Professional Documents
Culture Documents
Mcafee Data Loss Prevention 9.2.0: Installation Guide
Uploaded by
kishorsriramOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Mcafee Data Loss Prevention 9.2.0: Installation Guide
Uploaded by
kishorsriramCopyright:
Available Formats
Installation Guide
Revision A
McAfee Data Loss Prevention 9.2.0
COPYRIGHT
Copyright © 2012 McAfee, Inc. Do not copy without permission.
TRADEMARK ATTRIBUTIONS
McAfee, the McAfee logo, McAfee Active Protection, McAfee AppPrism, McAfee Artemis, McAfee CleanBoot, McAfee DeepSAFE, ePolicy Orchestrator,
McAfee ePO, McAfee EMM, McAfee Enterprise Mobility Management, Foundscore, Foundstone, McAfee NetPrism, McAfee Policy Enforcer, Policy Lab,
McAfee QuickClean, Safe Eyes, McAfee SECURE, SecureOS, McAfee Shredder, SiteAdvisor, SmartFilter, McAfee Stinger, McAfee Total Protection,
TrustedSource, VirusScan, WaveSecure, WormTraq are trademarks or registered trademarks of McAfee, Inc. or its subsidiaries in the United States and
other countries. Other names and brands may be claimed as the property of others.
LICENSE INFORMATION
License Agreement
NOTICE TO ALL USERS: CAREFULLY READ THE APPROPRIATE LEGAL AGREEMENT CORRESPONDING TO THE LICENSE YOU PURCHASED, WHICH SETS
FORTH THE GENERAL TERMS AND CONDITIONS FOR THE USE OF THE LICENSED SOFTWARE. IF YOU DO NOT KNOW WHICH TYPE OF LICENSE YOU
HAVE ACQUIRED, PLEASE CONSULT THE SALES AND OTHER RELATED LICENSE GRANT OR PURCHASE ORDER DOCUMENTS THAT ACCOMPANY YOUR
SOFTWARE PACKAGING OR THAT YOU HAVE RECEIVED SEPARATELY AS PART OF THE PURCHASE (AS A BOOKLET, A FILE ON THE PRODUCT CD, OR A
FILE AVAILABLE ON THE WEBSITE FROM WHICH YOU DOWNLOADED THE SOFTWARE PACKAGE). IF YOU DO NOT AGREE TO ALL OF THE TERMS SET
FORTH IN THE AGREEMENT, DO NOT INSTALL THE SOFTWARE. IF APPLICABLE, YOU MAY RETURN THE PRODUCT TO MCAFEE OR THE PLACE OF
PURCHASE FOR A FULL REFUND.
2 McAfee Data Loss Prevention 9.2.0 Installation Guide
Contents
Preface 5
About this guide . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5
Audience . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5
Conventions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5
Find product documentation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6
1 Introduction to McAfee Total Protection for DLP 9.2.0 7
McAfee Unified DLP deployment . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7
Management options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8
McAfee Unified DLP dashboards . . . . . . . . . . . . . . . . . . . . . . . . . 9
Installation scenarios . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 10
2 Setting up the hardware 11
Adding devices and servers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11
Check the shipment . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11
Plan your installation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 12
Rack mount the appliances . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 12
Connect a management console . . . . . . . . . . . . . . . . . . . . . . . . . . . 13
Configure McAfee DLP Manager . . . . . . . . . . . . . . . . . . . . . . . . . . . . 14
Select an integration mode for McAfee DLP Monitor . . . . . . . . . . . . . . . . . . . . 16
SPAN port configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . 16
Network tap configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . 17
Complete the setup . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 18
3 Installing or upgrading the software on Model 4400 19
Download and expand the archive . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
Boot options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 20
Load the primary image . . . . . . . . . . . . . . . . . . . . . . . . . . . . 21
Load the secondary image . . . . . . . . . . . . . . . . . . . . . . . . . . . 21
Install a fresh image . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 22
Set up the next boot option . . . . . . . . . . . . . . . . . . . . . . . . . . 22
Upgrade the products . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 23
Apply a hotfix . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 23
Convert an installation to another DLP product . . . . . . . . . . . . . . . . . . . . . 24
Restoring the drives . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 24
4 Installing or upgrading software on model 1650 and 3650 appliances 25
Download and expand the legacy archive . . . . . . . . . . . . . . . . . . . . . . . . 25
Install the products on legacy servers . . . . . . . . . . . . . . . . . . . . . . . . . 26
Upgrade to 9.2.0 on legacy appliances . . . . . . . . . . . . . . . . . . . . . . . . . 27
5 Configuring McAfee DLP appliances and adding servers 29
Configure McAfee DLP appliances using Setup Wizard . . . . . . . . . . . . . . . . . . . 29
Configure McAfee DLP appliances after installation . . . . . . . . . . . . . . . . . . . . 35
Add McAfee DLP products to McAfee DLP Manager . . . . . . . . . . . . . . . . . . . . 35
McAfee Data Loss Prevention 9.2.0 Installation Guide 3
Contents
Configuring McAfee DLP Prevent . . . . . . . . . . . . . . . . . . . . . . . . . . . 36
MTA requirements for McAfee DLP Prevent . . . . . . . . . . . . . . . . . . . . 37
Configure McAfee DLP Prevent . . . . . . . . . . . . . . . . . . . . . . . . . 37
Add LDAP servers to McAfee DLP Manager . . . . . . . . . . . . . . . . . . . . . . . 38
Add McAfee Logon Collector to McAfee DLP Manager . . . . . . . . . . . . . . . . . . . 40
Add syslog servers to McAfee DLP systems . . . . . . . . . . . . . . . . . . . . . . . 41
Resynchronize McAfee DLP systems with an NTP server . . . . . . . . . . . . . . . . . . 41
Testing the system . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 42
6 Installing McAfee DLP Endpoint 43
Verify system requirements . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 43
Configure the server . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 45
Install McAfee ePolicy Orchestrator . . . . . . . . . . . . . . . . . . . . . . . . . . 45
Install McAfee ePolicy Orchestrator . . . . . . . . . . . . . . . . . . . . . . . . . . 46
Installing McAfee DLP WCF service . . . . . . . . . . . . . . . . . . . . . . . . . . . 47
Install the McAfee DLP WCF service . . . . . . . . . . . . . . . . . . . . . . . 48
Repository folders . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 53
Creating and configuring repository folders . . . . . . . . . . . . . . . . . . . . 54
User and permission sets . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 56
Create and define McAfee DLP administrators . . . . . . . . . . . . . . . . . . . 56
Create and define permission sets . . . . . . . . . . . . . . . . . . . . . . . . 57
DLP permission set options . . . . . . . . . . . . . . . . . . . . . . . . . . . 57
Install the McAfee Data Loss Prevention Endpoint extension . . . . . . . . . . . . . . . . 58
Initialize the DLP Policy console . . . . . . . . . . . . . . . . . . . . . . . . . . . . 58
Upgrade the license . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 60
Check in the McAfee DLP Endpoint package to ePolicy Orchestrator . . . . . . . . . . . . . . 61
Deploying McAfee DLP Endpoint . . . . . . . . . . . . . . . . . . . . . . . . . . . 61
Define a default rule . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 61
Deploy McAfee DLP Endpoint with ePolicy Orchestrator . . . . . . . . . . . . . . . . 62
Verify the installation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 63
Uninstalling McAfee DLP Endpoint . . . . . . . . . . . . . . . . . . . . . . . . . . . 63
7 Integrating McAfee DLP Endpoint into a unified policy system 65
Setting up Unified DLP on ePolicy Orchestrator . . . . . . . . . . . . . . . . . . . . . 66
Install the network extension . . . . . . . . . . . . . . . . . . . . . . . . . 66
Install the UDLP (host) extension . . . . . . . . . . . . . . . . . . . . . . . . 66
Configure McAfee Agent on ePolicy Orchestrator . . . . . . . . . . . . . . . . . . 67
Add an evidence folder on McAfee DLP Manager . . . . . . . . . . . . . . . . . . 67
Connecting McAfee DLP Manager and the ePolicy Orchestrator server . . . . . . . . . . . . 68
Gather ePolicy Orchestrator registration information . . . . . . . . . . . . . . . . 68
Add a McAfee ePO database user for McAfee DLP Manager . . . . . . . . . . . . . . 68
Register McAfee DLP Manager on ePolicy Orchestrator server . . . . . . . . . . . . . 69
Register ePolicy Orchestrator on McAfee DLP Manager . . . . . . . . . . . . . . . . 69
Checking the connection . . . . . . . . . . . . . . . . . . . . . . . . . . . 70
Configuring McAfee DLP Endpoint on McAfee DLP Manager . . . . . . . . . . . . . . . . . 70
Generate a global policy for McAfee DLP Endpoint . . . . . . . . . . . . . . . . . . 71
Maintaining compatibility with installed McAfee clients . . . . . . . . . . . . . . . 71
Set an Agent Override password . . . . . . . . . . . . . . . . . . . . . . . . 72
Set the manual tagging option . . . . . . . . . . . . . . . . . . . . . . . . . 72
Installation and configuration complete . . . . . . . . . . . . . . . . . . . . . . . . . 73
Index 75
4 McAfee Data Loss Prevention 9.2.0 Installation Guide
Preface
This guide provides the information you need to install your McAfee product.
It contains all of the necessary information for installing McAfee® Data Loss Prevention software,
including detailed steps and verification of the installation and configuration process in both the new
hardware platform and legacy appliances. It also includes integration with McAfee® ePolicy
Orchestrator® and McAfee® Data Loss Prevention Endpoint to configure a unified policy installation.
When the process is completed, the user will have a fully functional McAfee DLP hardware and
software implementation that is properly configured.
About this guide
This information describes the guide's target audience, the typographical conventions and icons used
in this guide, and how the guide is organized.
Audience
McAfee documentation is carefully researched and written for the target audience.
The information in this guide is intended primarily for:
• Administrators — People who implement and enforce the company's security program.
• Security officers — People who determine sensitive and confidential data, and define the
corporate policy that protects the company's intellectual property.
Conventions
This guide uses the following typographical conventions and icons.
Book title or Emphasis Title of a book, chapter, or topic; introduction of a new term; emphasis.
Bold Text that is strongly emphasized.
User input or Path Commands and other text that the user types; the path of a folder or program.
Code A code sample.
User interface Words in the user interface including options, menus, buttons, and dialog
boxes.
Hypertext blue A live link to a topic or to a website.
Note: Additional information, like an alternate method of accessing an option.
Tip: Suggestions and recommendations.
McAfee Data Loss Prevention 9.2.0 Installation Guide 5
Preface
Find product documentation
Important/Caution: Valuable advice to protect your computer system,
software installation, network, business, or data.
Warning: Critical advice to prevent bodily harm when using a hardware
product.
Find product documentation
McAfee provides the information you need during each phase of product implementation, from
installation to daily use and troubleshooting. After a product is released, information about the product
is entered into the McAfee online KnowledgeBase.
Task
1 Go to the McAfee Technical Support ServicePortal at http://mysupport.mcafee.com.
2 Under Self Service, access the type of information you need:
To access... Do this...
User documentation 1 Click Product Documentation.
2 Select a product, then select a version.
3 Select a product document.
KnowledgeBase • Click Search the KnowledgeBase for answers to your product questions.
• Click Browse the KnowledgeBase for articles listed by product and version.
6 McAfee Data Loss Prevention 9.2.0 Installation Guide
1 Introduction to McAfee Total Protection
for DLP 9.2.0
McAfee® Data Loss Prevention Manager manages all of the McAfee DLP products from a centralized
console, then displays incidents and events found by them on its dashboards.
In the unified policy design, rules can be configured to find incidents and violations anywhere on an
intranet — in network traffic, in repositories containing structured or unstructured data, and on
endpoints. Actions can also be added to any rule to handle any problem as soon as it is detected.
Contents
McAfee Unified DLP deployment
Management options
Installation scenarios
McAfee Unified DLP deployment
The McAfee DLP products are designed to handle data in motion, data at rest, and data in use.
Figure 1-1 McAfee DLP products deployed
• The McAfee DLP Monitor capture engine analyzes all content on a network, classifies it into types,
and stores the resulting objects on capture partitions. Some traffic can be filtered out to improve
performance.
• McAfee DLP Prevent monitors all email and webmail and applies actions to resolve any problems.
McAfee Data Loss Prevention 9.2.0 Installation Guide 7
1
Introduction to McAfee Total Protection for DLP 9.2.0
Management options
• McAfee DLP Discover monitors file systems and repositories, locates significant data, and reports
data that is in violation of policy.
• McAfee DLP Endpoint finds significant events occurring at endpoints and reports any policy
violations. Endpoint rules and events are managed through the same workflow as the other
products in the McAfee DLP solution.
Management options
McAfee Data Loss Prevention Manager displays incidents and events on McAfee DLP Manager or
McAfee® ePolicy Orchestrator dashboards.
Depending on the installation, there are three options for managing McAfee Data Loss Prevention.
• If McAfee DLP is installed on a Linux appliance, McAfee DLP Manager is used as the management
console. You can log on to the console with a Mozilla Firefox or Microsoft Internet Explorer browser
using the address https://<server IP>.
• If McAfee DLP is installed in ePolicy Orchestrator, log on to the McAfee ePO™ console using the
address https://<server IP:8443>. Mozilla Firefox 3.0.x and Microsoft Internet Explorer 7
browsers are supported.
• If McAfee DLP is run as a virtual appliance, use the VMware vSphere Client to log on to the console.
Virtual appliance installations are beyond the scope of this guide. See the McAfee Data Loss
Prevention 9.2 Virtual Appliance Installation Guide for more information.
8 McAfee Data Loss Prevention 9.2.0 Installation Guide
1
Introduction to McAfee Total Protection for DLP 9.2.0
Management options
McAfee Unified DLP dashboards
All of the management functions are available in each option, but are organized slightly differently.
The McAfee DLP Manager dashboards have tabbed sections that are separate extensions in ePolicy
Orchestrator.
Figure 1-2 McAfee DLP Manager
Figure 1-3 McAfee DLP in ePolicy Orchestrator
McAfee Data Loss Prevention 9.2.0 Installation Guide 9
1
Introduction to McAfee Total Protection for DLP 9.2.0
Installation scenarios
Installation scenarios
McAfee Data Loss Prevention software can be installed on Linux appliances or as an ePolicy
Orchestrator application on a Windows server operating system.
McAfee Data Loss Prevention software comes in both Linux and Microsoft Windows versions. The Linux
version can be run as a virtual appliance.
Virtual appliance installation is documented in McAfee Data Loss Prevention 9.2 Virtual Appliance
Installation Guide.
Linux operating systems
These appliance models running the Linux operating system support McAfee DLP 9.2 software:
• Model 4400
• Model 1650
• Model 3650
McAfee DLP Discover, McAfee DLP Monitor, and McAfee DLP Prevent are typically installed on separate
appliances that are managed from McAfee DLP Manager. If McAfee DLP Endpoint is installed as part of
the network product suite, it is first installed on ePolicy Orchestrator on a Windows server operating
system. Integration of these components is discussed in chapter 7, Integrating McAfee DLP Endpoint
into a unified policy system.
Windows Server operating systems
These Windows Server operating systems support McAfee DLP 9.2.0 software installed on McAfee
ePolicy Orchestrator (McAfee ePO) versions 4.5 and 4.6.
• Windows Server 2008
• Windows Server 2003
For complete system requirements, see chapter 6, Installing McAfee DLP Endpoint.
See also
Verify system requirements on page 43
10 McAfee Data Loss Prevention 9.2.0 Installation Guide
2 Setting up the hardware
This Quick Start serves as a high-level road map for setting up your McAfee DLP system. McAfee DLP
Manager is shipped pre-installed; the other products in the suite (McAfee DLP Monitor, McAfee DLP
Discover, and McAfee DLP Prevent) must be installed on-site.
McAfee DLP Monitor must be set up to capture network traffic, so it requires additional configuration
steps.
Contents
Adding devices and servers
Check the shipment
Plan your installation
Rack mount the appliances
Connect a management console
Configure McAfee DLP Manager
Select an integration mode for McAfee DLP Monitor
Complete the setup
Adding devices and servers
The final setup for McAfee Total Protection for Data Loss Prevention depends on your protection
strategy. After you complete setup of all of the appliances, go to the System tab on McAfee DLP
Manager to add the products to be managed and the servers needed to complete the system.
For example, depending on your objectives, you might add McAfee DLP Discover or McAfee DLP
Prevent, which require additional configuration.
If you add McAfee DLP Endpoint to the network product suite, you must install it on McAfee® ePolicy
Orchestrator®, and add endpoint, evidence, and directory servers.
Check the shipment
Each product ships with all of the material needed to install it on a network. Check each shipment to
verify that all items on the packing list have been received.
Task
1 Refer to your Accessory Kit Content List to ensure that you received the following items:
• Region-specific power cords - 2
• CAT5 cables - 3
• Serial cable: RJ-45 to RS-232 - Cisco console cable
McAfee Data Loss Prevention 9.2.0 Installation Guide 11
2
Setting up the hardware
Plan your installation
• Intel Diagnostic Tool (IDT) USB
• Product notes for IDT (CD media)
• Safety document
• Warranty document
• Recovery media
2 If an item is missing or damaged, contact your supplier.
Plan your installation
Before installing, survey your environment and collect configuration information.
For the McAfee DLP Monitor appliance, you will also need a network tap (unless you are planning a
SPAN port configuration).
Task
1 Collect the following information about the network in which McAfee Total Protection for DLP will be
installed.
• Host name • Secondary DNS server
• IP address • Domain
• Subnet mask • NTP server
• Default gateway • Syslog server
• DNS domain • Email relay server
• Primary DNS server
2 Devise a protection strategy by evaluating the type of information you need to protect. Your
objectives will determine which policies you activate.
3 Determine who will be the primary administrator of the system.
Rack mount the appliances
Each of the McAfee DLP products is shipped on an Intel® Server System SR2612UR.
For rack mounting instructions, download the Intel® Server System SR2612UR Service Guide from the
Intel download site.
http://download.intel.com/support/motherboards/server/s5520ur/sb/r2612ur_service_guide_14.pdf
For more information, download the Intel® Server System SR2612UR Technical Product Specification.
http://download.intel.com/support/motherboards/server/s5520ur/sb/sr2612ur_tps_13.pdf
12 McAfee Data Loss Prevention 9.2.0 Installation Guide
2
Setting up the hardware
Connect a management console
Connect a management console
Connect a laptop to the management port of the McAfee DLP appliance so you can reconfigure it
through a directly connected device. Because McAfee DLP Manager requires additional steps,
reconfigure all other products first.
Before you begin
You will need the list of network parameters you prepared when you planned your installation.
Figure 2-1 Model 1650 appliance port configuration
1 Ethernet port 0
2 Ethernet port 1 — Management port
3 Ethernet port 2 — Capture port 0
4 Ethernet port 3 — Capture port 1
Figure 2-2 Model 3650 appliance port configuration
1 Ethernet port 0
2 Ethernet port 1 — Management port
3 Ethernet port 2 — Capture port 0
4 Ethernet port 3 — Capture port 1
Figure 2-3 Model 4400 appliance port configuration
1 Ethernet port 0
2 Ethernet port 1 — Management port
3 Ethernet port 3 — Capture port 1 — note reversed configuration
4 Ethernet port 2 — Capture port 0 — note reversed configuration
By default, each appliance is configured with the IP address 192.168.1.2, but a new IP address and
other network parameters are required to integrate it into the network.
McAfee Data Loss Prevention 9.2.0 Installation Guide 13
2
Setting up the hardware
Configure McAfee DLP Manager
You must connect a laptop to the management port so you can convey this information to the
appliance. Assign the laptop an IP address that is different, but on the same subnet, so it can access
the management port.
Task
1 Connect a laptop to the management port of the appliance using the supplied Ethernet cable.
2 Change the laptop to an address in the 192.168.1.X/24 IP range — for example, 192.168.1.10.
3 Open a web browser and connect to the DLP appliance.
https://192.168.1.2
The DLP user interface starts.
4 Log on to the McAfee DLP appliance.
The default logon is admin/mcafee.
The End User License Agreement appears.
5 Select the license agreement checkbox and click I Accept.
The Setup Wizard starts.
6 On the Network Configuration page, enter all of the IP addresses, and the host and domain names
needed to integrate the appliance into the network.
If you are configuring a McAfee DLP Manager, skip to the next topic.
7 Advance through the Setup Wizard pages to the Review page.
The interim pages will be completed only on the McAfee DLP Manager appliance.
8 Click Submit, then Exit Wizard.
When this step is complete, the appliance will have a new IP address and will be integrated into the
network. Restarting is not necessary.
If you have configured McAfee DLP Discover or McAfee DLP Prevent appliances, setup is complete. If
you are configuring McAfee DLP Manager, proceed to the next step. If you are configuring McAfee DLP
Monitor, proceed to the following step.
Configure McAfee DLP Manager
When you configure McAfee DLP Manager, you must provide additional information after the network
configuration is completed.
Before you begin
You must have completed the network settings required on the Network Configuration page of
the Setup Wizard.
14 McAfee Data Loss Prevention 9.2.0 Installation Guide
2
Setting up the hardware
Configure McAfee DLP Manager
Task
1 On the Time Configuration page, change the time zone.
2 Select Manual to set NTP to local time.
On this first configuration, you will not yet be able to set the NTP server because the default IP
address (192.168.1.2) will not allow it to be located. The NTP server can be defined only when the
system is restarted and integrated into the network.
3 On the Policy Activation page, select the checkboxes of the policies that will generate incidents that
are relevant to your protection strategy.
If you are in a region that is not listed, you will be able to activate policies that are directly relevant
to your location after the system is installed.
4 On the Administrator Setup page, enter the email address of the primary administrator and change the
password from the default.
5 On the Email and Email Server Setting page, enter the IP address or host name of the email server.
6 On the Review page, verify your settings, click Cancel, or click Previous to change them.
7 When you have confirmed your settings, click Submit, then Exit Wizard.
At this point, the McAfee DLP Manager setup is almost complete. After all other products are
integrated into the network, sync McAfee DLP Manager to the network by completing the final step
in this document.
McAfee Data Loss Prevention 9.2.0 Installation Guide 15
2
Setting up the hardware
Select an integration mode for McAfee DLP Monitor
Select an integration mode for McAfee DLP Monitor
McAfee DLP Monitor must be physically integrated into the network so it can capture traffic. There are
two integration modes: use of a mirror (SPAN) port on a LAN switch, or placement of a network tap
between the network and the appliance.
SPAN port configuration
A SPAN (Switched Port Analyzer) port configuration enables monitoring by transparently copying traffic
from source ports to the destination port to which McAfee DLP Monitor is connected.
If two capture ports are used, two traffic sources (for example, different subnets) must be used.
Certain switch models permit the use of a “remote SPAN”, or “RSPAN” capability, which allows ports
from multiple switches to be mirrored to the port to which McAfee DLP Monitor is connected. If you
want to mirror multiple ports on multiple switches to your DLP appliance, contact the switch vendor for
details on configuring RSPAN.
Figure 2-4 Span port configuration
1 Capture ports
2 WAN router traffic mirrored to McAfee DLP Monitor port
3 LAN
4 LAN switch
5 WAN
This method requires a change on the LAN switch, but no downtime is required because network
traffic is not disrupted.
With this configuration, some packets might be dropped under heavy loads. As a result, the number of
packets seen by McAfee DLP Monitor might not match the number seen by the ports being monitored.
Integrate the appliance using a SPAN port
Task
1 Connect McAfee DLP Monitor to a network switch using a console cable or network connection
(such as Telnet or SSH).
Note the port used to connect the appliance to the LAN switch, and the port used by the WAN router.
2 Apply the appropriate SPAN port configuration.
16 McAfee Data Loss Prevention 9.2.0 Installation Guide
2
Setting up the hardware
Select an integration mode for McAfee DLP Monitor
3 Using interface show commands on the switch, verify that traffic is being received on the switch
port to which McAfee DLP Monitor is connected.
4 Save the configuration on the switch.
Common configuration
If a SPAN port is configured on a Cisco switch, the WAN router would be connected to
interface "GigabitEthernet1/0/1". The DLP appliance would be connected to interface
"GigabitEthernet1/0/2".
Switch: configure terminal
Switch(config)# interface GigabitEthernet1/0/2
Switch(config-if)# port monitor GigabitEthernet1/0/1
Switch(config-if)# end
Switch# show port monitor
Monitor Port Port being monitored
--------------------- -------------------------
GigabitEthernet1/0/2 GigabitEthernet1/0/1
Switch# write memory
Network tap configuration
A network tap configuration enables monitoring by injecting a tap in between two network devices
(generally the LAN switch and the WAN router) using additional cabling, then connecting the tap to
McAfee DLP Monitor.
The network tap captures traffic through a tap that is attached to the LAN switch and WAN router
through two network ports. Traffic from these ports flows directly to the capture ports on McAfee DLP
Monitor.
In environments where there is a firewall or a series of devices separating the LAN switch from the WAN
router, the network tap should be installed between the LAN switch and the first device.
Figure 2-5 Network tap configuration
1 Capture ports
2 Analyzer ports
3 Network tap
4 LAN
5 LAN switch
6 Router
7 WAN
McAfee Data Loss Prevention 9.2.0 Installation Guide 17
2
Setting up the hardware
Complete the setup
This method requires physical disconnection and reconnection of network cables, so it disrupts traffic.
A service window is required.
With this configuration, full traffic capture is done even under heavy load conditions.
Network tap types
Network taps are available in copper or fiber media.
Regeneration taps for both types can be used to extend monitoring to multiple ports. When these taps
are used, signals are regenerated before sending a copy of the packets to the monitor port.
Table 2-1 Network tap types
Network tap type Description
Copper and copper These taps use twisted pair copper cabling (preferably CAT6 twisted
regenerative pair).
Fiber and fiber regenerative These taps use multimode fiber cabling with an LC connector on one
end (which connects to a capture port on the appliance) and an SC
connector on the other (which connects to a port on the tap).
Integrate the appliance using a network tap
Task
1 Disconnect the cable between your WAN router and your LAN switch.
2 Connect Monitor Port A of the network tap to Capture Port 0 on McAfee DLP Monitor.
3 Connect Monitor Port B of the network tap to Capture Port 1 on McAfee DLP Monitor.
4 Connect Network Port A of the network tap to a router inside the firewall.
5 Connect Network Port B of the network tap to the LAN switch.
Complete the setup
Add the NTP server to sync McAfee DLP Manager to the network.
Task
1 Open a web browser and enter the assigned IP address in the address bar to restart McAfee DLP
Manager.
2 Click the System tab and select the Configure link.
3 Scroll down to the Time section and enter the NTP server.
pool.ntp.org
4 Click Time at Server to verify the current time.
5 Click Update.
Configuration is complete. If you want to integrate the DLP system into McAfee® ePolicy Orchestrator®
4.5 or 4.6, you can do it now.
18 McAfee Data Loss Prevention 9.2.0 Installation Guide
3 Installing or upgrading the software on
Model 4400
A McAfee DLP installation on the Model 4400 contains two released images, each of which contains an
operating system (except for the kernal) and DLP software.
Primary and secondary images are initially duplicate installations. When the system is upgraded, the
primary and secondary disks can contain different versions of the same product.
The system automatically boots from the latest installed version.
Contents
Download and expand the archive
Boot options
Upgrade the products
Apply a hotfix
Convert an installation to another DLP product
Restoring the drives
Download and expand the archive
To prepare for installation, download the software from the Service Portal and copy it to the appliance.
When the compressed tar file is expanded, the installation scripts become available.
Before you begin
Locate the grant number you received after purchasing the product.
McAfee DLP Manager is pre-installed on the model 4400 appliance. Install the other McAfee DLP
products as needed.
Downloadable archives all have legacy names preceded by "i", although the product names have
changed. In particular, note that McAfee DLP Monitor is also known as "iguard".
Task
1 Open the McAfee Service Portal by typing support.mcafee.com into the address bar of a web browser.
2 From the Products & Solutions menu, select Product Downloads, or locate and click the link under the
Corporate Support heading.
3 In the Download My Products field, enter your grant number.
4 Scroll down the page, then select the McAfee Network DLP product and version.
McAfee Data Loss Prevention 9.2.0 Installation Guide 19
3
Installing or upgrading the software on Model 4400
Boot options
5 Select and save the appropriate *.tgz file to your desktop.
6 Log on as root to the model 4400 appliance and create a product directory under data.
The directory name you select should identify the product to be installed — for example,
imanager, imonitor (iguard), idiscover, iprevent.
7 Copy the archive into the data directory.
Use WinSCP to copy from Microsoft Windows to Linux.
8 Extract the contents of the archive, using the -C option to expand it into the product directory.
[root@4400 data]# tar zxf <product>.tgz -C <product>.
Boot options
Unlike the legacy DLP appliances, the model 4400 hardware platform runs the McAfee Linux Operating
System. It contains a boot loader package that allows users to switch between installations.
McAfee DLP uses Gnu GRUB (GRand Unified Bootloader) to install the primary and secondary images
on the model 4400 appliances.
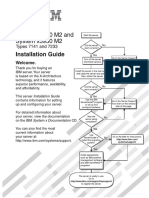
Figure 3-1 GRand Unified Bootloader
The default Disk Boot option is used only to boot the operating system of the appliance.
During the upgrade process, the configuration data in the /data directory and the kernel/boot loader
information in the boot directory are copied over to the new installation.
20 McAfee Data Loss Prevention 9.2.0 Installation Guide
3
Installing or upgrading the software on Model 4400
Boot options
Table 3-1 Boot options
Option Definition
McAfee NDLP Disk Boot Reboots the system from the operating system disk. Does not reinstall the
operating system or the product software.
McAfee NDLP Primary Image Loads the primary image to the system. Replaces the existing operating
Install system and product software, but retains the data in the /data and /boot
directories.
McAfee NDLP Secondary Image Loads the secondary image to the system. Replaces the existing operating
Install system and product software, but retains the data in the /data and /boot
directories.
Load the primary image
You can install the image on both primary and secondary disks with the install_new_full script, or
you can install only a primary image with the install_new_pri script.
Before you begin
Download the product archive, copy it to the appliance, and expand it into a product
directory under /data.
McAfee recommends installing duplicate images on both primary and secondary disks.
Task
1 Log on to the appliance as root.
2 Go to the product installation directory under the /data directory.
# cd /data/<product>
3 Run the installation script with the product name and the path to the product directory.
# ./install_new_pri iguard /data/monitor
When the installation is complete, a message appears stating which image will boot next.
4 Restart the system.
Load the secondary image
You can install the image on both primary and secondary disks with the install_new_full script, or
you can install only a secondary image with the install_new_sec script.
Before you begin
Download the product archive, copy it to the appliance, and expand it into a product
directory under /data.
McAfee recommends installing duplicate images on both primary and secondary disks.
Task
1 Log on to the appliance as root.
2 Go to the product installation directory under the /data directory.
# cd /data/<product>
McAfee Data Loss Prevention 9.2.0 Installation Guide 21
3
Installing or upgrading the software on Model 4400
Boot options
3 Run the installation script with the product name and the path to the product directory.
# ./install_new_sec iguard /data/monitor
When the installation is complete, a message appears stating which image will boot next.
4 Restart the system.
Install a fresh image
If a fresh image is needed, you can install a fresh image on the primary or secondary disk.
Before you begin
Download the product archive, copy it to the appliance, and expand it into a product
directory under /data.
Task
1 Log on to the appliance as root.
2 Run the system_info utility to determine which versions are installed, so that you can decide
where to install the fresh image.
# /data/stingray/ksh/system_info
3 Go to the product installation directory under the /data directory.
# cd /data/<product>
4 Run the primary or secondary installation script with the product name and the path to the product
directory.
# ./install_new_pri iguard /data/monitor
or
# ./install_new_sec iguard /data/monitor
The product image installs on the specified disk. When the installation is complete, a message
appears stating which image will boot next.
5 Reboot the system.
Set up the next boot option
After you install an image, the system automatically assigns the next boot to the image that was
installed. In rare instances, you might want to override that assignment by configuring the next boot
to a different disk.
Using this command has the same effect as changing the boot option using the Grub menu.
Take this step only if you have a specific need that cannot be addressed by the current configuration.
Task
1 Log on to the appliance as root.
2 Go to the product installation directory under the /data directory.
# cd /data/<product>
22 McAfee Data Loss Prevention 9.2.0 Installation Guide
3
Installing or upgrading the software on Model 4400
Upgrade the products
3 Run the setnextboot script to select one of three boot options: primary, secondary, or boot from
the operating system on the appliance.
# ./setnextboot [reboot_only | pri | sec]
The script sets up the selected option. When the option is set, a message appears stating which
image will boot next.
4 Restart the system.
Upgrade the products
Upgrade the products by installing new images on the primary or secondary disk, depending on which
was upgraded last. The system automatically boots from the latest image.
Before you begin
Download the product archive, copy it to the appliance, and expand it into a product
directory under /data.
The install_to_pri and install_to_sec scripts install the upgrade. After the process runs, the
existing configuration and database are copied to the new image.
Task
1 Log on to the appliance as root.
2 Check the current version.
# cat /data/stingray/etc/version
3 Run the system_info utility to determine which versions are installed and where they are located.
# /data/stingray/ksh/system_info
4 Run the appropriate installation script.
# install_to_pri iguard /data/monitor
or
# install_to_sec iguard /data/monitor
When the upgrade is complete, a message appears stating which image will boot next.
5 Reboot the system.
Apply a hotfix
Apply a hotfix by running a script that installs the hotfix RPM.
Before you begin
You need not check the version or product before installing the hotfix. The RPM ensures
that the package is being installed on the right platform, product, and version.
The hotfix script copies the Hotfix RPM to data/hotfix/<current version> and adds an installation
entry to /data/hotfix/<current_version>/install_hotfix<stingray_version>.sh.
In rare instances, a kernel RPM might be released. If this occurs, installation of the release image
automatically updates the boot loader for the corresponding kernel version.
McAfee Data Loss Prevention 9.2.0 Installation Guide 23
3
Installing or upgrading the software on Model 4400
Convert an installation to another DLP product
Task
1 Log on to the appliance as root.
2 Run the hotfix script with an option that identifies the current hotfix package.
# install_hotfix.ksh <hotfix_rpm>
The name of the package follows a convention — Hotfix-<product name>-<Bugzilla
number>-<Perforce change number>-<version number>-(sequence number>-x86-64.rpm.
For example, a package using this naming convention might be
Hotfix-iguard-750875-55025-9.2.0-01.x86-64.rpm.
3 Reboot the system.
When the system is booted up, the RPM will also install
Convert an installation to another DLP product
The model 4400 appliance ships with McAfee DLP Manager, but that installation can be converted to
another DLP product. However, only one product can be installed on the appliance, so the primary and
secondary images must both be installed with that product.
Before you begin
Download the product archive, copy it to the appliance, and expand it into a product
directory under /data.
Task
1 Log on to the appliance as root.
2 Go to the product installation directory under the /data directory.
# cd /data/<product>
3 Run the installation script with the product name and the path to the product directory.
# ./install_new_full iguard /data/imonitor
The script installs the product on both disks. When the installation is complete, a message appears
stating which image will boot next.
4 Reboot the system.
Restoring the drives
To restore the drives on the model 4400 appliance, insert the DVD that was shipped with your appliance.
The process that runs from the DVD restores the drives of the model 4400 appliance to their
pre-installed state.
24 McAfee Data Loss Prevention 9.2.0 Installation Guide
4 Installing or upgrading software on
model 1650 and 3650 appliances
A McAfee DLP installation on the model 1650 and 3650 appliances contains the software for a single
product. The software is installed or upgraded by running two installation scripts.
The platform script installs the operating system components, and it is customized to the hardware
used by entering a platform type option. A Stingray script installs the McAfee DLP application.
The installation and upgrade procedures for the management console (McAfee DLP Manager) and all of
its managed devices (McAfee DLP Discover, McAfee DLP Monitor, and McAfee DLP Prevent) are the
same. McAfee DLP Endpoint must be installed separately.
Contents
Download and expand the legacy archive
Install the products on legacy servers
Upgrade to 9.2.0 on legacy appliances
Download and expand the legacy archive
To prepare for installation, download the software from the Service Portal and copy it to the appliance.
When the compressed bzip2 file is expanded, the installation scripts become available.
Before you begin
Locate the grant number you received after purchasing the product.
Downloadable archives all have legacy names preceded by "cdrom_ i<product>", although
the product names have changed and they are no longer distributed on media. In
particular, note that McAfee DLP Monitor is also known as "iguard".
Task
1 Open the McAfee Service Portal by typing support.mcafee.com into the address bar of a web browser.
2 From the Products & Solutions menu, select Product Downloads, or locate and click the link under the
Corporate Support heading.
3 In the Download My Products field, enter your grant number.
4 Scroll down the page, then select the McAfee Network DLP product and version.
5 Select and save the appropriate *.bz2 file to your desktop.
McAfee Data Loss Prevention 9.2.0 Installation Guide 25
4
Installing or upgrading software on model 1650 and 3650 appliances
Install the products on legacy servers
6 Log on as root to the model 1650 or 3650 appliance and create a product directory under data.
The directory name you select should identify the product to be installed — for example,
imanager, imonitor (iguard), idiscover, iprevent.
7 Copy the archive into the data directory.
Use WinSCP to copy from Microsoft Windows to Linux.
8 Extract the contents of the archive, using the -C option to expand it into the product directory.
[root@4400 data]# tar jxf <product>.bz2 -C <product>.
Install the products on legacy servers
You can install any of the products on the model 1650 or 3650 appliances. The choice of hardware is
indicated by the platform type option.
Before you begin
Download the product archive, copy it to the appliance, and expand it into a product
directory under /data.
Each of the network DLP products is installed using two different scripts. The platform installation
includes the OS components, and the Stingray package contains the DLP application.
After installing the platform, you might be prompted to restart the system before installing Stingray, but
version 9.2 does not require this restart. You can continue directly to the next step.
Task
1 Log on to the McAfee DLP device as root.
2 Go to the directory containing the product software.
# cd /data/<product>
3 Install the platform.
Enter ./install_platform to display the current platform type, along with other options.
# ./install_platform –P <platform type>
4 Restart the system.
# reboot
Restarting the system might take 10-15 minutes.
5 Install the application.
Enter ./install_platform to display the current platform type, along with other options.
# ./install_stingray –P <platform type>
26 McAfee Data Loss Prevention 9.2.0 Installation Guide
4
Installing or upgrading software on model 1650 and 3650 appliances
Upgrade to 9.2.0 on legacy appliances
6 Restart the system.
# reboot
7 Log on to the McAfee DLP device as root, go to the installation directory, and verify the installation
with the command:
# cat /data/stingray/etc/version
If the Release field contains 9.2.0, installation is complete.
Upgrade to 9.2.0 on legacy appliances
You can upgrade to any of the products on model 1650 or 3650 appliances by upgrading a 9.0.x
systems to 9.0.4 before upgrading to 9.2.0. When that is done, apply any existing hotfixes.
Before you begin
Download the patch and hotfix, then copy them to the /tmp/ directory of the appliance.
Stop all scans and search tasks before upgrading, and wait until they are completely
stopped before proceeding.
If the patch installation fails, do not install it again. Call McAfee support and submit an
installation log file.
Task
1 Log on to the appliance as root.
2 Check the current version.
# cat /data/stingray/etc/version
3 Make a directory for the patch, check its location, then expand the archive into the new directory.
# mkdir -p /data/patch_9.0.4/686712_i<product>
# ls -l /tmp patch_686712_45025_02_i<product>.tar.gz
# tar zxvf /tmp patch_686712_45025_02_i<product>.tar.gz -C /data/patch_9_0_4/686712
_i<product>
4 Go to the patch directory, then find and read the README file.
# cd /data/patch_9_0_4/686712_i<product>
# ls -l
# cat README
Follow the installation steps in the README file.
5 Restart if prompted, or continue to the next step when prompted.
6 Make a directory for the hotfix, check its location, then expand the archive into the new directory.
# mkdir -p /data/hotfix
# ls -l /tmp hotfix_719847_45561_01.tar.gz
# tar zxvf /tmp hotfix_719847_45561_01.tar.gz -C /data/hotfix
Do not install the hotfix until the upgrade to 9.2.0 is complete.
McAfee Data Loss Prevention 9.2.0 Installation Guide 27
4
Installing or upgrading software on model 1650 and 3650 appliances
Upgrade to 9.2.0 on legacy appliances
7 Go to the hotfix directory, run the hotfix installation script, and reboot.
# cd /data/hotfix
# ./install_hotfix
# reboot
8 Start the network DLP service.
# service stingray restart
28 McAfee Data Loss Prevention 9.2.0 Installation Guide
5 Configuring McAfee DLP appliances and
adding servers
All McAfee DLP appliances can be registered to McAfee DLP Manager and managed from that console.
After the appliances are configured, servers that extend the functionality of the system can be added.
At the very least, an NTP server must be added during the installation process.
Most McAfee DLP enterprise configurations have LDAP servers configured, and McAfee® Logon Collector
is often used in addition to resolve the identities of specific users.
After installation of McAfee DLP Monitor, McAfee strongly recommends adding capture filters to
customize the system. Some default filters are provided to filter out extraneous data that would
ordinarily be captured, but each installation has a unique protection strategy that requires different
settings. Consult the McAfee Total Protection for Data Loss Prevention 9.2.0 Product Guide for more
information.
Contents
Configure McAfee DLP appliances using Setup Wizard
Configure McAfee DLP appliances after installation
Add McAfee DLP products to McAfee DLP Manager
Configuring McAfee DLP Prevent
Add LDAP servers to McAfee DLP Manager
Add McAfee Logon Collector to McAfee DLP Manager
Add syslog servers to McAfee DLP systems
Resynchronize McAfee DLP systems with an NTP server
Testing the system
Configure McAfee DLP appliances using Setup Wizard
After installing the appliances, configure them by running the Setup Wizard.
Before you begin
The software for the appliance to be configured must already be installed on the appliance.
After installation is complete, you can start the Setup Wizard from the Configure link on the System page if
you want to make changes.
Task
1 Open a web browser and start the application using the IP address.
# https://xxx.xxx.xxx.xxx
McAfee Data Loss Prevention 9.2.0 Installation Guide 29
5
Configuring McAfee DLP appliances and adding servers
Configure McAfee DLP appliances using Setup Wizard
2 At the logon prompt, type the default user name and password.
admin/mcafee
3 On the End User License Agreement page, select the checkbox and click I Accept.
4 On the Network Configuration page, assign the hostname, domain and IP addresses of the gateway and
DNS servers, then click Next.
Figure 5-1 Network configuration
You must enter a fully-qualified domain name into the Hostname field.
30 McAfee Data Loss Prevention 9.2.0 Installation Guide
5
Configuring McAfee DLP appliances and adding servers
Configure McAfee DLP appliances using Setup Wizard
5 On the Time Configuration page, set the time zone, select the NTP server, and click Next.
Figure 5-2 Time configuration
You might want to set the NTP server manually in some cases.
McAfee Data Loss Prevention 9.2.0 Installation Guide 31
5
Configuring McAfee DLP appliances and adding servers
Configure McAfee DLP appliances using Setup Wizard
6 On the Policy Activation page, select the policies that are needed for you to implement your protection
strategy, then click Next.
Figure 5-3 Policy activation
If you have to change this configuration later, you can activate or deactivate policies from the Policies
page. For example, you might want to use international policies that are available on that page.
32 McAfee Data Loss Prevention 9.2.0 Installation Guide
5
Configuring McAfee DLP appliances and adding servers
Configure McAfee DLP appliances using Setup Wizard
7 On the Administrator Setup page, type in an email address for the primary administrator and set a
password, then click Next.
Figure 5-4 Administrator setup
McAfee Data Loss Prevention 9.2.0 Installation Guide 33
5
Configuring McAfee DLP appliances and adding servers
Configure McAfee DLP appliances using Setup Wizard
If additional configuration is needed after installation, logon to the application after rebooting, then
click the Configure link on the System page.
Figure 5-5 Review
Figure 5-6 Email server setting
8 If you are setting up McAfee DLP Prevent, type in the IP address of a smart host, then click Next.
34 McAfee Data Loss Prevention 9.2.0 Installation Guide
5
Configuring McAfee DLP appliances and adding servers
Configure McAfee DLP appliances after installation
9 On the Review page, review your settings, then click Submit.
10 If the settings are correct, click OK to restart the appliance.
If additional configuration is needed after installation, log on to the application after restarting,
then click the Configure link on the System page.
Configure McAfee DLP appliances after installation
After installing the appliances, you can change their configuration by clicking its Configure link and
making changes on the System Configuration page of the device.
The Devices page is refreshed automatically every two minutes to reflect the new status of the devices
and statistics.
Task
1 In ePolicy Orchestrator, select Menu | Data Loss Prevention | DLP Sys Config | System Administration | Devices.
2 On your Linux-based appliance, select System | System Administration | Devices.
3 Select a device and click Configure.
4 Change parameters on the System Configuration page.
5 Click Update after each change is made.
Add McAfee DLP products to McAfee DLP Manager
Add McAfee DLP products to McAfee DLP systems by configuring McAfee DLP Manager to open an SSH
tunnel between the devices.
Before you begin
If you are going to install the network product suite on ePolicy Orchestrator, you must add
the netdlp.zip extension before adding any of the other products. See chapter 7,
Integrating McAfee DLP Endpoint into a unified policy system for details.
You cannot add McAfee DLP Endpoint to McAfee DLP using this procedure. It must be integrated into the
network product suite after it is installed on ePolicy Orchestrator.
Adding a McAfee DLP appliance wipes the current configuration of that machine, but captured data,
cases, and incidents will not be lost. Unless you have previously deployed policies to All Devices, you will
have to edit them to add the device.
If a device is registered with McAfee DLP Manager, the device cannot be brought back to standalone
mode after deregistering it, and it will have to be reinstalled.
On some networks you can choose a port configuration. The McAfee DLP appliance is a Gigabit network
device, so it is possible to bring it down.
McAfee Data Loss Prevention 9.2.0 Installation Guide 35
5
Configuring McAfee DLP appliances and adding servers
Configuring McAfee DLP Prevent
The Add Device page is also used to add an ePolicy Orchestrator server (ePolicy Orchestrator GUI IP
Address) and database (ePolicy Orchestrator Database IP or hostname). If the ePolicy Orchestrator
device checkbox is selected, the options change.
If Incident Copy Only is selected from the Type menu, there is no integration with unified policy, and you
must use the McAfee DLP Endpoint Policy Manager to update the policy.
Task
1 In ePolicy Orchestrator, select Menu | Data Loss Prevention | DLP Sys Config | System Administration | Devices.
2 On your Linux-based appliance, select System | System Administration | Devices.
3 Select Actions | New Device.
4 Enter the Device IP or hostname and Password.
Use the root user account for association. McAfee recommends that you change the root password
on the appliance before adding it to McAfee DLP Manager. If you change the IP address, the
network service needs to be restarted. Stingray automatically restarts the appliance to register the
change.
5 Click Add.
6 Click OK to confirm or Cancel the registration.
7 Wait for the Status icon in the device list to turn green.
The CPU usage display indicates that the registration tasks being performed. McAfee DLP Manager
does not display any CPU activity, because it serves only as a collection point for the data. Other
machines are capturing and indexing data and the processor indicates the CPU utilization. It should
not go over 70—80%.
If registration seems to be taking a long time, try refreshing the page.
When devices are added successfully, their status icons will turn green.
Configuring McAfee DLP Prevent
If McAfee DLP Prevent is being configured for email, you must identify a smart host and an email
address for testing the connection. If it is configured for webmail, a proxy server can be used, but only
the ALLOW and BLOCK actions will be available.
When configured with an email gateway, McAfee DLP Prevent monitors transmissions and applies
preventive actions to sensitive data found in network communications.
When configured with a web proxy server, McAfee DLP Prevent monitors transmissions and identifies
data in wikis, portals, blogs and other collaborative sites using HTTP and HTTPS protocols.
Both MTA and proxy servers can be handled by one McAfee DLP Prevent system, but contact a McAfee
Customer Service representative to assure proper performance.
If you need more information about how McAfee DLP Prevent works with SMTP and ICAP traffic, consult
the McAfee Total Protection for Data Loss Prevention 9.2.0 Product Guide.
36 McAfee Data Loss Prevention 9.2.0 Installation Guide
5
Configuring McAfee DLP appliances and adding servers
Configuring McAfee DLP Prevent
McAfee DLP Prevent can be configured with many different email and webmail systems. McAfee Email
and Web Gateway products are supported, and it has also been tested with some third party systems,
such as Blue Coat Systems products.
McAfee Email Security Appliance is set to handle up to 30 concurrent SMTP connections - but McAfee DLP
Prevent exceeds this limit. To get these two appliances to work together, you must modify the ESA
configuration files.
MTA requirements for McAfee DLP Prevent
Before setting up McAfee DLP Prevent, you must determine if your MTA (message transfer agent) can
support interoperability.
Before installing McAfee DLP Prevent, make sure that your email gateway has all of the following
capabilities.
• By incoming and outgoing, we mean emails that are either being sent to or received from
the outside world.
• By entering and leaving, we mean emails that are entering or leaving the MTA.
1 Must be capable of sending either all or a portion of outgoing traffic to the McAfee DLP Prevent
application. McAfee DLP Prevent is not typically used to inspect incoming email. Examples of a
requirement where only a portion of the traffic needs to be scanned might be in environments
where only traffic with attachments is to be scanned, or where scanning is limited to traffic directed
to public sites (for example, Yahoo).
2 Must be capable of inspecting email headers of messages entering the MTA.
3 Must be capable of taking actions based on specified match expressions for email headers. The
specific header strings received from McAfee DLP Prevent are the X header X-RCIS-Action header
with values ALLOW, BLOCK, QUART, ENCRYPT, BOUNCE, REDIR and NOTIFY.
4 Based on entering port or some other metric, must be capable of distinguishing between all emails
arriving from the McAfee DLP Prevent appliance, then applying header inspection and header-based
action rules exclusively to incoming email from McAfee DLP Prevent.
5 Must be capable of ensuring that emails arriving from the McAfee DLP Prevent appliance are not
routed back to the McAfee DLP Prevent appliance. This can be done either by using port /
srcIP-based mail routing, checking to see if an X-RCIS-Action header already exists in an email
scheduled to be routed to the McAfee DLP Prevent appliance, or by some other means.
6 Must be capable of implementing all of the McAfee DLP Prevent-based actions. If the MTA does not
have all of the required capabilities, inter-operation is still possible — but in that case, the actions
that can be set when rules are created must be limited to those supported by the MTA.
7 Must be able to inter-operate with an email encryption appliance (if this capability is needed) and
instruct the encryption appliance to encrypt specific messages based on header information or
other metrics.
Configure McAfee DLP Prevent
Unless McAfee DLP Prevent is used with a proxy server, you must identify a smart host. You must also
provide an email address for testing the connection to the smart host.
Before you begin
Unless McAfee DLP Prevent is deployed as a standalone unit, make sure it is registered to
McAfee DLP Manager before it is configured.
McAfee Data Loss Prevention 9.2.0 Installation Guide 37
5
Configuring McAfee DLP appliances and adding servers
Add LDAP servers to McAfee DLP Manager
Task
1 In ePolicy Orchestrator, select Menu | Data Loss Prevention | DLP Sys Config | System Administration | Devices.
2 On your Linux-based appliance, select System | System Administration | Devices.
3 Select the McAfee DLP Prevent appliance and click its Configure link.
4 On the System Configuration page, scroll down to Email and Email Server Setting.
5 Type in the IP address of the smart host and your email address.
Host names are not supported. A smart host is configured only if SMTP email is being processed,
and configuring more than one is not supported.
6 Click Send test mail and Update.
When you receive the test mail, you will know that the smart host is set up correctly.
Add LDAP servers to McAfee DLP Manager
You can add Active Directory or OpenLDAP servers to support integration of McAfee DLP with existing
user systems.
Before you begin
Determine what type of directory server to add. More than one can be added to McAfee
DLP Manager, but they must be of the same type. For example, if you add Active Directory
servers, you cannot add OpenLDAP servers.
Task
1 In ePolicy Orchestrator, select Menu | Data Loss Prevention | DLP Sys Config | System Administration | Directory
Services.
2 On your Linux-based appliance, select System | System Administration | Directory Services.
3 Select Actions | Create Directory Server.
4 Enter a label to identify the LDAP server.
38 McAfee Data Loss Prevention 9.2.0 Installation Guide
5
Configuring McAfee DLP appliances and adding servers
Add LDAP servers to McAfee DLP Manager
5 Do one of the following:
• Enter the Domain of the LDAP server.
If you use this option, you must log on to an administrative account on the LDAP server. The
system will then query the Domain Name Server to find the domain controller for the Active
Directory domain.
Figure 5-7 Add LDAP server
• In the Authorization Server field, enter the name or IP address of the server.
If you are using SSL (Secure Sockets Layer) to encrypt the connection, you must enter the
FQDN (fully qualified domain name) cited in the uploaded certificate.
Unlike the LDAP server domain name, you can use any valid account that has permission to
read from the LDAP server (an administrative account is not necessary). If you have already
entered the domain name of the LDAP server, any information you enter here will be ignored.
6 Type in the Server Port to be used for the connection.
7 In the Timeout and Retries fields, set intervals for connection (in seconds).
8 Type in the Loginid Attribute.
Use samaccountname to retrieve user names from the server.
9 Type in the user name (Login DN) and Password.
McAfee Data Loss Prevention 9.2.0 Installation Guide 39
5
Configuring McAfee DLP appliances and adding servers
Add McAfee Logon Collector to McAfee DLP Manager
10 Identify the local domain components in the Base DN field (for example, dc=mydomain,dc=com).
Use an administrative account whose password does not expire to maintain the connection, but a
non-administrative account name is acceptable when using an authorization server.
11 Enter the number of records you want to retrieve at one time in the Server Results limit field.
Before entering a value higher than 10, consult the administrator of the Active Directory server to
find out how many records can be served per request.
12 Select the SSL checkbox to encrypt the connection and enable LDAPS (LDAP over SSL).
A secure connection is not required, but is strongly recommended. Accept any available certificate,
or select one by uploading it. If you upload, you must find the FQDN name of the authorization
server in the encrypted file by logging on to the back end of the McAfee DLP appliance and running
the following.
# openssl x509 -noout -in <filename>.cer -subject
The FQDN will be returned in reverse order:
subject= /DC=net/DC=reconnex/CN=tyche
Read from left to right to get the name of the authorization server:
tyche.reconnex.net
Enter the name into the Authorization Server field.
13 Select a Scope to set the directory depth to be accessed on the server.
14 Click Apply.
Add McAfee Logon Collector to McAfee DLP Manager
Connect McAfee Logon Collector to McAfee DLP Manager by using certificates to authenticate them to
each other. When the process is concluded, an SSL connection is established between the servers.
Task
1 Open a web browser, type the IP address of the McAfee Logon Collector into the address bar, and
log on.
2 Go to Menu | Configuration | Server Settings | Identity Replication Certificate.
3 Select and copy all text in the Base 64 field and paste it into a text editor.
4 Add the following beginning and ending lines to the document, then paste in the Base 64 text.
-----BEGIN CERTIFICATE-----
<pasted Base 64 field text>
-----END CERTIFICATE-----
5 Highlight and copy the entire text, including the BEGIN and END CERTIFICATE lines.
6 Open a web browser and log on to the Network McAfee DLP Manager.
7 In ePolicy Orchestrator, select Menu | Data Loss Prevention | DLP Sys Config | System Administration | Directory
Services.
8 On your Linux-based appliance, select System | System Administration | Directory Services.
40 McAfee Data Loss Prevention 9.2.0 Installation Guide
5
Configuring McAfee DLP appliances and adding servers
Add syslog servers to McAfee DLP systems
9 Select Actions | Create McAfee Logon Collector.
10 Enter the IP address of the McAfee Logon Collector into the Export NetDLP Certificate field.
11 Select the Paste from Clipboard option and paste the Base 64 text into the box.
Alternatively, you can export the certificate from McAfee Logon Collector to your desktop, then
Browse to it from the Import MLC Certificate | From File field.
12 Click Apply.
This authenticates the McAfee Logon Collector to McAfee DLP Manager.
13 Click the Export link to save the NetDLP certificate to your desktop.
The file name is netdlp_certificate.cer.
14 Open a web browser, enter the IP address of the McAfee Logon Collector in the address bar, and log
on.
15 Select Menu | Configuration | Trusted CA.
16 Click New Authority.
17 Browse to the netdlp_certificate.cer file you saved to your desktop.
18 Click Open, then click Save.
This authenticates the DLP Manager to McAfee Logon Collector.
19 Open a Remote Desktop session on the McAfee Logon Collector server and restart it.
When the server comes up, the SSL connection between the servers is complete.
Add syslog servers to McAfee DLP systems
You can add syslog servers to McAfee DLP systems just by having them on the network. They are
automatically recognized if they reside on the same network as DLP devices.
You can use syslog servers to collect information about the McAfee DLP system. If a syslog server is
installed on the network, DLP automatically sends messages about significant events.
Resynchronize McAfee DLP systems with an NTP server
An NTP server is required to synchronize the connections between McAfee DLP appliances, servers,
and the network, but you only have to identify a time server during the initial installation of the system.
Stop and restart the NTP daemon to manually reset the time and resyncronize the system.
McAfee Data Loss Prevention 9.2.0 Installation Guide 41
5
Configuring McAfee DLP appliances and adding servers
Testing the system
Task
1 Log on as root to the McAfee DLP appliance.
2 Stop the NTP daemon.
# service ntpd stop
# chkconfig --level 2345 ntpd off
3 Restart the NTP daemon.
# service ntpd start
# chkconfig --level 2345 ntpd on
The service command will control the service while the system is running; the chkconfig
commands will control what happens at boot time.
Testing the system
If your system doesn't appear to be generating incidents after it is installed, you can take steps to
ensure that it is configured correctly.
Table 5-1 Configuration checklist
Checks Explanation Action
Are appliance Status icons display health of each On the System page, check to see if the
connections managed appliance. Status icon is green. If status is Registering
complete? or Unknown, wait until the process is
complete (you might want to refresh the
page). Critical systems must be reinstalled.
Are policies If policies are not activated during On the Policies page, check the State
activated? the setup phase, their rules cannot column. If policies are inactive, select
be matched to network data. policy boxes, then select Activate from the
Actions menu.
Is the timestamp The default is Previous 24 hours to keep On the Incidents page, set Filter by to a
filter set? the system from producing longer time period. If the system was
unmanageable numbers of results. recently installed, it will need some lead
time for data capture and analysis.
Are capture filters The system might have been set up On the System | Capture Filters page, remove
set? to block traffic that is needed to meet filters that might be blocking traffic.
your protection strategy. For
example, the RFC 1918 filter blocks
internal IP addresses.
Are common If data is being captured, you will be On the Basic Search page, type in a
keywords able to find keywords that are common keyword that can be found in
producing results? commonly found in your network captured data.
traffic — for example, your company
name.
Does changing the Data-in-Motion, Data-at-Rest, and Data-in-Use On the System page, check to see if the
dashboard view dashboards display results in network corresponding products are installed.
display different traffic, repositories and endpoints.
results?
Are existing filters When filters are set, only the On the Incidents page, click Clear All in the
blocking significant configured results are visible on the Filter by frame.
results? dashboard.
42 McAfee Data Loss Prevention 9.2.0 Installation Guide
6 Installing McAfee DLP Endpoint
Configure the McAfee ePO server before installing McAfee DLP Endpoint. After installation, several
steps are required to complete the installation.
Contents
Verify system requirements
Configure the server
Install McAfee ePolicy Orchestrator
Install McAfee ePolicy Orchestrator
Installing McAfee DLP WCF service
Repository folders
User and permission sets
Install the McAfee Data Loss Prevention Endpoint extension
Initialize the DLP Policy console
Upgrade the license
Check in the McAfee DLP Endpoint package to ePolicy Orchestrator
Deploying McAfee DLP Endpoint
Uninstalling McAfee DLP Endpoint
Verify system requirements
The following hardware is recommended for running McAfee DLP Endpoint software version 9.2 Patch 2.
Table 6-1 Hardware requirements
Hardware type Specifications
Servers • CPU — Intel Pentium IV 2.8 GHz or higher
• RAM —
• 512 MB minimum for McAfee Device Control software only (1 GB
recommended)
• 1 GB minimum for full McAfee DLP Endpoint software (2 GB recommended)
• Hard Disk: 80 GB minimum
Managed • CPU — Pentium III 1 GHz or higher
workstations
• RAM —
• 256 MB minimum for McAfee Device Control software (1 GB recommended)
• 512 MB minimum for full McAfee DLP Endpoint software (1 GB
recommended)
• Hard Disk — 200 MB minimum free disk space
Network 100 Mbit LAN serving all workstations and the McAfee ePO server
McAfee Data Loss Prevention 9.2.0 Installation Guide 43
6
Installing McAfee DLP Endpoint
Verify system requirements
The following operating system software is supported:
Table 6-2 Operating systems supported
Computer type Software
Servers • Windows 2003 Server Standard (SE) SP1 or later 32- or 64-bit
• Windows 2003 Enterprise (EE) SP1 or later 32- or 64-bit
• Windows 2008 Server Enterprise 32- or 64-bit
Managed • Windows XP Professional SP1 or later • Windows 2003 Server 32- or
workstations 32-bit 64-bit
• Windows Vista SP1 or later 32-bit only • Windows 2008 Server 32-bit
• Windows 7 32- or 64-bit • Windows 2008 Server R2 64-bit
Servers are supported for McAfee Device Control software only.
The user installing McAfee DLP Endpoint software on the servers must be a member of the local
administrators group.
The following software is required on the server running the McAfee DLP Endpoint policy console and
McAfee DLP Monitor:
Table 6-3 Server software requirements
Software Version
McAfee ePolicy Orchestrator • 4.5 Patch 3 or later
• 4.6 and 4.6 Patch 1
McAfee Agent • 4.5 Patch 3 or later
• 4.6
McAfee ePO Help System download the McAfee DLP Endpoint 9.2 Help extension ().
McAfee DLP Windows This is part of the McAfee DLP Endpoint software version 9.2.x
Communication Foundation package, but is installed separately. It should be installed
(DLP WCF) immediately after installing McAfee ePO.
Microsoft .NET 3.5 SP 1 or 4.0
Agent handlers on remote servers no longer require the .NET
Framework.
Microsoft SQL Server 2005 or 2008, Advanced Express or Enterprise, 32- or 64-bit
Microsoft SQL Server Install the version that matches the version of Microsoft SQL Server
Management Studio you are using.
The McAfee DLP Endpoint software version 9.2.x package includes the following:
• McAfee Data Loss Prevention Endpoint (McAfee Agent plugin)
• McAfee DLP Endpoint extension (contains the components installed through ePolicy Orchestrator)
44 McAfee Data Loss Prevention 9.2.0 Installation Guide
6
Installing McAfee DLP Endpoint
Configure the server
Configure the server
Basic configuration of the McAfee ePO server includes setting the security configuration and verifying
the .NET installation.
Verify that the server meets the minimum system requirements.
Task
1 Install Microsoft Windows Server 2003 SP1 or Windows Server 2008. See the System
Requirements for supported Windows systems.
2 Install Windows Installer 3.0 (Windows 2003) or 4.5 (Windows 2008) and restart the system.
Install all Microsoft Windows Service Packs.
3 Run Windows Update and install all updates.
4 Disable Microsoft Internet Explorer’s Enhanced Security Configuration Window Component.
• In Windows 2003, open the Windows Control Panel then select Add/Remove Windows Components.
• In Windows 2008, open the Server Manager then select Configure IE ESC in the Security
Information section.
This Microsoft product can hinder proper installation of McAfee DLP Endpoint components. Disable it
before installation, then reconfigure it after installation if it is required.
5 Verify that Microsoft .NET Framework 3.5 SP1 or 4.0 is installed.
6 Set the server to a static IP address.
We recommend using a subnet separate from your company's production network for initial testing.
If you are setting up a production environment, set the server’s static IP address within that range.
Install McAfee ePolicy Orchestrator
McAfee Data Loss Prevention Endpoint software version 9.2 Patch 2 can be installed in McAfee ePolicy
Orchestrator 4.5 or 4.6. There are a few precautions you should be aware of.
Read the McAfee ePolicy Orchestrator Installation Guide and release notes to familiarize yourself with
all installation issues.
Some of the installation scripts require the NETWORK SERVICE account to have write permission for the
C:\Windows\Temp folder. In secure systems, this folder might be locked down. In that case, you must
temporarily change the permissions for this folder. Otherwise, the installation fails. We recommend
completing all software installations before resetting the permissions.
McAfee Data Loss Prevention 9.2.0 Installation Guide 45
6
Installing McAfee DLP Endpoint
Install McAfee ePolicy Orchestrator
Pay attention to the following points when installing ePolicy Orchestrator:
1 In the McAfee ePO installation wizard, use the following settings.
Installation wizard Setting
screen
Installation Select Install Server and Console
Options
Setup When installing on Windows 2003 Server, we recommend using the SQL
Requirements Server 2005 Express installer included in the McAfee ePO installer.
Another configuration option is to create an ePolicy Orchestrator instance
on an existing SQL Server 2005 or 2008 server and select it. This is the
preferred option when installing on Windows 2008 Server.
After verification that you want to install the software, the SQL installation
continues without user input. If prompted to install SQL Server 2005
Backward Compatibility, you must install it.
Database Server We recommend using a SQL Server account. If preferred, an NT account
Account can also be used.
2 During the installation, you might see a warning about trusted sites. Write down the recommended
additions to the Microsoft Internet Explorer trusted sites list before clicking OK. You will need to add
them later.
Install McAfee ePolicy Orchestrator
McAfee Data Loss Prevention Endpoint software version 9.2 Patch 2 can be installed in McAfee ePolicy
Orchestrator 4.5 or 4.6. There are a few precautions you should be aware of.
Read the McAfee ePolicy Orchestrator Installation Guide and release notes to familiarize yourself with
all installation issues.
Some of the installation scripts require the NETWORK SERVICE account to have write permission for the
C:\Windows\Temp folder. In secure systems, this folder might be locked down. In that case, you must
temporarily change the permissions for this folder. Otherwise, the installation fails. We recommend
completing all software installations before resetting the permissions.
46 McAfee Data Loss Prevention 9.2.0 Installation Guide
6
Installing McAfee DLP Endpoint
Installing McAfee DLP WCF service
Pay attention to the following points when installing ePolicy Orchestrator:
1 In the McAfee ePO installation wizard, use the following settings.
Installation wizard Setting
screen
Installation Select Install Server and Console
Options
Setup When installing on Windows 2003 Server, we recommend using the SQL
Requirements Server 2005 Express installer included in the McAfee ePO installer.
Another configuration option is to create an ePolicy Orchestrator instance
on an existing SQL Server 2005 or 2008 server and select it. This is the
preferred option when installing on Windows 2008 Server.
After verification that you want to install the software, the SQL installation
continues without user input. If prompted to install SQL Server 2005
Backward Compatibility, you must install it.
Database Server We recommend using a SQL Server account. If preferred, an NT account
Account can also be used.
2 During the installation, you might see a warning about trusted sites. Write down the recommended
additions to the Microsoft Internet Explorer trusted sites list before clicking OK. You will need to add
them later.
Installing McAfee DLP WCF service
The McAfee DLP Windows Communication Foundation (WCF) service is used to communicate between
McAfee ePolicy Orchestrator, McAfee Data Loss Prevention Endpoint, and the McAfee DLP Monitor. In
McAfee Total Protection for Data Loss Prevention, it is not used to communicate with ePolicy
Orchestrator or with the McAfee DLP Monitor.
Web access authorized groups
When installing the McAfee DLP WCF service, you are asked to specify the Web Access Authorized Groups
(WAAG). We recommend setting up a group or groups in Windows Active Directory or Open LDAP with
the names of users authorized to log on to the database.
When the McAfee DLP Endpoint policy console attempts to connect to WCF, it impersonates the logged
on user. After the user name is authenticated, WCF checks to see if the user is a member of the WAAG
before connecting to the database.
WCF service installation options
There are two basic options for installing the Windows Communication Foundation (WCF) service: on
the same server as the McAfee ePO (SQL) database (local installation) or on a separate server (remote
installation). Where McAfee ePolicy Orchestrator is installed, together with its database or on a
separate server, is not relevant to this discussion; only the relative locations of WCF and the database.
Option 1: Installing WCF locally
When installing WCF on the same server as the McAfee DLP Endpoint database, you can use Windows
authentication or SQL authentication. The option is selected on the WCF service installation wizard.
The selected authentication applies only to the connection between WCF and the database. The
McAfee Data Loss Prevention 9.2.0 Installation Guide 47
6
Installing McAfee DLP Endpoint
Installing McAfee DLP WCF service
connection between the administration workstation and WCF always uses Windows authentication. If
you have selected Windows authentication, and the logged on user is a member of the WAAG,
connection to the database proceeds without further checking.
The user must be defined in the SQL database. See Adding a user in SQL Server.
Figure 6-1 WCF service local to the ePO database
Option 2: Installing WCF remotely
When installing WCF on a separate server from the McAfee DLP Endpoint database, you can now use
Windows authentication or SQL authentication. The former limitation to only SQL authentication has
been eliminated. The description of the connection details are the same as in local installation.
Figure 6-2 WCF service remote from the ePO database server
Install the McAfee DLP WCF service
There are two steps to installing the McAfee DLP WCF service. When the installation is complete, you
can troubleshoot the installation to resolve problems.
Before you begin
Before installing the McAfee DLP WCF service, create a user in Microsoft SQL server. You
must do this even if you are going to use Windows authentication.
48 McAfee Data Loss Prevention 9.2.0 Installation Guide
6
Installing McAfee DLP Endpoint
Installing McAfee DLP WCF service
Tasks
• Add a user in Microsoft SQL Server on page 49
To use either Windows or SQL authentication with the McAfee DLP WCF service or the
ePolicy Orchestrator database, an authorized user must be defined in the Microsoft SQL
database. The authorized user can be either a Windows or a SQL user. Typically, an account
with the minimal permissions required is created.
• Run the McAfee DLP WCF installer on page 53
The McAfee DLP Windows Communication Foundation (WCF) service is used to
communicate between ePolicy Orchestrator, McAfee DLP Endpoint, and the McAfee DLP
Monitor.
Add a user in Microsoft SQL Server
To use either Windows or SQL authentication with the McAfee DLP WCF service or the ePolicy
Orchestrator database, an authorized user must be defined in the Microsoft SQL database. The
authorized user can be either a Windows or a SQL user. Typically, an account with the minimal
permissions required is created.
Before you begin
To perform this task, you must have Microsoft SQL Server Management Studio installed. If
you are using Microsoft SQL Server Express, you should install the Express version of
Management Studio. The administrator performing the task should have system
administrator rights on the servers involved.
This is a required task. The default authorized user does not work with the McAfee DLP WCF service.
In McAfee DLP Manager product suite, Windows authentication is not supported because
communication is between the ePolicy Orchestrator database (Microsoft SQL) and the McAfee DLP
network product suite database (MySQL).
The credentials you set in the following procedure are used on the Add New Device page to connect McAfee
DLP Manager to ePolicy Orchestrator.
McAfee Data Loss Prevention 9.2.0 Installation Guide 49
6
Installing McAfee DLP Endpoint
Installing McAfee DLP WCF service
Task
1 Open SQL Server Management Studio (Express) and connect to the EPOSERVER instance.
2 In the Object Explorer, right-click the database name then select Properties.
3 On the Security page, select either Window Authentication mode or SQL Server and Windows Authentication mode,
according to which type of authentication you want to use. Click OK.
4 Select Security | Logins. Right-click in the Logins page, then select New Login.
50 McAfee Data Loss Prevention 9.2.0 Installation Guide
6
Installing McAfee DLP Endpoint
Installing McAfee DLP WCF service
5 On the General page of the Login Properties window, select SQL Server authentication and type the logon
name ndlpuser and a password. Set the default database to ePO4_SERVER and the default language
to English. Click OK.
6 On the Server Roles page, select the sysadmin checkbox.
7 On the User Mapping page of the Login Properties window, in the Users mapped to this login section, select
ePO4_SERVER and verify that the new logon user is listed in the User column, and that public is
checked in the database role membership section. Click OK.
8 Under User Mapping, define the database role memberships by selecting the db_owner and public
checkboxes.
9 Select Databases | ePO4_SERVER | Security | Users. Double-click the logon user name.
10 On the Securables page, click Add. Select Specific objects, and click OK.
11 In the Select Objects window, click Object Types and select Databases. Click OK.
McAfee Data Loss Prevention 9.2.0 Installation Guide 51
6
Installing McAfee DLP Endpoint
Installing McAfee DLP WCF service
12 Click Browse. Select [ePO4_SERVER] and click OK twice.
13 If you do not see all six effective permissions, browse through the Explicit Permissions list to locate
each of them and click Grant. Click OK. Repeat steps 9-13 to verify the Effective Permissions.
14 Click OK.
Troubleshoot the McAfee DLP WCF service
After installation of the McAfee DLP WCF service and installation of the McAfee DLP Endpoint policy
console, use the troubleshooter to verify the installation.
To troubleshoot the McAfee DLP WCF service, use the browser page http://localhost:8731/DLPWCF/
Admin/Testing.
Do not run this test page before installing the McAfee DLP Endpoint software suite in McAfee ePolicy
Orchestrator. The tests will fail if the McAfee DLP Endpoint database is not yet installed.
Figure 6-3 The McAfee DLP WCF service testing page
52 McAfee Data Loss Prevention 9.2.0 Installation Guide
6
Installing McAfee DLP Endpoint
Repository folders
Run the McAfee DLP WCF installer
The McAfee DLP Windows Communication Foundation (WCF) service is used to communicate between
ePolicy Orchestrator, McAfee DLP Endpoint, and the McAfee DLP Monitor.
Before you begin
Before installing the McAfee DLP WCF service, create a user in Microsoft SQL Server. You
must do this even if you are going to use Windows authentication.
When installing or upgrading McAfee DLP Endpoint software, you must upgrade the McAfee DLP
Windows Communication Foundation service to the latest version. Failure to upgrade McAfee DLP WCF
can lead to errors when trying to save the global policy to the reporting database or update database
credentials. To prevent this, the new version checks the client and server versions and displays an error
message if they don't match.
Add the logged on user to the Microsoft SQL database as a Windows or SQL user, according to which
form of authorization you plan to use. Log off of ePolicy Orchestrator.
Task
1 Browse to and run the McAfee DLP WCFServiceInstaller.msi installer.
Verify that the McAfee DLP Windows Communication Foundation service installer version matches
the McAfee DLP Endpoint software version you are installing.
2 In step 4 of the installation wizard (WCF Service Settings), do the following:
a Use the default WCF Server Port value. If you must change the server port, consult your McAfee
representative for instructions.
b We recommend setting up a group or groups in Windows Active Directory with the names of
users authorized to log on to the database. You must change the default Web Access Authorized
Groups entry from Everyone to a group or user with authorized access, as described in WCF
installation options.
c If you are using the confidential data redaction feature, select Obfuscate Sensitive Data in RSS Feed.
3 In step 5 of the installation wizard (Microsoft SQL Database), do the following:
a Review the defaults for Database Server and Database Name. Type other values if necessary.
b Select Windows Authentication or SQL Authentication and fill in the associated fields.
4 Click Finish to complete the installation.
Repository folders
Before you begin installation of McAfee DLP Endpoint software, prepare your system as described below.
Two folders and network shares must be created, and their properties and security settings must be
configured appropriately. The folders do not need to be on the same computer as the McAfee DLP
Endpoint Database server, but it is usually convenient to put them there.
We suggest the following folder paths, folder names, and share names, but you can create others as
appropriate for your environment.
McAfee Data Loss Prevention 9.2.0 Installation Guide 53
6
Installing McAfee DLP Endpoint
Repository folders
• c:\dlp_resources\
• c:\dlp_resources\evidence
• c:\dlp_resources\whitelist
• Evidence folder — Certain protection rules allow for storing evidence, so you must designate, in
advance, a place to put it. If, for example, an email is blocked, a copy of the email is placed in the
Evidence folder.
• Whitelist folder — Text fingerprints to be ignored by the DLP Endpoint are placed in a whitelist
repository folder. An example is boilerplate text such as disclaimers or copyright. McAfee DLP
Endpoint software saves time by skipping these chunks of text that are known to not include
sensitive content.
Creating and configuring repository folders
McAfee Data Loss Prevention Endpoint software requires certain repository folders on the server.
These folders must be created and configured before running the installer.
Tasks
• Configure folders on Windows 2003 Server on page 54
Configuration of the repository folders on Windows 2003 Server requires specific security
settings.
• Configure folders on Windows 2008 Server on page 55
Configuration of the repository folders on Windows 2008 Server requires specific security
settings.
Configure folders on Windows 2003 Server
Configuration of the repository folders on Windows 2003 Server requires specific security settings.
Before you begin
Create the evidence and whitelist folders, as described in Before you install the extension.
Both folder are configured in the same manner. Repeat this task for each folder.
Task
1 Right-click the evidence / whitelist folder and select Sharing and Security.
2 In the dialog box that appears, select Share this folder. Modify Share name to evidence$ / whitelist$.
The $ ensures that the share is hidden.
3 Click the Security tab, then click Advanced.
4 On the Permissions tab of the Advanced Security Settings for evidence dialog box, deselect Allow inheritable
permissions.
A confirmation message explains the effect this change will have on the folder.
5 Click Remove. The Permissions tab on the Advanced Security Settings dialog box shows all
permissions eliminated except administrators.
Setting permissions for administrators is required for the whitelist folder. It is optional for the
evidence folder, but can be added as a security precaution. Alternately, you can add permissions
only for those administrators who deploy policies.
54 McAfee Data Loss Prevention 9.2.0 Installation Guide
6
Installing McAfee DLP Endpoint
Repository folders
6 Double-click Administrators entry to open the Permission Entry dialog box. Change the Apply onto option to
This folder, subfolders and files. Click OK.
7 Click Add to select an object type.
8 In the Enter the object name to select text box, type Domain Computers, then click OK to display the
Permission Entry dialog box.
9 In the Allow column, select:
• Create Files/Write Data and Create Folders/Append Data for the evidence folder.
• List Folder/Read Data for the whitelist folder.
Verify that the Apply onto option says This folder, subfolders and files, then click OK.
The Advanced Security Settings dialog box now includes Domain Computers.
10 Click OK twice to close the dialog box.
Configure folders on Windows 2008 Server
Configuration of the repository folders on Windows 2008 Server requires specific security settings.
Before you begin
Create the evidence and whitelist folders, as described in Before you install the extension.
Both folder are configured in the same manner. Repeat this task for each folder.
Task
1 Right-click the evidence / whitelist folder and select Permissions.
2 Click the Sharing tab, then click Advanced sharing. Select the Share this folder option and click Apply.
3 Add the share name evidence$ / whitelist$.
The $ ensures that the share is hidden.
4 Click the Security tab, then click Advanced.
5 On the Permissions tab, deselect the Include inheritable permissions from the object's parent option.
A confirmation message explains the effect this change will have on the folder.
6 Click Remove.
The Permissions tab in the Advanced Security Settings window shows all permissions eliminated.
7 Click Add to select an object type.
8 In the Enter the object name to select field, type Domain Computers, then click OK.
The Permission Entry dialog box is displayed.
9 In the Allow column, select:
• Create Files/Write Data and Create Folders/Append Data for the evidence folder.
• List Folder/Read Data for the whitelist folder.
Verify that the Apply onto option says This folder, subfolders and files, then click OK.
McAfee Data Loss Prevention 9.2.0 Installation Guide 55
6
Installing McAfee DLP Endpoint
User and permission sets
The Advanced Security Settings window now includes Domain Computers.
10 Click Add again to select an object type.
11 In the Enter the object name to select text box, type Administrators, then click OK to display the
Permission Entry dialog box. Set the required permissions.
Adding administrators is required for the whitelist folder. It is optional for the evidence folder, but
can be added as a security precaution. Alternately, you can add permissions only for those
administrators who deploy policies.
12 Click OK twice to close the dialog box.
User and permission sets
We recommend creating specific administrator roles and permissions in ePolicy Orchestrator for
McAfee DLP Manager and McAfee DLP Monitor. These roles can include creating and saving policies,
viewing (but not changing) policies, generating override, uninstall, and quarantine release keys,
viewing the McAfee DLP Monitor, and revealing sensitive fields in the monitor.
Sensitive data redaction and the McAfee DLP Monitor permission sets
To meet the legal demand in some markets to protect confidential information in all circumstances,
McAfee DLP Endpoint software offers a data redaction feature. Fields in the McAfee DLP Monitor
containing confidential information are encrypted to prevent unauthorized viewing. The feature is
designed with a "double key" release. This means that to use the feature, you must create two
permission sets: one to view the monitor and another to view the encrypted fields. Both roles are
required to use the feature.
Create and define McAfee DLP administrators
Creates and defines a McAfee DLP administrator in McAfee ePolicy Orchestrator. Administrative users
can be created either before or after the permission sets assigned to them.
Task
1 Click New User.
2 Type a user name and specify logon status, authentication type, and permission sets.
We recommend creating user groups related to the role, for example DLP Quarantine Administrator.
The order of creating users and permission sets is not critical. If you create users first, user names
appear in the permission set form and you can attach them to the set. If you create permission sets
first, the permission set names appear in the user form and you can attach the user to them.
3 Click Save.
56 McAfee Data Loss Prevention 9.2.0 Installation Guide
6
Installing McAfee DLP Endpoint
User and permission sets
Create and define permission sets
Creates and defines a DLP administrator permission set in McAfee ePolicy Orchestrator Permission sets
are useful for defining different administrative roles in McAfee DLP Endpoint software.
Task
1 Click New Permission Set.
2 Type a name for the set and select users.
The order of creating users and permission sets is not critical. If you create users first, user names
appear in the permission set form and you can attach them to the set. If you create permission sets
first, the permission set names appear in the user form and you can attach the user to them.
3 Click Save.
4 In the Data Loss Prevention field for the new permission set, click Edit.
5 Select the required permissions and click Save.
Figure 6-4 Editing a permission set for McAfee DLP Endpoint
To turn off the sensitive data redaction feature, select User can view DLP Monitor in the monitor section.
DLP permission set options
Permission set options are designed to give granular control over administrator roles.
Table 6-4 Option definitions
Option Definition
User cannot view policies. User is not a policy administrator.
User can only generate Agent Override, Agent User administrator role is limited to override,
Uninstall, and Agent Quarantine Release keys. uninstall, and release keys.
User can only view policies. User can review but not edit policies.
User can view and save policies. User has full policy administrator permissions.
User cannot view DLP Monitor User is not a monitor administrator
User can view DLP Monitor User has full policy administrator permissions.
McAfee Data Loss Prevention 9.2.0 Installation Guide 57
6
Installing McAfee DLP Endpoint
Install the McAfee Data Loss Prevention Endpoint extension
Install the McAfee Data Loss Prevention Endpoint extension
The McAfee DLP Endpoint software extension and the Help module are installed in ePolicy Orchestrator.
Before you begin
Verify that the ePolicy Orchestrator server name is listed under Trusted Sites in the Internet
Explorer security settings.
The default installation is a 90-day license for McAfee Device Control software. If you purchased a
license for full McAfee Data Loss Prevention Endpoint software, you must upgrade the license after you
complete the installation.
Task
1 In ePolicy Orchestrator, select Menu | Software | Extensions, then click Install Extension.
2 Click OK. The extension is installed.
The following applications are installed:
• McAfee DLP Endpoint policy console (in ePolicy Orchestrator | Data Protection)
• McAfee DLP Monitor (in ePolicy Orchestrator | Data Protection)
• DLP Event Parser
3 Click OK.
Initialize the DLP Policy console
The first time you open the McAfee Data Loss Prevention Endpoint policy console, a wizard runs for
first-time initialization.
The wizard can be run at any time by selecting Initialization Wizard from the Tools menu in the McAfee DLP
Endpoint policy console.
The McAfee DLP Endpoint Management Tools installer and McAfee DLP Endpoint policy console
initialization wizard use ActiveX technology. To prevent the installer from being blocked, verify that the
following are enabled in Internet Explorer Tools | Internet Options | Security | Custom level:
• Automatic prompting for ActiveX controls
• Download signed ActiveX controls
Task
1 After the McAfee DLP Endpoint Management Tools installation has completed, the McAfee DLP
Endpoint policy console begins loading. If you have an existing policy, you are prompted to convert
it to the new XML format. Click Convert and skip to step 4.
2 If no previous policy exists, the message DLP global policy is unavailable. Loading default policy appears. Click
OK to continue.
3 When the message Agent configuration is unavailable. Loading a default agent. appears, click OK.
4 When the McAfee DLP Endpoint policy console First Time Initialization wizard appears, complete the
following steps:
58 McAfee Data Loss Prevention 9.2.0 Installation Guide
6
Installing McAfee DLP Endpoint
Initialize the DLP Policy console
Option Description
1 of 8 Click Next.
2 of 8 By default, the file system discovery crawler places sensitive files in quarantine. Though
we do not recommend it, you can delete these files instead by selecting the Support
discovery delete option.
This option is not available until you update to the full McAfee Data Loss Prevention
Endpoint software installation.
For troubleshooting, when you need to review an easily readable version of the policy,
select Generate verbose policy. For most installations, we recommend leaving these
checkboxes unselected.
In very large organizations where the rollout of McAfee DLP Endpoint 9.2 is staged over
time, earlier versions of the plug-in need to coexist. Select the appropriate Backward
compatibility mode:
• No compatibility (all endpoints are version 9.2)
• McAfee DLP Endpoint Agent 9.1 and later
• McAfee DLP Endpoint Agent 9.0 and later
• McAfee DLP Endpoint Agent 3.0 and later
The compatibility option McAfee DLP Endpoint Agent 3.0.5 or current version refers to a
specific hotfix. Unless you specifically know that you are using this hotfix, choose DLP
Agent 3.0 compatibility for all version 3 endpoints.
DLP Agent 2.2 Patch 4 is no longer supported.
Select your directory access protocol: Microsoft Active Directory or OpenLDap. When
using Microsoft AD in very large organizations where search times could be excessive,
select Restrict AD searches to default domain.
When you have completed all changes, click Next.
3 of 8
This step is not available when installing McAfee Device Control
.
Type user names, or click Add to search for user names (optional). Click Next.
We recommend creating a role-based group such as DLP Manual Tagging Users, and
using the group when configuring Access Control.
4 of 8 Type a password and confirmation (required). McAfee DLP Endpoint software version
9.2 requires strong passwords, that is, at least 8 characters with at least one each
uppercase, lower case, digit, and special character (symbol). If you are upgrading, this is
not implemented until you change a password.
If you don't want endpoint key generation events reported to the database, deselect the
checkbox. If you want to use short challenge/response (8 digits instead of 16), select the
checkbox.
See the McAfee Data Loss Prevention Endpoint Product Guide for more information on
Agent bypass.
Click Next.
McAfee Data Loss Prevention 9.2.0 Installation Guide 59
6
Installing McAfee DLP Endpoint
Upgrade the license
Option Description
5 of 8 Browse to the Whitelist storage share, then click Next. The UNC whitelist path is required
to apply the policy to ePolicy Orchestrator. Size limits are displayed, but cannot be
changed in the Initialization wizard.
6 of 8 Modify the default notification messages (optional). Select each event type in turn, and
type the message in the text box. Click Next.
7 of 8 Browse to the evidence storage share and click Next. The evidence storage path is
required to apply the policy to ePolicy Orchestrator. Set the required Evidence Replication
option. See the Release notes: New Features for more information on this option. Click
Next.
8 of 8 Click Finish.
5 The Initialization Wizard dialog box appears with the message, Apply initial configuration?
• If you have not skipped any required steps, you can click Yes and apply the initial policy.
• If you have skipped required steps, click No to complete the initialization.
A password and the evidence storage share are required to complete initialization. The other steps
indicated as required are necessary to complete the policy. They can be skipped during initialization
and completed at a later time. If you did not apply the policy, select File | Save to save the policy to a
file.
6 Click Finish.
Upgrade the license
McAfee DLP Endpoint software comes in two versions, McAfee Device Control and full McAfee Data
Loss Prevention Endpoint with two licensing options for each, 90-day trial and unlimited. The default
installation is McAfee Device Control with a 90-day trial license.
Before you begin
Before starting this task, purchase your upgrade license and get an activation key from
your McAfee sales representative.
Task
1 On the McAfee DLP Endpoint policy console menu bar, select Help | Update License.
The View and Update License window displays the current (default) activation key and expiration date.
2 Click Update.
3 Type or paste the Activation Key in the text box and click Apply.
A warning that you must log on again for the change to take effect appears.
4 Click OK to close the message box, and click Close to close the Update License window, then log off
ePolicy Orchestrator.
5 Log on to ePolicy Orchestrator to complete the upgrade.
6 From the Agent Configuration menu, select Edit Global Agent Configuration.
7 Go to the File Tracking tab and select Device Control and full content protection.
60 McAfee Data Loss Prevention 9.2.0 Installation Guide
6
Installing McAfee DLP Endpoint
Check in the McAfee DLP Endpoint package to ePolicy Orchestrator
8 Go to the Miscellaneous tab. Only the Agent Popup service, Device Blocking, and Reporting Service
modules are selected. Select the remaining modules you require to enable them and click OK.
Do not enable modules you don't use. They increase the McAfee DLP Endpoint agent size and slow
its operation unnecessarily.
9 On the Toolbar, click .
The policy changes are applied to ePolicy Orchestrator.
10 In ePolicy Orchestrator, issue a wake-up call to deploy the policy change to the workstations.
Check in the McAfee DLP Endpoint package to ePolicy
Orchestrator
Any enterprise computer with data protected by McAfee software must have the McAfee Agent
installed, making it a managed computer. To add data loss protection, you must also deploy the
McAfee DLP Endpoint plug-in for McAfee Agent. The installation can be performed using the ePolicy
Orchestrator infrastructure.
Task
1 Select package type Product or Update (.ZIP), browse to ..\HDLP_Agent_9_2_0_xxx.zip, then click Next.
The Check in Package page appears.
If you are upgrading, you are prompted that the product already exists. Click OK. The new package
replaces the old one.
2 Review the details on the screen, then click Save.
The package is added to the master repository.
Deploying McAfee DLP Endpoint
The final stage of McAfee DLP Endpoint software installation is to define a policy, deploy McAfee DLP
Endpoint agents to the managed computers, and verify the installation.
Tasks
• Define a default rule on page 61
To verify that the McAfee DLP Endpoint software has been deployed properly, we
recommend defining a default rule before deploying to the managed computers.
• Deploy McAfee DLP Endpoint with ePolicy Orchestrator on page 62
Before policies can be applied, McAfee DLP Endpoint must be deployed to the endpoint
computers by ePolicy Orchestrator.
• Verify the installation on page 63
After installing McAfee DLP Endpoint software, you should verify the installation in the
McAfee DLP Monitor.
Define a default rule
To verify that the McAfee DLP Endpoint software has been deployed properly, we recommend defining
a default rule before deploying to the managed computers.
The rule described is an example of a simple rule that can be used to test the system.
McAfee Data Loss Prevention 9.2.0 Installation Guide 61
6
Installing McAfee DLP Endpoint
Deploying McAfee DLP Endpoint
Task
1 Create a classification rule:
a In the McAfee DLP Endpoint policy console navigation pane under Content Protection, select
Classification Rules.
b Right-click in the Classification Rules window and select Add New | Content Classification Rule. Rename the
rule Email Classification Rule.
c Double-click the rule icon to modify the rule.
d In step 1 of the rule creation wizard, select either of the options (ANY or ALL) then scroll down
the text patterns list and select Email Address. Click Next three times, skipping to step 4.
e In step 4 of the rule creation wizard, click Add New to create a new category. Name it Email
Category, click OK to accept the new category, then click Finish.
f Right-click the rule icon and select Enable.
2 Create a protection rule:
a In the McAfee DLP Endpoint policy console navigation pane under Content Protection, select Protection
Rules.
b Right-click in the Protection Rules window and select Add New | Removable Storage Protection Rule.
c Double-click the rule icon to modify the rule.
d Click through to step 2 of the rule creation wizard and add the Email Category created when
creating the classification rule in the Included column.
e Click through to step 7 of the rule creation wizard. Select Monitor, then click Finish.
f Right-click the rule icon and select Enable.
3 On the Tools menu, select Run Policy Analyzer. You should receive warnings, but no errors.
If you receive errors, they probably come from improper initialization, such as not specifying an
evidence folder or override password. You can re-run the initialization from the Tools menu to
correct this.
4 On the Toolbar, click . The policy is applied to McAfee ePolicy Orchestrator.
Deploy McAfee DLP Endpoint with ePolicy Orchestrator
Before policies can be applied, McAfee DLP Endpoint must be deployed to the endpoint computers by
ePolicy Orchestrator.
Before you begin
Task
1 In the System Tree, select the level at which to deploy McAfee DLP Endpoint.
Leaving the level at My Organization deploys to all workstations managed by McAfee ePolicy
Orchestrator.
If you select a level under My Organization, the right-hand pane displays the available
workstations. You can also deploy McAfee DLP Endpoint to individual workstations.
62 McAfee Data Loss Prevention 9.2.0 Installation Guide
6
Installing McAfee DLP Endpoint
Uninstalling McAfee DLP Endpoint
2 In the Name field, type a suitable name, for example, Install DLP Endpoint. Typing a description
is optional.
3 Change the Schedule type to Run immediately. Click Next.
4 Review the task summary. When you are satisfied that it is correct, click Save. The task is scheduled
for the next time the McAfee Agent updates the policy. To force the installation to take place
immediately, issue an agent wake-up call.
5 After McAfee DLP Endpoint has been deployed, restart the managed computers.
Verify the installation
After installing McAfee DLP Endpoint software, you should verify the installation in the McAfee DLP
Monitor.
Task
• Verify the McAfee DLP Endpoint installation and apply the policy enforcement by using the
cmdagent.exe /s command. See the McAfee ePolicy Orchestrator McAfee Agent documentation
for more information.
Uninstalling McAfee DLP Endpoint
McAfee Data Loss Prevention Endpoint software is protected from unauthorized removal. There are
two methods of authorized removal.
• Network uninstall from ePolicy Orchestrator, performed by the McAfee ePO administrator.
• Local uninstall using Windows Add or Remove Programs. This method requires a challenge-response key
obtained from the McAfee DLP Administrator.
This task describes the local uninstall option.
Task
1 In the McAfee DLP Endpoint policy console, select Tools | Generate Agent Uninstall Key.
This step can also be performed with the McAfee DLP Help Desk tool, using the Generate Uninstall Key
tab.
2 Fill in the user information in Step 1.
3 Type the uninstall challenge code. (Step 2)
4 Type the agent override key password or select Use password from current policy. (Step 3)
5 Click Generate Key to create the uninstall key for the user.
This Release Code is sent to the user to enter into the request bypass dialog box.
McAfee Data Loss Prevention 9.2.0 Installation Guide 63
6
Installing McAfee DLP Endpoint
Uninstalling McAfee DLP Endpoint
64 McAfee Data Loss Prevention 9.2.0 Installation Guide
7 Integrating McAfee DLP Endpoint into a
unified policy system
Integrate McAfee DLP Endpoint into the McAfee DLP Manager network product suite by installing it on
ePolicy Orchestrator 4.5 or 4.6 and connecting it to McAfee DLP Manager.
Once you have integrated the network products and McAfee DLP Endpoint in a unified solution, you
won't be able to access the existing standalone McAfee DLP Endpoint global policy. Any policy
management will have to be done through McAfee DLP Manager.
The integration is achieved by uniting the McAfee DLP Endpoint global policy within a unified policy
design. When the unified installation is complete, communication between the McAfee DLP system and
its endpoints are handled by the McAfee Agent DLP client.
McAfee DLP Endpoint works with McAfee DLP Manager through ePolicy Orchestrator, so you must
configure all three products to unify the system under the network product suite.
The McAfee Agent DLP client routes policy updates to the clients and collects events from them. If
evidence collecting is enabled in the policy, events are sent to the event parser, then stored in an
evidence folder, which is normally located on the ePolicy Orchestrator.
If McAfee DLP Manager is configured to report endpoint events, they are copied to the ePolicy
Orchestrator database by the McAfee DLP client software, then displayed on the Data-in-Use dashboards.
Installing McAfee Logon Collector is optional, but is especially useful for enterprises that monitor large
numbers of endpoints. McAfee Endpoint Encryption for Files and Folders might also be useful to decrypt
events reported on the Data-in-Use dashboard.
Contents
Setting up Unified DLP on ePolicy Orchestrator
Connecting McAfee DLP Manager and the ePolicy Orchestrator server
Configuring McAfee DLP Endpoint on McAfee DLP Manager
Installation and configuration complete
McAfee Data Loss Prevention 9.2.0 Installation Guide 65
7
Integrating McAfee DLP Endpoint into a unified policy system
Setting up Unified DLP on ePolicy Orchestrator
Setting up Unified DLP on ePolicy Orchestrator
After ePolicy Orchestrator and McAfee DLP Manager are connected, you must install host and network
extensions on McAfee ePO, and add evidence folders on ePolicy Orchestrator and McAfee DLP Manager.
Install the network extension
You must install the latest network extension on ePolicy Orchestrator to establish a connection to
McAfee DLP Manager.
Before you begin
An ePolicy Orchestrator database user must be set up before the network extension is
installed.
Task
1 Open a web browser and enter the location of the network extension into the address bar.
https://<DLP_Manager_name>/eponetdlp/netdlp.zip
The extension can also be downloaded from the McAfee Support Portal, or copied from the /data
directory of the downloaded and expanded McAfee DLP Manager directory.
2 Log on to the ePolicy Orchestrator and go to Menu | Software | Extensions.
3 Click Install Extension.
4 Browse to the netdlp.zip file and click OK.
5 Click OK.
Install the UDLP (host) extension
You must install UDLP extension version 9.2.5.xxx on ePolicy Orchestrator to establish a connection to
ePolicy Orchestrator.
Task
1 Download UDLP extension version 9.2.5.xxx from the McAfee Support Portal to your desktop.
2 Log on to the ePolicy Orchestrator and go to Menu | Software | Extensions.
3 Click Install Extension.
4 Browse to the UDLP extension on your desktop and click OK.
5 Click Policy Catalog and select View/Duplicate to configure the agent.
The McAfee DLP Endpoint Management Tools installer runs, then the agent configuration console
begins loading. Add the required information to the fields.
6 Assign this policy to the agent.
If the agent configuration is not deployed on the endpoint computer, none of the protection rules
will work.
66 McAfee Data Loss Prevention 9.2.0 Installation Guide
7
Integrating McAfee DLP Endpoint into a unified policy system
Setting up Unified DLP on ePolicy Orchestrator
Configure McAfee Agent on ePolicy Orchestrator
You must add an evidence folder on ePolicy Orchestrator to collect the events forwarded by the McAfee
Agent client, then configure essential features to enable McAfee DLP Endpoint functionality through
McAfee DLP Manager.
Task
1 In the ePolicy Orchestrator header, select Menu | Policy | Policy Catalog.
2 From the Product menu, select Data Loss Prevention 9.2: Policies.
3 From the McAfee Default Client Configuration.
After you name the duplicate and select it, the Settings page appears.
4 In the Evidence tab, type the UNC Path of the evidence folder share and folder name.
\\server name\evidence
The same server will also be entered on the McAfee DLP Manager Add New Evidence Server page.
5 Select Copy evidence using NETWORK SERVICE or logged on user.
6 In the Evidence Replication section, select the Evidence and Hit Highlighting checkboxes.
Show abbreviated hits appears in the associated field.
Enabling this option allows users to easily see matching text in the events reported to the McAfee
DLP Manager Data-in-Use dashboards.
7 In the Security tab, type in a list of authorized users and groups to enable manual tagging of files
on agent machines.
For example, type in Everyone to give Manual Tagging Authorization to all users.
This sets up the agent to support manual tagging through McAfee DLP Manager. Selecting the Allow
Manual Tagging checkbox when creating tags on the Endpoint Configuration page makes the tags visible to
trusted users, who can use them to classify documents on their desktops.
8 Click Save.
Add an evidence folder on McAfee DLP Manager
An existing evidence folder must be registered to McAfee DLP Manager to transmit the events
collected by the McAfee Agent client.
Before you begin
McAfee DLP Manager and ePolicy Orchestrator must be authenticated to each other, and the
network and UDLP (host) extensions must be installed, and the McAfee Agent DLP client
must be installed.
The folder is normally on the ePolicy Orchestrator, but might be located on another computer.
Task
1 In ePolicy Orchestrator, select Menu | Data Loss Prevention | DLP Sys Config | System Administration | Devices.
2 On your Linux-based appliance, select System | System Administration | Devices.
3 From the Actions menu, select New Evidence Server.
4 In the Add New Evidence Server window, enter the required information in the following format.
McAfee Data Loss Prevention 9.2.0 Installation Guide 67
7
Integrating McAfee DLP Endpoint into a unified policy system
Connecting McAfee DLP Manager and the ePolicy Orchestrator server
• Hostname — \\<server name>
• IP Address — <IP address>
• Username — <domain name\user name
• Password — ********
5 Click Add.
Connecting McAfee DLP Manager and the ePolicy Orchestrator
server
McAfee DLP Manager and the ePolicy Orchestrator server must be authenticated to each other to
initiate the unified policy installation.
Each product requires information from the other before they can be connected. The database name is
needed from ePolicy Orchestrator, and an epouser account is needed from the McAfee DLP Manager.
Gather ePolicy Orchestrator registration information
You must log on to the ePolicy Orchestrator server (https://servername:port/core/config) and
SQL Server Configuration Manager to get the information needed to register McAfee DLP Manager on McAfee
ePO.
Table 7-1 Sources for ePolicy Orchestrator data
Field or menu item Where to find data
ePO database IP address or Menu | Configuration | Registered Servers (local McAfee ePO server)
hostname
ePO database password The SQL password created in Microsoft SQL Server Management Studio
ePO database port SQL Server Configuration Manager | TCP/IP Properties | IP Addresses | TCP Ports
ePO database user The logon name created in Microsoft SQL Server Management Studio
Unified policy / Incident copy If incident copy only is selected, no policy updates will be routed to
endpoints through ePolicy Orchestrator
ePO database Menu | Configuration | Registered Servers | Actions | Edit | Next | Database instance
ePO database instance Menu | Configuration | Registered Servers | Actions | Edit | Next | SQL Server
instance | instance name
ePO GUI IP address Address bar of McAfee ePO server
ePO GUI user User account name used to log on to McAfee ePO server
ePO GUI password User account password used to log on to McAfee ePO server
ePO GUI port Address bar of McAfee ePO server
Add a McAfee ePO database user for McAfee DLP Manager
Create ePolicy Orchestrator database users to authenticate connections from McAfee DLP Manager to
ePolicy Orchestrator servers. ePolicy Orchestrator servers are Windows-based, but a McAfee DLP
Manager is a Linux server that does not support Windows-based authentication of users. Database
user accounts are used to make the connection.
Creating an ePolicy Orchestrator database user is only one aspect of establishing a connection to the
ePolicy Orchestrator server, which is required to support McAfee DLP Endpoint features.
68 McAfee Data Loss Prevention 9.2.0 Installation Guide
7
Integrating McAfee DLP Endpoint into a unified policy system
Connecting McAfee DLP Manager and the ePolicy Orchestrator server
Task
1 In ePolicy Orchestrator, select Menu | Data Loss Prevention | DLP Sys Config | User Administration | DB User.
2 On McAfee DLP Manager, select System | User Administration | DB User.
3 On the ePO User Information page, enter and confirm a password.
The ePolicy Orchestrator User Name is not configurable.
4 Type an IP Address for the ePolicy Orchestrator user's account and Add it to the Selected IP Addresses box.
Repeat if more than one ePolicy Orchestrator user is needed.
5 Click Apply.
Register McAfee DLP Manager on ePolicy Orchestrator server
Registering McAfee DLP Manager on ePolicy Orchestrator completes the connection between the two.
Before you begin
You must have an ePolicy Orchestrator database user ready for entry on the ePolicy
Orchestrator Registered Server Builder page.
After McAfee DLP Manager and ePolicy Orchestrator are registered to each other, the extensions and
the McAfee Agent DLP client can be set up to manage McAfee DLP Endpoint communications between
the systems.
Task
1 In ePolicy Orchestrator, select Menu | Configuration | Registered Servers.
2 Click New Server.
3 Type in the name of the McAfee DLP Manager, add optional notes, and click Next.
The Registered Server Builder page appears.
4 In the Description field, type in the name of the McAfee DLP Manager.
5 In the Database Password field, type in the epouser database password from the McAfee DLP Manager
System | User Administration | DB User page.
This password allows access to the McAfee DLP Manager MySQL database from ePolicy Orchestrator.
6 If applicable, select the Copy Incidents/Device Data.
7 Type in the user name and password to McAfee DLP Manager and set the refresh period.
8 Click Test Connection.
9 If the test is successful, click OK.
Register ePolicy Orchestrator on McAfee DLP Manager
Registering ePolicy Orchestrator on McAfee DLP Manager initiates the connection between the two.
Before you begin
The network and unified DLP extensions must be installed at this point. You must have
ePolicy Orchestrator registration information ready for entry on the Add New Device page.
McAfee Data Loss Prevention 9.2.0 Installation Guide 69
7
Integrating McAfee DLP Endpoint into a unified policy system
Configuring McAfee DLP Endpoint on McAfee DLP Manager
Task
1 In ePolicy Orchestrator, select Menu | Data Loss Prevention | DLP Sys Config | System Administration | Devices.
2 On your Linux-based appliance, select System | System Administration | Devices.
3 From the Actions menu, select Add New Device.
4 Select the ePO device checkbox.
5 Select Actions | New Device.
6 Enter the information gathered from the ePolicy Orchestrator Registered Server Builder | 2 Details page.
7 Click Add.
8 Click OK to confirm or Cancel the registration.
9 Wait for the Status icon in the device list to turn green.
If the icon turns red, the netdlp.zip extension is probably not installed on ePolicy Orchestrator.
The CPU usage display indicates that the registration tasks being performed. McAfee DLP Manager
does not display any CPU activity, because it serves only as a collection point for the data. Other
machines are capturing and indexing data and the processor indicates the CPU utilization. It should
not go over 70—80%.
If registration seems to be taking a long time, try refreshing the page.
Checking the connection
If your connection through McAfee DLP Manager is successful, the ePolicy Orchestrator will display a
green Status icon on the System page.
The status icon does not apply to the evidence server, which is normally a folder on the ePolicy
Orchestrator server. If it is listed, it has been successfully added to McAfee DLP Manager.
If the ePolicy Orchestrator server loses connection to the database, you cannot use https://
servername:port/core/config to reconnect to the database. Refer to KB66320 in the McAfee
Knowledgebase for more information.
Configuring McAfee DLP Endpoint on McAfee DLP Manager
After McAfee DLP Endpoint and its components are installed on ePolicy Orchestrator, you must
configure the system to start detecting endpoint events through McAfee DLP Manager.
After McAfee DLP Endpoint is integrated McAfee DLP Manager, the following tasks must be completed
before McAfee DLP Endpoint can work with the network product suite.
• Enable unified policy management by generating a policy, setting a posting period, and selecting a
backward compatibility mode.
• Add an agent override password to encrypt and decrypt evidence and override default reactions.
• Add a list of printer models that cannot be controlled by McAfee DLP software.
• Create tags, then set up optional manual tagging
70 McAfee Data Loss Prevention 9.2.0 Installation Guide
7
Integrating McAfee DLP Endpoint into a unified policy system
Configuring McAfee DLP Endpoint on McAfee DLP Manager
When these operations are complete, you can define unified rules on the Policies page, then view the
Incidents | Data-in-Use dashboard to verify that the endpoint events are being generated and reported.
Click the Columns icon, then add or remove columns to display exactly the information that is needed.
Generate a global policy for McAfee DLP Endpoint
When you manage endpoints from McAfee DLP Manager, you must generate a policy, set a posting
interval, and select a compatibility mode. These settings support the distribution of McAfee DLP
Endpoint events to McAfee DLP Manager dashboards through ePolicy Orchestrator.
Rule definitions for McAfee DLP Endpoint were originally designed to share a single global policy
definition — only one policy supported multiple rules. But McAfee DLP Manager is designed around a
collection of unified international policies, and the McAfee DLP Endpoint global policy is accommodated
within that system.
If McAfee Host DLP is already installed on ePolicy Orchestrator, using the McAfee DLP Endpoint
networked version will overwrite the events on the evidence server. Because of this potential problem,
you must deliberately generate a policy to support installation of the updated endpoint product.
You must also set an interval for posting policy modifications through ePolicy Orchestrator. By default,
rule definitions are updated on the McAfee DLP Endpoint extension every 30 seconds, but you can
define a more conservative transfer interval (up to two hours, or 7200 seconds) by editing the Time
Duration for Posting Policy Definition setting.
Task
1 In ePolicy Orchestrator, select Menu | Data Loss Prevention | DLP Sys Config | Endpoint Configuration |
Miscellaneous and click Manage Endpoints.
2 On your Linux-based appliance, select System | Endpoint Configuration | Miscellaneous and click Manage
Endpoints.
3 Select the Generate Policy for Endpoint checkbox.
4 In the Time Duration for Posting Policy Definition field, enter a number between 30 and 7200 seconds.
The policy is generated, posted from McAfee DLP Manager to ePolicy Orchestrator, saved in the
database, forwarded to the connected agents, and updated at the defined interval.
5 Click Submit.
Maintaining compatibility with installed McAfee clients
Because McAfee DLP Manager supports multiple versions of McAfee DLP Endpoint client, the system
must be configured to handle the correct McAfee DLP agent before the system is implemented.
Management of endpoints by McAfee DLP Manager is disabled by default to avoid interference with any
existing McAfee DLP Host (v9.0 and 9.1) or McAfee DLP Endpoint (v9.2) operations that might already
be running on ePolicy Orchestrator.
Because any existing software installations must continue to be supported, the default unified policy
configuration is not activated until you generate a policy to provide the groundwork for connection
with the McAfee Agent client through ePolicy Orchestrator. Endpoints cannot be managed until a policy
is assigned, and events cannot be monitored until the McAfee Agent client has been updated.
The default configuration is DLP Agent 9.0 and above. If the McAfee Host DLP product installed on McAfee
ePolicy Orchestrator was released before version 9.1, no change is needed on the Manage Endpoints page.
The unified policy management process is initiated by selecting the Generate Policy for Endpoint checkbox
on the system Manage Endpoints page.
McAfee Data Loss Prevention 9.2.0 Installation Guide 71
7
Integrating McAfee DLP Endpoint into a unified policy system
Configuring McAfee DLP Endpoint on McAfee DLP Manager
The most significant reason for maintaining earlier versions of the endpoint product is the need for
staged updates. A group of clients might be updated to the new version, but support for older clients
still in use might still be needed.
The need for digital rights management, which controls use of digital content not authorized by the
content provider, might be an additional consideration. This feature of McAfee DLP Endpoint (also
known as McAfee Host DLP) is not supported in McAfee DLP Manager, so network and endpoint
applications might have to be run separately.
But if McAfee DLP Endpoint 9.1 is installed and digital rights management is not needed, No compatibility
should be selected. This means that the new features in that release will be available in the network
product suite. Features like Document Scan Scope and Password Protected Files will appear in the user interface
only if the 9.1 version of the McAfee Agent client is accessible through McAfee DLP Manager.
Set an Agent Override password
An Agent Override password must be defined before doing any McAfee DLP Endpoint task to ensure
encryption and decryption of evidence, and the possibility of reversing any default reactions.
A key must be used to unblock quarantined files, unlock and decrypt encrypted files, request
justification for blocked actions, or work around any other events that have been generated by McAfee
Agent. The administrator provides this password when appropriate.
For example, a unified rule might protect a certain group of financial files on certain network shares
and all endpoints. But because certain endpoint users will need read and write access to those files, it
might include a selected Request Justification checkbox in the Data-in-Use action rule that is applied to that
rule. As a result, when an authorized user opens the blocked file, he might be presented with a
Request Justification pop-up that will allow the administrator to make an exception to the rule by
providing the password. (The specific process and action is determined by the administrator.)
Task
1 In ePolicy Orchestrator, select Menu | Data Loss Prevention | DLP Sys Config | Endpoint Configuration |
Miscellaneous and click Agent Override Password.
2 On your Linux-based appliance, select System | Endpoint Configuration | Miscellaneous and click Agent
Override Password.
3 Enter a password in the Password field and confirm it.
McAfee DLP Endpoint 9.2 requires strong passwords — 8 or more upper and lower case characters,
plus a number and a symbol.
4 Click Submit.
Set the manual tagging option
If you have administrative privileges, you can apply tag labels to allow trusted users to classify specific
documents . If the Allow Manual Tagging checkbox is selected during that process, the tag is visible to your
trusted users, who can use it to classify specific documents by applying the appropriate tag.
Before you begin
McAfee DLP Endpoint and its components must be set up on McAfee DLP Manager.
After they are created, manual tags are pushed to users at endpoints by the McAfee Agent client.
The ability to classify documents with tags encourages users to take independent action to protect files
within their areas of responsibility. For example, users at medical facilities might be trusted to apply
HIPAA tags to patient records that must be kept confidential by law.
72 McAfee Data Loss Prevention 9.2.0 Installation Guide
7
Integrating McAfee DLP Endpoint into a unified policy system
Installation and configuration complete
If the Allow Manual Tagging checkbox is not selected, file tagging can still be done manually — but only by
administrative users, who can tag or remove files individually or in groups.
Task
1 In ePolicy Orchestrator, select Menu | Data Loss Prevention | DLP Sys Config | System Administration | Endpoint
Configuration | Tag Labels.
2 On your Linux-based appliance, select System | System Administration | Endpoint Configuration | Tag Labels.
3 Select a tag.
4 Select the Allow Manual Tagging checkbox.
5 Click Save.
Installation and configuration complete
Installation and configuration are now complete.
You can now start working with the unified policy version of McAfee DLP Endpoint. McAfee
recommends that you start by setting up protection rules and viewing the events reported on the
ePolicy Orchestrator Data-in-Use dashboard.
Consult the Product Guide for McAfee Total Protection for Data Loss Prevention 9.2 for more information.
McAfee Data Loss Prevention 9.2.0 Installation Guide 73
7
Integrating McAfee DLP Endpoint into a unified policy system
Installation and configuration complete
74 McAfee Data Loss Prevention 9.2.0 Installation Guide
Index
A M
about this guide 5 managing DLP 8
administrators, defining 56 McAfee ServicePortal, accessing 6
Microsoft SQL, adding a user 49
B Microsoft SQL, installing 53
backward compatibility 58
P
C permission set options 57
configuration, server 45 permission sets, defining 57
conventions and icons used in this guide 5 policy, initializing 58
D R
default rule, defining 61 redaction 53, 56
DLP administrators, defining 56 roles and permissions 53
DLP endpoint
checking in to ePolicy Orchestrator 61 S
DLP Endpoint server configuration 45
deploying 62 server software requirements 43
deployment verification 63 ServicePortal, finding product documentation 6
uninstalling 63 supported operating systems 43
DLP Help extension, installing 58 system requirements 43
DLP Policy console, installing 58
documentation T
audience for this guide 5 Technical Support, finding product information 6
product-specific, finding 6
typographical conventions and icons 5 U
uninstalling DLP Endpoint 63
E
ePolicy Orchestrator V
installing 45, 46 verifying the installation 63
evidence folder 53
evidence folder, configuring on Windows Server 2003 54 W
evidence folder, configuring on Windows Server 2008 55
WCF, installation options 47
WCF, installing 53
H
WCF, troubleshooting 52
hardware requirements 43 whitelist folder 53
whitelist folder, configuring on Windows Server 2003 54
I whitelist folder, configuring on Windows Server 2008 55
installation 10
L
license, Device Control and DLP 60
McAfee Data Loss Prevention 9.2.0 Installation Guide 75
700-3811A00
You might also like
- Programming the Intel Galileo: Getting Started with the Arduino -Compatible Development BoardFrom EverandProgramming the Intel Galileo: Getting Started with the Arduino -Compatible Development BoardRating: 5 out of 5 stars5/5 (1)
- CompTIA Linux+ Certification Study Guide (2009 Exam): Exam XK0-003From EverandCompTIA Linux+ Certification Study Guide (2009 Exam): Exam XK0-003No ratings yet
- Mcafee Virusscan For Mac 9.6.0: Product GuideDocument47 pagesMcafee Virusscan For Mac 9.6.0: Product GuideBui Hong MyNo ratings yet
- Getting Started Guide: Ibm Security Qradar Risk ManagerDocument41 pagesGetting Started Guide: Ibm Security Qradar Risk Managermohamed saadNo ratings yet
- Rzal 2 MSTDocument186 pagesRzal 2 MSTKumar ENo ratings yet
- Tie 230 Ig 0-00 En-UsDocument45 pagesTie 230 Ig 0-00 En-UsZMarku Jo PeNo ratings yet
- ndlp_931_pg_a_en-usDocument349 pagesndlp_931_pg_a_en-usAaron LuNo ratings yet
- Is 901SP1 IIR 02 Installation enDocument35 pagesIs 901SP1 IIR 02 Installation enAnsari Asif FaheemNo ratings yet
- LightOS Install Guide V3 2 1Document99 pagesLightOS Install Guide V3 2 1bharatrautNo ratings yet
- Software Installation Guide: Visual Effects and Finishing 2010 EditionDocument38 pagesSoftware Installation Guide: Visual Effects and Finishing 2010 EditionjeremiahNo ratings yet
- Ibm Powervp: Power SystemsDocument40 pagesIbm Powervp: Power Systemsmevtorres1977No ratings yet
- HP Storage Works Command View EVA Installation GuideDocument39 pagesHP Storage Works Command View EVA Installation Guideshibu000No ratings yet
- Xseries 345 Type 8670 - Hardware Maintenance ManualDocument182 pagesXseries 345 Type 8670 - Hardware Maintenance ManualRay CoetzeeNo ratings yet
- CV EVA Installation V 4.1 Without SMADocument34 pagesCV EVA Installation V 4.1 Without SMAGmail sNo ratings yet
- NetBackup Flex Appliance SecurityDocument14 pagesNetBackup Flex Appliance SecuritySuganthan RamadossNo ratings yet
- MAXtreme Users Guide v7.00.03Document17 pagesMAXtreme Users Guide v7.00.03Adilson VicenteNo ratings yet
- Mcafee Endpoint Security 10.6.0 - Installation Guide (Mcafee Epolicy Orchestrator) - Windows 1-29-2020Document36 pagesMcafee Endpoint Security 10.6.0 - Installation Guide (Mcafee Epolicy Orchestrator) - Windows 1-29-2020JasonTiamsonNo ratings yet
- Ms Mcafee Agent Product Guide PDFDocument72 pagesMs Mcafee Agent Product Guide PDFCitra Selviana FebrianyNo ratings yet
- Video Analytics V4 Installation GuideDocument72 pagesVideo Analytics V4 Installation GuideDaniel LopezNo ratings yet
- Airfiber 11fxDocument58 pagesAirfiber 11fxEsteban Becerra RiosNo ratings yet
- Mcafee Endpoint Security 10.6.0 - Installation Guide - MacosDocument23 pagesMcafee Endpoint Security 10.6.0 - Installation Guide - MacosJulian Chaparro LattorreNo ratings yet
- DMX BanerDocument94 pagesDMX BanerMark BukerNo ratings yet
- Esm 103x PG En-Us PDFDocument338 pagesEsm 103x PG En-Us PDFmbaezasotoNo ratings yet
- Getting Started With The Xilinx Spartan-6 FPGA SP605 Evaluation KitDocument32 pagesGetting Started With The Xilinx Spartan-6 FPGA SP605 Evaluation KitAnonymous bSvWwFNo ratings yet
- Installation Guide - IBM System x3850 M2 and x3950 M2 (7141, 7233, 7234)Document100 pagesInstallation Guide - IBM System x3850 M2 and x3950 M2 (7141, 7233, 7234)jojoloNo ratings yet
- Aeons ZTPsDocument29 pagesAeons ZTPsmmihir82No ratings yet
- ENS 10.5 InstallationDocument67 pagesENS 10.5 InstallationSecret SantaNo ratings yet
- NSP 83 Installation Guide RevO En-UsDocument200 pagesNSP 83 Installation Guide RevO En-UsDavid VillanuevaNo ratings yet
- Airfiber AF-11FX UG PDFDocument58 pagesAirfiber AF-11FX UG PDFKevin RiveraNo ratings yet
- Banner Student Overall Installation Guide 9.3Document57 pagesBanner Student Overall Installation Guide 9.3Sandeep GummadiNo ratings yet
- Pyscada Documentation: Release 0.6.17B2Document27 pagesPyscada Documentation: Release 0.6.17B2Jagadish PaulNo ratings yet
- Mcafee Data Loss Prevention 11.2.x Product Guide 6-16-2020Document226 pagesMcafee Data Loss Prevention 11.2.x Product Guide 6-16-2020tuanvukma6bNo ratings yet
- Manual Del Usuario LinkPlanner 3.1.2Document207 pagesManual Del Usuario LinkPlanner 3.1.2Fernando EspañaNo ratings yet
- NSP 83 Best Practices Guide Reve En-Us PDFDocument68 pagesNSP 83 Best Practices Guide Reve En-Us PDFabbuasherNo ratings yet
- InstallingDocument72 pagesInstallingSmitha VasNo ratings yet
- FOCIS Flex UserGuide FOCIS-FLX-1000Document26 pagesFOCIS Flex UserGuide FOCIS-FLX-1000GreciaNo ratings yet
- Installing and Configuring The Avaya S8400 Media Server: Release 3.1Document88 pagesInstalling and Configuring The Avaya S8400 Media Server: Release 3.1Ahmed hassan hafezNo ratings yet
- Ansible Tower Quick InstallDocument16 pagesAnsible Tower Quick InstallRag AravNo ratings yet
- Installation and Using Guide: Gigabit Ethernet-SX PCI-X Adapter and Dual Port Gigabit Ethernet-SX PCI-X AdapterDocument32 pagesInstallation and Using Guide: Gigabit Ethernet-SX PCI-X Adapter and Dual Port Gigabit Ethernet-SX PCI-X Adapterua09108No ratings yet
- NSP 92 Best Practices Guide RevA En-UsDocument68 pagesNSP 92 Best Practices Guide RevA En-UsAndres Miliano RodriguezNo ratings yet
- Guia de Instalacion de Mcafee Endpoint Security 10.7.x.pdf Filenameutf-8guc3ada20de20instalacic3b3n 9-27-2020 PDFDocument70 pagesGuia de Instalacion de Mcafee Endpoint Security 10.7.x.pdf Filenameutf-8guc3ada20de20instalacic3b3n 9-27-2020 PDFLuis Miguel Arce HuamanchumoNo ratings yet
- Citrix - Netscaler - v12 Administration GuideDocument3,766 pagesCitrix - Netscaler - v12 Administration GuideVishal Patel100% (2)
- Win ConfigGuideDocument117 pagesWin ConfigGuidetuyulNo ratings yet
- FOCIS Flex User GuideDocument26 pagesFOCIS Flex User GuideJael ChidNo ratings yet
- Epo 530 PG 0-00 En-UsDocument317 pagesEpo 530 PG 0-00 En-UsLama MokNo ratings yet
- Erdas Book by - Hassan MohamedDocument116 pagesErdas Book by - Hassan Mohamedomer1243No ratings yet
- Best Practice Security VMware HorizonDocument18 pagesBest Practice Security VMware HorizonppicyberNo ratings yet
- Mcafee Data Loss Prevention Monitor 11.1.x Installation Guide 11-7-2022Document57 pagesMcafee Data Loss Prevention Monitor 11.1.x Installation Guide 11-7-2022hakim hogNo ratings yet
- VMW 10q3 White Paper Cloud Director Security PDFDocument37 pagesVMW 10q3 White Paper Cloud Director Security PDFBernie Alejandro Miton CornejoNo ratings yet
- Reveal User GuideDocument98 pagesReveal User GuideYuriko MartinezNo ratings yet
- Veeam Backup 12 0 Whats NewDocument32 pagesVeeam Backup 12 0 Whats Newhaythem maghrebiaNo ratings yet
- itrioWF UserManual PDFDocument22 pagesitrioWF UserManual PDFCehanNo ratings yet
- Veritas Netbackup 5.0: Installation GuideDocument135 pagesVeritas Netbackup 5.0: Installation GuideRakesh SinghNo ratings yet
- Deploy Web Apps With DockerDocument61 pagesDeploy Web Apps With DockerlenhhoxungNo ratings yet
- HP Z800 Workstation Hardware Setup Guide: Visual Eff Ects, Finishing, and Color GradingDocument46 pagesHP Z800 Workstation Hardware Setup Guide: Visual Eff Ects, Finishing, and Color Gradingdiyar physicistNo ratings yet
- Epo 510 BPGDocument213 pagesEpo 510 BPGsanjay guravNo ratings yet
- GG Java v3Document46 pagesGG Java v3metallic1No ratings yet
- Mcafee DLP 11.0.400Document215 pagesMcafee DLP 11.0.400hoangcongchucNo ratings yet
- Zeb-ZebraNet 10-100 Internal Print Server 14197L-005Document132 pagesZeb-ZebraNet 10-100 Internal Print Server 14197L-005João CarlosNo ratings yet
- Programming Arduino Next Steps: Going Further with Sketches, Second EditionFrom EverandProgramming Arduino Next Steps: Going Further with Sketches, Second EditionRating: 3 out of 5 stars3/5 (3)
- HP 2530 Switch Series DataSheetDocument24 pagesHP 2530 Switch Series DataSheetluongnamNo ratings yet
- Fortigate 800C: Features & BenefitsDocument4 pagesFortigate 800C: Features & BenefitskishorsriramNo ratings yet
- CR15iNG: Future-Ready Security For SOHO/ROBO NetworksDocument2 pagesCR15iNG: Future-Ready Security For SOHO/ROBO NetworkskishorsriramNo ratings yet
- CyberoamCR100iNG PDFDocument2 pagesCyberoamCR100iNG PDFkishorsriramNo ratings yet
- J6350Document10 pagesJ6350Carlos Eduardo Segura VillarrealNo ratings yet
- Data Sheet c78-686782Document8 pagesData Sheet c78-686782ANOMUNSHANo ratings yet
- Cisco 3900 Series Udated FeaturesDocument18 pagesCisco 3900 Series Udated FeatureskishorsriramNo ratings yet
- Cisco Smart Net Total Care Service PDFDocument8 pagesCisco Smart Net Total Care Service PDFedwin_serpas2894No ratings yet
- Cisco Nexus 3048 Switch: Product OverviewDocument11 pagesCisco Nexus 3048 Switch: Product OverviewkishorsriramNo ratings yet
- CITRIX NS TRAD Site Resources Dynamic Salesdocs Adv Load Balancers 8 Features1Document9 pagesCITRIX NS TRAD Site Resources Dynamic Salesdocs Adv Load Balancers 8 Features1Alaa Al-saggafNo ratings yet
- CISCO Firepower NXGFWDocument24 pagesCISCO Firepower NXGFWkishorsriramNo ratings yet
- DATA SWITCH Product Data Sheet0900aecd806b0bd8Document17 pagesDATA SWITCH Product Data Sheet0900aecd806b0bd8Henry Santiago FloresNo ratings yet
- HP 280 Pro G5 - I5Document2 pagesHP 280 Pro G5 - I5kishorsriramNo ratings yet
- Cisco 500 Series Stackable Managed SwitchesDocument19 pagesCisco 500 Series Stackable Managed SwitchesMatheus AcacioNo ratings yet
- FortiOS-6 0 6-HandbookDocument2,702 pagesFortiOS-6 0 6-HandbookHumail JamalNo ratings yet
- 3par - Storeserv - 7200 - Installation and Setup PDFDocument35 pages3par - Storeserv - 7200 - Installation and Setup PDFkishorsriramNo ratings yet
- Guest Operating System Installation GuideDocument90 pagesGuest Operating System Installation Guidebalraj1No ratings yet
- 9.controlling Services and DaemonsDocument38 pages9.controlling Services and DaemonsJenberNo ratings yet
- Linux MITDocument206 pagesLinux MITquang khải trầnNo ratings yet
- Linux QuestionsDocument11 pagesLinux QuestionsMurali TungaNo ratings yet
- IT WorkShop Lab ManualDocument74 pagesIT WorkShop Lab ManualcomputerstudentNo ratings yet
- DracutDocument12 pagesDracutcarlosNo ratings yet
- 4532 DualBootDocument6 pages4532 DualBootNaveen IdxNo ratings yet
- RH124 RHEL6 en 1 20101029 SlidesDocument45 pagesRH124 RHEL6 en 1 20101029 SlidesShekhar Kumar100% (1)
- Kali Linux 3 in 1 Beginners GuideDocument420 pagesKali Linux 3 in 1 Beginners GuideQuod AntichristusNo ratings yet
- 17 PDFDocument9 pages17 PDFElena PaulNo ratings yet
- Grub CFGDocument12 pagesGrub CFGJKP GamingNo ratings yet
- Puppy Linux Installation Guide (Dual Boot)Document6 pagesPuppy Linux Installation Guide (Dual Boot)Bulu Thaodem100% (1)
- Download ebook Cert Guide Red Hat Rhcsa 9 Ex200 Pdf full chapter pdfDocument67 pagesDownload ebook Cert Guide Red Hat Rhcsa 9 Ex200 Pdf full chapter pdfmary.johnson764100% (23)
- POC Linux7 Multinode GFS2 Cluster On CentOS 7.3Document69 pagesPOC Linux7 Multinode GFS2 Cluster On CentOS 7.3kjell_furnesNo ratings yet
- Why Antibiotics Should Not Be OverusedDocument10 pagesWhy Antibiotics Should Not Be Overusedoicfbd100% (3)
- Number: 101-500 Passing Score: 800 Time Limit: 120 Min File Version: 1Document30 pagesNumber: 101-500 Passing Score: 800 Time Limit: 120 Min File Version: 1feliugarciaNo ratings yet
- Linux Cheat SheetDocument24 pagesLinux Cheat SheetAnkit AgrawalNo ratings yet
- Change Boot Order in Windows Linux Dual Boot With Grub CustomizerDocument1 pageChange Boot Order in Windows Linux Dual Boot With Grub CustomizerMusa DamaNo ratings yet
- Applies To:: Zpool Import and Mount of BE When Booted From Alternate Device in Solaris 11 (Doc ID 1912037.1)Document4 pagesApplies To:: Zpool Import and Mount of BE When Booted From Alternate Device in Solaris 11 (Doc ID 1912037.1)Fabrizio GiordanoNo ratings yet
- Reset Root Password LinuxDocument6 pagesReset Root Password LinuxDiego BetancourtNo ratings yet
- Manjaro Linux Beginner User GuideDocument96 pagesManjaro Linux Beginner User GuideGeorge Stroud100% (1)
- Booting The Linux Kernel Without An Initrd - Initramfs - DOTSLASHLINUXDocument14 pagesBooting The Linux Kernel Without An Initrd - Initramfs - DOTSLASHLINUXalexNo ratings yet
- Rufus - Create Bootable USB Drives The Easy WayDocument6 pagesRufus - Create Bootable USB Drives The Easy WaySyed Hassan Tariq100% (2)
- Void Linux HandbookDocument150 pagesVoid Linux HandbooknillblenderNo ratings yet
- Computer ForensicsDocument49 pagesComputer ForensicsJKONo ratings yet
- Linux Booting Process - A Step by Step Tutorial For Understanding Linux Boot SequenceDocument7 pagesLinux Booting Process - A Step by Step Tutorial For Understanding Linux Boot Sequencedeepak407No ratings yet
- Uefi Dual or More Boot Using RefindDocument13 pagesUefi Dual or More Boot Using RefindLeandro MoraisNo ratings yet
- Install Windows 7 From USBDocument153 pagesInstall Windows 7 From USBravi_gm81517No ratings yet
- Usb BootDocument67 pagesUsb BootnravinNo ratings yet
- Red Hat Enterprise Linux 7: Migration Planning GuideDocument89 pagesRed Hat Enterprise Linux 7: Migration Planning Guidedhaneeshd_2No ratings yet
- Lpic 2Document28 pagesLpic 2vilese7No ratings yet