Professional Documents
Culture Documents
3/25/2020 Muthukumar.A / ASP/ ECE / CNS / UNIT V / Firewall Design Principles 1
Uploaded by
Harseerat Sidhu0 ratings0% found this document useful (0 votes)
13 views9 pagesOriginal Title
1585136556
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
13 views9 pages3/25/2020 Muthukumar.A / ASP/ ECE / CNS / UNIT V / Firewall Design Principles 1
Uploaded by
Harseerat SidhuCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 9
Firewall Design Principles
Muthukumar.A / ASP/ ECE / CNS / UNIT V /
3/25/2020 1
Firewall Design Principles
Firewall Design Principles
Information systems in corporations, government agencies,
and other organizations have undergone a steady evolution:
● Centralized data processing system, with a central mainframe
supporting a number of directly connected terminals
● Local area networks (LANs) interconnecting PCs and terminals to
each other and the mainframe
● Premises network, consisting of a number of LANs,
interconnecting PCs, servers, and perhaps a mainframe or two
Enterprise-wide network, consisting of multiple, geographically
distributed premises networks interconnected by a private wide
area network (WAN)
● Internet connectivity, in which the various premises networks all
hook into the Internet and may or may not also be connected by a
private WAN.
Muthukumar.A / ASP/ ECE / CNS / UNIT V /
3/25/2020 2
Firewall Design Principles
Firewall Characteristics
The following are design goals for a firewall:
1. All traffic from inside to outside, and vice versa, must pass
through the firewall. This is achieved by physically blocking all
access to the local network except via the firewall. Various
configurations are possible, as explained later in this section.
2. Only authorized traffic, as defined by the local security policy, will
be allowed to pass. Various types of firewalls are used, which
implement various types of security policies.
3.The firewall itself is immune to penetration. This implies that use
of a trusted system with a secure operating system.
Muthukumar.A / ASP/ ECE / CNS / UNIT V /
3/25/2020 3
Firewall Design Principles
Firewall Characteristics
Originally, firewalls focused primarily on service control, but
they have since evolved to provide all four:
Service control: Determines the types of Internet services that can
be accessed, inbound or outbound. The firewall may filter traffic on
the basis of IP address and TCP port number; may provide proxy
software that receives and interprets each service request before
passing it on; or may host the server software itself, such as a Web
or mail service.
Direction control: Determines the direction in which particular
service requests may be initiated and allowed to flow through the
firewall.
Muthukumar.A / ASP/ ECE / CNS / UNIT V /
3/25/2020 4
Firewall Design Principles
Firewall Characteristics
•User control: Controls access to a service according to which user
is attempting to access it. This feature is typically applied to users
inside the firewall perimeter (local users). It may also be applied to
incoming traffic from external users; the latter requires some form
of secure authentication technology, such as is provided in IPSec.
● Behavior control: Controls how particular services are used. For
example, the firewall may filter e-mail to eliminate spam, or it may
enable external access to only a portion of the information on
a local Web server.
Muthukumar.A / ASP/ ECE / CNS / UNIT V /
3/25/2020 5
Firewall Design Principles
Firewall Characteristics
Firewalls have their limitations, including the following:
1. The firewall cannot protect against attacks that bypass the
firewall. Internal systems may have dial-out capability to connect to
an ISP. An internal LAN may support a modem pool that provides
dial-in capability for traveling employees and telecommuters.
2.The firewall does not protect against internal threats, such as a
disgruntled employee or an employee who unwittingly cooperates
with an external attacker.
3.The firewall cannot protect against the transfer of virus-infected
programs or files. Because of the variety of operating systems and
applications supported inside the perimeter, it would be impractical
and perhaps impossible for the firewall to scan all incoming files, e-
mail, and messages for viruses.
Muthukumar.A / ASP/ ECE / CNS / UNIT V /
3/25/2020 6
Firewall Design Principles
Figure-1: Firewall Types
Muthukumar.A / ASP/ ECE / CNS / UNIT V /
3/25/2020 7
Firewall Design Principles
Packet-Filtering Router
A packet-filtering router applies a set of rules to each incoming
and outgoing IP packet and then forwards or discards the packet.
The router is typically configured to filter packets going in both
Directions (from and to the internal network). Filtering rules are
based on information contained in a network packet:
● Source IP address: The IP address of the system that originated
the IP packet (e.g., 192.178.1.1)
● Destination IP address: The IP address of the system the IP
packet is trying to reach (e.g., 192.168.1.2)
● Source and destination transport-level address: The transport
level (e.g., TCP or UDP) port number, which defines applications
such as SNMP or TELNET
• IP protocol field: Defines the transport protocol
● Interface: For a router with three or more ports, which interface
of the router the packet came from or which interface of the
router the packet is destined for
Muthukumar.A / ASP/ ECE / CNS / UNIT V /
3/25/2020 8
Firewall Design Principles
Summarize
Muthukumar.A / ASP/ ECE / CNS / UNIT V /
3/25/2020 9
Firewall Design Principles
You might also like
- HTML CSS Javascript MCQDocument11 pagesHTML CSS Javascript MCQWaheed Anwar78% (18)
- Trusted Systems, Firewalls, Intrusion Detection SystemsDocument18 pagesTrusted Systems, Firewalls, Intrusion Detection SystemsMukesh100% (34)
- Seam Tracking Th6D Manual V.1.0 (Binzel - Scansonic) 2014Document24 pagesSeam Tracking Th6D Manual V.1.0 (Binzel - Scansonic) 2014Arda YazıcıNo ratings yet
- F5Document10 pagesF5pravinNo ratings yet
- System Security Case Studies Chapter 6 Firewall DesignDocument19 pagesSystem Security Case Studies Chapter 6 Firewall DesignPurvaNo ratings yet
- INformation Security 5Document11 pagesINformation Security 5Shantanu GuptaNo ratings yet
- Firewall: Hasibur Rahman ASH1711009MDocument13 pagesFirewall: Hasibur Rahman ASH1711009MFarida SiddiqiNo ratings yet
- Specific Instructional Objectives: Encryption/decryption Technique For Transfer of Data Between Two SecureDocument8 pagesSpecific Instructional Objectives: Encryption/decryption Technique For Transfer of Data Between Two SecureGanesh MoteNo ratings yet
- Network Access PoudelDocument6 pagesNetwork Access PoudelArchana VNo ratings yet
- FirewallDocument63 pagesFirewallLorie Jane ReyesNo ratings yet
- Techsem 2Document12 pagesTechsem 2207511 RehmanNo ratings yet
- Firrewall and Intrusion Prevention SystemDocument23 pagesFirrewall and Intrusion Prevention Systemfatima gullNo ratings yet
- An Overview of Firewall TechnologiesDocument9 pagesAn Overview of Firewall TechnologiesMATHEUS LÁZARONo ratings yet
- SE 4C03 Winter 2005 Firewall Design Principles: By: Kirk CraneDocument7 pagesSE 4C03 Winter 2005 Firewall Design Principles: By: Kirk CranePoulvilleNo ratings yet
- A Seminar Report On Firewall: Department of Computer Science & Engineering Assam Down Town UniversityDocument22 pagesA Seminar Report On Firewall: Department of Computer Science & Engineering Assam Down Town UniversityChao AmitNo ratings yet
- PR 12Document6 pagesPR 12jivanlad22No ratings yet
- Sec+ Study Guide 401Document34 pagesSec+ Study Guide 401Tuan NamNo ratings yet
- FireDocument61 pagesFireAnuj SinghNo ratings yet
- An Overview of Firewall Technologies: Keywords: Firewall Technologies, Network Security, Access Control, SecurityDocument9 pagesAn Overview of Firewall Technologies: Keywords: Firewall Technologies, Network Security, Access Control, SecurityAjitav BasakNo ratings yet
- Information Security and Assurance Security Technology 1: Course ModuleDocument24 pagesInformation Security and Assurance Security Technology 1: Course ModuleJenny ApiladoNo ratings yet
- SEC3014 Part4cDocument38 pagesSEC3014 Part4cYeong Lee SenggNo ratings yet
- M 3 I N S: Chapter 2: Server Management and FirewallsDocument45 pagesM 3 I N S: Chapter 2: Server Management and FirewallsChetan ChaudhariNo ratings yet
- Firewalls: Security TechnologiesDocument63 pagesFirewalls: Security TechnologiespiyushNo ratings yet
- Abe Catacutan Bsit 3G Student 4Document2 pagesAbe Catacutan Bsit 3G Student 4joriz punazlNo ratings yet
- Ch4 NISDocument33 pagesCh4 NISshrey6346No ratings yet
- Seminar on Firewall Protection and DesignDocument19 pagesSeminar on Firewall Protection and DesignSachin GoyalNo ratings yet
- Firewalls Are Used To Protect Both Home and Corporate NetworksDocument4 pagesFirewalls Are Used To Protect Both Home and Corporate NetworksAnkita SoniNo ratings yet
- 04 PresentationDocument24 pages04 PresentationAhmed HurmziNo ratings yet
- Firewalls VPNsDocument52 pagesFirewalls VPNsmikacraftNo ratings yet
- Firewall: Visit For More Learning ResourcesDocument26 pagesFirewall: Visit For More Learning ResourcesGeorge JR BagsaoNo ratings yet
- Data Security in Local Network Using Distributed FirewallDocument9 pagesData Security in Local Network Using Distributed FirewallSumanth NallaNo ratings yet
- Firewall PresentationDocument23 pagesFirewall PresentationmandeepNo ratings yet
- WQD7010 Network & Security: Dr. Saaidal Razalli Bin AzzuhriDocument40 pagesWQD7010 Network & Security: Dr. Saaidal Razalli Bin AzzuhriAbu Aisyah Yat SaaidalNo ratings yet
- Netwok CDocument36 pagesNetwok CMohammad Jakirul IslamNo ratings yet
- Firewalls and VPNS: Principles of Information Security, 2Nd Edition 1Document45 pagesFirewalls and VPNS: Principles of Information Security, 2Nd Edition 1Nishanth KrishnamurthyNo ratings yet
- firewallDocument3 pagesfirewallrahulpaswan8307No ratings yet
- Firewall Seminar ReportDocument15 pagesFirewall Seminar ReportkumarNo ratings yet
- "Firewall": A Seminar Report OnDocument15 pages"Firewall": A Seminar Report OnkumarNo ratings yet
- "Firewall": A Seminar Report OnDocument15 pages"Firewall": A Seminar Report OnkumarNo ratings yet
- Approach of Data Security in Local Network Using Distributed FirewallsDocument4 pagesApproach of Data Security in Local Network Using Distributed FirewallsAsad WaheedNo ratings yet
- FirewallDocument22 pagesFirewallanmol_baliyan0767% (3)
- 4.3.4.1 - Firewall Best PracticesDocument6 pages4.3.4.1 - Firewall Best PracticesAdeshina Segun AbefeNo ratings yet
- Advantages of FirewallDocument16 pagesAdvantages of FirewallBridget Smith69% (13)
- 08-CH09-CompSec2e-ver02 Firewalls PDFDocument33 pages08-CH09-CompSec2e-ver02 Firewalls PDFNikunj PatelNo ratings yet
- Feleke Firewall Note 2023Document21 pagesFeleke Firewall Note 2023Abni booNo ratings yet
- Firewall Security GuideDocument14 pagesFirewall Security GuideAshu BhallaNo ratings yet
- Firewall Security Basics ExplainedDocument9 pagesFirewall Security Basics ExplainedPhát TrầnNo ratings yet
- Sathish P 1011-0986-2050: Resented YDocument18 pagesSathish P 1011-0986-2050: Resented YSathish Parlapelly100% (1)
- Why Do We Need Firewalls?Document18 pagesWhy Do We Need Firewalls?Raveendra Babu PonnuruNo ratings yet
- Configuration of Firewall-Om ChauhanDocument6 pagesConfiguration of Firewall-Om Chauhan2203031240954No ratings yet
- OECLibrary Firewall GuideDocument24 pagesOECLibrary Firewall Guidemuneebrahat100% (1)
- Understanding Firewalls - Types, Techniques & UsesDocument30 pagesUnderstanding Firewalls - Types, Techniques & UsesabhishekNo ratings yet
- Network Firewall Technologies: 1. Security Threats From Connecting To The InternetDocument17 pagesNetwork Firewall Technologies: 1. Security Threats From Connecting To The InternetRanjan BhatNo ratings yet
- Firewall Security: Firewall Is A Barrier Between Local Area Network (LAN) and The Internet. ItDocument5 pagesFirewall Security: Firewall Is A Barrier Between Local Area Network (LAN) and The Internet. ItShamsNo ratings yet
- Cyber SecurityDocument15 pagesCyber Securityanon_901462304No ratings yet
- Seminar Report on Firewalls Submitted for BSc DegreeDocument17 pagesSeminar Report on Firewalls Submitted for BSc DegreePiYuSH khaTRINo ratings yet
- Firewall Features:: C C C CDocument6 pagesFirewall Features:: C C C CShrihari ShamjiNo ratings yet
- Chapter 4 Security DesignDocument50 pagesChapter 4 Security DesignyogaNo ratings yet
- QuestionsDocument43 pagesQuestionssukeerthi bmeNo ratings yet
- Computer Security and Intrusion DetectionDocument18 pagesComputer Security and Intrusion DetectionNARESH BADWENo ratings yet
- Unit-II 7033 - Additional NotesDocument32 pagesUnit-II 7033 - Additional NotesHari RNo ratings yet
- MIMIT Malout Timetable for 6th CSEDocument2 pagesMIMIT Malout Timetable for 6th CSEHarseerat SidhuNo ratings yet
- GB - Technical AssignmentDocument10 pagesGB - Technical AssignmentHarseerat SidhuNo ratings yet
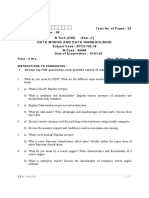
- Network Security and Cryptography: Inst Ruct Ions T O Cand Idat EsDocument1 pageNetwork Security and Cryptography: Inst Ruct Ions T O Cand Idat EsHarseerat SidhuNo ratings yet
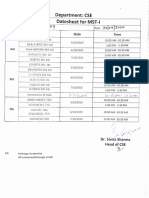
- Datesheet For Mst-1Document1 pageDatesheet For Mst-1Harseerat SidhuNo ratings yet
- Kgfonts TouDocument1 pageKgfonts TouHarseerat SidhuNo ratings yet
- Network Security and Cryptography: Inst Ruct Ions T O Cand Idat EsDocument1 pageNetwork Security and Cryptography: Inst Ruct Ions T O Cand Idat EsHarseerat SidhuNo ratings yet
- Network Security and Cryptography: Inst Ruct Ions T O Cand Idat EsDocument1 pageNetwork Security and Cryptography: Inst Ruct Ions T O Cand Idat EsHarseerat SidhuNo ratings yet
- July 2021Document1 pageJuly 2021Harseerat SidhuNo ratings yet
- Practical File OF "Parallel Computing"Document1 pagePractical File OF "Parallel Computing"Harseerat SidhuNo ratings yet
- SchemeSyllabus B.techCSE2018 CompleteDocument98 pagesSchemeSyllabus B.techCSE2018 CompleteHarseerat SidhuNo ratings yet
- Missing Topic of PCDocument4 pagesMissing Topic of PCHarseerat SidhuNo ratings yet
- B.tech Cse 7th Sem SyllabusDocument6 pagesB.tech Cse 7th Sem SyllabusHarseerat SidhuNo ratings yet
- Data Mining and Data Warehousing Exam QuestionsDocument2 pagesData Mining and Data Warehousing Exam QuestionsHarseerat SidhuNo ratings yet
- Performance Metrics: Parallel Computing 2015/2016Document42 pagesPerformance Metrics: Parallel Computing 2015/2016Harseerat SidhuNo ratings yet
- Missing Topic of PCDocument4 pagesMissing Topic of PCHarseerat SidhuNo ratings yet
- Parallel Computing Chapter 7 Performance and Scalability: Jun Zhang Department of Computer Science University of KentuckyDocument26 pagesParallel Computing Chapter 7 Performance and Scalability: Jun Zhang Department of Computer Science University of KentuckyWidya MeiriskaNo ratings yet
- Parallel Computing Chapter 7 Performance and Scalability: Jun Zhang Department of Computer Science University of KentuckyDocument26 pagesParallel Computing Chapter 7 Performance and Scalability: Jun Zhang Department of Computer Science University of KentuckyWidya MeiriskaNo ratings yet
- Missing Topic of PCDocument4 pagesMissing Topic of PCHarseerat SidhuNo ratings yet
- WSS1 Assignement 1BDocument23 pagesWSS1 Assignement 1BFrancis DanielNo ratings yet
- 2009 ABB Distribution and Transmission Protection and Control Training BrochureDocument14 pages2009 ABB Distribution and Transmission Protection and Control Training BrochureRagab TolbaNo ratings yet
- Internet & Its UsageDocument40 pagesInternet & Its UsageNandini PamulaNo ratings yet
- CmpE207 Reader spr11Document285 pagesCmpE207 Reader spr11Sahana DwrakanathNo ratings yet
- OSI model and TCP/IP model quiz with answersDocument5 pagesOSI model and TCP/IP model quiz with answersMakbool Shah W.No ratings yet
- A2 PDFDocument12 pagesA2 PDFMuhammad Usman SajadNo ratings yet
- iDirect-Remote Installation Guide 2xDocument76 pagesiDirect-Remote Installation Guide 2xTulio ArteagaNo ratings yet
- Or5 Pragya LodhaDocument16 pagesOr5 Pragya LodhaSudhit SethiNo ratings yet
- Final ReviewDocument7 pagesFinal ReviewMonicaP18No ratings yet
- Advant® OCS With Master Software User's GuideDocument74 pagesAdvant® OCS With Master Software User's GuideSuvendra Dev DasNo ratings yet
- Argela Convergence Gateway (CGW) : Date: 09/11/2007 Code: RGLA - P - SDES - CGW - 1.5 Keyword: CGWDocument49 pagesArgela Convergence Gateway (CGW) : Date: 09/11/2007 Code: RGLA - P - SDES - CGW - 1.5 Keyword: CGWGiorgi PapavaNo ratings yet
- ch2 Introduction To Data Communications PDFDocument80 pagesch2 Introduction To Data Communications PDFMelek KüçükNo ratings yet
- Data Communication Networks - DCN Living in A Network Centric WorldDocument60 pagesData Communication Networks - DCN Living in A Network Centric Worldsumit_choudhary002No ratings yet
- Packet Switching: ConceptDocument27 pagesPacket Switching: ConceptOlivia SamarNo ratings yet
- 6-OSI Model-10-01-2022 (10-Jan-2022) Material - I - 10-01-2022 - OSI - TCP-IP - ModelDocument39 pages6-OSI Model-10-01-2022 (10-Jan-2022) Material - I - 10-01-2022 - OSI - TCP-IP - ModelPrerna SinghNo ratings yet
- 1KGT151051 IEC Conversion PDFDocument33 pages1KGT151051 IEC Conversion PDFSyed Sabeeh AhsanNo ratings yet
- CS-AI 2ND YEAR Final SyllabusDocument40 pagesCS-AI 2ND YEAR Final Syllabusafgha bNo ratings yet
- CCNA Networking Case StudyDocument81 pagesCCNA Networking Case StudyAnonymous D5g37JjpGBNo ratings yet
- XVR5108HS 4KL X PDFDocument3 pagesXVR5108HS 4KL X PDFTelefonia Unificada De Oscar MiyNo ratings yet
- ID-017 Instrument Communications PDFDocument70 pagesID-017 Instrument Communications PDFФизули АбиловNo ratings yet
- Internet BasicsDocument42 pagesInternet Basicstojerix332No ratings yet
- CCNA Training CCNA - Access List Questions 2Document12 pagesCCNA Training CCNA - Access List Questions 2dauzayl3529100% (1)
- IT430 Handouts 1 45Document187 pagesIT430 Handouts 1 45usmanNo ratings yet
- OSI Layer With Functionalities PDFDocument33 pagesOSI Layer With Functionalities PDFNikhil Sai NethiNo ratings yet
- Datasheet of DS 2DE7232IW AE (B)Document7 pagesDatasheet of DS 2DE7232IW AE (B)Archie FloresNo ratings yet
- Omniswitch2220 Datasheet enDocument4 pagesOmniswitch2220 Datasheet enchau.t.quangNo ratings yet
- Interview Question and AnswerDocument14 pagesInterview Question and AnswerTarik A R BiswasNo ratings yet