Professional Documents
Culture Documents
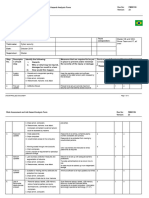
SR - No. Questions Option 1 Option 2
Uploaded by
Maryam Mohammed0 ratings0% found this document useful (0 votes)
21 views7 pagesThis document contains questions and multiple choice options about real-time systems and applications, e-business risk management issues, and e-security systems. It is a study guide for a class on IT business management. The questions cover topics such as types of real-time systems, definitions of common IT and security terms, examples of security threats and mitigation strategies, and names of cybersecurity software companies.
Original Description:
Original Title
Unit_4_ITBM_MCQ
Copyright
© © All Rights Reserved
Available Formats
XLSX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThis document contains questions and multiple choice options about real-time systems and applications, e-business risk management issues, and e-security systems. It is a study guide for a class on IT business management. The questions cover topics such as types of real-time systems, definitions of common IT and security terms, examples of security threats and mitigation strategies, and names of cybersecurity software companies.
Copyright:
© All Rights Reserved
Available Formats
Download as XLSX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
21 views7 pagesSR - No. Questions Option 1 Option 2
Uploaded by
Maryam MohammedThis document contains questions and multiple choice options about real-time systems and applications, e-business risk management issues, and e-security systems. It is a study guide for a class on IT business management. The questions cover topics such as types of real-time systems, definitions of common IT and security terms, examples of security threats and mitigation strategies, and names of cybersecurity software companies.
Copyright:
© All Rights Reserved
Available Formats
Download as XLSX, PDF, TXT or read online from Scribd
You are on page 1of 7
Programme: SYBMS
Class and Semester: Second Year and III
Subject: ITBM
Unit-4 Chapter: 19- E-Security system
Asst Prof. Archana Sanap
Sr.no. Questions option 1 option 2
1 To protect computer system from the list not mentioned Internal
p External
2 The non-physical threats are also known as _______ Logical Threats Physical Threats
3 The following list is the common types of non-physical thVirus Trojans
4 __________ one of the most harmless where it programm Worms Trojans
5 _________ something that keeps a record of every keyst Key Loggers Adwary
6 Website get hacking and issues therein: Access control Softwre vernabilites
7 Full form of XSS Xetention software sy Cross -site sripting
8 Full form of URL Uniform Resource LocaUniform Restored Loca
9 _________ is the most common risk management strategRisk Acceptance Risk Avoidance
10 A fake website which is designed to look almost like the Wabbits Backdoor
e: SYBMS
Second Year and III
TBM
E-Security system
option 3 option 4 Answer
Humans Middle 4
Non-Phyiscal Threats Security Threats 1
Worms All of the above 4
Virus spyware 1
spayware virus 1
Third Party IntegrationAll of the above 4
Cross site system Cross software system 2
Uniform Resource LocaUniverse Restored loca 1
Risk Limitation Risk Transferance 3
exploit Phishing 4
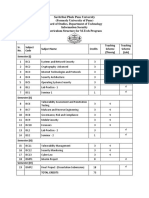
Programme: SYBM
Class and Semester: Second Y
Unit-4 Chapter: 20- E-Buisness Risk M
Asst Prof. Archana Sanap
Sr.no. Questions option 1
1 Full from of DoS Denial of service attac
2 A _____ attack is an application or device that can read,moniter & capture IP spoofing
3 A______ is a network security system,either hardware or software base that Fuirwall
4 What are the types of firwall according to NIST? Packet filter
5 Stateful inspection was first introduce in _____ 1993
6 Circuit level gatways are the second generation of _______ architectures. TCP
7 Types of network attack________ IP spoofing
8 The third generation of firewall architechures is called Application Level Gat
9 Firwall do not protect against_________ attack. Phishing
10 _______ controls How particular services are used. Behavior
Programme: SYBMS
s and Semester: Second Year and III
Subject: ITBM
er: 20- E-Buisness Risk Management issues
option 2 option 3 option 4 Answer
Denial of suface attack Denial of service attemptDenial of serface attempt 1
DoS attack Sniffer attack Man in the Middle aatack 3
Traffic Proxy DoS 1
proxy stateful inspection All of the above 4
1994 1998 1999 2
TCP/IP Firewall UDP 3
DoS attack Sniffer attack All of the above 4
Circuit Level Gateway Software Firwall Hardware Firwall 1
Adware Backdoor Virus 3
Service Direction User 1
Programme: SYBMS
Class and Semester: Second Year and III
Subject: ITBM
Unit-4 Chapter: 21- E-Real Time Application in B
Asst Prof. Archana Sanap
Sr.no. Questions option 1 option 2
1 A_____ system is a type of hardware or software that Real Time Real time system
2 ______ are those which must produce the correct respo Real Time Real time system
3 ______ a program for a which the correction of opratiReal Time Real time system
4 Types of real time system: clock base system interactive system
5 Task has to be compeleted in the specified time inter Real Time Real time clock
6 Full from of RTA Real Time application Real Type application
7 Full from of RTC Real time computing Real time computer
8 Threat hunting software and service not include Carbon black cybereason
9 _____ is an American Company founded in 2012 that ma sqrrl carbon black
10 _________is an enterprise technology company headqu sqrrl carbon black
me: SYBMS
r: Second Year and III
BM
l Time Application in Business
option 3 option 4 Answer
Real time program Hard Real time 1
Real time program hard Real time 2
Real time program Hard Real time 3
event base system all of the above 4
interactive system Real time system 2
Real type applicant Real time applicant 1
Real type computing Real type computer 1
sqrrl cyber Threat 4
cybereason ExtraHop Network 1
cybereason ExtraHop Network 4
You might also like
- SR - No. Questions Option 1 Option 2Document7 pagesSR - No. Questions Option 1 Option 2Maryam MohammedNo ratings yet
- Chapter 18: ProtectionDocument5 pagesChapter 18: ProtectionAbhishek DuttaNo ratings yet
- Security in Computing QuestionsDocument139 pagesSecurity in Computing Questionsshin chanNo ratings yet
- Ethical Hacking Proactive TrainingDocument16 pagesEthical Hacking Proactive TrainingMarcelo JuniorNo ratings yet
- Lect1 BasicSecurityConcepts 1Document19 pagesLect1 BasicSecurityConcepts 1RossyNo ratings yet
- Ccna SecurityDocument81 pagesCcna SecurityBrahim El-Asri100% (1)
- Cisco CCNA SecurityDocument85 pagesCisco CCNA SecurityPaoPound HomnualNo ratings yet
- Cisco CCNA Security, Chapter 1 Exam. Cisco CCNA Security, Chapter 1 Exam. Cisco CCNA Security, Chapter 1 ExamDocument54 pagesCisco CCNA Security, Chapter 1 Exam. Cisco CCNA Security, Chapter 1 Exam. Cisco CCNA Security, Chapter 1 ExamAlexa JahenNo ratings yet
- Metasploit Framework by Achilli3stDocument81 pagesMetasploit Framework by Achilli3stSavan Patel100% (1)
- Researching Network Attacks and Security Audit ToolsDocument4 pagesResearching Network Attacks and Security Audit ToolsAxelle CarcacheNo ratings yet
- Metasploit - Framework-A Quick Reference PDFDocument81 pagesMetasploit - Framework-A Quick Reference PDFsavanpatel16No ratings yet
- Multi Level Ransomware Detection FrameworkDocument8 pagesMulti Level Ransomware Detection FrameworkRyansNo ratings yet
- Prueba Cap 1 CCNA SecurityDocument11 pagesPrueba Cap 1 CCNA SecurityGuillermo E Lobo PNo ratings yet
- Malware: Botnets and Worms: by Apurba DhunganaDocument23 pagesMalware: Botnets and Worms: by Apurba DhunganaApurba DhunganaNo ratings yet
- Computer Networks NoteDocument38 pagesComputer Networks NoteSimple GuptaNo ratings yet
- Cisco CCNA Security Chapter 1 Exam AnswersDocument5 pagesCisco CCNA Security Chapter 1 Exam Answersstu3232No ratings yet
- Vulnerability Exploit Asset RiskDocument17 pagesVulnerability Exploit Asset RiskSandrita MaritzaNo ratings yet
- System AttacksDocument143 pagesSystem Attacksphishing ltaNo ratings yet
- 1.4.1.1 Lab - Researching Network Attacks and Security Audit ToolsDocument5 pages1.4.1.1 Lab - Researching Network Attacks and Security Audit ToolsPungky AgustineNo ratings yet
- 11.2.2.6 Lab - Researching Network Security ThreatsDocument3 pages11.2.2.6 Lab - Researching Network Security Threatsava pruzhanovskyNo ratings yet
- Broadband Network Virus Detection System Based On Bypass MonitorDocument4 pagesBroadband Network Virus Detection System Based On Bypass MonitorJohn GacheruNo ratings yet
- Ccna Security Examen 1. 100%Document7 pagesCcna Security Examen 1. 100%wamrojasNo ratings yet
- Answer CCNA Security Chapter 1 Test - CCNAS v1.1: Probe, Penetrate, Persist, Propagate, and ParalyzeDocument10 pagesAnswer CCNA Security Chapter 1 Test - CCNAS v1.1: Probe, Penetrate, Persist, Propagate, and ParalyzeFranco SalernoNo ratings yet
- CCNA Security - Chapter 1 Exam AnswersDocument6 pagesCCNA Security - Chapter 1 Exam Answersrockynaruto0% (1)
- Detection and Analysis Cerber Ransomware Based On Network Forensics BehaviorDocument8 pagesDetection and Analysis Cerber Ransomware Based On Network Forensics BehaviorMsik MssiNo ratings yet
- Cyber Security 06012022Document3 pagesCyber Security 06012022Nilesh Waikar 2No ratings yet
- Seletar Spirit - CyberSecurity JHADocument5 pagesSeletar Spirit - CyberSecurity JHARomit GuptaNo ratings yet
- Unit - IDocument15 pagesUnit - IashaNo ratings yet
- ZX301Document1 pageZX301siboruremarukundoc1No ratings yet
- Network Security Lab Report 5Document6 pagesNetwork Security Lab Report 5mohashinrajibNo ratings yet
- Case Study SMC Sesi I 2022.2023 - 13112022 (Ahmad f2008, Hidayat f2036, Syafiq f2056)Document11 pagesCase Study SMC Sesi I 2022.2023 - 13112022 (Ahmad f2008, Hidayat f2036, Syafiq f2056)F2056 SyafiqNo ratings yet
- 53 Cyber Forensics MinorDocument19 pages53 Cyber Forensics MinorPrasanna VNo ratings yet
- IS3110 LAB 5 Assesment WorksheetDocument6 pagesIS3110 LAB 5 Assesment WorksheetRaymond Young100% (1)
- Malware Capturing and Detection in Dionaea Honeypot: Dilsheer Ali. P Gireesh Kumar TDocument5 pagesMalware Capturing and Detection in Dionaea Honeypot: Dilsheer Ali. P Gireesh Kumar TBae SuzyNo ratings yet
- Pune University IS Tech. SyllabusDocument9 pagesPune University IS Tech. SyllabusPav TechnicalsNo ratings yet
- Vtu Network Security (10ec832) Unit-7 Notes.Document10 pagesVtu Network Security (10ec832) Unit-7 Notes.jayanthdwijesh h pNo ratings yet
- Evidential-Study-of-Ransomware Joa Eng 1018Document10 pagesEvidential-Study-of-Ransomware Joa Eng 1018Wili MamaniNo ratings yet
- Applsci 12 10755 v2Document12 pagesApplsci 12 10755 v2bee927172No ratings yet
- VulnerabilitatiDocument12 pagesVulnerabilitatiIon DanNo ratings yet
- IT Security - 2 Exercise 2 (Botnets, Mobile Malware) : 1 Task - 1: Botnets and The Underground EconomyDocument6 pagesIT Security - 2 Exercise 2 (Botnets, Mobile Malware) : 1 Task - 1: Botnets and The Underground Economytanmaya1991No ratings yet
- Darknet and Deepnet Mining For Proactive Cybersecurity Threat IntelligenceDocument6 pagesDarknet and Deepnet Mining For Proactive Cybersecurity Threat IntelligenceJorgeNo ratings yet
- Clsss 7 NOTES-1Document5 pagesClsss 7 NOTES-1CGM RO HYDNo ratings yet
- ReportDocument6 pagesReportdp.gadhiya100% (1)
- Lab - Researching Network Attacks and Security Audit ToolsDocument4 pagesLab - Researching Network Attacks and Security Audit ToolsAlvaro Avila QuirosNo ratings yet
- Seminar ReportDocument38 pagesSeminar Reportapi-384849680% (5)
- Challenges of Malware Analysis: Obfuscation TechniquesDocument11 pagesChallenges of Malware Analysis: Obfuscation Techniqueseto413199No ratings yet
- Penetration TestingDocument4 pagesPenetration TestingsipraNo ratings yet
- Malware Detection in Android ApplicationsDocument3 pagesMalware Detection in Android ApplicationsEditor IJTSRDNo ratings yet
- 9 Module 5 07 07 2023Document90 pages9 Module 5 07 07 2023Shreya RajpalNo ratings yet
- CHP3 Multiple Choice With AnswersDocument6 pagesCHP3 Multiple Choice With AnswersRonald FloresNo ratings yet
- Auditing Operating System and Network Multiple Choice Questions (With Answers) Micah CaraggayanDocument6 pagesAuditing Operating System and Network Multiple Choice Questions (With Answers) Micah CaraggayanRonald FloresNo ratings yet
- TCS-VA SyllabusDocument8 pagesTCS-VA SyllabusHacking LabNo ratings yet
- CCNAS Chapter 1 CCNA Security 1Document10 pagesCCNAS Chapter 1 CCNA Security 1Sergiy KalmukNo ratings yet
- How to Defeat Advanced Malware: New Tools for Protection and ForensicsFrom EverandHow to Defeat Advanced Malware: New Tools for Protection and ForensicsNo ratings yet
- Trusted Digital Circuits: Hardware Trojan Vulnerabilities, Prevention and DetectionFrom EverandTrusted Digital Circuits: Hardware Trojan Vulnerabilities, Prevention and DetectionNo ratings yet
- Penetration Testing Fundamentals-2: Penetration Testing Study Guide To Breaking Into SystemsFrom EverandPenetration Testing Fundamentals-2: Penetration Testing Study Guide To Breaking Into SystemsNo ratings yet
- Linux Malware Incident Response: A Practitioner's Guide to Forensic Collection and Examination of Volatile Data: An Excerpt from Malware Forensic Field Guide for Linux SystemsFrom EverandLinux Malware Incident Response: A Practitioner's Guide to Forensic Collection and Examination of Volatile Data: An Excerpt from Malware Forensic Field Guide for Linux SystemsNo ratings yet
- Common Windows, Linux and Web Server Systems Hacking TechniquesFrom EverandCommon Windows, Linux and Web Server Systems Hacking TechniquesNo ratings yet
- Security for Small Computer Systems: A Practical Guide for UsersFrom EverandSecurity for Small Computer Systems: A Practical Guide for UsersTricia SaddingtonNo ratings yet
- Attack and PenetrationDocument44 pagesAttack and PenetrationAchmad Hidayat100% (1)
- 10 BibliographyDocument5 pages10 Bibliographynandhaku2No ratings yet
- ArwinDocument3 pagesArwindede sutiawanNo ratings yet
- Kaspersky Lab: Mohamed Habeeb.ADocument21 pagesKaspersky Lab: Mohamed Habeeb.AsmatbalaNo ratings yet
- Detailed Lesson Plan in InformationDocument8 pagesDetailed Lesson Plan in InformationNelson ZaidiNo ratings yet
- Mafia BoyDocument2 pagesMafia BoyLester Viruz NavarroNo ratings yet
- Cisco VCS Authenticating Devices Deployment Guide X7-2Document50 pagesCisco VCS Authenticating Devices Deployment Guide X7-2Luis R. MeloNo ratings yet
- 20 BitDefenderDocument24 pages20 BitDefenderwiktor991No ratings yet
- Remote Desktop Protocol (RDP)Document44 pagesRemote Desktop Protocol (RDP)Jouris HofniNo ratings yet
- SAP BI Configuration En-1Document42 pagesSAP BI Configuration En-1Abhishek TiwariNo ratings yet
- Security Fundamentals MicrosoftDocument129 pagesSecurity Fundamentals MicrosoftAakash GujarNo ratings yet
- Quiz - The Threat LandscapeDocument2 pagesQuiz - The Threat Landscapedezao100% (1)
- Incedint Report ExampleDocument20 pagesIncedint Report Examplesaqer_11No ratings yet
- What Is Internet Privacy and What Does Privacy Mean To YouDocument2 pagesWhat Is Internet Privacy and What Does Privacy Mean To YouMatheus Mendes de AlbuquerqueNo ratings yet
- Cyber Security by Mannan Anand, Yugal Bairwa and Shiven PatelDocument13 pagesCyber Security by Mannan Anand, Yugal Bairwa and Shiven PatelMannan AnandNo ratings yet
- The Quest To Replace Passwords: A Framework For Comparative Evaluation of Web Authentication SchemesDocument15 pagesThe Quest To Replace Passwords: A Framework For Comparative Evaluation of Web Authentication SchemesTanmay SrivastavNo ratings yet
- Lab 8Document24 pagesLab 8RapacitorNo ratings yet
- Configure An External AAA Server For VPNDocument14 pagesConfigure An External AAA Server For VPNKeny Oscar Cortes GonzalezNo ratings yet
- HackingDocument24 pagesHackingprasad100% (1)
- Olo para V4,5,6,7,8,9 (Más Abajo Versión 10 Premium Y Otras Versiones, También Hay Trials para Ultimo Recurso Que Están Abajo Del Todo)Document4 pagesOlo para V4,5,6,7,8,9 (Más Abajo Versión 10 Premium Y Otras Versiones, También Hay Trials para Ultimo Recurso Que Están Abajo Del Todo)Iqp Edicson ZentellaNo ratings yet
- Three Level Password Authentication System MechanismDocument5 pagesThree Level Password Authentication System MechanismIJRASETPublicationsNo ratings yet
- Fortinet Solutions RSSO - RADIUS Single Sign OnDocument27 pagesFortinet Solutions RSSO - RADIUS Single Sign Onabaheabaheabahe100% (1)
- Login Logoff Auditing Quick Reference GuideDocument1 pageLogin Logoff Auditing Quick Reference GuidenicolepetrescuNo ratings yet
- Inoue Daisuke-National Ict InstituteDocument26 pagesInoue Daisuke-National Ict Instituterinbra4633No ratings yet
- LAN Security Concepts PDFDocument3 pagesLAN Security Concepts PDFAlonso Maurico Bolaños GuillenNo ratings yet
- Lightweight Directory Access Protocol (LDAP)Document2 pagesLightweight Directory Access Protocol (LDAP)Dayakar MeruguNo ratings yet
- Project Report On Password Manager With Multi Factor AuthenticationDocument60 pagesProject Report On Password Manager With Multi Factor AuthenticationMiracleNo ratings yet
- MIS Mid-Term ExaminationDocument8 pagesMIS Mid-Term ExaminationOWAIS AHMED NISAR AHMEDNo ratings yet
- IS4560 Lab 1 Assessment WorksheetDocument4 pagesIS4560 Lab 1 Assessment WorksheetAmanda KingNo ratings yet
- Ism FinalDocument12 pagesIsm FinalDeblina MukherjeeNo ratings yet