Professional Documents
Culture Documents
Analyzing The User Navigation Pattern From Weblogs Using Data Pre-Processing Technique
Uploaded by
Eman AlkurdiOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Analyzing The User Navigation Pattern From Weblogs Using Data Pre-Processing Technique
Uploaded by
Eman AlkurdiCopyright:
Available Formats
P.G.Vedaprakash et al, International Journal of Computer Science and Mobile Computing, Vol.5 Issue.5, May- 2016, pg.
90-99
Available Online at www.ijcsmc.com
International Journal of Computer Science and Mobile Computing
A Monthly Journal of Computer Science and Information Technology
ISSN 2320–088X
IMPACT FACTOR: 5.258
IJCSMC, Vol. 5, Issue. 5, May 2016, pg.90 – 99
ANALYZING THE USER NAVIGATION
PATTERN FROM WEBLOGS USING DATA
PRE-PROCESSING TECHNIQUE
Mr. P.G.Vedaprakash Mr. P.G.Om Prakash Mr. M.Navaneethakrishnan
M.E.Student – Department of CSE Asst.Prof - Department of CSE Asst.Prof & HOD – Department of CSE
ST.Joseph College of Engg ST.Joseph College of Engg ST.Joseph College of Engg
Chennai – 602 117. Chennai – 602 117. Chennai – 602 117.
vedaprakash1992@gmail.com ommail2004@gmail.com mnksjce@gmail.com
Abstract— In the real world, lot of users attracted towards online shopping, so lots of transactions are going on in the
websites. A weblog contains series of entries updating frequently by the user while accessing the website. Based on the user
interest, it can be classified as related and unrelated data. The related data can be considered as success response, but the
unrelated data can be considered as failure response. It analyze the pattern of user navigation while browsing, for that web
usage mining must be analyzed. The steps consisting for the process of web usage mining are data collection, pattern
discovery, and Pre-processing and pattern analysis.
Keywords— Cognitive user model, sessionization, software tool, test oracle, usability, web server log.
I. INTRODUCTION
Online shopping (sometimes known as electronic retail or e-shopping) is a form of electronic commerce which allows
consumers to buy goods or services from a seller over the internet using a web browser. Alternative names are: e-web-store-shop,
e-store, internet shop, online store, and virtual store. Mobile commerce describes about online retailers in mobile optimized online
site or app. online customers mostly use a credit card in order to make payments. Few online shops will not accept international
credit cards. Few of them requires both the purchaser‘s billing and shipping address to be in the same country. Other online
shopping allowing customers to any country to send gifts anywhere.
Customers searches the product of interest by visiting the website of the retailer directly or by searching among
alternative vendors by a shopping search engine. Once a particular product was found on the website, most of the online retailers
will chose shopping cart software to allow the consumer to accumulate multiple items and adjust quantities like filling a physical
shopping cart or basket in a conventional store. Some stores allow consumers to sign up for a permanent account usage. Less
sophisticated stores may reply on consumers to phone or e-mail their orders.
A cognitive model is an approximation to animal cognitive processes (predominantly human) for the Purposes of
comprehension and prediction. Cognitive models can be developed within or without a cognitive architecture, though the two are
not always easily distinguishable. Sessionization refers to the capture of all clickstream activity within the timeframe of a single
visitor‘s Website session. A programming tool or software development tool is a computer program that software developers use
© 2016, IJCSMC All Rights Reserved 90
P.G.Vedaprakash et al, International Journal of Computer Science and Mobile Computing, Vol.5 Issue.5, May- 2016, pg. 90-99
to create, debug, maintain, or otherwise support other programs and applications. Software testers and software engineers can use
an oracle as a mechanism for determining whether a test has passed or failed. In Software engineering, usability is the degree to
which a software can be used by specified consumers to achieve quantified objectives with effectiveness, efficiency, and
satisfaction in a quantified context of use. A server log is a log file (or several files) automatically created and maintained by
a server consisting of a list of activities it performed. A typical example is a web server log which maintains a history of page
requests.
Online customers must access the internet and a valid method of payment to complete the transactions. Generally higher
levels of education and personal income correspond to more favorable perceptions of online shopping. Increased exposure to
technology also increase the probability of developing favorable attitudes towards new online purchasing. Customers are attracted
to online shopping not only because of high levels of convenience, but also because of border selections, competitive pricing and
greater access to information. Business organizations seeks to offer online shopping not only because it is lower cost compared to
bricks and mortar stores, but also it offers a worldwide market, increases customer value, and builds sustainable capabilities.
Designers of online shop are carrying the effects of information load. Information load is the product of spatial and
temporal arrangements in web store. Comparing with conventional retail shopping, it provides additional product information
such as comparative products and services, with various alternatives and attributes. Two major dimensions of information load are
complexity and novelty. Complexity means number of different elements or features of a site, the result of increased information
diversity. Novelty means the unexpected, suppressed, new or unfamiliar aspects of the site.
A successful web store is not a good looking website with dynamic technical features, listed in many search engines.
Business often attempts to adopt online shopping techniques without understanding them without a sound business model.
Business produce web stores meets organizations culture and brand name without satisfying consumer expectations. User-
centered design is critical and complex. Understanding the customer needs is essential. Living in company‘s promises gives
customers a reason to come back and meeting their expectations. It is important that the website communicate how much the
company values to customers.
Customer needs and expectations are not equal for all customers. Age, gender, experience and culture are all important
factors for online shopping. Users with online experience focus more on the variables that directly influence the task, while other
users focus on understanding the information. To increase online purchases, businesses will be using significant time and money
to define, design, develop, test, implement and maintain the web store. It is to eliminate mistakes and more appealing to online
shoppers, many web shop designers study research on consumer expectations.
II. RELATED WORK
Matthias Rauterberg suggested that ―To support the human factors engineer in designing a good user interface, a method
has been developed to analyze the empirical Oataófttre interactive user behavior traced in a finite discrete state space. The
sequence of actions produced by user contain valuable information about the mental model of their, the individual problem
solution strategies for given task and the hierarchical structure of the task--sub tasks relationships. The presented method,
AMME, can analyze the action sequences and automatically generate (l) a net description of the task dependent model of the user,
(2) a state transition matrix, and (3) various quantitative measures of the user's task solving process. The behavioral complexity of
task-solving processes carried out by novices has been found to be significant than the complexity of task-solving processes
carried out by experts‖.
Michigan and Ann Arbor discovered that ―Weblog are analyses for the way of IT administrators to ensure adequate
bandwidth and server capacity on organizational web sites. In the past five years, Log file analysis has advanced with
companies; now mining files are fine-grained detail about visitor profiles and buying activity. Organizations are now seeks to
use log files to learn about the usability of web sites—that is, successful visitor meets their specific information or transaction
goals. Log file data can offer valuable insight into web site usage. It reflecting actual usage in natural working condition
compared to artificial settings of a usability lab. It represents activity of many users, over potentially long period of time visited
to a limited number of users for an hour or two each‖.
Linda Tauscher and Saul Greenberg discovered that ―We report on users‘ revisitation patterns to World Wide Web
pages, and empirical foundation for the design of history mechanisms in web browsers. Through history, it returns to visited
page by reducing the cognitive and physical overhead required to navigate for scratch. People tends to revisit pages for accessing
web pages frequently, browse in very small clusters of pages, and generates short sequences of URL paths. We compared
different history mechanisms, and found the stack-based prediction method prevalent in commercial browsers is inferior to
simpler approach of recently visited URLs with duplicates removed.
Fabio Paterno and TonioCarta discovered that ―Usability evaluation of Web sites is time consuming task performed
manually. It presents a tool that supports remote usability evaluation of Web sites. It supports client-side data's on user
interactions and JavaScript events. Moreover, the definition of custom events giving evaluates the flexibility to add specific
events to detected and considered for evaluation. The tool supports the Web site by exploiting a proxy-based architecture and
enables the evaluator to perform actual user behavior and an optimal sequence of actions‖.
© 2016, IJCSMC All Rights Reserved 91
P.G.Vedaprakash et al, International Journal of Computer Science and Mobile Computing, Vol.5 Issue.5, May- 2016, pg. 90-99
Jeff Tian, SunitaRudraraju and Zhao Li discovered that ―Based on the characteristics of web applications and web
environment, we classified web problems and focus on the subset of source content problems. Using information about web
accesses, we derived various measurements of web site workload at different levels of granularity and various perspectives. The
workload measures combined with failure information extracted from recorded errors. It evaluates the operational reliability for
source contents at potential for reliability improvement. The given results demonstrates the viability and effectiveness of our
approach‖.
Marcus Heinath, Jeronimo Dzaack, Andre Wiesner discovered that ―Usability of complex dynamic human computer
interfaces can be evaluated by cognitive modeling for their underlying structures. Even though the prediction of human behavior
can check the detective errors in interaction design and cognitive demands of the future. HTAmap, a high-level framework for
cognitive modeling, it aims to reduce the modeling effort. Within HTAmap the cognitive models transformed into pattern-
oriented model. This paper describes both concepts and first implementations. Both tools was shown using an example of
process control‖.
III. SYSTEM ARCHITECTURE
In system architecture, the user will browse the website for online shopping. After accessing the website, they sends
request to Web server and web server sends the response to web browser (HTTP request and HTTP response).The hypertext
transfer protocol (HTTP), it is an application protocol for distributed, collaborative, hypermedia information systems (Fig 1.1).
Hypertext is a structured text that uses logical links between nodes containing text. The series of entries between web browser
and web server is stored in weblogs. Weblog is a raw log using this pre-processing technique will be activated.
Fig 1.1
Online shopping is a form of electronic commerce it allows consumers to buy goods or services from a seller over
internet using web browser. Some online shops will not accept international credit cards. Few of them require both the purchaser
billing and shipping address to be in the same country. Other online shops allow customer‘s from any country to send gifts
anywhere. Online customers must access the internet and a valid method of payment to complete the transactions. Generally
higher levels of education and personal income corresponds to more favorable perception of online shopping (Fig 1.1). Increased
exposure to technology also increase the probability of developing favorable attitudes towards new online purchasing.
The new method to identify navigation related usability problems by comparing Web usage patterns extracted from
server logs against anticipated usage represented in some cognitive user models. It includes three major modules: They are: Usage
Pattern Extraction, Internet Usage for Information Provisioning (IUIP) Modeling, and Usability Problem Identification. First, it
extracts actual navigation paths from server logs and discover patterns for typical events. In parallel, it will construct IUIP models
for the same events. IUIP models are cognition of user behavior and it can represent anticipated paths for specific user-oriented
tasks. The result checking employees the mechanism of test oracle. An oracle is generally used to test that passed or failed. Here,
we use IUIP models as the oracle to identify the usability issues related to the users‘ actual navigation paths by analyzing the
deviations between the two.
© 2016, IJCSMC All Rights Reserved 92
P.G.Vedaprakash et al, International Journal of Computer Science and Mobile Computing, Vol.5 Issue.5, May- 2016, pg. 90-99
IV. DESCRIPTION METHOD
Implementation is the theoretical design is turned out into a working system .Each entry in a log contains the IP address
of the originating host, time stamp, requested Web page, referrer, user agent and other data. Typically, the raw data need to be
Pre-processed and converted into user sessions and transactions to extract usage patterns.
A. Log generation
In log generation module, the user searches the query and that hits the server as http request and server responds back to
the user as http response. Those http request and response is considered as web logs. The prepared raw weblog dataset contains
null values and unwanted datasets. Pre-processing technique is used to remove the null values in web search log dataset (Fig 1.2).
After the preprocessing process is completed, it will be moved on to Pattern generation module. In pattern generation, single
customer details will be covered. And then it can be classified into three categories: Frequent, semi-frequent and in-frequent.
Clearing denotes all activities from the time a commitment is made for a transaction until it is settled. Clearing of payments is
necessary to turn the promise of payment into actual movement of money from one bank to another.
Fig 1.2
In this phase, the application of web log data may need to be cleaned from entries such as pages that returned an error or
graphic file accesses. In such cases few information might be useful, but in other such data should be eliminated from log file.
Therefore, crawler activity can be filtered out, because such entries not provide information about the site‘s usability. Another
problem is too met with caching. Cached pages are not recorded in the web log. Caching is heavily depending on the client-side
technologies. Therefore cannot be deal with easily.
B. Weblogs
A weblog that consists of a series of entries updated on frequently with existing information. The information can be
written by the site owner, or other sources, or contributed by users. Generally, weblogs are usually of topical interest, and, in
general, it can be thought of as developing commentaries, individual or collective on their particular themes (Fig 1.3). A weblog
consists of the recorded ideas of an individual (a sort of diary) or be a complex collaboration .Since there are a number of
variation on this idea can be easily invented, the meaning of this term is to gather additional connotations with time.
© 2016, IJCSMC All Rights Reserved 93
P.G.Vedaprakash et al, International Journal of Computer Science and Mobile Computing, Vol.5 Issue.5, May- 2016, pg. 90-99
Fig 1.3
A weblog is an informational site published on the World Wide Web consisting of discrete entries ("posts") typically
displayed in the most recent post appears first. Weblogs were usually work in single individual group. Recently, "multi-author
blogs" have introduced with posts written by large numbers of authors and professionally edited. It is from newspapers, other
media outlets, universities, think tanks, advocacy groups and similar institutions account for increasing quantity of blog traffic.
C. Logs Preprocessing
The data preparation and preprocessing includes the following domain-dependent tasks.
1) Data cleaning: This task is usually site-specific and removing extraneous references to style files, graphics, or sound files
that may not be important for the purpose of analysis.
2) User identification: The remaining entries are grouped by individual users. Because no user authentication and cookie
information is available in most server logs, we used the combination of IP, user agent, and referrer fields to identify unique
users.
3) User session identification: The activity record of each user is segmented into sessions, with each representing a single
visit to a site. Without additional authentication information from users and without the mechanisms such as embedded
session IDs, one must rely on heuristics for session identification. For example, set an elapse time of 15 minutes between
two successive page accesses as a threshold to partition a user activity record into different sessions (Fig 1.4).
4) Path completion: Client or proxy side caching can often result in missing access references to some pages that have been
cached. These missing references can often be heuristically inferred from the knowledge of site topology and referrer
information, along with temporal information from server logs.
Fig 1.4
D. Pattern Generation Module
In Pattern Generation, analyzing the web log files through web usage mining is very important to discover the similar
behavior users of particular website. Our paper discusses how to find useful knowledge from web log file using some data mining
technique like Association rule mining and clustering. First we pre-process the web log file then apply association rule mining and
© 2016, IJCSMC All Rights Reserved 94
P.G.Vedaprakash et al, International Journal of Computer Science and Mobile Computing, Vol.5 Issue.5, May- 2016, pg. 90-99
clustering algorithm on web log file to discover usage pattern and same behavioral users. Classification consists of predicting a
certain outcome. In order to predict the outcome, the algorithm processes a training set containing a set of attributes and outcome
called goal or prediction attribute (Fig 1.5). The algorithm tries to discover the relationship between attributes would make it
possible to predict the outcome.
Fig 1.5
Classification consists of predicting a certain outcome based on given input. In order to predict the outcome, the
algorithm processes a training set with attributes and the respective outcome, also called goal or prediction attribute. The
algorithm tries to discover the relationship between the attributes makes it possible to predict the outcome. Classification consists
of Supervised and Unsupervised. Supervised Classification- Set of possible classes is known in advance. Unsupervised
Classification- Set of possible classes is not known. It is also called clustering.
E. Pattern Analysis
Web usage mining has many advantages which makes the technology attractive to corporations including the
government agencies. This technology has personalized marketing, which eventually results in higher trade volumes.
Government agencies are classified its threats and fight against terrorism. The predicting capability of mining applications can
identifying criminal activities. The companies can establish its own customer relationship by giving them exactly what they
need.
The companies can find, attract and retain customers depends on saving the production costs by utilizing the acquired
insight of customer's requirement. They can increases the profit by targeting price based on the profiles created. They can even
finds the customer who might find the default to a competitor the company will try to retain the customer by providing
promotional offers to the specific customers, thus reducing the risk of losing a customer or customers.
We adapted the tire algorithm to construct a tree structure that also captures user visit frequencies, which is called a trail
tree in our work. In a trail tree, a complete path from the root to a leaf node is called a trail. Each node corresponds to the
occurrence of a specific page in a transaction. It is annotated with the number of users having reached the node across the same
trail prefix (Fig 1.6).
Clustering is classified into three types:
1) Structure-based Clustering - Clustering result based on vertex connectivity. They are closely connected; e.g. half work on
XML and the other half work on Skyline in one of the cluster.
2) Attribute-based Clustering - Clustering results based on attribute similarity. Within clusters work on the same topics, however,
the relationship may be lost due to the partitioning so that author are quite isolated in one of the clusters.
3) Structure/Attribute Clustering - Clustering results based on both structure and attribute similarities. Within one cluster are
closely connected, meanwhile, they are homogeneous on research topics.
© 2016, IJCSMC All Rights Reserved 95
P.G.Vedaprakash et al, International Journal of Computer Science and Mobile Computing, Vol.5 Issue.5, May- 2016, pg. 90-99
Fig 1.6
F. Identify the user Behavior
In graph modeling, the Web usage mining and statistical analysis are the two ways to evaluate usage of Web site. Web
usage mining and statistical analysis considers client side data. In other words, it combines graph based Web usage mining and
browsing time analysis while taking client side data into account. It helps us to reconstruct user session exactly by based on these
data, we find Web usage patterns with more accuracy.
Some non-digital products have been more successful than others for online storage. Profitable items have a high value-
to-weight ratio, they involve embarrassing purchases, and typically go to people in remote locations, and they may have shut-ins
as their typical purchasers. Items can fit in a standard mailbox—such as music CD's, DVDs and books—are particularly suitable
for a virtual marketer (Fig 1.7).
Based on the ranking process classify the weblog data-set into frequent and infrequent item set. Here, frequent item set
indicates the user navigation. Then, forward the frequent item set and navigation to the respected user. This the procedure where
information stored in web server logs is processed by data mining techniques in order to,
1) Extract information and discover interesting usage patterns.
2) Cluster the users into groups according to their navigation behavior.
3) Discover potential correlation between web pages and user groups.
The process of extracting information concerns the browsing behavior of users can be regarded as part of the user
profiling process. It is evident that the user profiling and web usage modules overlap. In many cases information provides many
web site is not physically stored in the web site‘s server. In case of a web portal, users are interested in information from various
web sources. The web site editors are the contents of interest should consequently be classified into two categories. Searching
and relevance ranking techniques are employed in the process of acquisition of relevant information and in the publishing of the
appropriate data to each group of users.
Fig 1.7
Our IUIP models are based on the cognitive models surveyed in the Adaptive Control of Thought—Rational (ACT-R)
model. Due to the complexity of ACT-R model development and the low-level rule based programming language and
constructed our own cognitive architecture and supporting tool based on the ideas from ACT-R.
© 2016, IJCSMC All Rights Reserved 96
P.G.Vedaprakash et al, International Journal of Computer Science and Mobile Computing, Vol.5 Issue.5, May- 2016, pg. 90-99
V. SNAPSHOTS
A. ADMIN FORM
The admin form is used to view the Products. The registered users can see the various Products in On-line shopping.
While showing the user have to login the website; based on the user interest, it can be classified as related and unrelated data.
B. PRE-PROCESSING
The data preprocessing includes Data cleaning, User identification, User session identification and Path completion. The
user will see the products ‗n‘ number of times. It will be stored in weblogs; through the weblogs preprocessing will be prepared.
The administrator will show the single user weblog in pre-processing module.
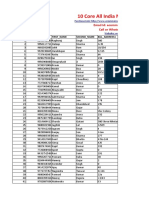
C. PATTERN GENERATION
It generates the various models of online shopping in pre-processing technique. Due to user satisfacion they will chose
the various models of products in pattern generation module. The various company likes motorola , samsug , sony , onida , etc. In
which due to user interest classified into success response and failure response. The related data can be considered as success
response and unrelated data can be considered as failure response.
© 2016, IJCSMC All Rights Reserved 97
P.G.Vedaprakash et al, International Journal of Computer Science and Mobile Computing, Vol.5 Issue.5, May- 2016, pg. 90-99
D. PATTERN ANALYSIS
In pattern analysis, it shows the user‘s selected products. In that various categories like brands, memory, size and cost.
Depends upon user satisfaction they will prefer best models. The admin will send the proper information to the concern user
through message or mail. Then the admin will maintain the specific graph or bar chart through that website.
E. IDENTIFY USER BEHAVIOR
In graph modeling, the Web usage mining and statistical analysis are the two ways to evaluate usage of Web site. The various
products of mobiles in pie chart shown below.
VI. CONCLUSION AND FUTURE WORK
The extraction of related information from web browser is identified the frequent and semi-frequent customers for
online-shopping.Using this type of information, users will save time management and quality products. In future, Web usage
mining is the base for navigation pattern mining and approach of clustering is used to perform that Mining, usage mining deals
with the discovery and analysis of usage patterns from Web data, specifically web logs, in order to improve web based
applications and also to improve the customer relationship management. I would like to conduct more comprehensive
experiments to further verify my approach and improve upon it.
© 2016, IJCSMC All Rights Reserved 98
P.G.Vedaprakash et al, International Journal of Computer Science and Mobile Computing, Vol.5 Issue.5, May- 2016, pg. 90-99
REFERENCES
1. A. McDonald and R. Welland, ―Web engineering in practice, in Proc. 10th Int. World Wide Web Conf., May 2001, pp.
21–30.
2. M. Rauterberg, ―AMME: An automatic mental model evaluation to analyse user behaviour traced in a finite, discrete
state space, Ergonomics, vol. 36, no. 11, pp. 1369–1380, 1993.
3. P. M. Sanderson and C. Fisher, ―Exploratory sequential data analysis: Foundations, Human–Comput. Interaction, vol.
9, nos. 3/4, pp. 251–317, 1994.
4. L. Tauscher and S. Greenberg, ―Revisitation patterns in World Wide Web navigation, in Proc. ACM SIGCHI Conf.
Human Factors Comput. Syst., New York, NY, USA, 1997, pp. 399– 406.
5. G. Christou, F. E. Ritter, and R. J. Jacob, ―CODEIN—A new notation for GOMS to handle evaluations of reality-based
interaction style interfaces, Int. J. Human-Comput. Interaction, vol. 28, no. 3, pp. 189–201, 2012.
6. Tec-Ed, ―Assessing web site usability from server log files, White Paper, Tec-Ed, 1999.
7. T. Arce, P. E. Roman,´ J. D. Velasquez,´ and V. Parada, ―Identifying web sessions with simulated annealing, Expert Syst.
Appl., vol. 41, no. 4 , pp. 1593–1600, 2014.
8. M. Heinath, J. Dzaack, and A. Wiesner, ―Simplifying the development and the analysis of cognitive models,‖ in Proc.
Eur. Cognitive Sci. Conf., Delphi, Greece, 2007, pp. 446–451.
9. F. E. Ritter, A. R. Freed, and O. L. Haskett, ―Discovering user information needs: The case of university department web
sites,‖ ACM Interactions, vol. 12, no. 5, pp. 19–27, 2005.
10. J. S. Valacich, D. V. Parboteeah, and J. D. Wells, ―The online consumer‘s hierarchy of needs,‖ Comm. ACM, vol. 50,
no. 9, pp. 84–90, Sep. 2007.
© 2016, IJCSMC All Rights Reserved 99
You might also like
- ETCW18Document7 pagesETCW18Editor IJAERDNo ratings yet
- Research Papers On Web Usage MiningDocument4 pagesResearch Papers On Web Usage Miningfvf66j19100% (1)
- Ijarcce 2023 124187Document5 pagesIjarcce 2023 124187JonathanNo ratings yet
- AbstractDocument10 pagesAbstractAmbuj JoshiNo ratings yet
- Project Report LsiDocument54 pagesProject Report LsiTejaswini GadekarNo ratings yet
- Web Usage Mining Research Papers 2014Document6 pagesWeb Usage Mining Research Papers 2014ggteukwhf100% (1)
- Sentimental Analysis of Amazon Reviews Using NaiveDocument11 pagesSentimental Analysis of Amazon Reviews Using NaiveANJALI DEORENo ratings yet
- Build Online Shop HtmlDocument10 pagesBuild Online Shop HtmlReagan LuckyNo ratings yet
- Online Shopping System Thesis DocumentationDocument5 pagesOnline Shopping System Thesis Documentationafkogftet100% (1)
- A Study of Application of Web Mining For E-Commerce: Tools and MethodologyDocument14 pagesA Study of Application of Web Mining For E-Commerce: Tools and MethodologyAnonymous gUySMcpSqNo ratings yet
- A Project Report On Web ShoppingDocument82 pagesA Project Report On Web ShoppingManish Negi100% (1)
- IJRTI2305089Document4 pagesIJRTI2305089Abhinav SureshNo ratings yet
- Online Shopping Application For Local Vendors.Document6 pagesOnline Shopping Application For Local Vendors.International Journal Of Emerging Technology and Computer ScienceNo ratings yet
- Ijcet: International Journal of Computer Engineering & Technology (Ijcet)Document7 pagesIjcet: International Journal of Computer Engineering & Technology (Ijcet)IAEME PublicationNo ratings yet
- Webdev-Research (Revised)Document38 pagesWebdev-Research (Revised)Sheena Dominica MorcosoNo ratings yet
- Report On StationaryDocument5 pagesReport On StationaryM.Basit RahimNo ratings yet
- Web Usage Mining Research Papers 2012Document6 pagesWeb Usage Mining Research Papers 2012c9rvcwhf100% (1)
- Consumer Perception Towards Online MarketingDocument14 pagesConsumer Perception Towards Online MarketingBRC POLURNo ratings yet
- Consumer Behavior Analytics Using Machine Learning AlgorithmsDocument3 pagesConsumer Behavior Analytics Using Machine Learning AlgorithmsAbdul RazzakNo ratings yet
- Thesis On Web Log MiningDocument8 pagesThesis On Web Log Mininghannahcarpenterspringfield100% (2)
- Literature Review On Online Shopping SystemDocument9 pagesLiterature Review On Online Shopping Systemauhavmpif100% (1)
- Developing An E-Commerce Web Application With ReactJS and FirebaseDocument6 pagesDeveloping An E-Commerce Web Application With ReactJS and FirebaseIJRASETPublicationsNo ratings yet
- A Review On E-Commerce Price Evaluation SystemDocument6 pagesA Review On E-Commerce Price Evaluation SystemIJRASETPublicationsNo ratings yet
- Website Evaluation Using Opinion Mining Jennifer E. TayagDocument8 pagesWebsite Evaluation Using Opinion Mining Jennifer E. TayagJes RamosNo ratings yet
- Project Report: Submitted in Partial Fulfillment of The Degree of Masters of Business Administration Session (2016-2017)Document69 pagesProject Report: Submitted in Partial Fulfillment of The Degree of Masters of Business Administration Session (2016-2017)Shahrukh Khan100% (1)
- Mca,Bca Project List 2023-2024Document90 pagesMca,Bca Project List 2023-2024rithu28021975No ratings yet
- Final ReportDocument38 pagesFinal Reportkocene9432No ratings yet
- Online Shop System ThesisDocument4 pagesOnline Shop System Thesisafkogftet100% (1)
- A Comprehensive Analysis of Consumer Decisions On Twitter Dataset Using Machine Learning AlgorithmsDocument9 pagesA Comprehensive Analysis of Consumer Decisions On Twitter Dataset Using Machine Learning AlgorithmsIAES IJAINo ratings yet
- Cluster Optimization For Improved Web Usage MiningDocument6 pagesCluster Optimization For Improved Web Usage MiningEditor IJRITCCNo ratings yet
- A Report On E-BusinessDocument65 pagesA Report On E-Businesssmartway projectsNo ratings yet
- Recommendation With Data Mining Algorithms For E-Commerce and M-Commerce ApplicationsDocument4 pagesRecommendation With Data Mining Algorithms For E-Commerce and M-Commerce ApplicationsInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- A Novel Technique To Predict Oftenly Used Web Pages From Usage PatternsDocument7 pagesA Novel Technique To Predict Oftenly Used Web Pages From Usage PatternsInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Artificial Neural Network Approach For Student S Behavior AnalysisDocument5 pagesArtificial Neural Network Approach For Student S Behavior AnalysisAnkit SoniNo ratings yet
- Price Comparison For Online ShoppingDocument4 pagesPrice Comparison For Online ShoppingInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- E-Commerce Website Publication PaperDocument9 pagesE-Commerce Website Publication PaperSoham Shrikant manjrekarNo ratings yet
- Piyush ThesiesDocument79 pagesPiyush ThesiesskkNo ratings yet
- Rubrics 1Document13 pagesRubrics 1HimanshuNo ratings yet
- Online Grocery Management System Recommendation EngineDocument6 pagesOnline Grocery Management System Recommendation EngineSuhel AhmedNo ratings yet
- Rubrics 2Document23 pagesRubrics 2HimanshuNo ratings yet
- An E-Commerce Decision Support System Design For Web Customer RetentionDocument7 pagesAn E-Commerce Decision Support System Design For Web Customer RetentionTho TranNo ratings yet
- Opinion MiningDocument7 pagesOpinion MiningMohit SnggNo ratings yet
- Fake Product Review Monitoring SystemDocument7 pagesFake Product Review Monitoring SystemIJRASETPublicationsNo ratings yet
- V - Total CafeteriaDocument13 pagesV - Total CafeteriaIJRASETPublicationsNo ratings yet
- Customer Sentiment Based Online Grocery Recommendation EngineDocument6 pagesCustomer Sentiment Based Online Grocery Recommendation EngineInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Online Shopping: Ccs University MeerutDocument11 pagesOnline Shopping: Ccs University Meerutsaikripa121No ratings yet
- Online Grocery Management System 3Document6 pagesOnline Grocery Management System 3karandesaurabh0901No ratings yet
- Relevancy Based Content Search in Semantic WebDocument2 pagesRelevancy Based Content Search in Semantic WebInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Reservation System Literature ReviewDocument5 pagesReservation System Literature Reviewjylavupovip2100% (1)
- IJRPR5223Document4 pagesIJRPR5223Aditya RajNo ratings yet
- Recent Research Paper On Web Usage MiningDocument4 pagesRecent Research Paper On Web Usage Miningtuigauund100% (1)
- The Effects of Online Shopping On The Customer LoyDocument10 pagesThe Effects of Online Shopping On The Customer LoyjothishNo ratings yet
- E-commerce Influence on Customer Buying BehaviourDocument8 pagesE-commerce Influence on Customer Buying BehaviourLeigh018No ratings yet
- Personalized Web Page Recommendation Using OntologyDocument6 pagesPersonalized Web Page Recommendation Using OntologyEditor IJRITCCNo ratings yet
- Analyzing Target Customer Behavior Using Data Mining Techniques For E-Commerce DataDocument4 pagesAnalyzing Target Customer Behavior Using Data Mining Techniques For E-Commerce Dataashish88bhardwaj_314No ratings yet
- Opinion Mining and Review Spam Detection: Issues and ChallengesDocument8 pagesOpinion Mining and Review Spam Detection: Issues and Challengesvivekgandhi7k7No ratings yet
- Evaluating Rakuten Indonesia Website with Eyetracking Usability TestingDocument9 pagesEvaluating Rakuten Indonesia Website with Eyetracking Usability TestingRizky AgungNo ratings yet
- Proposal On Online Shopping PDFDocument20 pagesProposal On Online Shopping PDFBekin Joc88% (8)
- DGS IA: Inquiry Process Document (IPD)Document5 pagesDGS IA: Inquiry Process Document (IPD)Hanani IzzahNo ratings yet
- Compositional Learning of Image-Text Query For Image RetrievalDocument9 pagesCompositional Learning of Image-Text Query For Image RetrievalEman AlkurdiNo ratings yet
- Metaseek: A Content-Based Meta-Search Engine For ImagesDocument11 pagesMetaseek: A Content-Based Meta-Search Engine For ImagesEman AlkurdiNo ratings yet
- Accelerating The Whirlpool Hash Function Using ParDocument17 pagesAccelerating The Whirlpool Hash Function Using ParEman AlkurdiNo ratings yet
- Utilizing Visual Information To Search Relevant Images Using Content-Based Image Retrieval (CBIR) SystemDocument8 pagesUtilizing Visual Information To Search Relevant Images Using Content-Based Image Retrieval (CBIR) SystemEman AlkurdiNo ratings yet
- Content-Based Image Retrieval Using Color Difference Histogram in Image TexturesDocument6 pagesContent-Based Image Retrieval Using Color Difference Histogram in Image TexturesEman AlkurdiNo ratings yet
- Pyretri: A Pytorch-Based Library For Unsupervised Image Retrieval by Deep Convolutional Neural NetworksDocument4 pagesPyretri: A Pytorch-Based Library For Unsupervised Image Retrieval by Deep Convolutional Neural NetworksEman AlkurdiNo ratings yet
- Using Rc4 and Whirlpool For The Encryption and Validation of Data in IotDocument4 pagesUsing Rc4 and Whirlpool For The Encryption and Validation of Data in IotEman AlkurdiNo ratings yet
- Information Retrieval and The Semantic WebDocument3 pagesInformation Retrieval and The Semantic WebEman AlkurdiNo ratings yet
- The W Hashing FunctionDocument20 pagesThe W Hashing FunctionSri Chandan KalavapudiNo ratings yet
- A5Document6 pagesA5Anonymous 2WKRBqFlf100% (1)
- The Whirlpool Secure Hash Function: William StallingsDocument15 pagesThe Whirlpool Secure Hash Function: William StallingsEman AlkurdiNo ratings yet
- Reusing Black Box Test Paths for White Box Testing of WebsitesDocument6 pagesReusing Black Box Test Paths for White Box Testing of WebsitesEman AlkurdiNo ratings yet
- A5Document6 pagesA5Anonymous 2WKRBqFlf100% (1)
- A Family of Experiments To Assess The Impact of Page Object Pattern in Web Test Suite DevelopmentDocument11 pagesA Family of Experiments To Assess The Impact of Page Object Pattern in Web Test Suite DevelopmentEman AlkurdiNo ratings yet
- Can We Measure Software Testing Effectiveness?: of of 10012Document8 pagesCan We Measure Software Testing Effectiveness?: of of 10012Eman AlkurdiNo ratings yet
- Research Article: Lessons Learnt From Gauging Software Metrics of Cabin Software in A Commercial AirlinerDocument12 pagesResearch Article: Lessons Learnt From Gauging Software Metrics of Cabin Software in A Commercial AirlinerEman AlkurdiNo ratings yet
- Applying Halstead Software Science On Different Programming Languages For Analyzing Software ComplexityDocument5 pagesApplying Halstead Software Science On Different Programming Languages For Analyzing Software ComplexityEman AlkurdiNo ratings yet
- Halstead Metric For Quality Measurement of Various Version of StatcatoDocument5 pagesHalstead Metric For Quality Measurement of Various Version of StatcatoEman AlkurdiNo ratings yet
- Halstead Metric For Quality Measurement of Various Version of StatcatoDocument5 pagesHalstead Metric For Quality Measurement of Various Version of StatcatoEman AlkurdiNo ratings yet
- Dynamic Code Coverage Metrics: A Lognormal Perspective: Swapna S. Gokhale Robert E. MullenDocument10 pagesDynamic Code Coverage Metrics: A Lognormal Perspective: Swapna S. Gokhale Robert E. MullenEman AlkurdiNo ratings yet
- Repairing Selenium Test Cases: An Industrial Case Study About Web Page Element LocalizationDocument2 pagesRepairing Selenium Test Cases: An Industrial Case Study About Web Page Element LocalizationEman AlkurdiNo ratings yet
- Halstead Metric For Quality Measurement of Various Version of StatcatoDocument5 pagesHalstead Metric For Quality Measurement of Various Version of StatcatoEman AlkurdiNo ratings yet
- Surviving A Zombie ApocalypseDocument4 pagesSurviving A Zombie ApocalypseSarah SmithNo ratings yet
- Personal Development PlanDocument10 pagesPersonal Development PlanNg Thị Kh ThiệnNo ratings yet
- Lembar Jawaban Skillab Evidence Based Edicine (Ebm) : Parameter Rerata SD RERATA+2sd Nilai AbnormalitasDocument26 pagesLembar Jawaban Skillab Evidence Based Edicine (Ebm) : Parameter Rerata SD RERATA+2sd Nilai Abnormalitassisil muntheNo ratings yet
- Wiley Soalan 6Document3 pagesWiley Soalan 6Rozita Abdullah SaniNo ratings yet
- UNILAG POSTGRADUATE ENTRANCE EXAMDocument12 pagesUNILAG POSTGRADUATE ENTRANCE EXAMTemitayoNo ratings yet
- Topic 1 - Introduction To Technical AnalysisDocument11 pagesTopic 1 - Introduction To Technical AnalysisZatch Series UnlimitedNo ratings yet
- AOE 5104 Class Notes and ScheduleDocument26 pagesAOE 5104 Class Notes and ScheduleverbicarNo ratings yet
- Pasyon and RevolutionDocument2 pagesPasyon and RevolutionBilly JoeNo ratings yet
- Techniques in Neuroanatomical ResearchDocument404 pagesTechniques in Neuroanatomical ResearchVlad TomaNo ratings yet
- 2006 Arawak Languages Encyclopedia of Language and LinguisticsDocument4 pages2006 Arawak Languages Encyclopedia of Language and LinguisticsSheldon JungleNo ratings yet
- United States Patent (19) : (52) U.S. C.260/583 KDocument5 pagesUnited States Patent (19) : (52) U.S. C.260/583 KkurniawanNo ratings yet
- Dr. Kirti MatliwalaDocument6 pagesDr. Kirti MatliwalaKirti Dakshesh ThakarNo ratings yet
- Tle Fos 9 11 q1 WK 7 d1Document6 pagesTle Fos 9 11 q1 WK 7 d1REYMOND SUMAYLONo ratings yet
- Karma Connection in Marriage PDFDocument27 pagesKarma Connection in Marriage PDFAavesh TapdeNo ratings yet
- Transforming Enterprises Through Diversity and Inclusion - ILODocument124 pagesTransforming Enterprises Through Diversity and Inclusion - ILODaniela GalvisNo ratings yet
- 1 Calimutan v. People - G.R. No. 152133Document1 page1 Calimutan v. People - G.R. No. 152133eiram23100% (1)
- Boston University Student Research: Zipcar, IncDocument28 pagesBoston University Student Research: Zipcar, Incforeverjessx3No ratings yet
- HF7E16HKEHDocument9 pagesHF7E16HKEHMarc Gerald TorresNo ratings yet
- 2 - PaintingDocument26 pages2 - PaintingELLEN MASMODINo ratings yet
- Tawassulan Fik TjakrabuanaDocument6 pagesTawassulan Fik TjakrabuanafikditasresNo ratings yet
- Oracle 1z0-986 Exam: Implementation EssentialsDocument23 pagesOracle 1z0-986 Exam: Implementation Essentialslakshmanan84No ratings yet
- Transits of The Year 2008: Text by Robert HandDocument27 pagesTransits of The Year 2008: Text by Robert HandjasminnexNo ratings yet
- The Great GatsbyDocument23 pagesThe Great Gatsbychia simNo ratings yet
- 5 All India Mobile Database SampleDocument15 pages5 All India Mobile Database Sampleali khan Saifi100% (1)
- (Appendix C-02) COT-RPMS Rating Sheet For T I-III For SY 2022-2023Document1 page(Appendix C-02) COT-RPMS Rating Sheet For T I-III For SY 2022-2023Michelle Tamayo TimadoNo ratings yet
- Bagi Latihan Soal 3Document3 pagesBagi Latihan Soal 3MUH LULU BNo ratings yet
- Benjamin Joel - American Grandmaster. Four Decades of Chess Adventures, 2007-OCR, Everyman, 270p PDFDocument270 pagesBenjamin Joel - American Grandmaster. Four Decades of Chess Adventures, 2007-OCR, Everyman, 270p PDFGabriel Henrique100% (1)
- Unit 5 Math-Parent Letter-4th GradeDocument4 pagesUnit 5 Math-Parent Letter-4th Gradeapi-346081420No ratings yet
- Voh Sham Kuch Ajeeb Thi - A Brother Sister Saga (HindiDocument403 pagesVoh Sham Kuch Ajeeb Thi - A Brother Sister Saga (HindiDesi Rocks100% (1)
- Bukhari Commentary Vol 2Document493 pagesBukhari Commentary Vol 2mhasnathNo ratings yet