
Strategies to Combat Loss and commonplace in other professions. Leveraging a
third party for cybersecurity purposes shifts the
Enterprises are implementing multiple strategies to
staffing requirements, including recruiting and
retain cybersecurity professionals. One frequently used
retaining staff, to another organization. This method
incentive is providing additional training. Fifty-seven
allows an enterprise to decrease any potential risk that
percent of respondents indicate that their enterprises
may arise from attempting to obtain and maintain
undertake increased training as an incentive for
cybersecurity professionals natively. The use of
employees to stay at their enterprises (figure 11). The
certifications is also an understandable method of
prevalence of this retention tool is understandable,
retention as individuals in the cybersecurity field find
because both the individual and the enterprise benefit
great professional pride and personal satisfaction in
from more highly trained professionals. Additionally,
obtaining a certification in the field.
FIGURE 11—MEANS TO MITIGATE CYBERSECURITY SKILLS GAP
Which, if any, of the following has your organization undertaken to help decrease this cybersecurity skills gap?
Increased training of staff 57%
Increased usage of
contract employees or 36%
outside consultants
Increased reliance on
certification to attest to 23%
actual skill mastery
Increased reliance on
artificial intelligence 18%
or automation
Nothing has been done 15%
Organization has
no skills gap 3%
0% 10% 20% 30% 40% 50% 60% 70% 80% 90% 100%
© 2019 ISACA. All Rights Reserved. 12
Personal Copy of Viriato Leao/Lopes De Souza (ISACA ID: 180411)
STATE OF CYBERSECURITY 2019: CURRENT TRENDS IN WORKFORCE DEVELOPMENT
Eighteen percent of respondents indicate that their Perception of Under-Preparedness
enterprises are relying more heavily on artificial
The lack of trained cybersecurity professionals
intelligence to decrease the cybersecurity skills gap
profoundly impacts enterprises and the professionals
(figure 11). Although these software solutions and
within them. Almost 70 percent of respondents believe
networked algorithms are becoming more prevalent in
that their enterprise’s cybersecurity team is understaffed,
all fields, they have yet to prove themselves as capable
with over 20 percent of respondents indicating that they
of complete workforce replacement. Respondents were
perceive their enterprise as significantly understaffed
not asked to indicate the effectiveness of these artificial
(figure 12). Despite leveraging incentives, such as
intelligence tools as replacements for trained and
education and certification opportunities, these
experienced human beings.
enticements are seemingly insufficient in the current
market to retain individuals. As a result, an overall
perception of under-preparedness arises.
FIGURE 12—PERCEPTION OF CYBERSECURITY STAFFING LEVELS
Do you feel that your organization’s cybersecurity team is currently:
Significantly understaffed 21%
Somewhat understaffed 48%
Appropriately staffed 25%
Somewhat overstaffed 2%
Significantly overstaffed 1%
Don’t know 2%
0% 10% 20% 30% 40% 50% 60% 70% 80% 90% 100%
© 2019 ISACA. All Rights Reserved. 13
Personal Copy of Viriato Leao/Lopes De Souza (ISACA ID: 180411)
STATE OF CYBERSECURITY 2019: CURRENT TRENDS IN WORKFORCE DEVELOPMENT
Gender Diversity Programs Are Declining,
and Their Effectivity Is Directionally Lower
Gender Diversity and Disparity there are significantly more men that women occupying
cybersecurity roles within their enterprise (figure 13).
The survey results identify a male dominant field in
cybersecurity—89 percent of respondents indicate that While this trend of a male-dominated cybersecurity
there are more men than women in cybersecurity roles work field is noteworthy, most respondents believe that
within their enterprise (figure 13). Of note, 15 percent of women are offered the same opportunities for career
respondents indicate that their entire cybersecurity advancement as men, with 80 percent responding that
group is comprised of men and 51 percent report that opportunity is equally distributed (figure 14). However,
FIGURE 13—PROPORTION OF MEN VS. WOMEN IN CYBERSECURITY ROLES
How would you describe the current proportion of men versus women in cybersecurity roles in your organization?
All men 15%
Significantly more
51%
men than women
Somewhat more
23%
men than women
Equal numbers of
8%
men and women
Somewhat more 2%
women than men
Significantly more 0%
women than men
All women 0%
0% 10% 20% 30% 40% 50% 60% 70% 80% 90% 100%
FIGURE 14—GENDER DISPARITY
Do you believe that women are offered the same opportunities for career advancement as men are offered in the field of
cybersecurity in your organization?
Yes 80%
No 20%
0% 10% 20% 30% 40% 50% 60% 70% 80% 90% 100%
© 2019 ISACA. All Rights Reserved. 14
Personal Copy of Viriato Leao/Lopes De Souza (ISACA ID: 180411)
STATE OF CYBERSECURITY 2019: CURRENT TRENDS IN WORKFORCE DEVELOPMENT
further analysis provides potentially more meaningful women in cybersecurity roles. This result may be due to
insight. Of respondents who identify as female, the fact that 71 percent of respondents indicate they
only 41 percent believe that opportunity for career have no difficulty in retaining women in cybersecurity
advancement is equally distributed (figure 15). This roles (figure 16).
response represents a downward trend from last
year’s survey, which indicated that 51 percent of Gender Gap Mitigation
female respondents believed career advancement Some cybersecurity organizations establish diversity
opportunities were equally distributed. programs to support women in the field. These
programs take many forms, most often with the goal to
Compounding the downward trend of opportunity
ensure that women have the same level of access to
perception, just over half of the survey respondents
training and advancement opportunities as men.
(56 percent) indicate that their organization does not
Compared to last year, however, the ISACA survey
currently have a goal of increasing the number of
FIGURE 15—BREAKDOWN OF GENDER DISPARITY RESPONSES
Do you believe that women are offered the same opportunities for career advancement as men are offered in the field of
cybersecurity in your organization?
41%
Yes
79%
51%
No
12%
8%
Don’t know
9%
0% 10% 20% 30% 40% 50% 60% 70% 80% 90% 100%
Female Male
FIGURE 16—RETENTION OF WOMEN IN CYBERSECURITY ROLES WITHIN AN ORGANIZATION
Has your organization experienced difficulty in retaining women in cybsersecurity roles?
Yes 29%
No 71%
0% 10% 20% 30% 40% 50% 60% 70% 80% 90% 100%
© 2019 ISACA. All Rights Reserved. 15
Personal Copy of Viriato Leao/Lopes De Souza (ISACA ID: 180411)
STATE OF CYBERSECURITY 2019: CURRENT TRENDS IN WORKFORCE DEVELOPMENT
FIGURE 17—DIVERSITY PROGRAMS
Does your organization have in place specific diversity programs to support women cybersecurity professionals?
Yes 44%
No 56%
0% 10% 20% 30% 40% 50% 60% 70% 80% 90% 100%
shows that these programs may be declining. with a diversity program believe equal opportunity
Correlating directly to the question about whether an for advancement exists within their enterprise (a
enterprise has a goal of increasing the number of three-percentage-point increase from last year).
women in cybersecurity roles (44 percent of this year’s The gap between men’s and women’s perceptions
respondents report that this is a goal), when in organizations that have a diversity program has
respondents were asked if their enterprises have increased from 10 percentage points last year to 31
specific diversity programs to support women percentage points this year. In short, when comparing
cybersecurity professionals, 44 percent also report last year’s data to this year’s data, the effectiveness of
affirmatively (figure 17). This represents a seven- diversity programs appears to be trending downward,
percentage-point decrease from the previous year. at least with regard to women’s perceptions of
these programs.
In addition to the decline in the number of programs
supporting women cybersecurity professionals, those Enterprise Implications
that are in place are arguably decreasing in
Previous reporting and surveys have indicated that
effectiveness. Among respondents in enterprises with a
diversity programs may have aided in providing variety
diversity program, 59 percent of women believe that
to the workforce. Analysis of the current data should
women are offered the same opportunities for
prompt consideration and potential reappraisal of these
career advancement as men. This represents an
programs’ impact and effectiveness. However, those
18-percentage-point decrease compared to last year, the
enterprises that do have female cybersecurity talent
first year that diversity data was collected. In contrast,
should find reassurance in the strong retention
this year, 90 percent of men respondents in enterprises
numbers of those professionals.
© 2019 ISACA. All Rights Reserved. 16
Personal Copy of Viriato Leao/Lopes De Souza (ISACA ID: 180411)
STATE OF CYBERSECURITY 2019: CURRENT TRENDS IN WORKFORCE DEVELOPMENT
Cybersecurity Budget Increases
Are Expected to Slow Slightly
Compared to last year, cybersecurity budgets are cybersecurity budgets (figure 18), which is a decrease
expected to decrease in 2019, but not to the lower levels of nine points from last year’s 64 percent. These results
of previous years. Specifically, when asked, 55 percent seem to align with a cyclical pattern where every other
of respondents report that they expect an increase in year cybersecurity budgets increase.
FIGURE 18—CHANGE IN ENTERPRISE SECURITY BUDGETS
How, if any, will your organization’s cybersecurity budget change in the next twelve months?
It will significantly increase 8%
It will somewhat increase 47%
It will stay the same 34%
It will somewhat decrease 9%
It will significantly decrease 3%
0% 10% 20% 30% 40% 50% 60% 70% 80% 90% 100%
FIGURE 19—PERCEPTION OF CYBERSECURITY BUDGET FUNDING LEVEL
Do you feel your organization’s cybersecurity budget is currently...
Significantly underfunded 19%
Somewhat underfunded 41%
Appropriately funded 34%
Somewhat overfunded 3%
Significantly overfunded 2%
0% 10% 20% 30% 40% 50% 60% 70% 80% 90% 100%
© 2019 ISACA. All Rights Reserved. 17
Personal Copy of Viriato Leao/Lopes De Souza (ISACA ID: 180411)
STATE OF CYBERSECURITY 2019: CURRENT TRENDS IN WORKFORCE DEVELOPMENT
These changing financial projections may act as significantly underfunded (figure 19). Analysis of these
reflections of current budget perceptions. Sixty percent statistics, in combination with the decreased budgetary
of survey respondents indicate that they feel that their expectations, may have the potential to create under-
cybersecurity budget is currently underfunded, with supported cybersecurity staff and tools, feeding the
nearly 20 percent believing that their budgets are retention struggles of the previously identified findings.
Conclusion: Current Trends Present
Opportunities for the Bold
The cybersecurity workforce gap is becoming more Although these statistics may prove disheartening to
pronounced as talent becomes more difficult to find. some, they actually present great opportunity for
These strong headwinds are compounded by a enterprises with initiative. Today’s skilled cybersecurity
suppliers’ market for the talent that exists, creating a professionals are in high demand. Organizations that
highly competitive environment in which traditional acknowledge the statistics shown in this research
retention strategies—such as education and should be able to fill open positions quicker and retain
certification incentives—lose out to incentives like their current talent. The successful hiring and retention
greater pay and career advancement that entice elements are attractive pay, career growth opportunities
individuals to seek employment at a different and healthy work environments. However, enterprises
enterprise. Furthermore, organizational attempts to that rely solely on old approaches and the status quo
diversify the workforce and create greater gender approach may continue to experience hiring and
inclusion are failing to meet the expectations of retention issues.
individuals within the field, many of whom those
programs are designed to benefit. Finally, expectations
of lower budgets will continue to feed the reality of
underfunded security programs and insufficient staff.
© 2019 ISACA. All Rights Reserved. 18
Personal Copy of Viriato Leao/Lopes De Souza (ISACA ID: 180411)
STATE OF CYBERSECURITY 2019: CURRENT TRENDS IN WORKFORCE DEVELOPMENT
Acknowledgments
ISACA would like to recognize:
Lead Developer ISACA Board of Directors
T. Frank Downs Rob Clyde, Chair Theresa Grafenstine
CEH, CEI, ECSA, LPT CISM ISACA Board Chair, 2017-2018
ISACA, USA Clyde Consulting LLC, USA CISA, CRISC, CGEIT, CGAP, CGMA, CIA,
CISSP, CPA
Brennan Baybeck, Vice-Chair
Deloitte & Touche LLP, USA
Expert Reviewers CISA, CRISC, CISM, CISSP
Oracle Corporation, USA Chris K. Dimitriadis, Ph.D.
Dustin Brewer ISACA Board Chair, 2015-2017
Tracey Dedrick
CSXP, CEH, CHFI, CSIS CISA, CRISC, CISM
Former Chief Risk Officer with Hudson
ISACA, USA INTRALOT, Greece
City Bancorp, USA
Marie Gilbert
Leonard Ong
ISACA, USA
CISA, CRISC, CISM, CGEIT, COBIT 5
Karen Heslop, J.D. Implementer and Assessor, CFE, CIPM,
ISACA, USA CIPT, CISSP, CITBCM, CPP, CSSLP,
GCFA, GCIA, GCIH, GSNA, ISSMP-ISSAP,
PMP
Merck & Co., Inc., Singapore
R.V. Raghu
CISA, CRISC
Versatilist Consulting India Pvt. Ltd.,
India
Gabriela Reynaga
CISA, CRISC, COBIT 5 Foundation, GRCP
Holistics GRC, Mexico
Gregory Touhill
CISM, CISSP
Cyxtera Federal Group, USA
Ted Wolff
CISA
Vanguard, Inc., USA
Tichaona Zororo
CISA, CRISC, CISM, CGEIT, COBIT 5
Assessor, CIA, CRMA
EGIT | Enterprise Governance of IT (Pty)
Ltd, South Africa
© 2019 ISACA. All Rights Reserved. 19
Personal Copy of Viriato Leao/Lopes De Souza (ISACA ID: 180411)
STATE OF CYBERSECURITY 2019: CURRENT TRENDS IN WORKFORCE DEVELOPMENT
About ISACA
Now in its 50th-anniversary year, ISACA® (isaca.org) is a global association helping
individuals and enterprises achieve the positive potential of technology. Today’s world 1700 E. Golf Road, Suite 400
is powered by information and technology, and ISACA equips professionals with Schaumburg, IL 60173, USA
the knowledge, credentials, education and community to advance their careers and
transform their organizations. ISACA leverages the expertise of its 460,000 engaged Phone: +1.847.660.5505
professionals—including its 140,000 members—in information and cybersecurity, Fax: +1.847.253.1755
governance, assurance, risk and innovation, as well as its enterprise performance Support: support.isaca.org
Web: www.isaca.org
subsidiary, CMMI® Institute, to help advance innovation through technology. ISACA
has a presence in more than 188 countries, including more than 220 chapters
worldwide and offices in both the United States and China.
Provide feedback:
About HCL www.isaca.org/state-of-cybersecurity-2019
HCL Technologies (HCL) is a leading global technology company that helps global
Participate in the ISACA Online Forums:
enterprises reimagine and transform their businesses through digital technology.
https://engage.isaca.org/onlineforums
HCL operates in 44 countries and had consolidated revenues of US $8.4 billion for
the 12 months ending 31 December 2018. HCL provides an integrated portfolio of Twitter:
services informed by its Mode 1-2-3 growth strategy. Mode 1 encompasses core www.twitter.com/ISACANews
services in the areas of applications, infrastructure, business processes outsourcing
(BPO) and engineering, research and development services, leveraging DRYiCE™ LinkedIn:
Autonomics to transform clients’ business and IT landscape, making them lean and www.linkedin.com/company/isaca
agile. Mode 2 focuses on experience-centric, outcome-oriented, integrated offerings
of Digital and Analytics, IoT WoRKS™, Cloud Native Services, and Cybersecurity Facebook:
and GRC services to drive business outcomes and enable enterprise digitization. www.facebook.com/ISACAHQ
Mode-3 strategy is ecosystem-driven, creating innovative IP-partnerships to build
product and platform business. HCL leverages its global network of integrated Instagram:
co-innovation labs to provide holistic multiservice delivery in key industry verticals www.instagram.com/isacanews
including financial services, manufacturing, telecommunications, media, publishing,
entertainment, retail and consumer packaged goods, life sciences and healthcare,
oil and gas, energy and utilities, travel, transportation and logistics, and government.
With 132,328 professionals from diverse nationalities, HCL creates real value for
customers by taking ‘Relationships Beyond the Contract’. For more information,
please visit www.hcltech.com.
Disclaimer
ISACA has designed and created State of Cybersecurity 2019, Part 1: Current Trends
in Workforce Development (the “Work”) primarily as an educational resource for
IT professionals. ISACA makes no claim that use of any of the Work will assure a
successful outcome. The Work should not be considered inclusive of all proper
information, procedures and tests or exclusive of other information, procedures and
tests that are reasonably directed to obtaining the same results. In determining the
propriety of any specific information, procedure or test, IT professionals should apply
their own professional judgments to the specific circumstances presented by the
systems or information technology environment.
RESERVATION OF RIGHTS
© 2019 ISACA. All rights reserved.
© 2019 ISACA. All Rights Reserved. 20
Personal Copy of Viriato Leao/Lopes De Souza (ISACA ID: 180411)
STATE OF CYBERSECURITY 2019: CURRENT TRENDS IN WORKFORCE DEVELOPMENT
© 2019 ISACA. All Rights Reserved. 21
Personal Copy of Viriato Leao/Lopes De Souza (ISACA ID: 180411)
You might also like
- State of Cybersecurity 2019 Part 1 Res Eng 0319Document21 pagesState of Cybersecurity 2019 Part 1 Res Eng 0319Elena VaciagoNo ratings yet
- State of Cybersecurity 2023Document43 pagesState of Cybersecurity 2023Tsifitahy SojaveloNo ratings yet
- RPT Cybersecurity Workforce ShortageDocument24 pagesRPT Cybersecurity Workforce ShortageGustavo SánchezNo ratings yet
- ISC2_Cybersecurity_Workforce_Study_2023Document84 pagesISC2_Cybersecurity_Workforce_Study_2023thecodehasbytesNo ratings yet
- How To Minimize The Impact of The Cyber Security Skills Shortage TrustwaveDocument15 pagesHow To Minimize The Impact of The Cyber Security Skills Shortage TrustwaveRezu JavNo ratings yet
- Can. Trust. Will.: Hiring for the Human Element in the New Age of CybersecurityFrom EverandCan. Trust. Will.: Hiring for the Human Element in the New Age of CybersecurityRating: 5 out of 5 stars5/5 (1)
- Wombat - Proofpoint - 2019 State of The Phish Report - FinalDocument23 pagesWombat - Proofpoint - 2019 State of The Phish Report - FinalTyler DurdenNo ratings yet
- Scalar Security Study 2019Document76 pagesScalar Security Study 2019Andrew Richard ThompsonNo ratings yet
- 2023 Phishing by Industry Benchmarking ReportDocument35 pages2023 Phishing by Industry Benchmarking Reportoria001No ratings yet
- RP Hacking Skills ShortageDocument20 pagesRP Hacking Skills ShortageRobin RichardsonNo ratings yet
- State of Cybersecurity 2020: Part 2: Threat Landscape and Security PracticesDocument23 pagesState of Cybersecurity 2020: Part 2: Threat Landscape and Security PracticesRey2000No ratings yet
- State of Cybersecurity 2020: Part 2: Threat Landscape and Security PracticesDocument23 pagesState of Cybersecurity 2020: Part 2: Threat Landscape and Security PracticesCarlos Fernández100% (1)
- Skill Gaps in Cybersecurity - Talent - FinalDocument2 pagesSkill Gaps in Cybersecurity - Talent - FinalAzmat PathanNo ratings yet
- Ey Federal Cybersecurity Trends ReportDocument30 pagesEy Federal Cybersecurity Trends ReportshirouhxNo ratings yet
- TR EB Cybersec Career2Document10 pagesTR EB Cybersec Career2RothNo ratings yet
- Securing What's Now and What's Next: 20 Cybersecurity Considerations For 2020Document25 pagesSecuring What's Now and What's Next: 20 Cybersecurity Considerations For 2020Lidia MefNo ratings yet
- Rethinking Security Operations: Creating Clarity Out of ComplexityDocument14 pagesRethinking Security Operations: Creating Clarity Out of ComplexityLuisNo ratings yet
- CISM Overview of Domains - Infosec ResourcesDocument10 pagesCISM Overview of Domains - Infosec ResourcesTyler DurdenNo ratings yet
- State of Cybersecurity 2021: Part 1: Global Update On Workforce Efforts, Resources and BudgetsDocument29 pagesState of Cybersecurity 2021: Part 1: Global Update On Workforce Efforts, Resources and BudgetssamanNo ratings yet
- State of The Internal Audit 2019 PDFDocument22 pagesState of The Internal Audit 2019 PDFAlexchandar AnbalaganNo ratings yet
- Wp Combat the Cyber Skills ShortageDocument7 pagesWp Combat the Cyber Skills Shortageeliud.cardenasNo ratings yet
- Building A Resilient Cybersecurity CultureDocument8 pagesBuilding A Resilient Cybersecurity CultureSaborYpan ReyesNo ratings yet
- Top Causes of Security BreachesDocument6 pagesTop Causes of Security BreachesMarcelo Plada IntNo ratings yet
- ISC2 Cybersecurity Workforce Study 2019Document37 pagesISC2 Cybersecurity Workforce Study 2019Dinesh GaikwadNo ratings yet
- FTNT 2023 Security Awareness and Training BriefDocument15 pagesFTNT 2023 Security Awareness and Training BriefAOSantanaNo ratings yet
- Africa Cyber Security Report 2017Document88 pagesAfrica Cyber Security Report 2017kskabuye100% (1)
- Cybersecurity Fundamentals Certificate Fact Sheet - 0318Document2 pagesCybersecurity Fundamentals Certificate Fact Sheet - 0318Mithun LomateNo ratings yet
- The State of Cybersecurity in AssociationsDocument17 pagesThe State of Cybersecurity in AssociationsSagayam MartinNo ratings yet
- Cybersecurity As A Business Differentiator: Susan WhittemoreDocument10 pagesCybersecurity As A Business Differentiator: Susan WhittemoreMADHUSUDAN DASNo ratings yet
- Isc2 Cyberedge 2020 CDR Report v10 - 641567Document58 pagesIsc2 Cyberedge 2020 CDR Report v10 - 641567Forense OrlandoNo ratings yet
- SanjoseDocument3 pagesSanjosekristinacassandra sanjoseNo ratings yet
- Rep 3Document5 pagesRep 3Sornali PaulNo ratings yet
- Article-Preparing CC Profesional To Make Impact-Nice - Rfi - Final - IsacaDocument8 pagesArticle-Preparing CC Profesional To Make Impact-Nice - Rfi - Final - IsacaharaikamuNo ratings yet
- Agents of Change: Women in The Information Security ProfessionDocument15 pagesAgents of Change: Women in The Information Security ProfessionAnca DbjNo ratings yet
- Sage Smbs Cyber Security Report GBDocument28 pagesSage Smbs Cyber Security Report GBvenusrambo8No ratings yet
- The Unsolved Opportunities For Cybersecurity ProvidersDocument6 pagesThe Unsolved Opportunities For Cybersecurity ProvidersMohamed TaufiqhNo ratings yet
- Information Security Benchmark 2019: A Balanced View On The Information Security LandscapeDocument20 pagesInformation Security Benchmark 2019: A Balanced View On The Information Security LandscapeJonas MeierNo ratings yet
- ESG Showcase Stellar Cyber Solutions Mar 2020Document5 pagesESG Showcase Stellar Cyber Solutions Mar 2020bienth89No ratings yet
- The Global State of Information Security Survey 2018Document8 pagesThe Global State of Information Security Survey 2018RogerNo ratings yet
- 0000 Eb Cybersecurity Risk Survey FileDocument13 pages0000 Eb Cybersecurity Risk Survey FileMd likhonNo ratings yet
- Re-Engineering Cybersecurity Education in The US: An Analysis of The Critical FactorsDocument9 pagesRe-Engineering Cybersecurity Education in The US: An Analysis of The Critical FactorsCom DigfulNo ratings yet
- CYBERSECURITY FOR MANAGERS: BUILD YOUR ACTION PLAN (39 charactersDocument13 pagesCYBERSECURITY FOR MANAGERS: BUILD YOUR ACTION PLAN (39 charactersshadab umairNo ratings yet
- Report Cybersecurity Great ConsultantDocument24 pagesReport Cybersecurity Great Consultantmraza17No ratings yet
- Future Proofing Internal AuditDocument21 pagesFuture Proofing Internal AuditPrince WasindaNo ratings yet
- A Best Practices Guide for Comprehensive Employee Awareness ProgramsFrom EverandA Best Practices Guide for Comprehensive Employee Awareness ProgramsNo ratings yet
- Blazic (2021) - The Cybersecurity Labour Shortage in EuropeDocument13 pagesBlazic (2021) - The Cybersecurity Labour Shortage in EuropeIvan BornacellyNo ratings yet
- Securing The Digital FutureDocument28 pagesSecuring The Digital FutureHardhik ChitaliaNo ratings yet
- Privacy in Practice 2022Document25 pagesPrivacy in Practice 2022shakawathNo ratings yet
- SailPoint Horizons of Identity Security Report 2023 SP2336Document39 pagesSailPoint Horizons of Identity Security Report 2023 SP2336pnorbertoNo ratings yet
- Cybersecurity Career Paths and Progressionv2Document18 pagesCybersecurity Career Paths and Progressionv2Madhur Hase100% (2)
- Cyber Security Maturity Assessment Framework For Technology Startups A Systematic Literature ReviewDocument11 pagesCyber Security Maturity Assessment Framework For Technology Startups A Systematic Literature ReviewZukoNo ratings yet
- Skilling & Empowering Women in Cyber Security: A Joint Skills Initiative ofDocument5 pagesSkilling & Empowering Women in Cyber Security: A Joint Skills Initiative ofqwertyNo ratings yet
- ESG ISSA Research Report Abstract Life of Cybersecurity Professionals Nov 2017 PDFDocument9 pagesESG ISSA Research Report Abstract Life of Cybersecurity Professionals Nov 2017 PDFAnonymous w1asC3A1qNo ratings yet
- 2Document28 pages2omar.fariedNo ratings yet
- Final CyberDocument27 pagesFinal Cyberomar.fariedNo ratings yet
- Building A Cyber Fitness and Resilience in Financial Institutions in Nigeria Using Hack Ability Score Technique and Cyber Security Self-Assessment ToolDocument11 pagesBuilding A Cyber Fitness and Resilience in Financial Institutions in Nigeria Using Hack Ability Score Technique and Cyber Security Self-Assessment ToolInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Part 2 CyberDocument10 pagesPart 2 Cyberjmutongu90No ratings yet
- (ISC) 2-IDC 2004 Global Information Security Workforce StudyDocument30 pages(ISC) 2-IDC 2004 Global Information Security Workforce StudyHiba AfanehNo ratings yet
- MSFT Cloud Architecture SecurityDocument9 pagesMSFT Cloud Architecture SecurityPratik KadamNo ratings yet
- Owner's Manual: WAS / WYS SeriesDocument20 pagesOwner's Manual: WAS / WYS SeriesViriato LeaoNo ratings yet
- Circle of 5thDocument1 pageCircle of 5thViriato LeaoNo ratings yet
- Owner's Manual: WAS / WYS SeriesDocument20 pagesOwner's Manual: WAS / WYS SeriesViriato LeaoNo ratings yet
- 70 Series Assembled 2 Panel Door Installation Instructions 1018 PDFDocument32 pages70 Series Assembled 2 Panel Door Installation Instructions 1018 PDFViriato LeaoNo ratings yet
- Alliance Key ManagementDocument1 pageAlliance Key ManagementViriato LeaoNo ratings yet
- Oracle EBS AIM Documents PDFDocument2 pagesOracle EBS AIM Documents PDFVKrishna KilaruNo ratings yet
- Economics Problems PDFDocument31 pagesEconomics Problems PDFev xvNo ratings yet
- Atlas Business CentreDocument2 pagesAtlas Business CentreWorkspaceGroupPLCNo ratings yet
- Rule Based-Principal BasedDocument10 pagesRule Based-Principal BasedYuri AnnisaNo ratings yet
- ASE20050 Practice Paper QPDocument6 pagesASE20050 Practice Paper QPRaj ChandaranaNo ratings yet
- FM Leverage SailDocument19 pagesFM Leverage SailMohammad Yusuf NabeelNo ratings yet
- Rwanda Public Procurement Law Covers Tenders, Bids and Procurement MethodsDocument179 pagesRwanda Public Procurement Law Covers Tenders, Bids and Procurement MethodsThéotime HabinezaNo ratings yet
- Competition Policy 2Document64 pagesCompetition Policy 2goyal_khushbu88No ratings yet
- Project Proposal TemplateDocument6 pagesProject Proposal TemplateGomathiNo ratings yet
- Employee EmpowermentDocument21 pagesEmployee EmpowermentLevent Guzel0% (1)
- Brains and BrandsDocument8 pagesBrains and BrandsMarina MarinakiNo ratings yet
- Trading in BinanceDocument11 pagesTrading in BinancededithegamingNo ratings yet
- KeyInitiativeOverview CloudComputingDocument5 pagesKeyInitiativeOverview CloudComputingajay_khandelwalNo ratings yet
- STS1036Document2 pagesSTS1036Shilpa AmitNo ratings yet
- Zachary Lewis ResumeDocument1 pageZachary Lewis Resumeapi-268735873No ratings yet
- 3 - Analysis of Financial Statements 2Document2 pages3 - Analysis of Financial Statements 2Axce1996No ratings yet
- Auditing Trs by IcapDocument53 pagesAuditing Trs by IcapArif AliNo ratings yet
- Business Plan For OutsourcingDocument26 pagesBusiness Plan For Outsourcingadeel77% (13)
- Sectorwise MF Top Share Changes Jul 2019Document45 pagesSectorwise MF Top Share Changes Jul 2019stockengageNo ratings yet
- PO GST 22230489 HanumaDocument2 pagesPO GST 22230489 HanumaSai SwaroopNo ratings yet
- Topic 1 Introduction To AccountingDocument14 pagesTopic 1 Introduction To AccountingSARAH SOFEA BINTI SOFIAN (BG)No ratings yet
- Atswa Cost AccountingDocument504 pagesAtswa Cost AccountingIbrahim MuyeNo ratings yet
- Rupee Appreciation & Its Impact On Indian EconomyDocument20 pagesRupee Appreciation & Its Impact On Indian EconomyShweta Gopika ChopraNo ratings yet
- Research Paper 2.6.1Document26 pagesResearch Paper 2.6.1Rianne Oosting0% (1)
- Chapter 1Document12 pagesChapter 1Jessica100% (1)
- RMK Akm 2-CH 21Document14 pagesRMK Akm 2-CH 21Rio Capitano0% (1)
- Verification of Model Transformations: A Case Study With BPELDocument17 pagesVerification of Model Transformations: A Case Study With BPELFatih ÖzulucanNo ratings yet
- Breaking The Time Barrier PDFDocument70 pagesBreaking The Time Barrier PDFCalypso LearnerNo ratings yet
- TMEICDocument2 pagesTMEICGunjan KhutNo ratings yet
- Chapter 14 Exchange Rates and The Foreign Exchange Market An Asset ApproachDocument61 pagesChapter 14 Exchange Rates and The Foreign Exchange Market An Asset ApproachBill BennttNo ratings yet