Professional Documents
Culture Documents
CMS Lec1
Uploaded by
Shaimaa Ashraf0 ratings0% found this document useful (0 votes)
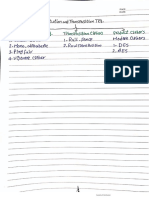
3 views3 pages1. The document discusses various types of attacks that can compromise computer security systems, including malware infection, software spying, and exploiting system weaknesses.
2. It covers security goals like confidentiality, integrity, and availability that aim to protect information and resources from threats or hazards.
3. Vulnerabilities in security systems that can damage systems or steal data are called exploits, while using exploits to carry out attacks is called hacking.
Original Description:
security
Original Title
CMS lec1
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this Document1. The document discusses various types of attacks that can compromise computer security systems, including malware infection, software spying, and exploiting system weaknesses.
2. It covers security goals like confidentiality, integrity, and availability that aim to protect information and resources from threats or hazards.
3. Vulnerabilities in security systems that can damage systems or steal data are called exploits, while using exploits to carry out attacks is called hacking.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
3 views3 pagesCMS Lec1
Uploaded by
Shaimaa Ashraf1. The document discusses various types of attacks that can compromise computer security systems, including malware infection, software spying, and exploiting system weaknesses.
2. It covers security goals like confidentiality, integrity, and availability that aim to protect information and resources from threats or hazards.
3. Vulnerabilities in security systems that can damage systems or steal data are called exploits, while using exploits to carry out attacks is called hacking.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 3
1. Piece of code infect your device for damaging is …………………..
2. Software is set on your computer for spying on each action ………………
3. Weakness is in a system and can be exploit ………………
4. Computer security also known as ………………. And ……………………
5. Computer security aims for ………………............................... from ………. or ………
6. Security goals are divided into …………………..., ……………… and ………….. (CIA)
7. Confidentiality try to …………… information , keep information …………... ,
revealing only to ……………………
8. Weakness in security system that can be used to damage the system or steal
information is called …………………
9. Integrity is the information that can be …………. And try to detect or prevent
…………….. modification
10. Availability is ………….. to information and resources and services are always
available to ……………… users
11. ………... is a possible danger that might make use of a vulnerability
12. An assault on system security or any action compromises the security is ………..
13. Categories of vulnerabilities if:
Corrupted data mean loss of ……………………
Leaky mean loss of ……………………
Unavailable or very slow mean loss of ……………………..
14. Use of the vulnerability and threats is called ………………
15. Types of attack are …………… and …………..
16. ………….. attack affect on system operation while ……….. attack doesn’t affect on
system resources
17. ……………… one who is implements attack
18. Types of threats :
………………….. : is unauthorized access to information
this threat to (Confidentiality – Integrity – Availability – All)
………………….. : is acceptance of false data
This threat to (Confidentiality – Integrity – Availability – All)
………………….: is interruption of correct operation
This threat to (Confidentiality – Integrity – Availability – All)
……………….. : is unauthorized system control
This threat to (Confidentiality – Integrity – Availability – All)
19. Communication security try to prevent ………… or detect ……………
20. Write the types of attack on each diagram
21. An asset of the system is destroyed or becomes unavailable or disrupting traffic is
…………….. which is an attack on (Confidentiality – Integrity – Availability – All)
22. Faking data or unauthorized party inserts into a system is …………………. which is
an attack on (Confidentiality – Integrity – Availability – All)
23. Overhearing over a communication line is …………………… which is an attack on
(Confidentiality – Integrity – Availability – All)
24. Corrupting transmitted data or tampering or change data before it reach its
destination is ……………. which is an attack on (Confidentiality – Integrity –
Availability – All)
25. ………….. attack that the attacker obtaining information without any modification and
it is (easy – difficult) to detect
26. Categories of passive attack are …………………….………. And ………………
27. Categories if active attack are ……………….. , ……………… , …………….. and
……………
28. Release of message is also called ……………. While traffic analysis is called ………
29. …….…… refers to unauthorized access to data or interception of data
30. ….……… refers to obtaining some other of information by monitoring online traffic
31. In traffic analysis (Spoofing) the attacker can determine the ……..…… and ………...
Of the host
32. Modification of data is type of (Passive - Active) attack
33. When an entity pretends to be different entity is (Replay – Masquerade –
Modification of message) which is an attack on (Confidentiality – Integrity –
Availability – All)
34. Some portions of message are altered is (Replay – Masquerade – Modification of
message) which is an attack on (Confidentiality – Integrity – Availability – All)
35. Involves the passive capture of data and retransmission to produce an unauthorized
effect (Replay – Masquerade – Modification of message) which is an attack on
(Confidentiality – Integrity – Availability – All)
36. Snooping and traffic analysis (spoofing) are attack on (Confidentiality – Integrity –
Availability – All)
37. DOS is attack on (Confidentiality – Integrity – Availability – All)
You might also like
- CEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021From EverandCEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021No ratings yet
- Attacking Rfid SystemsDocument20 pagesAttacking Rfid SystemsRamalingNo ratings yet
- Hacking Terminologies EbookDocument35 pagesHacking Terminologies EbookPraneeth Anpur100% (1)
- Oscp PDFDocument31 pagesOscp PDFYnaiara AparecidaNo ratings yet
- Security Reference HandbookDocument76 pagesSecurity Reference HandbookramiNo ratings yet
- La-Dimora Brochure PDFDocument23 pagesLa-Dimora Brochure PDFGaurav AggarwalNo ratings yet
- Securing ChatGPT: Best Practices for Protecting Sensitive Data in AI Language ModelsFrom EverandSecuring ChatGPT: Best Practices for Protecting Sensitive Data in AI Language ModelsNo ratings yet
- Attribution of Advanced Persistent Threats: How to Identify the Actors Behind Cyber-EspionageFrom EverandAttribution of Advanced Persistent Threats: How to Identify the Actors Behind Cyber-EspionageRating: 5 out of 5 stars5/5 (1)
- The Certified Ethical Hacker Exam - version 8 (The concise study guide)From EverandThe Certified Ethical Hacker Exam - version 8 (The concise study guide)Rating: 3 out of 5 stars3/5 (9)
- 葛传椝英语写作 by 葛传椝 (葛传椝)Document416 pages葛传椝英语写作 by 葛传椝 (葛传椝)付明璘100% (1)
- BruteForce SSH Attack StudyDocument36 pagesBruteForce SSH Attack StudysegrelNo ratings yet
- Penetration TestingDocument28 pagesPenetration TestingNour BushNo ratings yet
- Case Digests in Statutory Construction Philippine Law StudentDocument58 pagesCase Digests in Statutory Construction Philippine Law StudentJoshua Emmanuel100% (5)
- Value-Based Pricing: The Driver To Increased Short-Term ProfitsDocument4 pagesValue-Based Pricing: The Driver To Increased Short-Term ProfitsRiz DeenNo ratings yet
- Cars4u Project: Proprietary Content. © Great Learning. All Rights Reserved. Unauthorized Use or Distribution ProhibitedDocument30 pagesCars4u Project: Proprietary Content. © Great Learning. All Rights Reserved. Unauthorized Use or Distribution ProhibitedAbhay Poddar100% (2)
- Rebirthing Philippine ForestsDocument50 pagesRebirthing Philippine Forestsfpe_scribdNo ratings yet
- Introduction To Network Security ThreatsDocument8 pagesIntroduction To Network Security Threatsiwc2008007100% (1)
- Operating System Security 2008Document236 pagesOperating System Security 2008j2ch5en100% (11)
- Quiz Infection Prevention and Control MDocument3 pagesQuiz Infection Prevention and Control MGareth McKnight0% (1)
- Intrusion Detection SystemDocument36 pagesIntrusion Detection SystemNand LalNo ratings yet
- BS en Iso 11125-6-1997 (2000) BS 7079-E11-1994 PDFDocument12 pagesBS en Iso 11125-6-1997 (2000) BS 7079-E11-1994 PDFShankar GurusamyNo ratings yet
- More Than Hot Air: The Lasting Impact of Inflatable Architecture - in The AirDocument17 pagesMore Than Hot Air: The Lasting Impact of Inflatable Architecture - in The Airbarry4zimmerman3No ratings yet
- Security for Microsoft Windows System Administrators: Introduction to Key Information Security ConceptsFrom EverandSecurity for Microsoft Windows System Administrators: Introduction to Key Information Security ConceptsRating: 4 out of 5 stars4/5 (1)
- Nursing Council CXC Past Paper MCQ (1) (319) IMPORTANTDocument25 pagesNursing Council CXC Past Paper MCQ (1) (319) IMPORTANTAaron Wallace88% (32)
- Fayol General and Industrial Management PDFDocument2 pagesFayol General and Industrial Management PDFJennifer33% (6)
- Read The Text and Answer The Questions That Follow.: 1 Complete The Sentences Using The Information Given in The TextDocument2 pagesRead The Text and Answer The Questions That Follow.: 1 Complete The Sentences Using The Information Given in The TextTeresa ValverdeNo ratings yet
- Competitive Profile Matrix (CPM)Document17 pagesCompetitive Profile Matrix (CPM)AaaaaaNo ratings yet
- CMS Lecture 1 AnswerDocument3 pagesCMS Lecture 1 AnswerShaimaa AshrafNo ratings yet
- Esecurity ReportDocument23 pagesEsecurity Reportapi-3700991No ratings yet
- Hardware VandalismDocument6 pagesHardware VandalismAhmed ZiadNo ratings yet
- Ethical Hacking Unit-3Document9 pagesEthical Hacking Unit-3Sunil Gautam0% (1)
- Digital SecurityDocument21 pagesDigital SecurityKrishna NayakNo ratings yet
- Information and Communication Technology Paper 2 StructredDocument6 pagesInformation and Communication Technology Paper 2 StructredRatnasiri ArangalaNo ratings yet
- Maltego Whitepaper Threat Intel Providers For Small SOC TeamsDocument29 pagesMaltego Whitepaper Threat Intel Providers For Small SOC TeamsIvan DoriNo ratings yet
- COMPUTER SECURITY Definition & NeedDocument98 pagesCOMPUTER SECURITY Definition & Need142 Bhumika LachakeNo ratings yet
- Information SecurityDocument24 pagesInformation Security3bdelr7man z3z3No ratings yet
- Seminar Report: " Intrusion Detection SystemDocument38 pagesSeminar Report: " Intrusion Detection SystemChaitanyaNo ratings yet
- Ôn tập TACNDocument42 pagesÔn tập TACNKhánh MinhNo ratings yet
- CybersecDocument3 pagesCybersecGayathri.SNo ratings yet
- Information SecurityDocument39 pagesInformation SecurityRem RemNo ratings yet
- Ethical HackingDocument2 pagesEthical HackingsachvinawiniNo ratings yet
- Ethical Hacking: by Sachin TyagiDocument27 pagesEthical Hacking: by Sachin TyagiHarsh BajajNo ratings yet
- WhitepaperDocument115 pagesWhitepaperRipunjoy SonowalNo ratings yet
- Intrusion Detection SystemsDocument18 pagesIntrusion Detection Systemsapi-3827000No ratings yet
- Xerox Workcentre 5632/5638/5645/5655/5665/5675/5687 Multifunction Systems Security TargetDocument89 pagesXerox Workcentre 5632/5638/5645/5655/5665/5675/5687 Multifunction Systems Security TargetSunny SinghNo ratings yet
- Module 5-OsDocument25 pagesModule 5-Oscreations400abNo ratings yet
- OSINT CyberTalentsDocument8 pagesOSINT CyberTalentsaneyomainstreamNo ratings yet
- Os 213Document35 pagesOs 213Ankur SinghNo ratings yet
- IA LectureSlideCh-3Document31 pagesIA LectureSlideCh-3AB FruitNo ratings yet
- On Ethical Hacking: Prepared By:-Bhargav Dabhi (090010107040)Document18 pagesOn Ethical Hacking: Prepared By:-Bhargav Dabhi (090010107040)Rijy LoranceNo ratings yet
- Basic PrinciplesDocument15 pagesBasic PrinciplesErnest Kamrad BndNo ratings yet
- Report Ruag Espionage CaseDocument34 pagesReport Ruag Espionage Casemaruka33No ratings yet
- The Road Map of A VirusDocument3 pagesThe Road Map of A VirusmominansariNo ratings yet
- Data Integrity & SecurityDocument3 pagesData Integrity & SecurityReshma WawhalNo ratings yet
- Information SecurityDocument15 pagesInformation SecurityDanish KhanNo ratings yet
- 02 Hacking Concepts HandoutDocument7 pages02 Hacking Concepts Handoutzoword70100% (1)
- CS 685-002: Security in Mobile Computing Systems Term PaperDocument38 pagesCS 685-002: Security in Mobile Computing Systems Term PaperItwzfnbeing ZeronineNo ratings yet
- Int Us IonDocument13 pagesInt Us IonHinaa SyedNo ratings yet
- PIPE InjectDocument12 pagesPIPE InjectOscar Millan ChavarriaNo ratings yet
- Code Injection and Computer VirusesDocument66 pagesCode Injection and Computer VirusesBeerend CeulemansNo ratings yet
- Computer and Network Security Notes Bca 6 Semester: Unit 1Document53 pagesComputer and Network Security Notes Bca 6 Semester: Unit 1Rohit SolankiNo ratings yet
- CS&P CHP 1Document31 pagesCS&P CHP 1BESUFEKAD TABORNo ratings yet
- Computer Literacy 4Document127 pagesComputer Literacy 4Gabriel MashoodNo ratings yet
- I.C.T Method Past QuestionDocument84 pagesI.C.T Method Past QuestionKelly KelvinNo ratings yet
- Computer Security ThreatsDocument38 pagesComputer Security ThreatsIDRISA NKUNYANo ratings yet
- 6b79 PDFDocument66 pages6b79 PDFደስታ ጌታውNo ratings yet
- Implications of Rootkit To User Privacy: Term PaperDocument14 pagesImplications of Rootkit To User Privacy: Term PaperpraneethkorallaNo ratings yet
- Cyber CrimesDocument13 pagesCyber CrimesChege AmbroseNo ratings yet
- Chapter 3: Tools and Methods Used in CybercrimeDocument34 pagesChapter 3: Tools and Methods Used in CybercrimeNarasimha MurthyNo ratings yet
- Numerical Method3Document21 pagesNumerical Method3Shaimaa AshrafNo ratings yet
- CMS ProblemsDocument11 pagesCMS ProblemsShaimaa AshrafNo ratings yet
- CMS Lecture 2 AnswersDocument2 pagesCMS Lecture 2 AnswersShaimaa AshrafNo ratings yet
- Numerical Method - MT Jan 2015Document3 pagesNumerical Method - MT Jan 2015Shaimaa AshrafNo ratings yet
- Numerical Method - Finalt F 2014Document4 pagesNumerical Method - Finalt F 2014Shaimaa AshrafNo ratings yet
- Desktop Documents Downloads Music Pictures Public Templates VideosDocument22 pagesDesktop Documents Downloads Music Pictures Public Templates VideosShaimaa AshrafNo ratings yet
- Assignment 2-103Document1 pageAssignment 2-103Shaimaa AshrafNo ratings yet
- 200 SongsDocument5 pages200 SongsJocelyn Atangan Alaba50% (2)
- Telephone Directory 2018Document6 pagesTelephone Directory 2018CLO GENSANNo ratings yet
- Token Bus (IEEE 802)Document9 pagesToken Bus (IEEE 802)anon_185146696No ratings yet
- March 28 2013 Mount Ayr Record-NewsDocument14 pagesMarch 28 2013 Mount Ayr Record-NewsMountAyrRecordNewsNo ratings yet
- A Beginner's Guide To Large Language Mo-Ebook-Part1Document25 pagesA Beginner's Guide To Large Language Mo-Ebook-Part1John O'MearaNo ratings yet
- Linear Search in JavaDocument2 pagesLinear Search in JavaWipuli Lochana DisanayakeNo ratings yet
- E-07e-AUF Magnetic Fields in CoilsDocument7 pagesE-07e-AUF Magnetic Fields in CoilsV. GrigorasNo ratings yet
- ZumbroShopper15 10 07Document12 pagesZumbroShopper15 10 07Kristina HicksNo ratings yet
- The Evidence Base For The Efficacy of Antibiotic Prophylaxis in Dental PracticeDocument17 pagesThe Evidence Base For The Efficacy of Antibiotic Prophylaxis in Dental PracticebmNo ratings yet
- Homogenize RsDocument16 pagesHomogenize RsNamraNo ratings yet
- Basic Keyboarding & Fastyping: by The End of This Module, Students Must Be Able ToDocument7 pagesBasic Keyboarding & Fastyping: by The End of This Module, Students Must Be Able TomaristellaNo ratings yet
- Preliminary Energy Audit Methodology Preliminary Energy Audit Is A Relatively Quick Exercise ToDocument1 pagePreliminary Energy Audit Methodology Preliminary Energy Audit Is A Relatively Quick Exercise Tojons ndruwNo ratings yet
- Excel Property Management Invoice TemplateDocument10 pagesExcel Property Management Invoice Templatenull22838No ratings yet
- Issue 490Document44 pagesIssue 490The Independent MagazineNo ratings yet
- Ict351 4 Logical FormulasDocument32 pagesIct351 4 Logical FormulastheoskatokaNo ratings yet
- Fortnightly Tax Table 2016 17Document10 pagesFortnightly Tax Table 2016 17nirpatel2No ratings yet
- HSE L141 - 2005 - Whole-Body VibrationDocument56 pagesHSE L141 - 2005 - Whole-Body VibrationKris WilochNo ratings yet
- OCTG & PIPELINE Coatings Brochure PDFDocument41 pagesOCTG & PIPELINE Coatings Brochure PDFfelipe castellanosNo ratings yet