Professional Documents
Culture Documents
Anti Spoofing Techniques in Face Recognition
Uploaded by
Thành TouliverOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Anti Spoofing Techniques in Face Recognition
Uploaded by
Thành TouliverCopyright:
Available Formats
Table of Contents
Face recognition: How it works
Presentation attacks: An overview
PAD solutions: Top techniques
Hand crafted features: Local Binary Pattern
Finding the distinctions: Eye blink detection
Deep learning features: Convolutional Neural Network
Comparing actions: Challenge-response
Stable and reliable: 3D Camera
An answer: Active Flash
Overview Of Face Anti-spoofing Solutions
Measuring efficacy: Metrics
Preventing attacks: What’s next?
Anti-spoofing techniques in face recognition 1
Biometric face recognition technology is a key to security. Finding
someone’s photo or video on Facebook or Youtube is easy. These
images and videos can be used for ill intent. Face-based biometric
systems are vulnerable to attacks via paper photographs, screen replay
or 3D face reconstruction. A security system designed to prevent face
spoofing is important.
Following is an overview of presentation attacks and anti-spoofing
techniques powered by Machine
Learning.
Face recognition: How it works
Face identification and recognition is a process of comparing data
received from the camera to a database of known faces and finding the
match. See the video below for an example:
This general face recognition process is flawed. What if someone uses
a fake face? A liveness check counters this, distinguishing between a
real face and a picture.
Anti-spoofing techniques in face recognition 2
Presentation attacks: An overview
Attacks on a face recognition system are called Presentation Attacks, or
PA. These attacks can be sorted into the following categories:
Of course, as technologies evolve, so do presentation attacks.
3D spoofing is not a big problem yet. 2D spoofing is more widespread.
This puts the onus on detecting and preventing presentation attacks.
The requirements are precise. The product must:
- combat 2D attacks, static or dynamic
- use images, not videos
- work without user interaction
The objective: achieve maximum accuracy in minimum time while also
providing a user-friendly experience. A model meeting these
requirements would be easy to integrate with existing face recognition
systems.
Anti-spoofing techniques in face recognition 3
This video provides an overview of face recognition spoofing:
PAD solutions: Top techniques
Presentation attack detection (PAD) technology stacks include:
Tensorflow: An open-source framework for building and computing data
flowgraphs, allowing for the creation and training of neural networks for
any level of complexity
Keras: High-level neural network application programming interface, or
API, written in Python and capable of running on top of TensorFlow
Scikit-learn: Software machine learning library for the Python
programming language
OpenCV: An open-source computer vision and machine learning software
library
During research PyTorch was also used, a machine learning library used
for deep learning applications and natural language processing. While this
same abilities as Tensorflow, its ease of use and
framework has the
flexibility make it popular among researchers. Following is a detailed
overview of PAD solutions:
Anti-spoofing techniques in face recognition 4
Hand crafted features: Local Binary Pattern
Local Binary Pattern (LBP) is an anti-spoofing technique of texture image
analysis, thresholding image pixels according to their neighbors. An image
is split into small patches. All pixels are taken from around the center pixel
and subtracted. LBP is outdated and cannot be used against a large variety
of attacks. But it does have merit when used in combination with other
solutions.
A negative result means 0 and a positive means 1. The resulting sequence
of 0 and 1 (clockwise) is interpreted as a decimal number. The same
calculations are made for all pixels in the patch. A histogram is
constructed from the calculated values. This histogram is the texture
descriptor of the patch. Histograms from all patches are then
concatenated. That provides the feature descriptor of the image. It can be
fed into a Support Vector Machine or any other algorithm, thus making a
classification.
Anti-spoofing techniques in face recognition 5
Finding the distinctions: Eye blink detection
Natural blinking can reveal the difference between live and fake faces.
Humans blink an average of 15 to 30 times per minute. During a blink, the
eyes remain shut for about 250 milliseconds. Modern cameras record
videos with far smaller intervals between frames (50 milliseconds at 30
frames per second). Videos can be used to find frames showing the eyes
shut. Those frames then can be counted. Implementation of eye blink
detection can be based on face landmarks analysis and by calculating the
area of the eye regions. Deep learning can also be applied
for this task.
Deep learning features: Convolutional Neural Network
The development of convolutional neural networks (CNN) makes it natural
to think of anti-spoofing as a binary classification problem. But there is no
specific set of features the convolutional neural network would "see" and
"understand." The hope is that trained convolution kernels will detect
what human eyes can't
see.
For example, distortions, if there are any, in the left picture can't be seen.
Distortions are visible in the right picture, but they are so diverse and
the
dependent on the environmental conditions and device specifics that
network can't use the image to generalize.
Anti-spoofing techniques in face recognition 6
The network can work, but there's a high risk of overfit on the dataset. Face
anti-spoofing performance will be strong within a certain dataset, but the
network won't work in real conditions. A more viable solution is needed.
*The most accurate result will be achieved through a combination of
several solutions.
Anti-spoofing techniques in face recognition 7
Comparing actions: Challenge-response
Under this face recognition approach, a user is required to take a special
action called a challenge. The system ensures that required action was
taken. Usually, a group of actions is required to make the model reliable.
These actions can include smiles, expressions of emotions such as
sadness, surprise or head movements. These interactions require
significant time and are inconvenient for users.
Stable and reliable: 3D Camera
The most reliable anti-spoofing technique uses a 3D camera. Precise pixel
depth information provides high accuracy against presentation attacks.
The difference between a face and a flat shape is discernible. While 3D
attacks still cause difficulties, stable performance makes this technology
the most promising. It works with smartphones and web cameras.
Technologies that work with RGB images are preferable.
An answer: Active Flash
This meets all the requirements. It has no "black box problem." It allows
is to
for the detection of spoofing using light reflections on a face. The idea
change light environment by using the device screen as an additional
source of light. White area, which covers the screen, produces appropriate
reflection on the face.
Anti-spoofing techniques in face recognition 8
Here is an example with raw pixel difference. In such an artificial way, real
faces are distinguished from fake ones because of the differences in their
surfaces. Frames before and after active flashing provide the data sample
for training the network. Active flash helps separate and classify face
features.
Note: Although this model works regardless of how the head is turned (with
reasonable limits), proper alignment can increase accuracy.
*Each of these solutions is difficult to implement and takes time to
develop.The most accurate result will be achieved through a combination
of solutions.
Anti-spoofing techniques in face recognition 9
Techniques can be used both separately and in combination. Some
examples:
Overview Of Face Anti-spoofing Solutions
Approaches can be combined. Challenge-response and LBP is one
example. The first approach uses movements to determine face liveness.
The second ensures these movements are not shown on a flat screen.
Light reflection and challenge-response can be combined, showing
whether a face appears on a flat surface and whether it's a static mask or
3D print.
Anti-spoofing techniques in face recognition 10
Measuring efficacy: Metrics
The accuracy of an anti-spoofing system can and should be measured.
False Acceptance Rate (FAR) and False Rejection Rate (FRR), which are
common for biometric verification, are also used for anti-spoofing. Task
specifics define the metrics used to interpret errors. If the objective is to
catch every attack, FAR should be minimized. If a user-friendly experience
has higher priority, FRR becomes more important. If we visualize
probabilities in the following way we will see that 2 curves intersect at a
certain point. This point is Equal Error Rate and it helps to select the best
threshold value for decision making. Depending upon the security
requirements, we can move threshold value left or right giving an
advantage to FAR or FRR. In our case, smooth user experience was more
important so we adjusted the threshold value in order to minimize FRR.
Preventing attacks: What’s next?
The question
of presentation attack detection is still open in the research
community. But there is opportunity for change.
Anti-spoofing techniques in face recognition 11
Cheaper 3D cameras
It makes sense to use cheap hardware, if it can provide depth information,
to get the safest and most reliable PAD system. A significant amount of
recent research is based on datasets collected with the help of 3D
cameras.
Anomaly detection
In each PAD approach mentioned above, the task was considered a
two-class classification. Some propose that anomaly detection is better
suited to anti-spoofing, making the network more generalized. All genuine
samples have the same nature in common. Attack samples differ but are
diverse and rarely combined into a single class.
Metric learning techniques
Metric learning techniques are applied to achieve better generalization by
minimizing the variance in feature distributions. Variance can be caused by
domain or identity specifics. Presentation attack instruments are
considered as domains in this case. For example, print and screen replay
attacks form separate distributions in the feature space. When the model
faces new, unseen devices used for making an attack, there will be a new
domain distribution and thus feature separation might lead to
misclassifications. This problem can be solved by using distance-based
metrics to help change the network training process to reduce separation
between distributions.
Anti-spoofing based on deep learning is not hype. It's reality when
well-defined product goals are combined with the right approaches and
metrics.
Anti-spoofing
techniques in face recognition 12
You might also like
- Software Quality for Managers: 8 Essential Software Quality KPIs Every Manager Should Know!From EverandSoftware Quality for Managers: 8 Essential Software Quality KPIs Every Manager Should Know!No ratings yet
- Recent trends of Facial Recognition for IoT securityDocument4 pagesRecent trends of Facial Recognition for IoT securitymuhammad ariff baharudinNo ratings yet
- Internet of Things (IoT) A Quick Start Guide: A to Z of IoT EssentialsFrom EverandInternet of Things (IoT) A Quick Start Guide: A to Z of IoT EssentialsNo ratings yet
- IJRPR7765Document5 pagesIJRPR7765Abdul nazarNo ratings yet
- Sat - 27.Pdf - Face Mask Detection Using Convolutional Neural NetworkDocument10 pagesSat - 27.Pdf - Face Mask Detection Using Convolutional Neural NetworkVj KumarNo ratings yet
- Software Engineering Software Requirements Specification (SRS) DocumentDocument13 pagesSoftware Engineering Software Requirements Specification (SRS) DocumenttoxNo ratings yet
- Face Detection by Using OpenCVDocument4 pagesFace Detection by Using OpenCVvickey rajputNo ratings yet
- Face Recognition in Real-World Surveillance Videos With Deep Learning MethodDocument5 pagesFace Recognition in Real-World Surveillance Videos With Deep Learning Methodlokithor45500No ratings yet
- SC 103 Endpoint and Intercept X Sales Overview v2.0.0Document19 pagesSC 103 Endpoint and Intercept X Sales Overview v2.0.0Anderson Traslaviña AlvarezNo ratings yet
- Virt-ICE: Next-Generation Debugger For Malware AnalysisDocument8 pagesVirt-ICE: Next-Generation Debugger For Malware AnalysisBacktrack LinuxNo ratings yet
- Face Detection and Recognition Using Opencv and PythonDocument3 pagesFace Detection and Recognition Using Opencv and PythonGeo SeptianNo ratings yet
- Facial Recognition Using OpenCVDocument7 pagesFacial Recognition Using OpenCVVishalKumarNo ratings yet
- Needar 2Document29 pagesNeedar 2dave poojaNo ratings yet
- Kaspersky Lab Whitepaper Machine LearningDocument17 pagesKaspersky Lab Whitepaper Machine LearningCristian SalazarNo ratings yet
- Wa000Document7 pagesWa000SourabhNo ratings yet
- PDF Course Advanced Malware Analysis PDFDocument2 pagesPDF Course Advanced Malware Analysis PDFVasilica IonutNo ratings yet
- Facial Recognition: U Bio-M (I)Document13 pagesFacial Recognition: U Bio-M (I)kiran_ballamudiNo ratings yet
- Hadoop BI Questions and Answers - Trenovision PDFDocument32 pagesHadoop BI Questions and Answers - Trenovision PDFManjula SuryakanthNo ratings yet
- Face Mask Detection Using Machine Learning and Deep LearningDocument5 pagesFace Mask Detection Using Machine Learning and Deep Learningvikas mandaNo ratings yet
- Bsi10 Ops PDFDocument5 pagesBsi10 Ops PDFTrong Thua HuynhNo ratings yet
- Image Forgery Detection Using Deep LearningDocument21 pagesImage Forgery Detection Using Deep LearningPradyuman Sharma100% (1)
- Ieee Access Image Malware Aug22Document10 pagesIeee Access Image Malware Aug22chowsaj9No ratings yet
- Facial Emotion Recognition Using Convolutional Neural NetworksDocument11 pagesFacial Emotion Recognition Using Convolutional Neural NetworksSudesha BasuNo ratings yet
- Final Project Presentation On "Ai Face Detection"Document12 pagesFinal Project Presentation On "Ai Face Detection"Saini SaabNo ratings yet
- Face Recognition Using PythonDocument9 pagesFace Recognition Using PythonHarshit yadavNo ratings yet
- Vault Box Using Biometric: - Naman Jain (04614803115) - Mohammed Tabish (04514803115)Document17 pagesVault Box Using Biometric: - Naman Jain (04614803115) - Mohammed Tabish (04514803115)Naman JainNo ratings yet
- Implementation of Smart Attendance On FPGA: October 2019Document6 pagesImplementation of Smart Attendance On FPGA: October 2019Yogeshwar nath singhNo ratings yet
- Music Recommendation Based On Facial ExpressionDocument4 pagesMusic Recommendation Based On Facial ExpressionInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- (Adik 1) Sophos-Intercept-X-Deep-Learning-DsnaDocument2 pages(Adik 1) Sophos-Intercept-X-Deep-Learning-DsnaJOhnNo ratings yet
- Open Source and Free SoftwareDocument3 pagesOpen Source and Free Softwarejane7arian7berzabalNo ratings yet
- Chapter 1: INTRODUCTION: 1.1 Problem DefinitionDocument26 pagesChapter 1: INTRODUCTION: 1.1 Problem DefinitionChetan ChoudharyNo ratings yet
- PA-GAN: A Patch-Attention Based Aggregation Network For Face Recognition in SurveillanceDocument10 pagesPA-GAN: A Patch-Attention Based Aggregation Network For Face Recognition in SurveillanceGOURISREE MNo ratings yet
- MalwareAnalysis Report2S17Document15 pagesMalwareAnalysis Report2S17itcom068No ratings yet
- Week 1 IntroductionDocument15 pagesWeek 1 IntroductionZain AhmedNo ratings yet
- Face Mask Detection Using Deep LearningDocument26 pagesFace Mask Detection Using Deep LearningZakaria ElasriNo ratings yet
- Malware Classification Using Static Disassembly and Machine LearningDocument10 pagesMalware Classification Using Static Disassembly and Machine LearningeDu809No ratings yet
- Unit 1Document42 pagesUnit 1harodanurag123No ratings yet
- Theoretical and Practical Analysis On CNN, MTCNN and Caps-Net Base Face Recognition and Detection PDFDocument35 pagesTheoretical and Practical Analysis On CNN, MTCNN and Caps-Net Base Face Recognition and Detection PDFDarshan ShahNo ratings yet
- Face Recognition Technology: Nagendra.P.Mahato, Tejal.S.MarleDocument6 pagesFace Recognition Technology: Nagendra.P.Mahato, Tejal.S.MarleSonia DubeyNo ratings yet
- Face Recognition Using Machine LearningDocument3 pagesFace Recognition Using Machine Learningkamal aminNo ratings yet
- 1 Creative EngagementDocument21 pages1 Creative EngagementCelesamae VicenteNo ratings yet
- Data Augmentation and Transfer Learning To ClassifDocument20 pagesData Augmentation and Transfer Learning To ClassifAM serrakterNo ratings yet
- ASIDE IDE Support For Web Application SecurityDocument10 pagesASIDE IDE Support For Web Application SecurityYash MehtaNo ratings yet
- Face RecognitionDocument2 pagesFace RecognitionantsouNo ratings yet
- Software & Software EngineeringDocument17 pagesSoftware & Software EngineeringAfrime ArafNo ratings yet
- AI - Playbook Executive Briefing Artificial IntelligenceDocument27 pagesAI - Playbook Executive Briefing Artificial IntelligencemeetsarkarNo ratings yet
- A Review of FaceDocument12 pagesA Review of FaceNilesh SharmaNo ratings yet
- Face DetectionDocument14 pagesFace Detectionrudracudasma25No ratings yet
- E13236 e TarjomeDocument6 pagesE13236 e TarjomeSADI HOSSAINNo ratings yet
- Research Paper Version 0Document9 pagesResearch Paper Version 0NidhiNo ratings yet
- Multi-Stage CNN Architecture For Face Mask DetectiDocument12 pagesMulti-Stage CNN Architecture For Face Mask Detectiankita meenaNo ratings yet
- Anti Spoofing Face Detection With Convolutional Neural Networks ClassifierDocument6 pagesAnti Spoofing Face Detection With Convolutional Neural Networks ClassifierInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Facial Recognition Using Deep LearningDocument6 pagesFacial Recognition Using Deep LearningInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Industrial Training: Face Detection Using Viola Jones Algorithm and KLT TrackingDocument15 pagesIndustrial Training: Face Detection Using Viola Jones Algorithm and KLT Trackingtanuj bhallaNo ratings yet
- Face DetectionDocument7 pagesFace Detectionchakshupal339No ratings yet
- program-curriculum-CAIEDocument6 pagesprogram-curriculum-CAIEVijayKhareNo ratings yet
- SWE 211 Ch1 Introduction (With Ahmed Notes)Document21 pagesSWE 211 Ch1 Introduction (With Ahmed Notes)عبدالرحمن النويصرNo ratings yet
- Introduction To Software EngineeringDocument31 pagesIntroduction To Software Engineeringbint - e - ayeshaNo ratings yet
- Vol. 49. No. 01. January 2022 第 49 卷第 01 期 2022 年 1 月 湖南大学学 报(自然科学版) Journal of Hunan University(Natural Sciences)Document21 pagesVol. 49. No. 01. January 2022 第 49 卷第 01 期 2022 年 1 月 湖南大学学 报(自然科学版) Journal of Hunan University(Natural Sciences)حسين رياضNo ratings yet
- Question Bank 1 (1)Document6 pagesQuestion Bank 1 (1)siri chandanaNo ratings yet
- Certificate of Incorporation Phlips India LimitedDocument1 pageCertificate of Incorporation Phlips India LimitedRam AgarwalNo ratings yet
- Guide To Equilibrium DialysisDocument29 pagesGuide To Equilibrium DialysisHaripriya SantoshNo ratings yet
- ks20201 Sample Questions Psycholinguistics Module3Document6 pagesks20201 Sample Questions Psycholinguistics Module3Anurag TiwariNo ratings yet
- TOS - MathDocument4 pagesTOS - MathGeorge Ezar N. QuiriadoNo ratings yet
- D Series: Instruction ManualDocument2 pagesD Series: Instruction ManualMartin del ValleNo ratings yet
- Intro To Factor AnalysisDocument52 pagesIntro To Factor AnalysisRawnak JahanNo ratings yet
- SreejithDocument23 pagesSreejithAkn SNo ratings yet
- Yuken Series PVL Vane Pumps Catalogue en PDFDocument69 pagesYuken Series PVL Vane Pumps Catalogue en PDFAgilRinaldiNo ratings yet
- Ficha de Seguridad Dispositivo Pruba Doble Recamara 2875 - 2876Document133 pagesFicha de Seguridad Dispositivo Pruba Doble Recamara 2875 - 2876janetth rubianoNo ratings yet
- Writing Visual Basic ProjectsDocument1 pageWriting Visual Basic ProjectsAmmuKuttyNo ratings yet
- Perceptron: Tirtharaj DashDocument22 pagesPerceptron: Tirtharaj DashKishan Kumar GuptaNo ratings yet
- Ac and DC MeasurementsDocument29 pagesAc and DC MeasurementsRudra ChauhanNo ratings yet
- Oven Nordson ElectronicDocument60 pagesOven Nordson ElectronicDanijela KoNo ratings yet
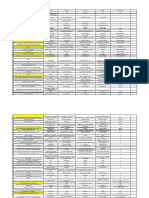
- Resume summary of monthly sparepart costs and production in 2021Document590 pagesResume summary of monthly sparepart costs and production in 2021winda listya ningrumNo ratings yet
- Sheet 5 SolvedDocument4 pagesSheet 5 Solvedshimaa eldakhakhnyNo ratings yet
- This Content Downloaded From 3.6.73.78 On Wed, 21 Dec 2022 07:40:53 UTCDocument81 pagesThis Content Downloaded From 3.6.73.78 On Wed, 21 Dec 2022 07:40:53 UTCabcdNo ratings yet
- Quadratic SDocument22 pagesQuadratic SShawn ShibuNo ratings yet
- Sleep Hygiene Sleep QualityandDocument8 pagesSleep Hygiene Sleep QualityandVriddhi AgrawalNo ratings yet
- 3.4 Linearization of Nonlinear State Space Models: 1 F X Op 1 F X Op 2 F U Op 1 F U Op 2Document3 pages3.4 Linearization of Nonlinear State Space Models: 1 F X Op 1 F X Op 2 F U Op 1 F U Op 2Ilija TomicNo ratings yet
- Risk Assessment: Overall RatingDocument3 pagesRisk Assessment: Overall RatingandirizaNo ratings yet
- Impact of Microfinance On Women's Empowerment: A Case Study On Two Microfinance Institutions in Sri LankaDocument11 pagesImpact of Microfinance On Women's Empowerment: A Case Study On Two Microfinance Institutions in Sri Lankamandala jyoshnaNo ratings yet
- Advanced Long Range Proximity Reader PDFDocument1 pageAdvanced Long Range Proximity Reader PDFPhangkie RecolizadoNo ratings yet
- Sophiajurgens Resume EdtDocument2 pagesSophiajurgens Resume Edtapi-506489381No ratings yet
- PDFDocument42 pagesPDFDanh MolivNo ratings yet
- 11.1 Exam Practice 30 U11Document6 pages11.1 Exam Practice 30 U11Đỗ LoanNo ratings yet
- Well Plan Release NotesDocument28 pagesWell Plan Release Notesahmed_497959294No ratings yet
- COE10205, Other Corrosion Monitoring TechniquesDocument62 pagesCOE10205, Other Corrosion Monitoring Techniquesامين100% (1)
- Nucleus ERPDocument3 pagesNucleus ERPdimensionone1No ratings yet
- Mitspeck 2014 e VersionDocument130 pagesMitspeck 2014 e VersionVedantDomkondekarNo ratings yet
- DRAFT RoA (TSBINUANG) TSB 12 PDFDocument1 pageDRAFT RoA (TSBINUANG) TSB 12 PDFAchwan FebNo ratings yet
- Make Money with ChatGPT: Your Guide to Making Passive Income Online with Ease using AI: AI Wealth MasteryFrom EverandMake Money with ChatGPT: Your Guide to Making Passive Income Online with Ease using AI: AI Wealth MasteryNo ratings yet
- ChatGPT Millionaire 2024 - Bot-Driven Side Hustles, Prompt Engineering Shortcut Secrets, and Automated Income Streams that Print Money While You Sleep. The Ultimate Beginner’s Guide for AI BusinessFrom EverandChatGPT Millionaire 2024 - Bot-Driven Side Hustles, Prompt Engineering Shortcut Secrets, and Automated Income Streams that Print Money While You Sleep. The Ultimate Beginner’s Guide for AI BusinessNo ratings yet
- Generative AI: The Insights You Need from Harvard Business ReviewFrom EverandGenerative AI: The Insights You Need from Harvard Business ReviewRating: 4.5 out of 5 stars4.5/5 (2)
- ChatGPT Side Hustles 2024 - Unlock the Digital Goldmine and Get AI Working for You Fast with More Than 85 Side Hustle Ideas to Boost Passive Income, Create New Cash Flow, and Get Ahead of the CurveFrom EverandChatGPT Side Hustles 2024 - Unlock the Digital Goldmine and Get AI Working for You Fast with More Than 85 Side Hustle Ideas to Boost Passive Income, Create New Cash Flow, and Get Ahead of the CurveNo ratings yet
- Scary Smart: The Future of Artificial Intelligence and How You Can Save Our WorldFrom EverandScary Smart: The Future of Artificial Intelligence and How You Can Save Our WorldRating: 4.5 out of 5 stars4.5/5 (54)
- Artificial Intelligence: The Insights You Need from Harvard Business ReviewFrom EverandArtificial Intelligence: The Insights You Need from Harvard Business ReviewRating: 4.5 out of 5 stars4.5/5 (104)
- Artificial Intelligence: A Guide for Thinking HumansFrom EverandArtificial Intelligence: A Guide for Thinking HumansRating: 4.5 out of 5 stars4.5/5 (30)
- The Master Algorithm: How the Quest for the Ultimate Learning Machine Will Remake Our WorldFrom EverandThe Master Algorithm: How the Quest for the Ultimate Learning Machine Will Remake Our WorldRating: 4.5 out of 5 stars4.5/5 (107)
- AI Money Machine: Unlock the Secrets to Making Money Online with AIFrom EverandAI Money Machine: Unlock the Secrets to Making Money Online with AINo ratings yet
- Who's Afraid of AI?: Fear and Promise in the Age of Thinking MachinesFrom EverandWho's Afraid of AI?: Fear and Promise in the Age of Thinking MachinesRating: 4.5 out of 5 stars4.5/5 (13)
- Mastering Large Language Models: Advanced techniques, applications, cutting-edge methods, and top LLMs (English Edition)From EverandMastering Large Language Models: Advanced techniques, applications, cutting-edge methods, and top LLMs (English Edition)No ratings yet
- AI and Machine Learning for Coders: A Programmer's Guide to Artificial IntelligenceFrom EverandAI and Machine Learning for Coders: A Programmer's Guide to Artificial IntelligenceRating: 4 out of 5 stars4/5 (2)
- ChatGPT Money Machine 2024 - The Ultimate Chatbot Cheat Sheet to Go From Clueless Noob to Prompt Prodigy Fast! Complete AI Beginner’s Course to Catch the GPT Gold Rush Before It Leaves You BehindFrom EverandChatGPT Money Machine 2024 - The Ultimate Chatbot Cheat Sheet to Go From Clueless Noob to Prompt Prodigy Fast! Complete AI Beginner’s Course to Catch the GPT Gold Rush Before It Leaves You BehindNo ratings yet
- Artificial Intelligence: The Complete Beginner’s Guide to the Future of A.I.From EverandArtificial Intelligence: The Complete Beginner’s Guide to the Future of A.I.Rating: 4 out of 5 stars4/5 (15)
- How to Make Money Online Using ChatGPT Prompts: Secrets Revealed for Unlocking Hidden Opportunities. Earn Full-Time Income Using ChatGPT with the Untold Potential of Conversational AI.From EverandHow to Make Money Online Using ChatGPT Prompts: Secrets Revealed for Unlocking Hidden Opportunities. Earn Full-Time Income Using ChatGPT with the Untold Potential of Conversational AI.No ratings yet
- 2084: Artificial Intelligence and the Future of HumanityFrom Everand2084: Artificial Intelligence and the Future of HumanityRating: 4 out of 5 stars4/5 (81)
- The AI Advantage: How to Put the Artificial Intelligence Revolution to WorkFrom EverandThe AI Advantage: How to Put the Artificial Intelligence Revolution to WorkRating: 4 out of 5 stars4/5 (7)
- Midjourney Mastery - The Ultimate Handbook of PromptsFrom EverandMidjourney Mastery - The Ultimate Handbook of PromptsRating: 4.5 out of 5 stars4.5/5 (2)
- Artificial Intelligence & Generative AI for Beginners: The Complete GuideFrom EverandArtificial Intelligence & Generative AI for Beginners: The Complete GuideRating: 5 out of 5 stars5/5 (1)
- 100+ Amazing AI Image Prompts: Expertly Crafted Midjourney AI Art Generation ExamplesFrom Everand100+ Amazing AI Image Prompts: Expertly Crafted Midjourney AI Art Generation ExamplesNo ratings yet
- Machine Learning: The Ultimate Beginner's Guide to Learn Machine Learning, Artificial Intelligence & Neural Networks Step by StepFrom EverandMachine Learning: The Ultimate Beginner's Guide to Learn Machine Learning, Artificial Intelligence & Neural Networks Step by StepRating: 4.5 out of 5 stars4.5/5 (19)
- Power and Prediction: The Disruptive Economics of Artificial IntelligenceFrom EverandPower and Prediction: The Disruptive Economics of Artificial IntelligenceRating: 4.5 out of 5 stars4.5/5 (38)