Professional Documents
Culture Documents
Foundations of Computer Security: Lecture 49: Public Key Encryption II
Uploaded by
Mc Robinson Regucera0 ratings0% found this document useful (0 votes)
12 views6 pagesOriginal Title
lecture14
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
12 views6 pagesFoundations of Computer Security: Lecture 49: Public Key Encryption II
Uploaded by
Mc Robinson ReguceraCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 6
Foundations of Computer Security
Lecture 49: Public Key Encryption II
Dr. Bill Young
Department of Computer Sciences
University of Texas at Austin
Lecture 49: 1 Public Key Encryption II
RSA Algorithm
The Rivest-Shamir-Adelman (RSA) algorithm relies on the
difficulty of factoring large numbers.
Two keys, e and d, are used for encryption and decryption. The
algorithm is such that:
{{P}d }e = P = {{P}e }d .
A plaintext block P is encrypted as (P e mod n). d is chosen so
that:
(P e )d mod n = P.
An interceptor would have to factor P e to recover the plaintext.
The legitimate receiver knows d and merely computes
(P e )d mod n = P, which is much easier.
Lecture 49: 2 Public Key Encryption II
Other Public Key Algorithms
A public key system can be based on any one-way function. A rich
source is the set of NP-complete problems. These are infeasible to
solve, but a solution can be checked in polynomial time.
Merkle and Hellman proposed a public key system based on the
knapsack problem: given a set of integers and a target sum, find a
subset of the integers that sum to the target.
The algorithm is theoretically very secure, but has practical
weaknesses.
Lecture 49: 3 Public Key Encryption II
Authentication with Public Keys
Assume Ka is A’s public key. Suppose B sends the following
message to A: {M}Ka . What assurances does A have?
1 No-one intercepting the message could read it. Why?
2 He can’t be sure it actually came from B. Why not?
Thus, encryption with the public key is a privacy transformation,
but not an authenticity transformation.
Lecture 49: 4 Public Key Encryption II
Authentication with Public Keys
Using RSA, B send {M}K −1 to A. If A can decrypt it using Kb ,
b
what assurance is gained?
1 A is sure it originated with B. Why?
2 But, someone intercepting the message might read it. Why?
Thus, encryption with the private key is an authenticity
transformation, not a privacy transformation.
Note this only works in RSA, because:
{{P}d }e = P = {{P}e }d .
In other public key systems, you typically need two pairs of keys:
one pair for privacy and the other pair for “signing” (authenticity).
Lecture 49: 5 Public Key Encryption II
Lessons
RSA is the most widely used public key cryptosystem.
RSA is symmetric in the use of keys; most public key schemes
are not.
A public key encryption can be used for authenticity or for
privacy but not both at once.
Next lecture: Cryptographic Hash Functions
Lecture 49: 6 Public Key Encryption II
You might also like
- In Depth Security Vol. III: Proceedings of the DeepSec ConferencesFrom EverandIn Depth Security Vol. III: Proceedings of the DeepSec ConferencesNo ratings yet
- RSA Public Key Encryption AlgorithmDocument77 pagesRSA Public Key Encryption AlgorithmPaksmilerNo ratings yet
- Unit 4 Note For IV CseDocument17 pagesUnit 4 Note For IV CsetnagaviNo ratings yet
- Public Key-Crypto SystemDocument44 pagesPublic Key-Crypto SystemAnkit RajNo ratings yet
- Principles of Public CryptosystemsDocument32 pagesPrinciples of Public Cryptosystemskanna karthik reddyNo ratings yet
- Discrete Mathematics AssignmentDocument12 pagesDiscrete Mathematics AssignmentLalitSisodiaNo ratings yet
- Unit 4Document99 pagesUnit 4testNo ratings yet
- Security of C.N.: By: Eng. Ahmed K. DarajDocument8 pagesSecurity of C.N.: By: Eng. Ahmed K. DarajAHMED DARAJNo ratings yet
- CNS Mod 3Document13 pagesCNS Mod 3NikhilNo ratings yet
- Lab02 - Public-Key CryptographyDocument9 pagesLab02 - Public-Key CryptographyMinh Châu Đặng ĐạiNo ratings yet
- Unit 3Document34 pagesUnit 3Mahesh ThallapelliNo ratings yet
- Chapter 4Document84 pagesChapter 4Ahmed MohammedNo ratings yet
- Rsa (Cryptosystem) : RsaisaDocument10 pagesRsa (Cryptosystem) : RsaisaXerus AnatasNo ratings yet
- Lect1 PDFDocument10 pagesLect1 PDFssecureNo ratings yet
- CNS R16 - Unit-3Document29 pagesCNS R16 - Unit-3Geethanjali KotaruNo ratings yet
- Diffie-Hellman and Its Application in Security Protocols: ISO 9001:2008 CertifiedDocument5 pagesDiffie-Hellman and Its Application in Security Protocols: ISO 9001:2008 CertifiedHarish KumarNo ratings yet
- RSA (Cryptosystem) : 1 HistoryDocument9 pagesRSA (Cryptosystem) : 1 HistoryTanmay RajNo ratings yet
- Public Key Cryptography: S. Erfani, ECE Dept., University of Windsor 0688-558-01 Network SecurityDocument7 pagesPublic Key Cryptography: S. Erfani, ECE Dept., University of Windsor 0688-558-01 Network SecurityAbrasaxEimi370No ratings yet
- Gautam Gambhir Unit 2Document19 pagesGautam Gambhir Unit 2huntfortechNo ratings yet
- Assymetric Cryptography, Kerberos, X.509 CertificatesDocument34 pagesAssymetric Cryptography, Kerberos, X.509 CertificatesMukesh80% (5)
- Lecture 12: Public-Key Cryptography and The RSA Algorithm Lecture Notes On "Computer and Network Security"Document90 pagesLecture 12: Public-Key Cryptography and The RSA Algorithm Lecture Notes On "Computer and Network Security"Anshu MittalNo ratings yet
- Lecture 1: Cryptography: 1.2.1 Symmetric CaseDocument3 pagesLecture 1: Cryptography: 1.2.1 Symmetric Caseajay YadavNo ratings yet
- UNIT-3 (PART-I) (Number Theory) Prime Numbers: A QN + RDocument29 pagesUNIT-3 (PART-I) (Number Theory) Prime Numbers: A QN + Rsriramganesh8107No ratings yet
- This Article Is About An Algorithm For Public-Key Encryption. For The U.S. Encryption and Network Security Company, See - For Other Uses, SeeDocument27 pagesThis Article Is About An Algorithm For Public-Key Encryption. For The U.S. Encryption and Network Security Company, See - For Other Uses, SeeSonali PanigrahiNo ratings yet
- RSA CodingDocument13 pagesRSA Codingsaraakhtar1551No ratings yet
- Network Security (10ec832) : 8th E&CDocument42 pagesNetwork Security (10ec832) : 8th E&CbadboyNo ratings yet
- Modified RSA Public Key Cryptosystem Using Two Key PairsDocument3 pagesModified RSA Public Key Cryptosystem Using Two Key PairsJainul AbudinNo ratings yet
- RSA Public Key Encryption AlgorithmDocument5 pagesRSA Public Key Encryption AlgorithmRanda MoustafaNo ratings yet
- Lecture 3 RSADocument7 pagesLecture 3 RSAAHMED DARAJNo ratings yet
- C&NS Unit-2bDocument9 pagesC&NS Unit-2bRammohanNo ratings yet
- CRYPTO Mod4@AzDOCUMENTS - inDocument19 pagesCRYPTO Mod4@AzDOCUMENTS - insasindhur rNo ratings yet
- A Public Key Cryptosystem Based On Number Theory: Ashish Agarwala R SaravananDocument4 pagesA Public Key Cryptosystem Based On Number Theory: Ashish Agarwala R SaravananPraful MandaliyaNo ratings yet
- فتح Public keyDocument22 pagesفتح Public keygymfitness202320No ratings yet
- Seminar ReportDocument28 pagesSeminar Reporter_saritajain92No ratings yet
- UE20CS314 Unit3 SlidesDocument238 pagesUE20CS314 Unit3 SlidesKoushiNo ratings yet
- Introduction Graphic in PCDocument43 pagesIntroduction Graphic in PChahajsNo ratings yet
- NW & S Unit-6Document10 pagesNW & S Unit-6Sony ElipeNo ratings yet
- Deciding The Security of Protocols With Commuting Public Key EncryptionDocument12 pagesDeciding The Security of Protocols With Commuting Public Key EncryptionLorena StrechieNo ratings yet
- CS311 CryptographyReport VicheaphalkunRayDocument7 pagesCS311 CryptographyReport VicheaphalkunRayVicheaphalkun RayNo ratings yet
- Internet Encryption DecrypyionDocument4 pagesInternet Encryption DecrypyionBhushan PatleNo ratings yet
- 11 - Public Key CryptographyDocument24 pages11 - Public Key CryptographyTrevor ZhangNo ratings yet
- Lecture 6: Overview of Public-Key Cryptography and RSA: AckgroundDocument8 pagesLecture 6: Overview of Public-Key Cryptography and RSA: AckgroundnoorhillaNo ratings yet
- M S Ramaiah Institute of Technology: Department of Computer Science and Engineering BangaloreDocument47 pagesM S Ramaiah Institute of Technology: Department of Computer Science and Engineering BangaloreRithvik ShettyNo ratings yet
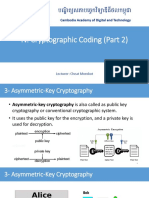
- 4.2. Cryptographic Coding (Part 2)Document27 pages4.2. Cryptographic Coding (Part 2)ReachNo ratings yet
- Generate An Encryption Key by Using Biometric Cryptosystems To Secure Transferring of Data Over A NetworkDocument7 pagesGenerate An Encryption Key by Using Biometric Cryptosystems To Secure Transferring of Data Over A NetworkInternational Organization of Scientific Research (IOSR)No ratings yet
- CSC Case StudyDocument2 pagesCSC Case StudyPrajwal BhajeNo ratings yet
- Cryptanalysis and Enhancement of An Anonymous Self-Certified Key Exchange ProtocolDocument29 pagesCryptanalysis and Enhancement of An Anonymous Self-Certified Key Exchange ProtocolS G ShivaPrasad YadavNo ratings yet
- Diffie Hellman Key & ELiptic Curve - 3Document23 pagesDiffie Hellman Key & ELiptic Curve - 3RAMESH M (RA2113003011001)No ratings yet
- Image To Text Encryption and Decryption Using Modified RSA AlgorithmDocument5 pagesImage To Text Encryption and Decryption Using Modified RSA AlgorithmAbdul Rahman KhamisNo ratings yet
- CH 2Document12 pagesCH 2SamNo ratings yet
- Comparative Study and Performance Analysis of Encryption in RSA, ECC and Goldwasser-Micali CryptosystemsDocument8 pagesComparative Study and Performance Analysis of Encryption in RSA, ECC and Goldwasser-Micali CryptosystemsInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Unit 4Document18 pagesUnit 421EE026 Anushka SrivastavaNo ratings yet
- Cryptography 4Document33 pagesCryptography 4Venera MakhambayevaNo ratings yet
- Cryptography & Protocols: Presented By: Dr. S. S. Bedi Department of CSIT, MJP Rohilkhsnd University, BareillyDocument59 pagesCryptography & Protocols: Presented By: Dr. S. S. Bedi Department of CSIT, MJP Rohilkhsnd University, BareillyShreya YadavNo ratings yet
- UNIT - 4 NotesDocument28 pagesUNIT - 4 NotesSushant YadavNo ratings yet
- Rabin Cryptosystem 1.1 IntroductionDocument8 pagesRabin Cryptosystem 1.1 IntroductionBillal HossainNo ratings yet
- Cryptography and Network SecurityDocument19 pagesCryptography and Network SecurityShivali GuptaNo ratings yet
- Public Key Cryptography 569692953829aDocument58 pagesPublic Key Cryptography 569692953829aJ SanthanakrishnanNo ratings yet
- RSA Algorithm CS13Document6 pagesRSA Algorithm CS13api-3730515100% (1)
- Curriculum BasisDocument9 pagesCurriculum BasisMc Robinson ReguceraNo ratings yet
- Recent Security Attacks and Challenges: James Patrick A. Acang - Department of Computer ScienceDocument10 pagesRecent Security Attacks and Challenges: James Patrick A. Acang - Department of Computer ScienceMc Robinson ReguceraNo ratings yet
- Human Information Processing: James Patrick A. Acang - Deparment of Computer ScienceDocument24 pagesHuman Information Processing: James Patrick A. Acang - Deparment of Computer ScienceMc Robinson ReguceraNo ratings yet
- Lecture 1Document22 pagesLecture 1Mc Robinson ReguceraNo ratings yet
- Intensified ISCC Thesis Parts 1Document2 pagesIntensified ISCC Thesis Parts 1Mc Robinson ReguceraNo ratings yet
- CBC Photography NC IIDocument71 pagesCBC Photography NC IIKrishna CruzNo ratings yet
- Foundations of Computer Security: Lecture 1: IntroductionDocument11 pagesFoundations of Computer Security: Lecture 1: IntroductionMc Robinson ReguceraNo ratings yet
- Foundations of Computer Security: Lecture 2: Why Security Is HardDocument9 pagesFoundations of Computer Security: Lecture 2: Why Security Is HardMc Robinson ReguceraNo ratings yet
- Lecture 3Document7 pagesLecture 3xssdNo ratings yet
- Lecture 6Document7 pagesLecture 6Mc Robinson ReguceraNo ratings yet
- Human Information Processing: James Patrick A. Acang - Deparment of Computer ScienceDocument24 pagesHuman Information Processing: James Patrick A. Acang - Deparment of Computer ScienceMc Robinson ReguceraNo ratings yet
- Affine Cipher: WWW - Radford.eduDocument48 pagesAffine Cipher: WWW - Radford.eduMc Robinson ReguceraNo ratings yet
- Foundations of Computer SecurityDocument8 pagesFoundations of Computer SecurityMc Robinson ReguceraNo ratings yet
- Foundations of Computer Security: Lecture 39: Properties of CiphersDocument7 pagesFoundations of Computer Security: Lecture 39: Properties of CiphersMc Robinson ReguceraNo ratings yet
- Foundations of Computer Security: Lecture 40: Substitution CiphersDocument9 pagesFoundations of Computer Security: Lecture 40: Substitution CiphersMc Robinson ReguceraNo ratings yet
- EncryptionDocument7 pagesEncryptionRicardo Gómez ParedesNo ratings yet
- Programme: Department HeadsDocument2 pagesProgramme: Department HeadsMc Robinson ReguceraNo ratings yet
- Visual Arts Introduction and CPRCDocument7 pagesVisual Arts Introduction and CPRCMc Robinson ReguceraNo ratings yet
- Didi 1001Document1 pageDidi 1001Mc Robinson ReguceraNo ratings yet
- Programme: Reton, Liverty SDocument2 pagesProgramme: Reton, Liverty SMc Robinson ReguceraNo ratings yet
- Foundations of Computer Security: Lecture 48: Public Key EncryptionDocument7 pagesFoundations of Computer Security: Lecture 48: Public Key EncryptionMc Robinson ReguceraNo ratings yet
- Code EquivalenceDocument49 pagesCode EquivalenceErica S EricaNo ratings yet
- Final Reduced Objective Allowable Allowable Cell Name Value Cost Coefficient Increase DecreaseDocument6 pagesFinal Reduced Objective Allowable Allowable Cell Name Value Cost Coefficient Increase DecreaseSharjeel NaeemNo ratings yet
- Deep Learning 4/7: Convolutional Neural Networks: C. de Castro, IEIIT-CNR, Cristina - Decastro@ieiit - Cnr.itDocument49 pagesDeep Learning 4/7: Convolutional Neural Networks: C. de Castro, IEIIT-CNR, Cristina - Decastro@ieiit - Cnr.itFathimuthu JoharaNo ratings yet
- 06 Inductive Data TypesDocument55 pages06 Inductive Data TypesvalekhzNo ratings yet
- Analysis of AlgorithmDocument43 pagesAnalysis of AlgorithmAzeemNo ratings yet
- A Model in Decision MakingDocument32 pagesA Model in Decision MakingKebede KassuNo ratings yet
- Stack and QueueDocument53 pagesStack and QueueAditi PatilNo ratings yet
- Answer Chapter 4 Fas Ed 3Document19 pagesAnswer Chapter 4 Fas Ed 3ahmed mahamedNo ratings yet
- Rr720507 Neural NetworksDocument5 pagesRr720507 Neural NetworksandhracollegesNo ratings yet
- SS Lab ManualDocument66 pagesSS Lab ManualVaishnavi Das C HNo ratings yet
- Coding Interview in JavaDocument190 pagesCoding Interview in JavaHari PedapatiNo ratings yet
- Unit 3 AI Srs 13-14Document45 pagesUnit 3 AI Srs 13-14Supriya AttarkarNo ratings yet
- Midterm Exam SolutionDocument11 pagesMidterm Exam SolutionShelaRamosNo ratings yet
- 10.1007@s10462 020 09906 6Document87 pages10.1007@s10462 020 09906 6Dĩnh TràNo ratings yet
- To Implement Boundary Fill AlgorithmDocument4 pagesTo Implement Boundary Fill AlgorithmSanjayLullaNo ratings yet
- Week 1 Learning Task 1: Evaluate The Following Polynomials in Your Answer SheetDocument12 pagesWeek 1 Learning Task 1: Evaluate The Following Polynomials in Your Answer SheetlouiseNo ratings yet
- Lesson 8 - Introduction To Deep Learning PDFDocument25 pagesLesson 8 - Introduction To Deep Learning PDFJoe1No ratings yet
- Exam Advanced Linear Programming, May 14, 13.30-16.30Document4 pagesExam Advanced Linear Programming, May 14, 13.30-16.30tequesta95No ratings yet
- Information Retrieval - Question BankDocument3 pagesInformation Retrieval - Question BankPapithaNo ratings yet
- Comparison of Gauss Jacobi Method and Gauss Seidel Method Using ScilabDocument3 pagesComparison of Gauss Jacobi Method and Gauss Seidel Method Using ScilabEditor IJTSRDNo ratings yet
- DE - KOE 039 - Assignment #1Document2 pagesDE - KOE 039 - Assignment #1Sanu SanuNo ratings yet
- 5 Fuzzy Expert SystemDocument6 pages5 Fuzzy Expert Systemcloud projectNo ratings yet
- EEL 6266 Power System Operation and Control: Unit CommitmentDocument31 pagesEEL 6266 Power System Operation and Control: Unit CommitmentBenny Wijaya NababanNo ratings yet
- LaberportDocument9 pagesLaberportMark GadgetsNo ratings yet
- Implementing Bubble Sort AlgorithmDocument6 pagesImplementing Bubble Sort AlgorithmhariniNo ratings yet
- Implementation of Booth Multiplier and Modified Booth MultiplierDocument8 pagesImplementation of Booth Multiplier and Modified Booth Multiplierlokesh kadagalaNo ratings yet
- Script Programming: Scheme of Valuation 18IT404 B.Tech., (Semester-IV)Document2 pagesScript Programming: Scheme of Valuation 18IT404 B.Tech., (Semester-IV)nalluri_08No ratings yet
- Numerical Analysis 323Document161 pagesNumerical Analysis 323maths203No ratings yet
- PDF 2 6 Study Guide and Intervention Special FunctionsDocument2 pagesPDF 2 6 Study Guide and Intervention Special FunctionsVIPNo ratings yet
- Chapter 4 Signal Flow GraphDocument34 pagesChapter 4 Signal Flow GraphAbhishek PattanaikNo ratings yet