Professional Documents
Culture Documents
Ktustudents in
Ktustudents in
Uploaded by
Vishnu Prasad MOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Ktustudents in
Ktustudents in
Uploaded by
Vishnu Prasad MCopyright:
Available Formats
MODULE 4 EMBEDDED SYSTEM
Module 4
Programming concepts of Embedded programming – Features
of Embedded C++ and Embedded Java (basics only). Software
Implementation, Testing, Validation and debugging, system-
KTUStudents.in
on- chip.
MBCCET, PEERMADE, ECE DPT
For more study materials: WWW.KTUSTUDENTS.IN 1
MODULE 4 EMBEDDED SYSTEM
Assembly language
Assembly Language based development was (is) the most common technique
adopted from the beginning of embedded technology development. Thorough
understanding of the processor architecture, memory organisation, register
sets and mnemonics is very essential for Assembly Language based
development. If you master one processor architecture and its assembly
instructions, you can make the processor as flexible as a gymnast.
Assembly language programming
The Assembly language program written in assembly code is saved as .asm
(Assembly file) file or an .src (source) file. Any text editor like 'notepad' or
'WordPad' from Microsoft@ or the text editor provided by an Integrated
Development (IDE) tool can be used for writing the assembly instructions.
similar to 'C' and other high level language programming, you can have
multiple source files called modules in assembly language programming.
Each module is represented by an .asm' or '.src' file similar to the '.c' files in
C programming.
This approach is known as 'Modular Programming'. Modular programming is
employed when the program is too complex or too big. In 'Modular
Programming', the entire code is divided into submodules and each module is
KTUStudents.in
made re-usable. Modular Programs are usually easy to code, debug and alter.
Conversion of the assembly language to machine language
Source File to Object File Translation
Translation of assembly code to machine code is performed by assembler. he
assemblers for different target machines are different and it is common that
assemblers from multiple vendors are available in the market for the same
target machines. Each source module is written in Assembly and is stored in
.src file or .asm file.Each file can be assembled separately to examine the
syntax and incorrect assembly instructions.
MBCCET, PEERMADE, ECE DPT
For more study materials: WWW.KTUSTUDENTS.IN 2
MODULE 4 EMBEDDED SYSTEM
On Successful assembling of each .src/.asm: file a corresponding object tile
is created with extension ‘.obj. The object file does not contain the absolute
address of where the generated code needs to be placed on the program
memory and hence it is called a re-locatable.
Library File Creation and Usage:
Libraries are specially formatted, ordered program collections of object
modules that may be used by the linker at a later time. When the linker
processes a library, only those object modules in the library that are necessary
to create the program are used. Library files are generated with extension lib'.
Library file is some kind of source code hiding technique.
If you don't want to reveal the source code behind the various functions you
have written in your program and at the same time you want them to be
distributed to application developers for making use of them in their
applications, you can supply them as library files and give them the details of
the public functions available from the library (function name, function
input/output, etc). For using a library file in a project, add the library to the
project.
Linker and Locater:
Linker and Locater is another software utility responsible for "linking the
KTUStudents.in
various object modules in a multi-module project and assigning absolute
address to each module. Linker generates an absolute object module by
extracting the object modules from the library, if any and those obj files
created by the assembler, which is generated by assembling the individual
modules Of a project.
It is the responsibility of the linker to link any external dependent variables
or functions declared on various modules and resolve the external
dependencies among the modules.
Object to Hex File Converter
This is the final stage in the conversion of Assembly language (mnemonics)
to machine understandable language (machine code). Hex File is the
representation of the machine code and the hex file is dumped into the code
memory Of the processor/controller. The hex file representation varies
depending on the target processor/controller make.
Advantages of Assembly Language Based Development
a. Efficient Code Memory and Data Memory Usage (Memory
Optimisation): Since the developer is well versed with the target
processor architecture and memory organization, optimised code can
be written for performing operations. This leads to less utilisation of
code memory and efficient utilisation of data memory. Remember
memory is a primary concern in any embedded product
b. High Performance: Optimised code not only improves the code memory
usage but also improves the total system performance. Through
effective assembly coding, optimum performance can be achieved for a
target application.
MBCCET, PEERMADE, ECE DPT
For more study materials: WWW.KTUSTUDENTS.IN 3
MODULE 4 EMBEDDED SYSTEM
c. Low Level Hardware Access: Most of the code for low level
programming like accessing external device specific registers from the
operating system kernel, device drivers, and low level interrupt
routines, etc. are making use of direct assembly coding since low level
device specific operation support is not commonly available with most
of the high-level language cross compilers.
d. Code Reverse Engineering: Reverse engineering is the process of
understanding the technology behind a product by extracting the
information from a finished product. Reverse engineering is performed
by 'hawkers' to reveal the technology behind 'Proprietary Products'.
e. Though most of the products employ code memory protection, if it may
be possible to break the memory protection and read the code memory,
it can easily be converted into assembly code using a dis-assembler
program for the target machine.
f. Assembly codes are sensitive to the processor, memory, ports and
devices. Assembly software gives a precise control of the processor
internal devices, and makes full use of processor-specific features of
processor instruction set and addressing modes.
g. Machine codes are compact, and are processor and memory sensitive.
The system thus needs a smaller memory. No additional memory need
due to data type's selection, conditions, and declarations of rules. A
program is also not compiler specific and library-function specific.
KTUStudents.in
h. Certain codes such as device-driver codes may need only a few
assembly instructions. Assembly codes for these can be compact and
precise, and are conveniently written.
i. Bottom-up-design approach is easily usable. Approach to this way of
designing a program is as follows: First code the basic functional
modules (submodules) and then use these to build a bigger module.
Submodules of the specific and distinct sets of actions are first coded.
Programs for delay, counting, finding time intervals and many
applications can be written. Then the final program is signed by
integrating the modules.
Drawbacks of Assembly Language Based Development
a. High Development Time: Assembly language is much harder to
program than high level languages. The developer must pay attention
to more details and must have thorough knowledge of the architecture
memory organization and register details of the target processor in use.
Learning the inner details Of the processor and its assembly
instructions is highly time consuming and it creates a delay impact in
product development. Also more lines of assembly code are required for
performing an action which can be done with a single instruction in a
high-level language like 'C'.
b. Developer Dependency: There is no common written rule for
developing assembly language based applications whereas all high level
languages instruct certain set of rules for application development.
In assembly language programming, the developers will have the
freedom to choose the different memory location and registers. Also the
MBCCET, PEERMADE, ECE DPT
For more study materials: WWW.KTUSTUDENTS.IN 4
MODULE 4 EMBEDDED SYSTEM
programming approach varies from developer to developer depending
on his/her taste.
c. Non-Portable: Target applications written in assembly instructions are
valid only for that particular family of processors (e.g. Application
written for Intel x86 family of processors) and cannot be re-used for
another target processor/controllers (Say ARMI I family of processors).
High Level Language Based Development
As we have seen in the earlier section, Assembly language based programming
is highly time consuming, tedious and requires skilled programmers with
sound knowledge of the target processor architecture. Also applications
developed in Assembly language are non-portable.
Here comes the role of high level languages. Any high level language (like C,
C++ or Java) with a supported cross compiler (for converting the application
developed in high level language to target processor specific assembly code)
for the target processor can be used for embedded firmware development.
The most commonly used high level language for embedded firmware
application development is ' C'. You may be thinking why 'C' is used as the
popular embedded firmware development language.
The answer is "C is the well-defined, easy to use high level language with
KTUStudents.in
extensive cross platform development tool support
The various steps involved in high level language based embedded firmware
development is same as that Of assembly language based development except
that the conversion of source file Written in high level language to object file
is done by a cross-compiler, whereas in Assembly language based
development it is carried out by an assembler.
The various steps in high level language to machine language
The program written in any of the high level language is saved with the
corresponding language extension (.c for C, .cpp for C++ etc). Any text editor
MBCCET, PEERMADE, ECE DPT
For more study materials: WWW.KTUSTUDENTS.IN 5
MODULE 4 EMBEDDED SYSTEM
like 'notepad' or G WordPad' from Microsoft@ or the text editor provided by an
Integrated Development (IDE) tool supporting the high level language in use
can be used for writing the program
Most of the high level languages support modular programming approach and
hence you can have multiple source files called modules written in
corresponding high level language.
Translation of high level source code to executable object code is done by a
cross compiler. The cross-compilers for different high level languages for the
same target processor are different.
It should be noted that each high level language should have a cross-compiler
for converting the high level source code into the target processor machine
code. Without cross-compiler support a high level language cannot be used
for embedded firmware development.
Advantages of High Level Language
1. Reduced Development Time: Developer requires less or little
knowledge on the internal hardware details and architecture of the
target processor/controller.
Bare minimal knowledge of the memory organisation and register
details of the target processor in use and syntax of the high level
KTUStudents.in
language are the only pre-requisites for high level language based
firmware development.
2. Developer Independency: The syntax used by most of the high level
languages are universal and a program written in the high level
language can easily be understood by a second person knowing the
syntax of the language.
Certain instructions may require little knowledge of the target hardware
details like register set, memory map etc. High level languages always
instruct certain set of rules for writing the code and commenting the
piece of code. If the developer strictly adheres to the rules, the firmware
will be 100% developer independent.
3. Portability: Target applications written in high level languages are
converted to target processor/controller understandable format
(machine codes) by a cross-compiler.
An application written in high level language for a particular target
processor can easily be converted to another target processor/controller
specific application, with little or less effort by simply re-compiling/little
code modification followed by re-compiling the application for the
required target processor/controller, provided, the cross-compiler has
support for the processor/controller selected.
This makes applications written in high level language highly portable.
Little effort may be required in the existing code to replace the target
processor specific header files with new header files, register definitions
with new ones, etc. This is the major flexibility offered by high level
language based design.
4. Program-development cycle is much shorter in high-level language even
for complex systems due to the following: use of (i) routines (procedures)
MBCCET, PEERMADE, ECE DPT
For more study materials: WWW.KTUSTUDENTS.IN 6
MODULE 4 EMBEDDED SYSTEM
(called functions in C/C++ and methods in Java), (ii) standard library
functions, and (iii) modular programming, top-down design and object
oriented design approaches. Application programs in high-level
language are structured. This ensures that the software is based on
sound software engineering principles
5. Top-down-design programming approach, used in high-level language
is as follows: Main program is designed first, then its modules,
submodules, and finally, the functions.
6. A high-level language program facilitates declaration of data types. Type
declarations simplify the programming. Each data type is an
abstraction for the methods, which are permitted for using'
manipulating, representing, and for defining a set of permissible
operations on that data.
7. The program facilitates 'type checking'. This makes a program less
prone to error. For example,' type checking does not permit subtraction,
multiplication and division on the char.data types.
8. The program facilitates use of program-flow-control structures, such as
loops and conditional. The program has portability, and is not processor
specific.
Limitations of High Level Language Based Development
KTUStudents.in
1. Some cross-compilers available for high level languages may not be so
efficient in generating optimised target processor specific instructions.
2. Target images created by such compilers may be messy and non-
optimised in terms of performance as well as code size.
3. High level language based code snippets may not be efficient in
accessing low level hardware where hardware access timing is critical
(of the order of Nano or micro seconds).
4. The investment required for high level language based development
tools (Integrated Development Environment incorporating cross-
compiler) is high compared to Assembly Language based firmware
development tools.
PROGRAMMING IN EMBEDDED C
Whenever the conventional 'C' Language and its extensions are used for
programming embedded systems, it is referred as 'Embedded C'
programming.
Programming in 'Embedded C' is quite different from conventional Desktop
application development using 'C' language for a particular OS platform.
Desktop computers contain working memory in the range of Megabytes
(Nowadays Giga bytes) and storage memory in the range of Giga bytes. For a
desktop application developer, the resources available are surplus in quantity
and s/he can be very lavish in the usage of RAM and ROM and no restrictions
are imposed at all.
This is not the case for embedded application developers. Almost all embedded
systems are limited in both storage and working memory resources.
MBCCET, PEERMADE, ECE DPT
For more study materials: WWW.KTUSTUDENTS.IN 7
MODULE 4 EMBEDDED SYSTEM
Embedded application developers should be aware of this fact and should
develop applications in the best possible way which optimises the code
memory and working memory usage as well as performance. In other words,
the hands of an embedded application developer are always tied up in the
memory usage context.
'C' v/s ‘Embedded C'
C is a well-structured, well defined and general purpose programming
language with extensive bit manipulation support.
'C' offers a combination of the features of high level language and assembly
and help in hardware access programing as well as business package
developments (Application developments like pay roll systems, banking
applications, etc).
The conventional 'C' language follows ANSI standard and it incorporates
various library files for different operating systems.
A platform (operating system) specific application, known as, compiler is used
for the conversion of programs written in 'C' to the target processor (on which
the OS is running) specific binary files.
'Embedded C
KTUStudents.in
Embedded 'C' can be considered as a subset of conventional 'C' language.
Embedded 'C' supports all 'C' instructions and incorporates a few target
processor specific functions/instructions. It should be noted that the
standard ANSI 'C' library implementation is always tailored to the target
processor/controller library files in Embedded C.
The implementation of target processor/controller specific
functions/instructions depends upon the processor/controller as well as the
supported cross-compiler for the particular Embedded 'C' language.
A software program called 'Cross-compiler' is used for the conversion of
programs written in Embedded 'C' to target processor/controller specific
instructions (machine language).
Compiler vs. Cross-Compiler
Compiler is a software tool that converts a source code written in a high level
language on top of a particular operating system running on a specific target
processor architecture. Here the operating system, the compiler program and
the application making use of the source code run on the same target
processor. The source code is converted to the target processor specific
machine instructions.
The development is platform specific (OS as well as target processor on which
the OS is running). Compilers are generally termed as 'Native Compilers'. A
native compiler generates machine code for the same machine (processor) on
which it is running
Cross-compilers are the software tools used in cross-platform development
applications. In cross- platform development, the compiler running on a
MBCCET, PEERMADE, ECE DPT
For more study materials: WWW.KTUSTUDENTS.IN 8
MODULE 4 EMBEDDED SYSTEM
particular target processor/OS converts the source code to machine code for
a target processor whose architecture and instruction set is different from the
processor on which the compiler is running or for an operating system which
is different from the current development environment OS.
Embedded system development is a typical example for cross- platform
development where embedded firmware is developed on a machine with
Intel/AMD or any Other target processors and the same is converted into
machine code for any other target processor architecture (e.g. 8051, PIC, ARM
etc). Keil C51 is an example for cross-compiler. The term 'Compiler' is used
interchangeably with 'Cross-compiler' in embedded firmware applications.
Whenever you see the term 'Compiler' related to any embedded firmware
application, please understand that it is referring the cross-compiler.
Embedded C programing
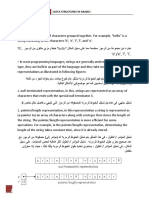
Keywords and identifiers:
Keywords are the reserved names used by the 'C' language. All keywords have
a fixed meaning in the 'C' language context and they are not allowed for
programmers for naming their own variables or functions. ANSI 'C' supports
32 keywords and they are listed below. All 'C' supported keywords should be
written in 'lowercase' letters.
KTUStudents.in
Identifiers are user defined names and labels. Identifiers can contain letters
of English alphabet (both upper and lower case) and numbers. The starting
character of an identifier should be a letter. The only special character allowed
in identifier is underscore.
Data Types:
Data type represents the type of data held by a variable. It should be noted
that the storage size may vary for data type depending on the cross-compiler
in use for embedded applications.
Since memory is a big constraint in embedded applications, select the
optimum data type for a variable. For example if the variable is expected to be
within the range 0 to 255, declare the same as an 'unsigned char' or 'unsigned
MBCCET, PEERMADE, ECE DPT
For more study materials: WWW.KTUSTUDENTS.IN 9
MODULE 4 EMBEDDED SYSTEM
short int' data type instead of declaring it as 'int' or 'unsigned int'. This will
definitely save considerable amount of memory.
Storage Class:
KTUStudents.in
Keywords related to storage class provide information on the scope (visibility
or accessibility) and life time (existence) of a variable. 'C' supports four types
of storage classes and they are listed below.
Arithmetic Operations:
The list of arithmetic operators supported by 'C' are listed below
MBCCET, PEERMADE, ECE DPT 10
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
Logical Operations:
Logical operations are usually performed for decision making and Program
control transfer. The list of logical operations supported by 'C' are listed below.
Relational Operations :
Relational operations are normally performed for decision making and
program control transfer on the basis of comparison. Relational operations
supported by 'C' are listed below.
KTUStudents.in
Branching Instructions:
Branching instructions change the program execution flow conditionally or
unconditionally. Conditional branching depends on certain conditions and if
the conditions are met, the program execution is diverted accordingly.
Unconditional branching instructions divert program execution
unconditionally. Commonly used conditional branching instructions are
listed below
MBCCET, PEERMADE, ECE DPT 11
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
KTUStudents.in
MBCCET, PEERMADE, ECE DPT 12
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
Looping Instructions:
Looping instructions are used for executing a particular block of code
repeatedly till a condition is met or wait till an event is fired. Embedded
programming often uses the looping instructions for checking the status of
certain I/o ports, registers, etc. and also for producing delays.
Certain devices allow write/read operations to and from some registers of the
device only when the device is ready and the device ready is normally
indicated by a status register or by Setting/clearing certain bits of status
registers.
Hence the program should keep on reading the status register till the device
KTUStudents.in
ready indication comes. The reading operation forms a loop. The looping
instructions supported by 'C' are listed below.
MBCCET, PEERMADE, ECE DPT 13
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
C' PROGRAM ELEMENTS: HEADER AND SOURCE FILES AND
PREPROCESSOR DIRECTIVES
A 'C' program has the following structural elements:
Pre-processor declarations, definitions and statements,
Main function, and
Functions, exceptions and ISRs.
A 'C' program has the following preprocessor structural elements.
Include directives for the file inclusion
KTUStudents.in
Definitions for pre-processor global variables (global means all
throughout the program module)
Definitions of constants
Declarations for global data types, type declaration and data structures,
macros and functions.
Include Directive for the Inclusion of Files
Include is a pre-processor directive to include the contents (codes or data) of
a file. Inclusion of all files and specific header files has to be as per
requirements. A 'C' program first includes the header and source files. These
are readily available files. The purpose Of each included file is mentioned in
the comments within the /* and */ symbols as per practice in 'C'.
including Codes Files :These are the files for the codes already available.
For example, #include "prct1Handlers. c . /* Include file for the codes for
handling and actions as per the protocols used for driving streams to the
network. */
including Constant Data Files: These are the files for the codes and may have
the extension ' .const'.
Including Strings Data Files These are the files for the strings and may have
the extension '.strings' or '.str.' or '.txt.
Including Initial Data Files :Initial or default data files are for locating in ROM
of embedded system. Boot-up program is copied later into RAM and has
extension, '.init'. On the other hand, data files have the extension, .'data'.
MBCCET, PEERMADE, ECE DPT 14
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
Including Basic Variables Files: Files for the local or global static variables
are stored in RAM. These basic variables are stored in the files with the
extension '.bss'.
Including Header Files :It is a pre-processor directive. It includes the contents
(codes or data of a set of source files. These are files for specific modules. A
header file has the extension '.h'. Example # include "vxWorks.h"/* Include
VxWorks functions * /
Source Files
source files are program files for the functions of application software. The
source files need to be compiled, tested and validated. A source file also
possesses the pre-processor directives of application software. The file has the
first function (main function) from where the processing will start. The code
in C for first function is void main ( ). The main function calls other functions.
Configuration Files
configuration files are the files for the configuration of a subsystem. Device
configuration codes can be put in a file of basic variables and included when
needed. If these codes are in the file "serial Line_ cfg. h", then # include
"serialLine __ cfg.h " will be pre-processor directive.
Pre-processor Directives
KTUStudents.in
A pre-processor directive starts with a sharp (hash) sign. These commands
are for the following directives to the compiler for processing. Pre-processor
Global Variables For example, in a program "# define time pre-processor
Constants "# define false 0" is a pre-processor directive in an example. It
means it is a directive before processing to assume 'false' as 0
program elements: macros and functions
pre-processor Macros A macro is a collection of codes that is defined in a
program by a name. It differs from a function in the sense that once a macro
is defined by a name, the compiler puts the corresponding codes for it at every
place wherever that macro name appears.
Example : Consider two macros, 'enable_ Maskable _ Intr ( ) ' and disable
Maskable_ Intr ( ) ' (The pair of brackets in the macro is optional. If it is
present, it improves readability as it distinguishes a macro from a constant).
Whenever the name enable Mask able Intr appears, the compiler places the
codes designed for it.
How does a macro differ from a function?
The codes for a function are compiled only once. Processor has to save the
context on calling that function, and on return, processor restores the
context. Further, a function may return nothing (void declaration case) or
return a Boolean value, an integer, or any primitive or reference type of data.
Primitive means similar to an integer or character. Reference type means
similar to an array or structure.
MBCCET, PEERMADE, ECE DPT 15
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
The codes for Macro are compiled in every function wherever that macro name
is used, Compiler, before compilation, puts the codes at the places wherever
the macro is used. When a macro runs in a function, the processor does not
save the context, and thus does not have to restore the context, as there is no
return in macro.
Macros are used for short codes only. This is because, if a function call is
used for short codes instead of macro, the overheads (context saving and other
actions on function call and return) take additional time T overheads ,The
time is the same order of magnitude as the time .T exec , for execution
overheads of short codes within a function. We use a function for codes when
the T overheads <<T exec macro for codes when T overheads >> T exec.
PROGRAM ELEMENTS: DATA TYPES, DATA STRUCTURES, MODIFIERS,
STATEMENTS, LOOPS AND POINTERS
Use of Data Types: Whenever data is named using an identifier, it will have
the address(es) allocated at the memory. Number of allocated addresses for
data depends upon data type
Use of Modifiers: A modifier modifies the actions of a data type.
Use of Pointers and Null Pointers: Pointers are powerful tools when used
correctly and according to certain basic principles. A Pointer is a reference to
KTUStudents.in
a starting memory address. A pointer can refer to a variable, data structure
or function.
In the 'C' language, symbol * is used before a pointer. For example, unsigned
char * Ox 1000 means a character of 8 bit at the address Oxl000. A NULL
pointer declares the following: ' #define NULL (void*) Ox0000'.
Use of Data Structures: Stack, Queue, Array, List, Tree, Pipe, Table and
Hash Table
A data structure is a way of organising several data elements of same types
or different types. A data in a data structure can then be identified and
accessed with the help of a few pointers and/or indices and/ or functions.
A data structure is an important element of any program. A data structure
saves a set of memory addresses in an organized way. Any data structure
element can be retrieved. Few important data structures are stack, one-
dimensional array, queue, circular queue, pipe, a table (two-dimensional
array), lookup table, hash table and list.
Stack: It is a structure with a series of elements with its last element waiting
for an operation. An operation can be done only in the last in first out (LIFO)
mode. An element can be pushed (inserted) only at the top in the series of
elements and is still waiting for an operation.
There is only one pointer used for pop (deleting) after the operation as well as
for push (inserting). A pointer which points to stack top is needed for handling
each stack. It is called SP (Stack Pointer) or Stop which points to the top of
the stack and changes on each push or pop.
MBCCET, PEERMADE, ECE DPT 16
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
Array: A data structure, array, is an important programming element. An
array has a multiple data element, each identifiable by an index or by a set of
indices. Index is an integer that starts from 0 to (array length — l) in a one
dimension. Data word can be retrieved from any element address in the block
that is allocated to the array.
Queue: The data structure, called queue, is another important programming
element. The reading is with the help of indices in case of array, and first
element address (identifier address). Therefore, any element can be read or
written at any instance.
Each element is read in queue from an address next to the address from where
queue was last read. This reading is called deletion. It is written to an address
next to the address from where queue element was last written. This writing
is called insertion.
A queue is a data structure with an allotted memory block (buffer) from which
a data element is always retrieved in FIFO mode. It has two pointers, one for
its head and the other for its tail. Any deletion is made from the head address
and any insertion is made at the tail address.
An exception (an error indication) must be thrown whenever the pointer
increments beyond the block end boundary so that appropriate action can be
taken.
KTUStudents.in
List: A list is for nonconsecutively located objects at the memory. A list is a
data structure with a set of number of distinct sets of memory addresses, one
for each element.
A list has a top (head) pointer for the memory address from where the list
starts. Each list element at the memory also stores a pointer to the next
element at next set of addresses. The last element in the list points to null.
A table: is a two-dimensional array (matrix). It is an important data set in
memory block. There is always a base pointer for a table. The base points to
its first element at the first column, first row. There are two indices, one for a
row and the other for a column Look-up Table and Hash Table.
OBJECTED-ORIENTED PROGRAMMING
When a large program is made, an object-oriented language offers many
advantages. An Objected Oriented Programming (OOP) language provides for
the followings:
defining of an object or set of objects, which are common or similar
objects within a program and between many programs,
defining the methods that manipulate the objects without modifying
their definitions,
creation of multiple instances of the defined object or set of objects or
new objects,
inheritance,
data encapsulation, and design of reusable components
An object can be characterized by the following.
MBCCET, PEERMADE, ECE DPT 17
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
An identity (a reference to a memory block that holds its state and
behavior).
A state (its data, property, fields and attributes).
A behavior (method or methods that can manipulate the state of the
object).
A procedure-based language, such as FORTRAN, COBOL, Pascal and C, are
large programs that are split into simpler functional blocks and statements.
In an object-oriented language like Smalltalk C++ or Java, logical groups (also
known as classes) are first made.
Each group defines the data and the methods of using the data. A set of these
groups then gives an application program. Each group has internal user-level
data fields and methods of processing that data at these fields.
Each group can then create many objects by copying the group and making
it functional. Each object is functional. Each object can interact with other
objects to process the user's data. The language provides for formation of
classes by the definition of a group of objects having similar attributes and
common behavior. A class creates the objects. An object is an instance of a
class.
EMBEDDED PROGRAMMING IN C++
KTUStudents.in
Programming concepts for embedded programming in C++ are as follows:
A class binds all the member functions together for creating objects. The objects will
have memory allocation as well as default assignments to its variables that are not
declared static.
A class can derive (inherit) from another class also. Creating a child class from a parent
class creates a new application
Methods (C functions) can have same name in the inherited class. This
is called method overloading. Methods can have the same name as well
as the same number and type of arguments in the inherited class. This
is called method overriding. These are the two significant features that
are extremely useful in a large program.
Operators in can be overloaded like in method overloading
There is struct that binds all the member functions together in C. But
a C++ class has object features. It can be extended and child classes
can be derived from it.A number of child classes can be derived from a
common class. This feature is called polymorphism.A class can be
declared as public or private.
The data and methods access is restricted when a class is declared
private. Struct does not have these features.
Embedded system programmers use C++ due to the OOP features of software
re-usability, extendibility, polymorphism, function overriding and overloading
along with the portability with the C codes and in-line assembly codes. also
provides for overloading of operators.
Embedded C++ is a C++ version, which makes large program development
simpler by providing Object-Oriented Programming (OOP) features of using
MBCCET, PEERMADE, ECE DPT 18
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
an object, which binds state and behavior and which is defined by an instance
of a class. We use objects in a way that minimises memory needs and run-
time overheads in the system
Advantages of C++
1. C++is an Object-Oriented Program (OOP) language, which in addition,
supports the procedure oriented codes of C.
2. Program coding in C++ codes provides the advantage of objected-
oriented programming as well as the advantage of C and in-line
assembly.
Disadvantages of C++
The program codes become lengthy, particularly when certain features of the
standard C++ are used.
Examples of these features are as follows:
(a) Template (b) Multiple Inheritance (Deriving a class from many parents) (c)
Exceptional handling (d) Virtual base classes (e) Classes for I/O Streams ( Two
library functions are cin (for character (s) in) and cout (for character (s) out)).
The I/O stream class library provides for the input and output streams of
characters
KTUStudents.in
EMBEDDED PROGRAMMING IN JAVA
Java programming starts from coding for the classes. A class has members.
A field is like a variable or struct in 'C'. A method defines the operations on
the fields, similar to function in 'C‘. Class is a named set of codes that has a
number of members such as data fields (variables), and methods (functions).
Class is used to create objects with instances of these members. The
operations are done on the objects by passing the messages to the objects in
object-oriented programming. Each class is a logical group with an identity, a
state and a behavior specification.
Java program elements
1. Local Variable: A variable within a block of codes that is defined inside
the curly braces and has limited scope.
2. Instance Method: Blocks of Java codes, which are given a name, a call
(invocation) is made by other Java codes that can also pass (transmit)
the needed reference to the values, parameters, etc.
3. Instance Field: An identifier with a name using which, a declaration is
made in a Java class. It does have a default value and the field is also
present in the objects which are instances of the class.
4. Class: a class is a basic structural unit in a Java program. A class
consists of data fields and methods that operate on the fields. A class
is a group of objects with similar attributes and common behavior and
relationships. A class is used to create objects as its instances.
5. Inheritance: Java Class inherits members when a Java class is
extended from a parent class called super class. The inherited instance
fields and methods can be overridden by redefining them in extended
MBCCET, PEERMADE, ECE DPT 19
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
class. Methods can be overloaded by redefining them for different
number of arguments
6. Interface: Interface has only abstract methods and corresponding
data fields. Methods do not have implementation at the Interface. A
Java class which is interfaced to an Interface, implements the abstract
methods specified at the Interface.
7. Data Types: Java Class uses primitive data types: Byte (8-bit), shot (16-
bit), int (32-bit, long (64-bit, float, double, char (16-bit). Java Class uses
reference data types. A reference can be Class type in which there are
groups of fields and methods to operate on the fields. A reference can
be array type in which there are groups of objects as array elements.
8. Exception: Java has built-in exception classes. The occurrences of
exceptional conditions are handled when exception is thrown. It is also
possible to define exception conditions in a program so that exceptions
are thrown from try block codes and caught by catch-exception method.
Java Programming Advantages
1. Java is completely an OOP language. Java program starts with classes.
Application program consist of classes and interfaces.
2. There is a huge class library on the network that makes program
development quick.
3. Java has extensibility
KTUStudents.in
4. Java has in-built support for creating multiple threads. It obviates the
need for an operating system based scheduler for handling the task
5. Java generates the byte codes. These are executed on an installed JVM
(Java Virtual Machine) on a machine. Virtual machine takes the Java
byte codes in the input and runs on the given platform (processor,
system and OS ); virtual Machine (VM) in embedded systems is stored
at the ROM. Therefore, Java codes can host on diverse platforms.
Platform independence in hosting the compiled code permit java for
N/W applications.
6. Platform independence gives portability with respect to the processor
and the OS used. Java is considered as write once and run anywhere.
7. Java is the language for most Web applications and allows machines
of different types to communicate on the Web.
8. Java is easier to learn by C++ programmer.
9. Java does not permit pointer manipulation instructions. So it is robust
in the sense that memory leaks and memory related errors do not occur.
10. Java
does not permit dual way of object manipulation by value and reference.
There are no struc, enum, typedef and union.
11. Java
does not permit multiple inheritances and operator overloading, except
for + sign used for string concatenation
Java objects bind state and behavior by the instance of a Java class. Java
has large number Of readily available classes for the I/O stream, network and
security. Object-oriented features and ready availability of classes make a
MBCCET, PEERMADE, ECE DPT 20
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
large program development simpler task. JVM is configured to minimise
memory needs and runtime overheads in the system. Java programs possess
the ability to run under restricted permissions.
Disadvantages of Java
Java has following disadvantages for embedded programming as follows:
1. Since Java codes are first interpreted by the JVM, it runs comparatively
slowly. Java byte codes can be converted to native machine codes for
fast running using Just-In-Time (JIT) compilation.
2. Java byte codes that are generated need a larger memory. An embedded
Java system may need a minimum of 512 kB ROM and 512 kB RAM
because of the need to first install JVM and run the application.
Software Development Life Cycle (SDLC)
Software Development Life Cycle (SDLC) is a process used by the software
industry to design, develop and test high quality software’s. The SDLC aims
to produce a high-quality software that meets or exceeds customer
expectations, reaches completion within times and cost estimates.
SDLC is the acronym of Software Development Life Cycle.
It is also called as Software Development Process.
SDLC is a framework defining tasks performed at each step in the
KTUStudents.in
software development
process.
ISO/IEC 12207 is an international standard for software life-cycle
processes. It aims to be
the standard that defines all the tasks required for developing and
maintaining software.
SDLC is a process followed for a software project, within a software
organization. It consists of a detailed plan describing how to develop,
maintain, replace and alter or enhance specific software. The life cycle defines
a methodology for improving the quality of software and the overall
development process.
Planning and Requirement Analysis
Requirement analysis is the most important and fundamental stage in SDLC.
It is performed by the senior members of the team with inputs from the
MBCCET, PEERMADE, ECE DPT 21
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
customer, the sales department, market surveys and domain experts in the
industry. This information is then used to plan the basic project approach
and to conduct product feasibility study in the economical, operational and
technical areas. Planning for the quality assurance requirements and
identification of the risks associated with the project is also done in the
planning stage. The outcome of the technical feasibility study is to define the
various technical approaches that can be followed to implement the project
successfully with minimum risks.
Defining Requirements
Once the requirement analysis is done the next step is to clearly define and
document the product requirements and get them approved from the
customer or the market analysts. This is done through an SRS (Software
Requirement Specification) document which consists of all the product
requirements to be designed and developed during the project life cycle.
Designing the Product Architecture
SRS is the reference for product architects to come out with the best
architecture for the product to be developed. Based on the requirements
specified in SRS, usually more than one design approach for the product
architecture is proposed and documented in a DDS - Design Document
Specification. This DDS is reviewed by all the important stakeholders and
KTUStudents.in
based on various parameters as risk assessment, product robustness, design
modularity, budget and time constraints, the best design approach is selected
for the product.
A design approach clearly defines all the architectural modules of the product
along with its communication and data flow representation with the external
and third party modules (if any). The internal design of all the modules of the
proposed architecture should be clearly defined with the minutest of the
details in DDS.
Building or Developing the Product
In this stage of SDLC the actual development starts and the product is built.
The programming code is generated as per DDS during this stage. If the design
is performed in a detailed and organized manner, code generation can be
accomplished without much hassle. Developers must follow the coding
guidelines defined by their organization and programming tools like
compilers, interpreters, debuggers, etc. are used to generate the code.
Different high level programming languages such as C, C++, Pascal, Java and
PHP are used for coding. The programming language is chosen with respect
to the type of software being developed.
Testing the Product
This stage is usually a subset of all the stages as in the modern SDLC models,
the testing activities are mostly involved in all the stages of SDLC. However,
this stage refers to the testing only stage of the product where product defects
are reported, tracked, fixed and retested, until the product reaches the quality
standards defined in the SRS.
MBCCET, PEERMADE, ECE DPT 22
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
Deployment in the Market and Maintenance
Once the product is tested and ready to be deployed it is released formally in
the appropriate market. Sometimes product deployment happens in stages as
per the business strategy of that organization. The product may first be
released in a limited segment and tested in the real business environment
(UAT- User acceptance testing).
Embedded Software Testing
Testing is the process of evaluating a system or its component(s) with the
intent to find whether it satisfies the specified requirements or not. In simple
words, testing is executing a system in order to identify any gaps, errors, or
missing requirements in contrary to the actual requirements.
STLC - Software Testing Life Cycle
Software Testing Life Cycle (STLC) is defined as a sequence of activities
conducted to perform Software Testing. It consists of series of activities
carried out methodologically to help certify your software product.
KTUStudents.in
Each of these stages have a definite Entry and Exit criteria; , Activities &
Deliverables associated with it.
Entry Criteria: Entry Criteria gives the prerequisite items that must be
completed before testing can begin.
Exit Criteria: Exit Criteria defines the items that must be completed before
testing can be concluded
Requirement Analysis
During this phase, test team studies the requirements from a testing point of
view to identify the testable requirements. The QA team may interact with
various stakeholders (Client, Business Analyst, Technical Leads, System
Architects etc) to understand the requirements in detail. Requirements could
be either Functional (defining what the software must do) or Non Functional
(defining system performance /security availability) .Automation feasibility for
the given testing project is also done in this stage.
MBCCET, PEERMADE, ECE DPT 23
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
Activities
Identify types of tests to be performed.
Gather details about testing priorities and focus.
Prepare Requirement Traceability Matrix (RTM).
Identify test environment details where testing is supposed to be carried
out.
Automation feasibility analysis (if required).
Test Planning
Typically, in this stage, a Senior QA manager will determine effort and cost
estimates for the project and would prepare and finalize the Test Plan. In this
phase, Test Strategy is also determined.
Activities
Preparation of test plan/strategy document for various types of testing
Test tool selection
Test effort estimation
Resource planning and determining roles and responsibilities.
Training requirement
Test Case Development
KTUStudents.in
This phase involves creation, verification and rework of test cases & test
scripts. Test data , is identified/created and is reviewed and then reworked
as well.
Activities
Create test cases, automation scripts (if applicable)
Review and baseline test cases and scripts
Create test data (If Test Environment is available)
Test Environment Setup
Test environment decides the software and hardware conditions under which
a work product is tested. Test environment set-up is one of the critical aspects
of testing process and can be done in parallel with Test Case Development
Stage. Test team may not be involved in this activity if the
customer/development team provides the test environment in which case the
test team is required to do a readiness check (smoke testing) of the given
environment.
Activities
Understand the required architecture, environment set-up and prepare
hardware and
software requirement list for the Test Environment.
Setup test Environment and test data
Perform smoke test on the build
MBCCET, PEERMADE, ECE DPT 24
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
Test Execution
During this phase the testers will carry out the testing based on the test plans
and the test cases prepared. Bugs will be reported back to the development
team for correction and retesting will be performed.
Activities
Execute tests as per plan
Document test results, and log defects for failed cases
Map defects to test cases in RTM
Retest the Defect fixes
Track the defects to closure
Test Cycle Closure
Testing team will meet, discuss and analyse testing artefacts to identify
strategies that have to be implemented in future, taking lessons from the
current test cycle. The idea is to remove the process bottlenecks for future
test cycles and share best practices for any similar projects in future.
Activities
Evaluate cycle completion criteria based on Time, Test coverage, Cost,
Software, Critical
KTUStudents.in
Business Objectives, Quality
Prepare test metrics based on the above parameters.
Document the learning out of the project
Prepare Test closure report
Qualitative and quantitative reporting of quality of the work product to
the customer.
Test result analysis to find out the defect distribution by type and
severity.
Type of testing strategies
1. Black-Box Testing
The technique of testing without having any knowledge of the interior
workings of the application is called black-box testing. The tester is oblivious
to the system architecture and does not have access to the source code.
Typically, while performing a black-box test, a tester will interact with the
system's user interface by providing inputs and examining outputs without
knowing how and where the inputs are worked upon.The following table lists
the advantages and disadvantages of black-box testing.
Advantages
Well suited and efficient for large code segments.
Code access is not required.
Clearly separates user's perspective from the developer's perspective
through visibly defined roles.
MBCCET, PEERMADE, ECE DPT 25
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
Large numbers of moderately skilled testers can test the application
with no knowledge of implementation, programming language, or
operating systems.
Disadvantages
Limited coverage, since only a selected number of test scenarios is
actually performed.
Inefficient testing, due to the fact that the tester only has limited
knowledge about an application.
Blind coverage, since the tester cannot target specific code segments or
error prone areas.
The test cases are difficult to design.
2. White-Box Testing
White-box testing is the detailed investigation of internal logic and structure
of the code. White-box testing is also called glass testing or open-box testing.
In order to perform white-box testing on an application, a tester needs to know
the internal workings of the code. The tester needs to have a look inside the
source code and find out which unit/chunk of the code is behaving
inappropriately.
KTUStudents.in
The following table lists the advantages and disadvantages of white-box
testing.
Advantages
As the tester has knowledge of the source code, it becomes very easy to
find out which type of data can help in testing the application effectively.
It helps in optimizing the code.
Extra lines of code can be removed which can bring in hidden defects.
Due to the tester's knowledge about the code, maximum coverage is
attained during test scenario writing.
Disadvantages
Due to the fact that a skilled tester is needed to perform white-box
testing, the costs are increased.
Sometimes it is impossible to look into every nook and corner to find
out hidden errors that may create problems, as many paths will go
untested.
It is difficult to maintain white-box testing, as it requires specialized
tools like code analyzers and debugging tools.
3. Grey-Box Testing
Grey-box testing is a technique to test the application with having a limited
knowledge of the internal workings of an application. In software testing, the
MBCCET, PEERMADE, ECE DPT 26
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
phrase the more you know, the better carries a lot of weight while testing an
application.
Mastering the domain of a system always gives the tester an edge over
someone with limited domain knowledge. Unlike black-box testing, where the
tester only tests the application's user interface; in grey-box testing, the tester
has access to design documents and the database. Having this knowledge, a
tester can prepare better test data and test scenarios while making a test plan.
Advantages
Offers combined benefits of black-box and white-box testing wherever
possible.
Grey box testers don't rely on the source code; instead they rely on
interface definition and functional specifications.
Based on the limited information available, a grey-box tester can design
excellent test scenarios especially around communication protocols and
data type handling.
The test is done from the point of view of the user and not the designer.
Disadvantages
Since the access to source code is not available, the ability to go over
the code and test coverage is limited.
KTUStudents.in
The tests can be redundant if the software designer has already run a
test case.
Testing every possible input stream is unrealistic because it would take
an unreasonable amount of time; therefore, many program paths will
go untested.
The following table lists the points that differentiate black-box testing, grey-
box testing, and white-box testing.
MBCCET, PEERMADE, ECE DPT 27
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
Integration & Testing of Embedded Hardware
A detailed design process consists of integration of software into Hardware.
Integration and testing of embedded hardware give the embedded system'
Following figure shows a design development process for integration and
testing.
KTUStudents.in
Design for Testability
An embedded system developer needs to design for Hardware as well as
Software Testability. Hardware Testability means provisioning of input ports
and output ports during designing such that the Hardware can be tested for
any fault in assembly. The developer considers software testability of the
software components and requirements
Testability is a degree to which it is possible to control and observe the states
and output of a component during testing. Software Testability means a
design such that it should be possible to test a system using the sets of data
or automate the test of the component under test.
Assert Macro: Use of assert macros is a method to incorporate testability in a
system. A macro is inserted to assert certain conditions so that effect or
output can be tested. The use of an assert macro is an important test
technique. We can use the assert macro at different critical places in the
application program.
MBCCET, PEERMADE, ECE DPT 28
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
Design of Self-Test: Self-test means that a system performs the tests for all
the functions expected on its own. The developer writes self-tests. A self-test
enables to test the specified functions of a system.
Testing on Host Machine
The system embeds three types of codes such as
l. Host-dependent
2. Target-independent
3. Target-dependent codes.
Following figure shows the test system in a development process, which
consists of host and target Hardware systems.
KTUStudents.in
We have two computing systems such as host and target. Each has a distinct
CPU or microcontroller. Hardware architecture of each is also distinct. The
host is generally a workstation, PC or laptop. The target is actual Hardware
for the embedded system, which is in the development phase. dependent
codes and test systems in a development process. Testing and debugging are
required at each stage as well as at the final stage when the modules integrate
together. Initial stage tests are done on the host machine. The developer tests
hardware-independent codes on a host machine. A simulator is then run on
the host. codes have two parts
l. Hardware-independent codes.
2. Hardware-dependent codes.
DEBUGGING
Debugging is the process of checking the errors and correcting those errors.
Software debugging can be done by compiling and executing the code on a PC
or workstation. Debugging can be performed in two sides, one is the software
side and another one is the Hardware side for both sides many debugging
tools are involved.
MBCCET, PEERMADE, ECE DPT 29
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
TYPES OF SOFTWARE DEBUGGING TOOLS
There are two types of software debugging tools are available.
l. Serial Port tool
2. Break point tool
Serial Port Tool (USB) : The serial port debugging Tool is the most important
debugging tools. This tool will perform the debugging process from the initial
state of embedded system design. The serial port can be used not only for
development debugging but also for solving problems in the field.
Break Point Tool : Break point tool is the most important tool in which user
to specify an address where the programs execution is to break. Once the PC
reaches that address, control is returned to the monitor program. From the
monitor program, the user can examine or modify CPU registers, after that
the process can be continued.
Advantage
Implementing break points does not require any external devices.
TYPES OF HARDWARE DEBUGGING TOOLS
When Software tools are inefficient to debug the system, Hardware tools will
KTUStudents.in
be used. Hardware tools clearly mention what is happening in the system and
when the system is running. As like software tolls it has the following tools.
I. Microprocessor In- Circuit Emulator (ICE)
2. Logic Analyzer
Microprocessor In-Circuit Emulator
The Microprocessor in circuit emulator is a specialized Hardware tool that can
help debug software in a working embedded system. In circuit emulator is a
special version of the microprocessor that has internal registers it will be read
out when it is stopped. The CPU provides as much debugging functionality
without any memory utilization.
Drawbacks
l. In- circuit emulator machine is must specific to a particular microprocessor.
2. Several microprocessors used means maintaining a fleet of in-circuit
emulators can be very expensive.
Logic Analyzer
The logic analyzer can sample many different signals simultaneously but can
display only 0, 1 or changing values for each. The logic analyzer records the
values on the into an internal memory and then displays the results on a
display once the memory is full or the run is aborted.
The logic Analyzer can capture thousands or even millions of samples of data
on all of these channels and providing a much larger time window into the
MBCCET, PEERMADE, ECE DPT 30
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
operation of the machine than is possible a conventional oscilloscope. Data is
having two kinds of modes.
Data modes of Logic Analyzer
1. State mode
2. Timing mode
(i) State Mode: State mode represents different ways of sampling the values.
State mode uses the systems own clock to control sampling. It samples each
signal only once per clock cycle. State mode having less memory to store a
given number of system clock cycles, It is used for sequentially oriented
problems.
(ii) Timing Mode: Timing mode represents different ways of sampling the
values. Timing mode uses an internal clock and it is fast to take several
samples per clock period in a typical system.
Timing mode requires more memory to store a given number Of system clock
cycles and it is used for glitch oriented debugging problems.
Drawback of logic analyzer
The logic Analyzer does not provide access to the internal state of the
KTUStudents.in
components. But it gives a very good view of the externally visible signals, that
information can be used for both Functional and timing debugging.
DEBUGGING CHALLENGES
Logical errors in software can be hard to track down and it will create
many problems in real time code.
Real Time programs are required to finish their work within a certain
amount of time.
Real time programs run too long means -it creates very unexpected
behavior.
The exact results of missing real time deadlines is it depends on the
detailed characteristics of the I/O devices.
Missing of deadline makes debugging process as difficult.
DEBUGGING TECHNIQUES
Simulator
A simulator helps in the development of the system before the final target
system is ready with only a PC as the tool for development. Simulators are
readily available for different processors and processing devices employing
embedded systems. System designer and /or developer need not code for the
simulator for application software and hardware development in the design
laboratory.
The simulator uses knowledge of target processor or microcontroller, and
target system architecture on the host processor. The simulator first does
cross complication of the codes and places these into the host-system RAM.
The behavior of processor registers in a target system is also simulated in the
MBCCET, PEERMADE, ECE DPT 31
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
RAM. The simulator software also simulates hardware units like emulator,
peripherals, network and input-output devices on a host. A simulator remains
independent of a particular target system. It is useful during the development
phase for, application software for the system that is expected to employ a
particular processor, microcontroller or device.
Simulator Features:
It defines the processor or processing device family as well as its various
versions for the target system. It monitors the detailed information of a source
code part with labels and symbolic arguments as the execution goes on for
each single step. It provides the detailed information of the status of RAM and
ports Of the defined target system as the execution goes on for each single
step. It provides the detailed information of the status of peripheral devices
with the defined system.
It helps the window on the screen to provide the detailed meaning Of the
present command. It supports the conditions and unconditional break points.
It facilitates synchronizing the internal peripherals and delays. It provides a
network driver and device-driver support. It employs an RTOS scheduler that
preempts tasks.
Validation
KTUStudents.in
The process of evaluating software during the development process or at the
end of the development process to determine whether it satisfies specified
business requirements.
Validation Testing ensures that the product actually meets the client's needs.
It can also be defined as to demonstrate that the product fulfils its intended
use when deployed on appropriate environment.
MBCCET, PEERMADE, ECE DPT 32
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
Unit Testing :A level of the software testing process where individual units of
software are tested. The purpose is to validate that each unit of the software
performs as designed.
Integration Testing: A level of the software testing process where individual
KTUStudents.in
units are combined and tested as a group. The purpose of this level of testing
is to expose faults in the interaction between integrated units.
System Testing : A level of the software testing process where a complete,
integrated system is tested. The purpose of this test is to evaluate the system’s
compliance with the specified requirements.
Acceptance Testing: A level of the software testing process where a system
is tested for acceptability. The purpose of this test is to evaluate the system’s
compliance with the business requirements and assess whether it is
acceptable for delivery.
SYSTEM-ON-CHIP (SOC)
There are two approaches to design an embedded system such as
1. Using System-on-Chip (SOC)
2. Using chips on a circuit Board (COB)
System-on-chip approach is used for extensively used systems, for example,
mobile phone and cameras.
In chips on. a circuit board approach, separate chips for the microprocessor
or ASIP, memory, single-purpose processors and peripherals are
interconnected on a board.
All chips interface with an appropriate circuit. The chips interconnect on a
board and software embeds into memory in a chip.
MBCCET, PEERMADE, ECE DPT 33
For more study materials: WWW.KTUSTUDENTS.IN
MODULE 4 EMBEDDED SYSTEM
A complex embedded system is designed on a single silicon chip consisting of
multiple processors, hardware units and the software. System-on-chip is a
design innovation for the embedded systems.
System-on-chip is a system on a VLSI chip that has multiple processors,
software and all the needed digital as well as analog circuits on the chip. SOC
embeds software, specific to dedicated application(s) and may have the Analog
circuits. SOC may embed the following interconnected components on the
chip,
1. Embedded General Purpose Processor (CPU)
2. Embedded Application Specific Instruction Set Processor (ASIP) with
instruction set of microcontroller or digital signal processor or graphic
processor.
3. ASIPs with instruction set designed for specific application units in the
system.
4. Single purpose processors
5. Multiple processors
6. Cache, RAM and Flash memory
7. Multiple standard source solutions, called IP (Intellectual property)
cores.
8. Circuits for special functions or single purpose using Application
Specific Integrated Circuit (ASICs).
KTUStudents.in
9. Other logic circuits and Analog units.
Advantages of SOC:
The system has very high performance, functionalities and very low power
dissipation. Therefore, SoCs are used in Embedded systems, which are
extensively and commonly used, need the small size, high system
performance, much functionality, very low power dissipation and have low
energy consumption. Examples of extensively used systems are mobile
phones, tablets, personal computers, Set-top boxes, digital TVs and cameras.
MBCCET, PEERMADE, ECE DPT 34
For more study materials: WWW.KTUSTUDENTS.IN
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5813)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1092)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (844)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (897)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (540)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (348)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (822)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (401)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- PHP A Visual BlueprintDocument132 pagesPHP A Visual Blueprintrjoffray100% (1)
- GUI Programming - Java Programming TutorialDocument52 pagesGUI Programming - Java Programming TutorialRanjith M KumarNo ratings yet
- Top 50 Java Design Pattern Interview QuestionsDocument67 pagesTop 50 Java Design Pattern Interview QuestionsАлекс ПолNo ratings yet
- What's Happeni Explore Notifications Messages Bookmarks Lists Profile MoreDocument19 pagesWhat's Happeni Explore Notifications Messages Bookmarks Lists Profile MoreVishnu Prasad MNo ratings yet
- 4 R 67 Bto 67 QTBR 8 T 37 o 87 T 4 Orfn 78 Ygh 8 o 7 HodfklsuDocument29 pages4 R 67 Bto 67 QTBR 8 T 37 o 87 T 4 Orfn 78 Ygh 8 o 7 HodfklsuVishnu Prasad MNo ratings yet
- Connect. Organize. Get Things DoneDocument13 pagesConnect. Organize. Get Things DoneVishnu Prasad MNo ratings yet
- Dashboard: Interview Preparation Kit Add Your First SkillDocument2 pagesDashboard: Interview Preparation Kit Add Your First SkillVishnu Prasad MNo ratings yet
- 4 R 67 Bto 67 QTBR 8 T 37 o 87 T 4 Orfn 78 Ygh 8 o 7 HodfklsuDocument18 pages4 R 67 Bto 67 QTBR 8 T 37 o 87 T 4 Orfn 78 Ygh 8 o 7 HodfklsuVishnu Prasad MNo ratings yet
- DC Mod 6 Ktunotes - inDocument24 pagesDC Mod 6 Ktunotes - inVishnu Prasad MNo ratings yet
- Ktustudents - In: Ec 308 Embedded Systems Module-6Document12 pagesKtustudents - In: Ec 308 Embedded Systems Module-6Vishnu Prasad MNo ratings yet
- Ktustudents - In: Ec 308 Embedded Systems Module-5Document22 pagesKtustudents - In: Ec 308 Embedded Systems Module-5Vishnu Prasad MNo ratings yet
- Ktustudents - In: Ec 308 Embedded Systems Module-3Document21 pagesKtustudents - In: Ec 308 Embedded Systems Module-3Vishnu Prasad MNo ratings yet
- Ktustudents - In: Ec 308 Embedded Systems Module-2Document16 pagesKtustudents - In: Ec 308 Embedded Systems Module-2Vishnu Prasad MNo ratings yet
- For More Study Materials: WWW - KTUSTUDENTS.INDocument16 pagesFor More Study Materials: WWW - KTUSTUDENTS.INVishnu Prasad MNo ratings yet
- Hibernate PracticalsDocument49 pagesHibernate PracticalsTamil kutty videosNo ratings yet
- The F Survival Guide PDFDocument136 pagesThe F Survival Guide PDFAdna KarkeLjaNo ratings yet
- Course PackDocument267 pagesCourse PackZaw HtetNo ratings yet
- Block-1 Application Development Life Cycle PDFDocument143 pagesBlock-1 Application Development Life Cycle PDFArpit ShahNo ratings yet
- Java Programming For BeginnersDocument3 pagesJava Programming For Beginnersazphyo100% (1)
- MVC ExampleDocument4 pagesMVC ExampleTran Duc Duy (K16HL)No ratings yet
- Lecture 1 - OOP PHPDocument27 pagesLecture 1 - OOP PHPJisun AurnobNo ratings yet
- Lesson09 - Exercises (PS11-12 Hoh Jungi)Document4 pagesLesson09 - Exercises (PS11-12 Hoh Jungi)Jungi HohNo ratings yet
- Intro To Expert SystemDocument39 pagesIntro To Expert Systemme_mumuNo ratings yet
- Jinendra Major ProjectDocument127 pagesJinendra Major ProjectArham KhanNo ratings yet
- Why Main Method Is Public Static in Java PDFDocument6 pagesWhy Main Method Is Public Static in Java PDFPhanidhar S GadiyaramNo ratings yet
- COMP1406 Course Notes: Introduction To Computer Science IIDocument3 pagesCOMP1406 Course Notes: Introduction To Computer Science IINoraniah Abd AzizNo ratings yet
- C++ Notes For Discussion - ..Document3 pagesC++ Notes For Discussion - ..vkhawareyNo ratings yet
- Constructors Continued : ReviewDocument40 pagesConstructors Continued : ReviewVijay KumarNo ratings yet
- Object Oriented JavaScriptDocument15 pagesObject Oriented JavaScripts10_sharmaNo ratings yet
- Learn Al LanguageDocument160 pagesLearn Al Languageraoravinder714No ratings yet
- KisahuDocument8 pagesKisahukishanmayappaNo ratings yet
- Hacking Hacking Practical Guide For Beginners (Hacking With Python) (PDFDrive)Document94 pagesHacking Hacking Practical Guide For Beginners (Hacking With Python) (PDFDrive)Asif Ahammed50% (2)
- Oda Bultum UniverstyDocument64 pagesOda Bultum Universtyidrisabdurazek0123No ratings yet
- Component-Based Software EngineeringDocument48 pagesComponent-Based Software EngineeringHarshavardhan Virendra MallaNo ratings yet
- String يضِشٌا طٍخٌا: Chapter TwoDocument5 pagesString يضِشٌا طٍخٌا: Chapter TwoMAHMOUD CERAYNo ratings yet
- Week-02 Assignment - 2023 UpdatedDocument5 pagesWeek-02 Assignment - 2023 UpdatedPrabha KNo ratings yet
- Design Patterns For Simulations in ErlangDocument72 pagesDesign Patterns For Simulations in ErlangSkyezine Via Kit Fox0% (1)
- 1923 B.E Eee Batchno Intern 54Document34 pages1923 B.E Eee Batchno Intern 54VickyNo ratings yet
- FS Program5Document5 pagesFS Program5RanjithaRanjuNo ratings yet
- Java Exception Handling NotesDocument31 pagesJava Exception Handling NotesBSKNo ratings yet
- IMP Qestion Answers AJP PDFDocument771 pagesIMP Qestion Answers AJP PDFAtharva Nitin ChandwadkarNo ratings yet