Professional Documents
Culture Documents
Cybersecurity Competence
Uploaded by
shanthi rajesh0 ratings0% found this document useful (0 votes)
5 views3 pagesThe document outlines 8 domains of cybersecurity competence:
1. Security and risk management including governance, compliance, risk analysis and security policies.
2. Asset security such as data classification, ownership and privacy.
3. Security architecture and engineering including secure design principles and vulnerability assessment.
4. Communication and network security including secure network components and channels.
5. Identity and access management including control of physical/logical access and user provisioning.
6. Security assessment and testing including strategies, controls testing and auditing.
7. Security operations including investigations, logging, patching and incident management.
8. Software development security including the SDLC, coding standards and acquired software
Original Description:
CyberSEcurity
Copyright
© © All Rights Reserved
Available Formats
DOCX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThe document outlines 8 domains of cybersecurity competence:
1. Security and risk management including governance, compliance, risk analysis and security policies.
2. Asset security such as data classification, ownership and privacy.
3. Security architecture and engineering including secure design principles and vulnerability assessment.
4. Communication and network security including secure network components and channels.
5. Identity and access management including control of physical/logical access and user provisioning.
6. Security assessment and testing including strategies, controls testing and auditing.
7. Security operations including investigations, logging, patching and incident management.
8. Software development security including the SDLC, coding standards and acquired software
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
5 views3 pagesCybersecurity Competence
Uploaded by
shanthi rajeshThe document outlines 8 domains of cybersecurity competence:
1. Security and risk management including governance, compliance, risk analysis and security policies.
2. Asset security such as data classification, ownership and privacy.
3. Security architecture and engineering including secure design principles and vulnerability assessment.
4. Communication and network security including secure network components and channels.
5. Identity and access management including control of physical/logical access and user provisioning.
6. Security assessment and testing including strategies, controls testing and auditing.
7. Security operations including investigations, logging, patching and incident management.
8. Software development security including the SDLC, coding standards and acquired software
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
You are on page 1of 3
Cybersecurity Competence:
Domain 1: Security and Risk Management
- Understand and apply concepts of confidentiality, integrity and availability
- Evaluate and apply security governance principles
- Determine compliance requirements
- Understand legal and regulatory issues that pertain to information security in a global context
- Understand, adhere to, and promote professional ethics
- Develop, document, and implement security policy, standards, procedures, and guidelines
- Identify, analyze, and prioritize Business Continuity (BC) requirements
- Contribute to and enforce personnel security policies and procedures
- Understand and apply risk management concepts
- Understand and apply threat modelling concepts and methodologies
- Apply risk-based management concepts to the supply chain
- Establish and maintain a security awareness, education, and training program
Domain 2: Asset Security
- Identify and classify information and assets
- Determine and maintain information and asset ownership
- Protect privacy - Ensure appropriate asset retention
- Determine data security controls
- Establish information and asset handling requirements
Domain 3: Security Architecture and Engineering
- Implement and manage engineering processes using secure design principles
- Understand the fundamental concepts of security models
- Select controls based upon systems security requirements
- Understand security capabilities of information systems (e.g., memory protection, Trusted
Platform Module (TPM), encryption/decryption)
- Assess and mitigate the vulnerabilities of security architectures, designs, and solution elements
- Assess and mitigate vulnerabilities in web-based systems
- Assess and mitigate vulnerabilities in mobile systems
- Assess and mitigate vulnerabilities in embedded devices
- Apply cryptography - Apply security principles to site and facility design
- Implement site and facility security controls
Domain 4: Communication and Network Security
- Implement secure design principles in network architectures
- Secure network components
- Implement secure communication channels according to design
Domain 5: Identity and Access Management (IAM)
- Control physical and logical access to assets
- Manage identification and authentication of people, devices, and services
- Integrate identity as a third-party service
- Implement and manage authorization mechanisms
- Manage the identity and access provisioning lifecycle
Domain 6: Security Assessment and Testing
- Design and validate assessment, test, and audit strategies
- Conduct security control testing
- Collect security process data (e.g., technical and administrative)
- Analyse test output and generate report
- Conduct or facilitate security audits
Domain 7: Security Operations
- Understand and support investigations
- Understand requirements for investigation types
- Conduct logging and monitoring activities
- Securely provisioning resources
- Understand and apply foundational security operations concepts
- Apply resource protection techniques
- Conduct incident management
- Operate and maintain detective and preventative measures
- Implement and support patch and vulnerability management
- Understand and participate in change management processes
- Implement recovery strategies
- Implement Disaster Recovery (DR) processes
- Test Disaster Recovery Plans (DRP)
- Participate in Business Continuity (BC) planning and exercises
- Implement and manage physical security
- Address personnel safety and security concerns
Domain 8: Software Development Security
- Understand and integrate security in the Software Development Life Cycle (SDLC)
- Identify and apply security controls in development environments
- Assess the effectiveness of software security
- Assess security impact of acquired software
- Define and apply secure coding guidelines and standards
You might also like
- Information Security ManagementDocument33 pagesInformation Security ManagementBCC College DepartmentNo ratings yet
- Program:B.Tech (BA+BD) Course Code:CSBD4070 Course Name:Big Data SecurityDocument23 pagesProgram:B.Tech (BA+BD) Course Code:CSBD4070 Course Name:Big Data SecurityVairavel ChenniyappanNo ratings yet
- Issue Specific Security PoliciesDocument20 pagesIssue Specific Security PoliciesPankaj MalviyaNo ratings yet
- Chapter (4) - ModifiedDocument27 pagesChapter (4) - Modifiedغسان الشليفNo ratings yet
- Sec Arch TrainingDocument10 pagesSec Arch TrainingIt ProfessionalNo ratings yet
- IT Infrastructure Audit ScopeDocument2 pagesIT Infrastructure Audit Scopeegidiah15No ratings yet
- SPG U4 2Document25 pagesSPG U4 2S.DixitNo ratings yet
- Nformation Ecurity Olicy: HapterDocument51 pagesNformation Ecurity Olicy: HapterBin FlanNo ratings yet
- UntitledDocument8 pagesUntitledLEE PEI YI YUKINo ratings yet
- CH 14Document34 pagesCH 14Firas ZawaidehNo ratings yet
- How To Prepare For The CISSP Exam: Outline, Study Tips & StrategyDocument37 pagesHow To Prepare For The CISSP Exam: Outline, Study Tips & StrategyDodo winyNo ratings yet
- Unit 3 (A)Document70 pagesUnit 3 (A)Dennis Ebenezer DhanarajNo ratings yet
- 8 Access Control - CISSPDocument86 pages8 Access Control - CISSPChristian GccNo ratings yet
- Cissp Domain Refresh Webinar SlidesDocument35 pagesCissp Domain Refresh Webinar Slidesuwb_groupNo ratings yet
- 2.critical Characteristics of InformationDocument29 pages2.critical Characteristics of InformationVairavel ChenniyappanNo ratings yet
- Information Security-Assignment #04Document7 pagesInformation Security-Assignment #04maidah sabirNo ratings yet
- Access Control Domain: Cissp Common Body of Knowledge ReviewDocument86 pagesAccess Control Domain: Cissp Common Body of Knowledge ReviewKaran MehtaNo ratings yet
- Certified Information Systems Security Professional - CISSPDocument3 pagesCertified Information Systems Security Professional - CISSPirfantrvlNo ratings yet
- INFO 333 - Introduction To Information Security: Week 1Document5 pagesINFO 333 - Introduction To Information Security: Week 1Marty SharkingtonNo ratings yet
- RISK ASSESSMENT FOR IT TemplateDocument8 pagesRISK ASSESSMENT FOR IT Templatejenito215402No ratings yet
- Lecture 5Document34 pagesLecture 5Tinotenda NyawashaNo ratings yet
- IT Information Security Management Principles, 23 - 26 November 2015 Dubai UAEDocument4 pagesIT Information Security Management Principles, 23 - 26 November 2015 Dubai UAE360 BSINo ratings yet
- Principles of Information Security, Fifth EditionDocument67 pagesPrinciples of Information Security, Fifth EditionCharlito MikolliNo ratings yet
- Security Policy DocumentDocument5 pagesSecurity Policy DocumentKefa MwitaNo ratings yet
- The Structure of ISO 27001Document11 pagesThe Structure of ISO 27001Mohammed Abdus Subhan100% (1)
- 4 Operations SecurityDocument69 pages4 Operations SecurityRuppee EdwardNo ratings yet
- Recommended Data Practices (ISO 27001, 27002)Document46 pagesRecommended Data Practices (ISO 27001, 27002)shifan110% (1)
- UEU Jaminan Dan Kemanan Informasi Pertemuan 3Document31 pagesUEU Jaminan Dan Kemanan Informasi Pertemuan 3bangiNo ratings yet
- ISA1 Module1Topic3Document67 pagesISA1 Module1Topic3サカイ アルジェイNo ratings yet
- IA MethodologyDocument20 pagesIA MethodologySiddharthNo ratings yet
- Principles of Information SecurityDocument67 pagesPrinciples of Information Securityali sheikhNo ratings yet
- A Sensitive Data Test Strategy Outlines The ApproachDocument2 pagesA Sensitive Data Test Strategy Outlines The ApproachneeleshsinghtomarNo ratings yet
- CISSP Student Guide V2.0Document913 pagesCISSP Student Guide V2.0thetzo100% (5)
- Course Overview: This Course Provides In-Depth Coverage of The Eight Domains Required To Pass The CISSP ExamDocument30 pagesCourse Overview: This Course Provides In-Depth Coverage of The Eight Domains Required To Pass The CISSP ExamAbdul GhaffarNo ratings yet
- FALLSEM2022-23 CSE3501 ETH VL2022230103435 Reference Material I 19-10-2022 Lect 20Document33 pagesFALLSEM2022-23 CSE3501 ETH VL2022230103435 Reference Material I 19-10-2022 Lect 20Rajvansh SinghNo ratings yet
- Isms ReportDocument5 pagesIsms ReportWanambisi JnrNo ratings yet
- Unit-5 Info SecuDocument9 pagesUnit-5 Info Secuworkwithasr04No ratings yet
- Information Security Governance & Risk ManagementDocument37 pagesInformation Security Governance & Risk Managementsamirdas_hyd67% (9)
- CISSP Study GuideDocument73 pagesCISSP Study GuideSteve Norfolk92% (12)
- Cybersecurity CISO Vital Part OperationsDocument11 pagesCybersecurity CISO Vital Part Operationsseek4secNo ratings yet
- Program:B.Tech (BA+BD) Course Code:CSBD4070 Course Name:Big Data SecurityDocument29 pagesProgram:B.Tech (BA+BD) Course Code:CSBD4070 Course Name:Big Data SecurityVairavel ChenniyappanNo ratings yet
- Mani - AkellaDocument6 pagesMani - AkellaKrishnamohan VaddadiNo ratings yet
- 8 Access ControlDocument81 pages8 Access ControlRuppee Edward100% (1)
- CH 05Document66 pagesCH 05faisal_cseduNo ratings yet
- Information Security Risk Assessment ChecklistDocument7 pagesInformation Security Risk Assessment ChecklistAdil Raza SiddiquiNo ratings yet
- Module 11 Maintaining InfoSec 211Document57 pagesModule 11 Maintaining InfoSec 211Umair AmjadNo ratings yet
- Information Security Lesson 9Document31 pagesInformation Security Lesson 9Marvellous R MakuweNo ratings yet
- Lecture 1-Overview & Course ProjectsDocument74 pagesLecture 1-Overview & Course ProjectsHasham AkramNo ratings yet
- IssDocument2 pagesIssDinda Alifal BalqisNo ratings yet
- Module-4: Information Security Audit PreparationDocument35 pagesModule-4: Information Security Audit PreparationNirabhra RayNo ratings yet
- Bca Ds Sem-5 Information Security FundamentalsDocument4 pagesBca Ds Sem-5 Information Security FundamentalsVikas SharmaNo ratings yet
- Security Audit Course ProjectDocument6 pagesSecurity Audit Course ProjectmaryamNo ratings yet
- Chapter 5Document66 pagesChapter 5nandiny 97No ratings yet
- Operating Systems and Computer Security: Week - 1Document26 pagesOperating Systems and Computer Security: Week - 1Mangala SemageNo ratings yet
- Principles of Information Security 6th Edition Whitman Solutions Manual 1Document17 pagesPrinciples of Information Security 6th Edition Whitman Solutions Manual 1john98% (52)
- CSS L-5Document6 pagesCSS L-5Utkarsh Singh MagarauthiyaNo ratings yet
- Familiarity With Basic Principles of Information Security.: Pre-RequisiteDocument2 pagesFamiliarity With Basic Principles of Information Security.: Pre-RequisiteP S VimalNo ratings yet
- CISO Recruitment - CISO Recruiter - CISO Executive SearchDocument1 pageCISO Recruitment - CISO Recruiter - CISO Executive Searchshanthi rajeshNo ratings yet
- FinacleDocument28 pagesFinacleshanthi rajesh100% (1)
- TandemDocument2 pagesTandemshanthi rajeshNo ratings yet
- EMV2Document2 pagesEMV2shanthi rajeshNo ratings yet
- Chip TechnologyDocument1 pageChip Technologyshanthi rajeshNo ratings yet
- Offline Data Authentication The EMV ChipDocument1 pageOffline Data Authentication The EMV Chipshanthi rajeshNo ratings yet
- Coceptual Model - DevSecOpsDocument28 pagesCoceptual Model - DevSecOpsshanthi rajeshNo ratings yet
- BI TestingDocument4 pagesBI Testingshanthi rajeshNo ratings yet
- Security Expertise in Dev Sec OpsDocument5 pagesSecurity Expertise in Dev Sec Opsshanthi rajeshNo ratings yet
- API Autoamtion TestingDocument27 pagesAPI Autoamtion Testingshanthi rajeshNo ratings yet
- CAMSDocument2 pagesCAMSshanthi rajeshNo ratings yet
- UEBADocument2 pagesUEBAshanthi rajeshNo ratings yet
- AppiumDocument18 pagesAppiumshanthi rajeshNo ratings yet
- What Is A Security Operations Center (SOC) ?Document3 pagesWhat Is A Security Operations Center (SOC) ?shanthi rajeshNo ratings yet
- Threat DetectionDocument9 pagesThreat Detectionshanthi rajeshNo ratings yet
- SIEMDocument3 pagesSIEMshanthi rajeshNo ratings yet
- Mitre Att&ckDocument3 pagesMitre Att&ckshanthi rajeshNo ratings yet
- Network Traffic AnalysisDocument8 pagesNetwork Traffic Analysisshanthi rajeshNo ratings yet
- Incident ResponseDocument5 pagesIncident Responseshanthi rajeshNo ratings yet
- Cloud Security ToolsDocument12 pagesCloud Security Toolsshanthi rajeshNo ratings yet
- KirbyDocument42 pagesKirbyandrogutlay55555No ratings yet
- 122pm - Ijmr August 2023 Full JournalDocument488 pages122pm - Ijmr August 2023 Full Journalsinok5078No ratings yet
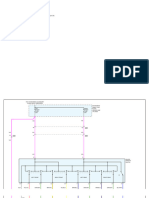
- DIAGRAMA-ventanas Electricas SparkevDocument3 pagesDIAGRAMA-ventanas Electricas SparkevHarvey LaresNo ratings yet
- Electrochimica Acta 50 (2005) 4174-4181Document8 pagesElectrochimica Acta 50 (2005) 4174-4181Dulce BaezaNo ratings yet
- ETM - Starter Picanto MT 2013Document1 pageETM - Starter Picanto MT 2013Hendra Gunawan100% (1)
- Audi Qrs A4-2009 PDFDocument98 pagesAudi Qrs A4-2009 PDFJOHNNY5377No ratings yet
- HSG Lop 11 2022-2023 KEYSDocument7 pagesHSG Lop 11 2022-2023 KEYSHà Trần Thị ThuNo ratings yet
- Chapter 7Document36 pagesChapter 718071052 Nguyễn Thị MaiNo ratings yet
- History of Microsoft OfficeDocument2 pagesHistory of Microsoft OfficeRichie BlasabasNo ratings yet
- CISM Study NotesDocument4 pagesCISM Study NotesLa Vita Di Lusso44% (9)
- Economía EnergéticaDocument8 pagesEconomía EnergéticaSERGIO MANZO ANDRADENo ratings yet
- Evidence Planning My TripDocument4 pagesEvidence Planning My TripDanielaRodríguez50% (2)
- E DLetterDocument4 pagesE DLetterDhruba Kumar SethiNo ratings yet
- Template 2 PIA Report Part 2 Appendix ADocument14 pagesTemplate 2 PIA Report Part 2 Appendix AJhong100% (1)
- Well Control Daily Checklist Procedure VDocument13 pagesWell Control Daily Checklist Procedure VmuratNo ratings yet
- Plant Manager in Modesto CA Resume Edward DarnellDocument2 pagesPlant Manager in Modesto CA Resume Edward DarnellEdwardDarnellNo ratings yet
- Prestressed Transfer Plate Design and ConstructionDocument16 pagesPrestressed Transfer Plate Design and Constructiona96lhf0% (1)
- DPI - Jul-Aug 16Document59 pagesDPI - Jul-Aug 16ratninp9368No ratings yet
- Eu-R SAA ULDocument74 pagesEu-R SAA ULCarlos Alberto de Andrade Freitas Junior100% (1)
- Abhishek Intern ReportDocument44 pagesAbhishek Intern ReportAbhishek sharma100% (1)
- Acr ArtrozaDocument14 pagesAcr Artrozacodruta soareNo ratings yet
- Iqta'Document3 pagesIqta'ZABED AKHTARNo ratings yet
- TICO Pro Spotter Repair Manual 1Document211 pagesTICO Pro Spotter Repair Manual 1Ivailo Zapryanov0% (1)
- Voxler 2 Demo Part 4Document2 pagesVoxler 2 Demo Part 4RizalabiyudoNo ratings yet
- Aldinga Bay's Coastal Views December 2014Document40 pagesAldinga Bay's Coastal Views December 2014Aldinga BayNo ratings yet
- Strategic Management PaperDocument97 pagesStrategic Management PaperElle Woods100% (3)
- Bach, Well Tempered ClavierDocument3 pagesBach, Well Tempered ClavierLucas BauerNo ratings yet
- Cx2000 Ac Drive CatalogueDocument24 pagesCx2000 Ac Drive CataloguepandurangaNo ratings yet
- Crop Protection 51-15 - Insect Pest Control - Plant HealthDocument36 pagesCrop Protection 51-15 - Insect Pest Control - Plant HealthDarwin M. CacalNo ratings yet
- Kyocera Fs-1020d Service ManualDocument109 pagesKyocera Fs-1020d Service ManualvonBoomslangNo ratings yet