Professional Documents
Culture Documents
Security and Fraud Issues
Uploaded by
Ethan MonkhouseCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Security and Fraud Issues
Uploaded by
Ethan MonkhouseCopyright:
Available Formats
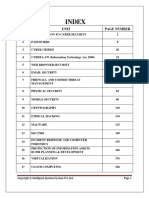
Information security activities that protect info systems data procedures
EC securitymanagement product IN
Terminology
Business continuity plan keeps thebusiness runningafter a disaster
Cybercrime
criminal
Cyber
Exposure UnintentionalThreats
Fraud HumanError
Malware Environmental Hazards
Phishing Malfunctions in the computer system
Risk
social engineering
Spam
Venerability
computers underthe control
Zombie of a hacker
EC Security Requirements
Authentication whatyou do
Authorisation who you are
Auditing websitequeries
Availability
Nonrepudiation stopsusers denyingCfasely theirpurchaseetc
Technical Malware Attack Methods
Virus spreads andfor damages
Worm can replicate itself devices
many
Trojan Horse looks harmless
Cryptolocker ransomware trojan
bug
Dos Attack flooding
Botnet like a mean proxy
Malvertising internet advertising
Nontechnical methods
socialengineeringand fraud
phishing
idtheft
id fraud
DefendingInformationSystems and E Commerce
Access control encryption and PKI
in e commerce networks
Security
General controls spam popups SE
Encryption Plaintext Ciphertext encryption algorithm key keyspace
encrypt and decrypt
Symmetrickey Encryption same
key to in plaintext
Public two keys public and private Cowner
keyencryption key
also digital signatures CA's
Security in e Commerce
Firewalls
VPN's
IntrusionDetection System IDs
controls
Physical controls
Administrative Controls
Protecting Against Spam
ProtectingAgainst Phishing
Protecting Against Malvertising
ProtectingAgainst spyware
You might also like
- CYBER SECURITY HANDBOOK Part-2: Lock, Stock, and Cyber: A Comprehensive Security HandbookFrom EverandCYBER SECURITY HANDBOOK Part-2: Lock, Stock, and Cyber: A Comprehensive Security HandbookNo ratings yet
- CEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021From EverandCEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021No ratings yet
- Cryptic NoriDocument8 pagesCryptic NoriAurelian Ionel CostinNo ratings yet
- The Lady in WaitingDocument45 pagesThe Lady in WaitingNobleNo ratings yet
- E Commerce Security LawDocument19 pagesE Commerce Security LawAdnan sayedNo ratings yet
- Cybercrime: Information Security Related Security CategoriesDocument3 pagesCybercrime: Information Security Related Security CategoriesCassandra KarolinaNo ratings yet
- Knowledge Trees - Topics-List v1Document51 pagesKnowledge Trees - Topics-List v1yulianto setiawanNo ratings yet
- 4-Info Security Essentials v3.3 (LUMS)Document16 pages4-Info Security Essentials v3.3 (LUMS)MahnoorNo ratings yet
- 4-Info Security Essentials v3.3 (LUMS)Document16 pages4-Info Security Essentials v3.3 (LUMS)MahnoorNo ratings yet
- Cyber Crime Prevention and DetectionDocument4 pagesCyber Crime Prevention and DetectionJoshua AyoolaNo ratings yet
- Internet Security: Group 8Document30 pagesInternet Security: Group 8Cương NhậtNo ratings yet
- EHDFchapter 1 PPTDocument6 pagesEHDFchapter 1 PPTAhmad Raza AnsariNo ratings yet
- National Conference of CIRC On Corporate Laws-: Cybercrimes and Legal Enforcement in IndiaDocument55 pagesNational Conference of CIRC On Corporate Laws-: Cybercrimes and Legal Enforcement in IndiapshedatNo ratings yet
- Presentation 1Document11 pagesPresentation 1Harsh RavadkaNo ratings yet
- Information About Ethical HackingDocument2 pagesInformation About Ethical HackingSoham SawantNo ratings yet
- Unit 5 AND 6 - UpdatedDocument56 pagesUnit 5 AND 6 - UpdatedAsmit ShresthaNo ratings yet
- Cyber Security AwarenessDocument38 pagesCyber Security AwarenesssathesachinNo ratings yet
- Computer SecurityDocument50 pagesComputer SecuritymaxventoNo ratings yet
- Chapter 4, E Commerce Security & Payment SystemsDocument21 pagesChapter 4, E Commerce Security & Payment SystemsKnowledge HunterNo ratings yet
- Cyber CrimeDocument19 pagesCyber CrimeRishabh AggarwalNo ratings yet
- Cyber Crime Cyber Crime: Presented By: Presented byDocument30 pagesCyber Crime Cyber Crime: Presented By: Presented byVijay Kumar SinghNo ratings yet
- Introduction To Cybercrime and Security: A.Hari ChandanaDocument17 pagesIntroduction To Cybercrime and Security: A.Hari ChandanabpraveensinghNo ratings yet
- Final Cyber Security Book (2014-15)Document188 pagesFinal Cyber Security Book (2014-15)Kartik GulatiNo ratings yet
- Cyber Security Version 3Document32 pagesCyber Security Version 3Hunter CyeNo ratings yet
- Cyber Law ProjectDocument13 pagesCyber Law ProjectSagarNo ratings yet
- Cyber Security: Table of ContentsDocument75 pagesCyber Security: Table of ContentsayushNo ratings yet
- CyberDocument19 pagesCyberRajesh Kumar MaddalaNo ratings yet
- Cybersecurity Awareness Month 2021 PartnerPresentation FinalDocument24 pagesCybersecurity Awareness Month 2021 PartnerPresentation Finalpola ritzNo ratings yet
- Lesson 2 - CyberSecurity FundamentalsDocument132 pagesLesson 2 - CyberSecurity FundamentalsZozer Mbula Lwanga100% (2)
- Ciber CrimeDocument12 pagesCiber CrimeAshutosh ShuklaNo ratings yet
- Ciber CrimeDocument12 pagesCiber CrimeAshutosh Shukla100% (1)
- Chapter 8Document25 pagesChapter 8Velia MonicaNo ratings yet
- Is SecurityDocument23 pagesIs Securityashishgiri100% (3)
- Cyber Crime and SecurityDocument10 pagesCyber Crime and SecurityAvi SharmaNo ratings yet
- Cyber Security: NAME: Priyanka Sudarshan Padhi Class: T. Y. B. Com Div: C ROLL NO.: 294Document27 pagesCyber Security: NAME: Priyanka Sudarshan Padhi Class: T. Y. B. Com Div: C ROLL NO.: 294Pooja PadhiNo ratings yet
- UntitledDocument518 pagesUntitledvu psyNo ratings yet
- Cyber SecurityDocument8 pagesCyber Securitydpratik2708No ratings yet
- Foundation of Information Technology: Fatima Attari R.N. 19 (A) I.T. Sem-IIIDocument21 pagesFoundation of Information Technology: Fatima Attari R.N. 19 (A) I.T. Sem-IIIHuzefa.tarwalaNo ratings yet
- Cyber Security - Indian PerspectiveDocument29 pagesCyber Security - Indian PerspectiveSwaraj MhaskarNo ratings yet
- Cybercrime Namita MamDocument19 pagesCybercrime Namita MamEkta PaliwalNo ratings yet
- Introduction To Cybercrime and Security: Submitted To: Shivani MamDocument15 pagesIntroduction To Cybercrime and Security: Submitted To: Shivani MamManish GuptaNo ratings yet
- CyberSecurityConclaveAtVigyanBhavanDelhi 1Document66 pagesCyberSecurityConclaveAtVigyanBhavanDelhi 1Sheenal ChhabraNo ratings yet
- System Design and Analysis - Information Security and Cyber CrimeDocument29 pagesSystem Design and Analysis - Information Security and Cyber CrimeMilon MahatoNo ratings yet
- Unit 5 AND 6Document62 pagesUnit 5 AND 6Asmit ShresthaNo ratings yet
- Chapter 4, E Commerce Security & Payment SystemsDocument21 pagesChapter 4, E Commerce Security & Payment SystemsKnowledge Hunter0% (1)
- Introduction To Cyber SecurityDocument25 pagesIntroduction To Cyber Securitynaeemmarketing0508No ratings yet
- CYBERSECURITYPPTDocument23 pagesCYBERSECURITYPPTAkula SreenivasuluNo ratings yet
- Information Technology Act 2000Document36 pagesInformation Technology Act 2000api-3712367100% (7)
- Day 3: Introduction To Cyber SecurityDocument18 pagesDay 3: Introduction To Cyber SecurityAdedinewNo ratings yet
- Flyer 2023 BaliDocument1 pageFlyer 2023 BaliAmir WicaksonoNo ratings yet
- The Detail Interpretation of Ethical HackingDocument8 pagesThe Detail Interpretation of Ethical Hackingjoel enciso enekeNo ratings yet
- Cybersecurity 21 09 22Document28 pagesCybersecurity 21 09 22pyari mohanNo ratings yet
- Security in E-Commerce: Monir ArabjafariDocument59 pagesSecurity in E-Commerce: Monir ArabjafariChandra ShekarNo ratings yet
- Cyber CrimeDocument25 pagesCyber Crimermerala100% (1)
- Ch7. Securing Information Systems: Improper Use - Crimes) Change)Document3 pagesCh7. Securing Information Systems: Improper Use - Crimes) Change)karimNo ratings yet
- Faculty of Engineering, Sciences & Technology Cryptography and Data Security Assignment Instructor: Ali Ahmad SiddiquiDocument11 pagesFaculty of Engineering, Sciences & Technology Cryptography and Data Security Assignment Instructor: Ali Ahmad SiddiquiUsama AshrafNo ratings yet
- Computer CrimeDocument15 pagesComputer CrimePravina RavinaNo ratings yet
- Cyber Crime: By, Shrinidhi K.RDocument16 pagesCyber Crime: By, Shrinidhi K.RMuragesh KabbinakantimathNo ratings yet
- Ethics in Information Technology: by Prof. Vikrant CholeDocument36 pagesEthics in Information Technology: by Prof. Vikrant Cholevikrant choleNo ratings yet
- Your System's Sweetspots: CEO's Advice on Basic Cyber Security: CEO's Advice on Computer ScienceFrom EverandYour System's Sweetspots: CEO's Advice on Basic Cyber Security: CEO's Advice on Computer ScienceNo ratings yet
- E-Commerce PlatformsDocument2 pagesE-Commerce PlatformsEthan MonkhouseNo ratings yet
- Payment MethodsDocument1 pagePayment MethodsEthan MonkhouseNo ratings yet
- Blockchain in E-BusinessDocument1 pageBlockchain in E-BusinessEthan MonkhouseNo ratings yet
- Personalization and Recommender SystemsDocument3 pagesPersonalization and Recommender SystemsEthan MonkhouseNo ratings yet
- Blockchain in E-BusinessDocument1 pageBlockchain in E-BusinessEthan MonkhouseNo ratings yet
- Blockchain in E-BusinessDocument1 pageBlockchain in E-BusinessEthan MonkhouseNo ratings yet
- Blockchain in E-BusinessDocument1 pageBlockchain in E-BusinessEthan MonkhouseNo ratings yet