Professional Documents
Culture Documents
Ip Oct R1 25
Uploaded by
rizwana fathima0 ratings0% found this document useful (0 votes)
6 views2 pagesOriginal Title
IP_OCT_R1_25
Copyright
© © All Rights Reserved
Available Formats
DOCX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
6 views2 pagesIp Oct R1 25
Uploaded by
rizwana fathimaCopyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
You are on page 1of 2
QP CODE
VEL’S PUBLIC SCHOOL,SANKARANKOVIL IP251021
GRADE-XII
REVISION TEST
MAX TIME : 90 MINS 065-INFORMATICS PRACTICES MAX MARKS:35
SECTION-A
ANSWER ALL THE 15 QUESTIONS
Q1. Digital footprints are also known as _____________
a. Digital data b. Plagiarism c. Digital tattoos d. Digital print
Q2. Proprietary software is a software which is available _________
a. free of charge b. on paying license fee c. free for first year only d. None of the above
Q3. Which of the following is not a cyber crime?
a. Phishing b. Ransomware c. Hacking d. Tracking
Q4. In India _______ law provides guidelines to the user on the processing, storage and transmission of
sensitive information.
a. Information Technology Act, 2000 b. Indian Technology Act, 2000
c. Inform Technology Act, 2000 d. Information Techware Act, 2000
Q5. Communication etiquette include to _____
a. be polite with others b. be credible c. be precise d. All of the above
Q6. Which of the following is an example of Social media?
a. Facebook b. Twitter c. Instagram d. All of the above
Q7. ________ are websites or applications that enable users to participate by creating and sharing content
with others in the community.
a. Social media b. Social channel c. Social networking d. None of the above
Q8. In social media platform, we can share _____________
a. Images b. text c. videos d. All of the above
Q9. Is having the same password for all your accounts on different websites is safe?(T/F)
a. True b. False
Q10. To be a responsible netizen, we should ___________
a. Choose password wisely b. think before uploading anything online.
c. change our password frequently. d. All of the above
Q11. Example of sensitive data is ___________
a. Name of a person b. Credit card detail of a person c. Date of birth of a person d. None
Q12. IPR stands for ______________
a. Indian Property Right b. Intellectual Property Right
c. Intelligent Property Right d. Intellectual Property Resource
Q13. The ____________ include right to copy (reproduce) a work, right to distribute copies of the work to
the public, and right to publicly display or perform the work.
a. Copyright b. Patent c. Createright d. None of the above
Q14. Patentee has the full right of using, selling, or distributing the protected invention.(T/F)
a. True b. False
Q15. _________________covers all clauses of software purchase, viz., how many copies can be installed,
whether source is available, whether it can be modified and redistributed and so on.
a. EULA b. EULE c. AULA d. AULI
Q16. _____________ means unauthorized use of other’s trademark on products and services.
a. Copyright Infringement b. Trademark Infringement c. Plagiarism d. Patent
Q17. Which of the following is a popular category of public licenses?
a. GPL b. CC c. Both of the above d. None of the above
Q18. GPL is primarily designed for providing public license to a ______
a. Software b. websites c. literature d. music
Q19. ____________ operating system come under FOSS.
a. Ubuntu b. Unix c. Mac d. Windows
Q20. _______ is defined as a crime in which computer is the medium of crime.
a. Computer crime b. Cyber crime c. Internet crime d. Digital crime
Q21. Which of the following is cyber crime?
a. Hacking b. Phishing c. Spamming d. All of the above
Q22. A ___________ is some lines of malicious code that can copy itself and can have detrimental effect on
the computers, by destroying data or corrupting the system.
a. Cyber crime b. Computer virus c. Program d. Software
Q23. Primary focus of ________ is on security cracking and data stealing.
a. ethical hacker b. non ethical hacker c. white hat hacker d. None of the above
Q24. Hackers try to break security system ___________
a. for Identity theft b. for monetary gain c. to leak sensitive information d. All of the above
Q25. ______________ is an activity where fake websites or emails that look original or authentic are
presented to the user.
a. Phishing b. Hacking c. Spamming d. Identity theft
Q26. e-waste is responsible for the degradation of our environment.(T/F)
a. True b. False
Q27. Which of the following are feasible methods of e-waste management?
a. Reduce b. Reuse c. Recycle d. All of the above
Q28. ____________ is a branch of science that deals with designing or arranging workplaces including the
furniture, equipment and systems so that it becomes safe and comfortable for the user.
a. Ergonomics b. Ergomics c. Agonomics d. All of the above
Q29. What do we have to ensure to maintain the good health of a computer system?
a. Wipe monitor’s screen often using the regular microfiber soft cloth.
b. Keep it away from direct heat, sunlight and put it in a room with enough ventilation for air
circulation.
c. Do not eat food or drink over the keyboard
d. All of the above
Q30. Being a responsible digital citizen, we should ______
a. not use copyrighted materials b. avoid cyberbullying
c. respect privacy of others d. All of the above
Q31. Online posting of rumours, giving threats online, posting the victim’s personal information, comments
aimed to publicly ridicule a victim is termed as __________
a. Cyber bullying b. Cyber crime c. Cyber insult d. All of the above
Q32. _______ is a person who deliberately sows discord on the Internet by starting quarrels or upsetting
people, by posting inflammatory or off topic messages in an online community.
a. Netizen b. Digital Citizen c. Internet troll d. None of the above
Q33. Digital communication includes ________
a. Email b. Texting c. Instant messaging d. All of the above
Q34. Rishika found a crumpled paper under her desk. She picked it up and opened it. It contained some text
which was struck off thrice. But she could still figure out easily that the struck off text was the email ID and
password of Garvit , her classmate. What is ethically correct for Rishika to do?
a. Inform Garvit so that he may change his password
b. Give the password of Garvit’s email ID to all other classmates
c. Use Garvit’s password to access his account
d. None of the above
Q35. Ravi downloaded a software from the internet (free of cost) and moreover the source code of the
software is also available which can be modified. What category of software is this?
a. Shareware b. Freeware c. FOSS d. Malware
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5796)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1091)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (589)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (345)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (400)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- CyberArk EPM OverviewDocument9 pagesCyberArk EPM OverviewSohitNo ratings yet
- Vel'S Public School, Sankarankovil Informatics Practices (065) Worksheet-2 Unit-2: Database Query Using SQLDocument6 pagesVel'S Public School, Sankarankovil Informatics Practices (065) Worksheet-2 Unit-2: Database Query Using SQLrizwana fathima0% (1)
- Calls - SECMETDocument138 pagesCalls - SECMETgaju6190% (1)
- Creation of Series Using List, Dictionary & NdarrayDocument65 pagesCreation of Series Using List, Dictionary & Ndarrayrizwana fathimaNo ratings yet
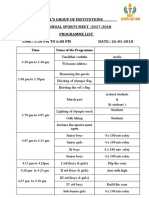
- Vel'S Group of Institutions 4 ANNUAL SPORTS MEET - 2017-2018 Programme List Time: 3.30 PM To 6.00 PM Date: 26-01-2018Document2 pagesVel'S Group of Institutions 4 ANNUAL SPORTS MEET - 2017-2018 Programme List Time: 3.30 PM To 6.00 PM Date: 26-01-2018rizwana fathimaNo ratings yet
- GR 12 Program ListDocument14 pagesGR 12 Program Listrizwana fathimaNo ratings yet
- Sports Day Schedule For 2016Document3 pagesSports Day Schedule For 2016rizwana fathimaNo ratings yet
- Societal Impact - HotsDocument6 pagesSocietal Impact - Hotsrizwana fathimaNo ratings yet
- Worksheey Grade ViiDocument36 pagesWorksheey Grade Viirizwana fathimaNo ratings yet
- Read The Passages Given Below and Answer The Questions That Follow Each of ThemDocument60 pagesRead The Passages Given Below and Answer The Questions That Follow Each of Themrizwana fathima0% (1)
- Print (Sequences Head (4) )Document3 pagesPrint (Sequences Head (4) )rizwana fathimaNo ratings yet
- SQL Functions: Assignments QDocument4 pagesSQL Functions: Assignments Qrizwana fathimaNo ratings yet
- Grxii-St 8-Python-Bio - IpDocument1 pageGrxii-St 8-Python-Bio - Iprizwana fathimaNo ratings yet
- Lots Question Bank: Objective Type QuestionsDocument3 pagesLots Question Bank: Objective Type Questionsrizwana fathima100% (1)
- HOTs Questions On Computer NetworkDocument1 pageHOTs Questions On Computer Networkrizwana fathimaNo ratings yet
- Worksheet-1 (Python)Document9 pagesWorksheet-1 (Python)rizwana fathimaNo ratings yet
- Authors Name Starting WithDocument3 pagesAuthors Name Starting Withrizwana fathimaNo ratings yet
- Computer Networks: What Is Computer Network?Document12 pagesComputer Networks: What Is Computer Network?rizwana fathimaNo ratings yet
- I Tamil WorksheetDocument3 pagesI Tamil Worksheetrizwana fathimaNo ratings yet
- Transformer Protection Using Microcontroller Based Relay & Monitoring Using GSM Technology PDFDocument5 pagesTransformer Protection Using Microcontroller Based Relay & Monitoring Using GSM Technology PDFrizwana fathima100% (1)
- Demo Exercise Class 11Document19 pagesDemo Exercise Class 11rizwana fathimaNo ratings yet
- Case Study On Social Engineering Techniques For PersuasionDocument7 pagesCase Study On Social Engineering Techniques For PersuasionMegan BellNo ratings yet
- Software ValidationDocument36 pagesSoftware ValidationHilario AlinabonNo ratings yet
- 1822 B.tech It Batchno 364Document34 pages1822 B.tech It Batchno 364StArK ツKuNuNo ratings yet
- Smart Contract Automated Testing GuidelinesDocument7 pagesSmart Contract Automated Testing GuidelinesloclubuNo ratings yet
- Session 1 ICS Basics - Q and ADocument5 pagesSession 1 ICS Basics - Q and ARocKetNo ratings yet
- Compliance Reference Card - PPDDocument4 pagesCompliance Reference Card - PPDDJ KetersonNo ratings yet
- WWW - tcs-CA - Tcs.co - in Index - JSP LeftHtml HTML Faqsleft - HTDocument9 pagesWWW - tcs-CA - Tcs.co - in Index - JSP LeftHtml HTML Faqsleft - HTsumitsemwalNo ratings yet
- Emerging Cybersecurity TechnologiesDocument14 pagesEmerging Cybersecurity TechnologieslukownNo ratings yet
- Social Engineering For Pentester PenTest - 02 - 2013Document81 pagesSocial Engineering For Pentester PenTest - 02 - 2013Black RainNo ratings yet
- Cybersecurity, Risk Management, and Financial CrimeDocument12 pagesCybersecurity, Risk Management, and Financial CrimeErnesa Novita50% (2)
- A Guide To Security PolicyDocument30 pagesA Guide To Security PolicyAnju JaiswalNo ratings yet
- Azure Active Directory Identity ProtectionDocument162 pagesAzure Active Directory Identity ProtectionstaffdewaNo ratings yet
- 2023 Phishing by Industry Benchmarking ReportDocument3 pages2023 Phishing by Industry Benchmarking ReporttalpurfaisalNo ratings yet
- G 33 KeymgmtDocument20 pagesG 33 KeymgmtDevashish NigamNo ratings yet
- Module 1Document86 pagesModule 1deepika vettikuntlaNo ratings yet
- ANH 10COBAN - Ma de Thu 2Document6 pagesANH 10COBAN - Ma de Thu 2nguyễn ngânNo ratings yet
- IT Security Manager For Windows - DeskmanDocument5 pagesIT Security Manager For Windows - DeskmanwedfgdsNo ratings yet
- Free ISC2 CISSP Sample Questions and Study Guide - EDUSUM - EDUSUMDocument3 pagesFree ISC2 CISSP Sample Questions and Study Guide - EDUSUM - EDUSUMFlorin ConduratNo ratings yet
- Platform AssignmentDocument7 pagesPlatform AssignmentDhivyadharshini Neelakandan100% (1)
- Sunmi KLD KeyManagement V2.101Document7 pagesSunmi KLD KeyManagement V2.101pratimNo ratings yet
- Ai Compliance in ControlDocument16 pagesAi Compliance in ControlYasir ButtNo ratings yet
- North Field East Project Onshore LNG FacilitiesDocument87 pagesNorth Field East Project Onshore LNG FacilitiesMohammed Moulan sayyedNo ratings yet
- Nipper Users Guide 2 13 0Document50 pagesNipper Users Guide 2 13 0Nguyễn Văn CườngNo ratings yet
- A Novel Framework For Smart Cyber Defence A Deep-Dive Into Deep Learning Attacks and DefencesDocument22 pagesA Novel Framework For Smart Cyber Defence A Deep-Dive Into Deep Learning Attacks and DefencesnithyadheviNo ratings yet
- Ethical Hacking With Python ToolsDocument66 pagesEthical Hacking With Python Toolskorab korabNo ratings yet
- ISA49092 - Reporte Semanal - PC LINK S.A.C.-2023-10-02-0145 - 6513Document14 pagesISA49092 - Reporte Semanal - PC LINK S.A.C.-2023-10-02-0145 - 6513Rolando Contreras CuaresmaNo ratings yet
- Demystifying AI What Digital TransformationDocument25 pagesDemystifying AI What Digital TransformationNathaly BarriosNo ratings yet
- Smart Card IntroductionDocument6 pagesSmart Card IntroductionPRAVINITNo ratings yet