Professional Documents
Culture Documents
Privacy and Security in Aadhar
Uploaded by
046-ESHWARAN SCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Privacy and Security in Aadhar
Uploaded by
046-ESHWARAN SCopyright:
Available Formats
190701051
190701046
190701052
PRIVACY AND SECURITY IN AADHAR
INTRODUCTION:
The Aadhaar project is the world’s largest national identity project, launched by
government of India, which seeks to collect biometric and demographic data of residents and
store these in a centralised database. To date, 1036 million users have enrolled in the system,
and the government has spent at least 890 million USD on the project. However, recently
there has been considerable deliberations over the privacy and security issues related to the
Aadhaar project. In this article, we examine these issues from a Computer Science
perspective.
THE AADHAR MODEL:
1. The Unique Identification Authority of India (UIDAI) is responsible for providing
the basic identification and authentication services. It provides a unique identifier
(Aadhaar number) to each resident and maintains their biometric and demographic
data in a Central Identities Data Repository (CIDR). The UIDAI manages the CIDR
and provides identification and authentication services with yes/no answers.
2. An Authentication User Agency (AUA) who provides services to users that are
successfully authenticated. Thus, an AUA connects to the CIDR and uses Aadhaar
authentication to validate a user and enable its services. Examples of AUAs and
services are banks, various state and central government ministries providing services
such as the Public Distribution System (PDS), the National Rural Employment
Guarantee Scheme (NREGS), and even private agencies like mobile phone operators.
The responsibility of logistics of service delivery rests with the AUAs. In this
federated model an AUA may choose to use only Aadhaar identification, or also
authentication in conjunction with their own legacy identification and authentication
systems. An AUA is required to enter in to a formal contract with UIDAI to be able to
use Aadhaar authentication services.
3. An Authentication Service Agency (ASA) is an entity that has a secure leased line
connectivity with the CIDR. ASAs transmit authentication requests to CIDR on behalf
of one or more AUAs. An ASA enters into a formal contract with UIDAI.
4. The users, namely, the residents of the country who enrol themselves with UIDAI and
are issued unique identification numbers (Aadhaar numbers). A user has to present
this number as the basic identification to an AUA for availing Aadhaar authentication
services. The Aadhaar number for a user is common across all AUAs and service
domains.
5. The Point of Sale (POS) device, also known as authentication device which collects
personal identity data from Aadhaar holders, prepares the information for
transmission, transmits the authentication 4 packets for authentication and receives
the authentication results.
6. An Enrolment Station, which is a collection of field devices used by enrolment
agencies appointed by UIDAI to enrol people in to the Aadhaar database and capture
their demographic and biometric particulars.
Identity verification vs authentication:
Aadhaar is a national identity project, but we believe that the subtle difference between
identity verification and authentication is itself not well understood, and this leads to
confusions in policy making and deployment. Below, we attempt to first demarcate the two
concepts. According to standard notions of digital authentication, a security principal (a user
or a computer), while requesting access to a service, must provide two independent pieces of
information - identity and authentication. Whereas identity provides an answer to the
question “who are you?”, authentication is a challenge-response process that provides a
“proof of the claim of identity”, typically using an authentication credential. Common
examples of identity are User ID (Login ID), cryptographic public keys, email ids, ATM or
smart cards; some common authentication credentials are passwords (including OTPs), PINs
and cryptographic private keys. Identity may be considered public information but an
authentication credential must necessarily be private - a secret that is known only to the user.
Moreover, authentication must be a conscious process that requires active participation by a
user, but not necessarily so for identity verification. As example use cases, 5 a bank may
want an identity verification while opening an account at which stage no secret like a
password is usually necessary, but a user needs to authenticate with a PIN for transactions
like ATM withdrawals. No publicly known information should be used as an authentication
credential.
Privacy protection:
Fundamental assumptions To determine the extent to which security and privacy are
achieved, we must first define the desired expectations in this context. Our analysis is based
on the following assumptions, which we believe are fundamental:
1. Authentication without consent should never be possible under any circumstances.
Identification without consent should also not be possible except in some special situations
like disaster management, identification of accident victims, law enforcement and such
others. It should be noted that providing one’s identity for obtaining services in any local
context is always with consent.
2. Unapproved profiling, tracking and surveillance of individuals should not be possible.
There should be sufficiently strong measures to prevent such breaches in privacy, with user-verifiable
proof of the same.
3. The technical implementation of privacy and security must be provably correct with
respect to the legal framework. The legal framework, in turn, needs to be suitably enhanced with
special provisions to protect the privacy of individuals and society in an advanced information
technology setting.
Possible ways of breach of privacy
In what follows we briefly examine the various ways in which the privacy of an individual
can be compromised in a setting such as in Aadhaar.
1. Correlation of identities across domains: It may become possible to track an
individual’s activities across multiple domains of service (AUAs) using their global Aadhaar
ids which are valid across these domains. This would lead to identification without consent.
2. Identification without consent using Aadhaar data : There may be unauthorised
use of biometrics to illegally identify people. Such violations may include identifying people
by inappropriate matching of fingerprint or iris scans or facial photographs stored in the
Aadhaar database, or using the demographic data to identify people without their consent and
beyond legal provisions.
3. Illegal tracking of individuals : Individuals may be tracked or put under surveillance
without proper authorisation or legal sanction using the authentication and identification
records and trails in the Aadhaar database, or in one or more AUA’s databases. Such records
will typically also contain information on the precise location, time and context of the
authentication or identification, and the services availed. We wish to emphasize that insider
attacks are the most dangerous threats in this context. For instance, the second and third
attacks above are much more likely if the attacker can collude with an insider with access to
various components of the Aadhaar system.
Requirement analysis for privacy protection
In view of the above, effective privacy protection not only requires protecting the Aadhaar
system from external attacks but from internal attacks as well. This requires strong guarantees
on securing the data, logs and the transaction trails in the Aadhaar and the AUA systems.
Specifically, one requires that:
1. UIDAI cannot be trusted against possible system hacks, insider leaks, and tampering of
authentication records and audit trails. Indeed, the identity verification and authentication
providing applications running on UIDAI computer systems should be trustworthy even
when the UIDAI systems and the network cannot be trusted.
2. Manual inspection of user data, authentication records and audit trails should not be
possible. In special cases of properly authorised investigations, such inspections may only be
possible through pre-approved, audited and provably tamper proof computer programs, and
an accurate tamper proof record of the entire investigation and digitally signed authorisation
chain must be maintained at all times.
3. The enrolment agencies and the enrolment devices cannot be trusted from data privacy and
security points of view; neither can the Point of Sale (POS) devices and various
authentication user agencies (AUAs), whether government or private, be trusted for data
protection.
4. Authentication User Agencies (AUAs) cannot be trusted with biometric and demographic
data; neither can they be trusted with sensitive user data of private nature (for example,
medical and immunisation records etc.). All provisions of data privacy and security that apply
to UIDAI, must also apply to the AUAs. Strong legal and policy frameworks are required to
ensure this.
5. It should not be possible to correlate identities across application domains, except on
suitably anonymised data through pre-approved, audited and provably tamper proof computer
programs for carrying out data analysis. In what follows we discuss the various threats and
vulnerabilities that result from the Aadhaar project in more detail and analyse the measures
adopted by the UIDAI against these. We also suggest a few possibilities of enhancing the
privacy and security protections.
You might also like
- CART1Document46 pagesCART1aligadot4536No ratings yet
- Important Links Login Id and Password RM Details For PLDocument3 pagesImportant Links Login Id and Password RM Details For PLSaicharan UppalapattiNo ratings yet
- Hampering the Human Hacker and the Threat of Social EngineeringFrom EverandHampering the Human Hacker and the Threat of Social EngineeringNo ratings yet
- 01a - General Security ConceptsDocument61 pages01a - General Security ConceptsMa Hoàng Hải KhôiNo ratings yet
- Security Testing Handbook for Banking ApplicationsFrom EverandSecurity Testing Handbook for Banking ApplicationsRating: 5 out of 5 stars5/5 (1)
- PWDDocument3 pagesPWDSneha DubeyNo ratings yet
- JeremyDocument5 pagesJeremyPROJEKT PAWZNo ratings yet
- Enterprise Cyber Security Fundamentals: Presented by Matt ConstableDocument47 pagesEnterprise Cyber Security Fundamentals: Presented by Matt Constabletapera_mangeziNo ratings yet
- Citizen Card SystemDocument148 pagesCitizen Card SystemAzad Dhillon54% (13)
- Credentials ListDocument1 pageCredentials ListAlexssandra SevalhoNo ratings yet
- Aadhaar Project Presentation on India's National Identity SystemDocument15 pagesAadhaar Project Presentation on India's National Identity SystemArul Ambalavanan ThenappenNo ratings yet
- Aadhaar Authentication API 1 6Document37 pagesAadhaar Authentication API 1 6ranger1021994No ratings yet
- UID and Implications For Other Countries PDFDocument38 pagesUID and Implications For Other Countries PDFRuturaj SawantNo ratings yet
- AADHAAR - A Unique Identification Number: Opportunities and Challenges AheadDocument10 pagesAADHAAR - A Unique Identification Number: Opportunities and Challenges AheadResearch Cell: An International Journal of Engineering SciencesNo ratings yet
- Eligibility Criteria For AUA KUADocument25 pagesEligibility Criteria For AUA KUARam RNo ratings yet
- Aadhaar Authentication Framework v1.0 Explains Identity Proof OptionsDocument14 pagesAadhaar Authentication Framework v1.0 Explains Identity Proof OptionsShubham DwivediNo ratings yet
- Aadhaar Handbook For Registrars: Unique Identification Authority of India Planning Commission, Government of IndiaDocument35 pagesAadhaar Handbook For Registrars: Unique Identification Authority of India Planning Commission, Government of Indiaonc30187No ratings yet
- Aadhaar Authentication API 1.5Document29 pagesAadhaar Authentication API 1.5Syed Nazir RazikNo ratings yet
- (18 30) Marks Aadhaar Scam BSL FinalDocument15 pages(18 30) Marks Aadhaar Scam BSL FinalArjun AulNo ratings yet
- Ies Ips Academy Indore: Submitted To: Submitted byDocument11 pagesIes Ips Academy Indore: Submitted To: Submitted bysneh22No ratings yet
- R.V. College of EngineeringDocument17 pagesR.V. College of Engineeringashwinikh21No ratings yet
- Aadhaar Authentication API 1 5 Rev2Document33 pagesAadhaar Authentication API 1 5 Rev2parag_2k6No ratings yet
- AADHAAR - A Unique Identification Number Opportunities and Challenges Ahead PDFDocument10 pagesAADHAAR - A Unique Identification Number Opportunities and Challenges Ahead PDFRahul PinnamaneniNo ratings yet
- Aadhaar Handbook for Registrars GuideDocument35 pagesAadhaar Handbook for Registrars GuideAshutosh Kumar SinghNo ratings yet
- Aadharr System Case StudyDocument2 pagesAadharr System Case StudyviewpawanNo ratings yet
- Aadhaar FAQDocument16 pagesAadhaar FAQAbhishek_555No ratings yet
- C. in Older Identity Systems, It Was Normal To Load The ID Number With D. However This Makes The Number Susceptible To Fraud and Theft, and MigrationDocument13 pagesC. in Older Identity Systems, It Was Normal To Load The ID Number With D. However This Makes The Number Susceptible To Fraud and Theft, and MigrationManuBhatiaNo ratings yet
- Uidai - Aadhaar Card: E - CommerceDocument16 pagesUidai - Aadhaar Card: E - CommerceDeepali PanditNo ratings yet
- ICT RIght To Privacy (Aadhar Card)Document14 pagesICT RIght To Privacy (Aadhar Card)Vineet RajNo ratings yet
- Direct Benefit TransferDocument16 pagesDirect Benefit TransfershanujssNo ratings yet
- LSE ID BlueprintDocument12 pagesLSE ID BlueprintDexter B. Donaire IINo ratings yet
- Aadhaar Data LeaksDocument17 pagesAadhaar Data LeaksMintoo VermaNo ratings yet
- Aadhaar Usage-Dos and DontsDocument2 pagesAadhaar Usage-Dos and DontsrussainiNo ratings yet
- Aadhaar and Other Laws Amendment Bill 2018Document3 pagesAadhaar and Other Laws Amendment Bill 2018jeevitharkgNo ratings yet
- Cartes 2010 UID Aadhaar ArticleDocument3 pagesCartes 2010 UID Aadhaar ArticleManju S MurthyNo ratings yet
- Inbound 7203216121794448310Document3 pagesInbound 7203216121794448310Julesbon ParsaliganNo ratings yet
- Project Plan AADHAR ProjectDocument9 pagesProject Plan AADHAR ProjectIndranath MitraNo ratings yet
- THEKEY Whitepaper 171112 PDFDocument50 pagesTHEKEY Whitepaper 171112 PDFeo112No ratings yet
- Aadhaar Myth Busters - Unique Identification Authority of India - Government of IndiaDocument3 pagesAadhaar Myth Busters - Unique Identification Authority of India - Government of IndiabpbhattiNo ratings yet
- ABOUT UID-Aadhaar Number-MANMOHAN SINGH CHANDOLIYADocument17 pagesABOUT UID-Aadhaar Number-MANMOHAN SINGH CHANDOLIYAMANMOHAN SINGH CHANDOLIYANo ratings yet
- White Card Management Systems.Document6 pagesWhite Card Management Systems.Gateway ManagerNo ratings yet
- Uidai Citizen Charter FinalDocument18 pagesUidai Citizen Charter FinalMind OptimaNo ratings yet
- GDPR QuestionnaireDocument3 pagesGDPR QuestionnaireLeopoldo DelgadoNo ratings yet
- Introduction to Biometric Systems for Identification and AuthenticationDocument8 pagesIntroduction to Biometric Systems for Identification and AuthenticationAayush SrivastavaNo ratings yet
- IdentificationDocument7 pagesIdentificationSachin Kumar PatelNo ratings yet
- Aadhaar FAQs ExplainedDocument6 pagesAadhaar FAQs ExplainedVaibhav MarodeNo ratings yet
- A Question of Identity: What Should Aadhaar Be LikeDocument12 pagesA Question of Identity: What Should Aadhaar Be LikeDeepak UpadhyayNo ratings yet
- Unique Identification Number Repaired)Document22 pagesUnique Identification Number Repaired)sweet_binalNo ratings yet
- How to protect personal dataDocument15 pagesHow to protect personal datakai Leo-AndohNo ratings yet
- Fingerprint Biometric Based Online Cashless Payment SystemDocument6 pagesFingerprint Biometric Based Online Cashless Payment SystempranathiNo ratings yet
- Biometric Authentications To Control ATM Theft: Ahmad Tasnim SiddiquiDocument6 pagesBiometric Authentications To Control ATM Theft: Ahmad Tasnim SiddiquiAhmad T SiddiquiNo ratings yet
- ITSM Retaining The DataDocument3 pagesITSM Retaining The DatavishnuameyaNo ratings yet
- Aadhaar Act 2016 Upsc Notes 82Document3 pagesAadhaar Act 2016 Upsc Notes 82Avik PodderNo ratings yet
- Smart Card Technology in Healthcare FAQ FINAL 052709Document14 pagesSmart Card Technology in Healthcare FAQ FINAL 052709Adireddy SatyatrinadhNo ratings yet
- A Brief Introduction of Biometrics and Fingerprint Payment TechnologyDocument14 pagesA Brief Introduction of Biometrics and Fingerprint Payment TechnologyRajwecNo ratings yet
- Aadhaar Overview by BioenableDocument10 pagesAadhaar Overview by Bioenablenikhiljain17No ratings yet
- Advantages: - SecurityDocument4 pagesAdvantages: - SecurityABBILASHANo ratings yet
- Everything You Need to Know About Aadhaar, India's Unique ID ProgramDocument3 pagesEverything You Need to Know About Aadhaar, India's Unique ID ProgramS Dinesh KumarNo ratings yet
- Uid-Aadhar: What Is Unique Identification Authority of India (UIDAI) and Where Does It Get Its Authority From?Document6 pagesUid-Aadhar: What Is Unique Identification Authority of India (UIDAI) and Where Does It Get Its Authority From?Geordie Job PottasNo ratings yet
- Digital Identity: Appendix B: Case StudiesDocument16 pagesDigital Identity: Appendix B: Case StudiesCash Cash CashNo ratings yet
- NIDDocument14 pagesNIDNeethu PrakashNo ratings yet
- Chapter 3 CaseDocument2 pagesChapter 3 CaseLordNo ratings yet
- Innovya Traceless Biometrics TechnologyDocument7 pagesInnovya Traceless Biometrics TechnologyMicha.Shafir100% (4)
- Aadhaar Card ControversyDocument18 pagesAadhaar Card ControversySugandha Kaul100% (1)
- Bio MetricsDocument3 pagesBio MetricsMohd ShoebNo ratings yet
- Aadhaar Enabled Service Delivery: WWW - Uidai.gov - inDocument26 pagesAadhaar Enabled Service Delivery: WWW - Uidai.gov - inSahilRainaNo ratings yet
- PCI DSS Version 4.0: A guide to the payment card industry data security standardFrom EverandPCI DSS Version 4.0: A guide to the payment card industry data security standardNo ratings yet
- Change of Sim FormDocument1 pageChange of Sim FormPrincess Maevelle Chan PecaocoNo ratings yet
- Two Factor AuthenticationDocument12 pagesTwo Factor Authenticationmulemy46No ratings yet
- E-Travel Management System - Activity DiagramsDocument6 pagesE-Travel Management System - Activity DiagramsSandesh AhirNo ratings yet
- VouchersDocument4 pagesVouchersBeniSaputroNo ratings yet
- OI2 Bavjd ZLVZC 1 RsDocument8 pagesOI2 Bavjd ZLVZC 1 RsRavi S. SharmaNo ratings yet
- Pia Casos Ed Eq3Document77 pagesPia Casos Ed Eq3tomas olvera sepulvedaNo ratings yet
- Securenvoy Server Administration GuideDocument112 pagesSecurenvoy Server Administration GuideAllen ValseNo ratings yet
- Security Hub ReportDocument16 pagesSecurity Hub Reporthenryvu2205No ratings yet
- ComponentSpace ADFS Relying Party Integration GuideDocument42 pagesComponentSpace ADFS Relying Party Integration GuideАндрей ТиминNo ratings yet
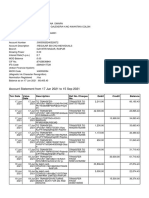
- Account Statement From 1 Mar 2023 To 31 Mar 2023: TXN Date Value Date Description Ref No./Cheque No. Debit Credit BalanceDocument3 pagesAccount Statement From 1 Mar 2023 To 31 Mar 2023: TXN Date Value Date Description Ref No./Cheque No. Debit Credit BalancePrashant ShuklaNo ratings yet
- Configuring MAC-Based Authentication On A Switch Through The Command Line InterfaceDocument14 pagesConfiguring MAC-Based Authentication On A Switch Through The Command Line InterfaceBuba HanakoyeNo ratings yet
- PSO 0905 Operation of The Police National ComputerDocument26 pagesPSO 0905 Operation of The Police National ComputerhollandusaNo ratings yet
- Validate Registration, Login & Payment PagesDocument11 pagesValidate Registration, Login & Payment Pagessingaram VenkateshNo ratings yet
- v1 Kode Script Hack FB HTML Inspect ElementDocument1 pagev1 Kode Script Hack FB HTML Inspect ElementBhono Rada KerokNo ratings yet
- APS 2016 Registration Login DetailsDocument1 pageAPS 2016 Registration Login Detailsdurgesh srivastavaNo ratings yet
- Skype BruteDocument2 pagesSkype BruteMarko SavicNo ratings yet
- IT Access Control and Account Management StandardDocument9 pagesIT Access Control and Account Management StandardMagda FakhryNo ratings yet
- Poster Get Your New Microsoft ID @DELIMaDocument1 pagePoster Get Your New Microsoft ID @DELIMaMOHD FIRDAUS BIN MOHD JAMIL MoeNo ratings yet
- SSOLoginDocument5 pagesSSOLoginsreeharivaletiNo ratings yet
- B3000 Installation Guide: Standard SettingsDocument3 pagesB3000 Installation Guide: Standard SettingsultimatemobileNo ratings yet
- E-Statement 25-07-2021Document1 pageE-Statement 25-07-2021swathiNo ratings yet
- How to install SSH accountsDocument3 pagesHow to install SSH accountsHajauNo ratings yet
- Sec Tech: Firewalls and VPNsDocument76 pagesSec Tech: Firewalls and VPNsAbdiraxman MaxamedNo ratings yet