Professional Documents
Culture Documents
Midterm Exam Questions - Compress
Midterm Exam Questions - Compress
Uploaded by
Jannaviel Mirandilla0 ratings0% found this document useful (0 votes)
12 views3 pagesOriginal Title
midterm-exam-questions_compress
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
12 views3 pagesMidterm Exam Questions - Compress
Midterm Exam Questions - Compress
Uploaded by
Jannaviel MirandillaCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 3
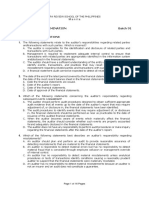
Multiple Choice Questions 5.
Which type of audit involves a review of
1. Information that needs to be stored for general and application controls, with a
10 years or more would most likely be focus on determining if there is
stored in which type of file? compliance with policies and adequate
a. Back up safeguarding of assets?
b. Archive a. Information systems audit
c. Encrypted b. Financial Audit
d. Log c. Operational Audit
2. Which of the following is an example of d. Compliance Audit
the kind of batch total called a hash 6. At what step in audit process do the
total? concepts of reasonable assurance and
a. The sum of the purchase materiality enter into the auditor’s
amount field in a set of decision process?
purchase orders a. Planning
b. The sum of the purchase order b. Evidence Collection
number field in a set of c. Evidence Evaluation
purchase orders d. They are important in all three
c. The number of completed steps
documents in a set of purchase 7. Which of the following procedures is
orders not used to detect unauthorized
d. All of the Above program changes
3. Which of the following is a a. Source code comparison
characteristic of auditing? b. Parallel Simulation
a. Auditing is a systematic, step- c. Reprocessing
by-step process d. Reprogramming code
b. Auditing involves the collection 8. The fundamental purpose of internal
and review of evidence control is to
c. Auditing involves the use of a. Safeguard the resources of the
established criteria to evaluate organization
evidence b. Provide reasonable assurance
d. All of the above are that the objective of the
characteristic of the auditing organization are achieved
4. Which of the following is not a reason c. Encourage compliance with
an internal auditor should participate in organization objectives
internal control reviews during the d. Ensure the accuracy, reliability,
design of new system? and timeliness of information
a. It is more economical to design e. All of the above
controls during the design than f. None of the Above
to do so later 9. The auditor would most likely be
b. It eliminates the need for concerned with internal control policies
testing controls during regular and procedures that provide reasonable
audits assurance about the
c. It minimizes the need for a. Efficiency of management’s
expensive modifications after decision making process
the system is implemented b. Appropriate prices the entity
d. It permits the design of audit should charge for its products
trails while they are economical c. Methods of assigning
production tasks to employees
d. Entity’s ability to process and b. The auditor’s specific audit
summarize financial data objectives
e. All of the Above c. The consideration of inherent
10. Components of internal control risk and control risk through
includes: which the auditor arrives at the
a. Control Environment risk assessment
b. Risk Assessment d. The auditor’s design and
c. Information and performance of tests of control
Communication Systems and substantive procedures
d. Control Activities appropriate to meet the audit
e. All of the Above objective
f. None of the Above 13. Which of the following statement is not
11. The characteristics the distinguish correct?
computer processing from manual a. The overall objective and scope
processing include the following: of an audit do not change in a
I. Computer processing uniformly CIS Environment
subjects like transactions to the b. When computer or CIS are
same instructions introduced, the basic concept
II. Computer System always ensure of evidence accumulation
that complete transaction trails remain the same
useful for audit purposes are c. Most CIS rely extensively on
preserved for indefinite periods (1 the same type of procedures for
characteristics of CIS is the lack of control that are used in manual
visible transaction trail) processing system
III. Compute processing virtually d. The specific methods
eliminates the occurrence of clerical appropriate for implementing
errors normally associated with the basic auditing concepts do
manual processing not change
IV. Control procedures as to 14. Which of the following is not a general
segregation of functions may no control?
longer be necessary in computer D. Processing Controls
environment (may be combined but 15. Which of the following activities would
is necessary) most likely be performed in the CIS
a. All of the above statements Department?
are true B. Conversion of information to machine-
b. Only Statements 2 and 4 readable form
are True 16. For control purposes, which of the
c. Only Statements 1 and 3 following should be organizationally
are True segregated from the computer
d. All of the above statement operations functions?
are False B. System Development
12. The use of CIS will least likely affect the 17. Unauthorized alteration of online
a. The procedures followed by the records can be prevented by employing
auditor in obtaining a sufficient D. Database Access Controls
understanding of the 18. Some CIS control procedures relate to
Accounting and Internal Control all CIS activities (general controls) and
Systems some relate to specific tasks
(application controls). General Controls 1. Data and computer program can’t be
include access and altered by unauthorized
C. Controls for documenting and approving persons without leaving visible evidence.
programs and changes to the programs TRUE
19. The management of ABC Co. suspects 2. Incorporating appropriate controls to the
that someone is tampering with pay system to limit the access of data files and
rates by entering changes through the programs only to authorized personnel is
Company’s remote terminals located in very important.
the factory. The method ABC Co. should TRUE
implement to protect the system from 3. In a CIS environment, functions that are
these unauthorized alterations to the normally segregated in manual processing
system’s file is are combined.
C. Passwords FALSE
20. Which of the following controls most 4. All transactions are initiated by the CIS
likely would assure that an entity can itself without the need for an input
reconstruct its financial records? document.
B. Back up disks or tapes of files is stored TRUE
away from originals 5. The information on the computed can be
21. A Co. updates its accounts receivable easily changed, leaving no trace of the
master file weekly and retains the master original content.
files and corresponding update transactions FALSE
for the most recent 2- week period. The
purpose of this practice is to 6. The elements of internal control are the
C. Permit reconstruction of the master file if same; the computer just changes the
needed methods by which these elements are
22. Which of the following is correct? implemented.
D. Check digits are designed to detect TRUE
transcription errors 7. General controls are those control
23. In updating a computerized accounts policies and procedures that relate to the
receivable file, which one of the following overall computer information system.
would be used a batch controls to verify the These controls include input controls,
accuracy of the posting of cash receipts processing controls and output controls.
remittances? FALSE
D. The sum of the cash deposits plus the 8. Application controls refer to the
discounts taken by customers transactions and data relating to each
24. Which statement is not correct? The computer- based application system,
goal of batch controls is to ensure that therefore, they are specific to each
during processing application.
C. Transactions are not added TRUE
25. The employee entered “40” in the hours 9. Input controls are used mainly to check
worked per day field. Which check would detect the integrity of data entered into a
this unintentional error? business application, whether the data is
C. Limit Check entered directly by staff, remotely by a
business partner or through a Web-
True or False enabled application or interface. Data
FALSE input is checked to ensure that is remain
within specified parameters.
TRUE
You might also like
- CS Construction-Company ProfileDocument10 pagesCS Construction-Company Profilebrian santos0% (1)
- Chapter 7: Auditing in A Computerized Environment (No 85)Document22 pagesChapter 7: Auditing in A Computerized Environment (No 85)JIL Masapang Victoria ChapterNo ratings yet
- Finals Financial ManagementDocument22 pagesFinals Financial Managementsammie helsonNo ratings yet
- Bad Debt Provision Under IFRS 9 PDFDocument90 pagesBad Debt Provision Under IFRS 9 PDFtunlinoo.067433No ratings yet
- Group 2 MiCparDocument21 pagesGroup 2 MiCparCarlito B. BancilNo ratings yet
- Acrev 422 AfarDocument19 pagesAcrev 422 AfarAira Mugal OwarNo ratings yet
- Consolidation Notes Complex Group StructuresDocument6 pagesConsolidation Notes Complex Group StructuresRobert MunyaradziNo ratings yet
- Chapter 10 Test BankDocument48 pagesChapter 10 Test BankDAN NGUYEN THE100% (1)
- ASR Quizzer 6 - Planning and Risk AssessmenttDocument18 pagesASR Quizzer 6 - Planning and Risk AssessmenttInsatiable LifeNo ratings yet
- AK Purchase and Disbursement CycleDocument7 pagesAK Purchase and Disbursement CyclecykenNo ratings yet
- Bl2: The Law On Private Corporation Final Examination General InstructionsDocument4 pagesBl2: The Law On Private Corporation Final Examination General InstructionsShaika HaceenaNo ratings yet
- Aud Theo Quizzer 1Document16 pagesAud Theo Quizzer 1KIM RAGANo ratings yet
- Partnership Diagnostic ExercisesDocument24 pagesPartnership Diagnostic ExercisesBrithney TurlaNo ratings yet
- TBCH02Document8 pagesTBCH02Arnyl ReyesNo ratings yet
- MCQ (New Topics-Special Laws) - PartDocument2 pagesMCQ (New Topics-Special Laws) - PartJEP WalwalNo ratings yet
- Unit-2 Audit of Cash and Marketable SecuritiesDocument6 pagesUnit-2 Audit of Cash and Marketable SecuritiesKiya AbdiNo ratings yet
- Reflective EssayDocument13 pagesReflective Essaylufemos OlufemiNo ratings yet
- AC316 Chapter 6 & 7 Test BankDocument30 pagesAC316 Chapter 6 & 7 Test BankNanon Wiwatwongthorn100% (1)
- Multiple Choice Question: General ControlsDocument20 pagesMultiple Choice Question: General ControlsEj TorresNo ratings yet
- This Study Resource Was Shared Via: National Mock Board Examination 2017 Regulatory Framework For Business TransactionsDocument8 pagesThis Study Resource Was Shared Via: National Mock Board Examination 2017 Regulatory Framework For Business TransactionsSEAN LEJEE BAJANNo ratings yet
- Reviewer in AuditngDocument32 pagesReviewer in AuditngHazel MoradaNo ratings yet
- Aaca Receivables and Sales ReviewerDocument13 pagesAaca Receivables and Sales ReviewerLiberty NovaNo ratings yet
- Practice Questions For Audit TheoryDocument4 pagesPractice Questions For Audit TheoryHanna Lyn BaliscoNo ratings yet
- Chapter 7Document27 pagesChapter 7phillipNo ratings yet
- AUD Final Preboard QuestionsDocument12 pagesAUD Final Preboard QuestionsVillanueva, Mariella De VeraNo ratings yet
- Chapter 8 Consideration of Internal Control in An InformatiDocument32 pagesChapter 8 Consideration of Internal Control in An Informatichristiansmilaw100% (1)
- Auditing Multiple ChoicesDocument8 pagesAuditing Multiple ChoicesyzaNo ratings yet
- At Quizzer 6 - Planning and Risk Assessment - FEU MktiDocument18 pagesAt Quizzer 6 - Planning and Risk Assessment - FEU Mktiiyah0% (1)
- Accounting For Special TransactionDocument31 pagesAccounting For Special Transactionchadskie20No ratings yet
- Part 4D (Information Systems) 264Document71 pagesPart 4D (Information Systems) 264Colleidus Khoppe100% (2)
- Audit CH 6 and 7Document30 pagesAudit CH 6 and 7Nanon WiwatwongthornNo ratings yet
- Pre EngagementDocument3 pagesPre EngagementJanica BerbaNo ratings yet
- MI0039-MQP With Answer KeysDocument17 pagesMI0039-MQP With Answer KeysckivmlNo ratings yet
- Gramling 9e Auditing Solman Audit SamplingDocument29 pagesGramling 9e Auditing Solman Audit Samplingkimjoonmyeon22100% (1)
- Module 2 Answer Key On Property Plant and EquipmentDocument7 pagesModule 2 Answer Key On Property Plant and EquipmentLoven BoadoNo ratings yet
- Angelo - Chapter 10 Operating LeaseDocument8 pagesAngelo - Chapter 10 Operating LeaseAngelo Andro Suan100% (1)
- BLT 2012 First Pre-Board July 28Document14 pagesBLT 2012 First Pre-Board July 28Lester AguinaldoNo ratings yet
- Requirement No. 1: PROBLEM NO. 1 - Heats CorporationDocument1 pageRequirement No. 1: PROBLEM NO. 1 - Heats CorporationjhobsNo ratings yet
- CL Cup 2018 (AUD, TAX, RFBT)Document4 pagesCL Cup 2018 (AUD, TAX, RFBT)sophiaNo ratings yet
- Practice Test 1 KeyDocument11 pagesPractice Test 1 KeyAshley Storey100% (1)
- 5.a in The Case That The AI Were To Have Made The Entries Themselves, It Would Ruin Their Function andDocument2 pages5.a in The Case That The AI Were To Have Made The Entries Themselves, It Would Ruin Their Function andAngeloNo ratings yet
- Test Bank Inter Acc 1 CH 2 Part 1Document8 pagesTest Bank Inter Acc 1 CH 2 Part 1Study OuoNo ratings yet
- Acctg 17nd-Final Exam ADocument14 pagesAcctg 17nd-Final Exam AKristinelle AragoNo ratings yet
- Auditing Chapter 3Document3 pagesAuditing Chapter 3Patricia100% (1)
- Cma/Cfm: Preparatory ProgramDocument42 pagesCma/Cfm: Preparatory Programpaperdollsx0% (2)
- R R N N C: Permutations & CombinationsDocument9 pagesR R N N C: Permutations & CombinationsTEE PEI LENG MoeNo ratings yet
- AUD Final Preboard Examination QuestionnaireDocument16 pagesAUD Final Preboard Examination QuestionnaireJoris YapNo ratings yet
- Chapter FourDocument18 pagesChapter Fourmubarek oumerNo ratings yet
- Completion of Audit Quiz ANSWERDocument9 pagesCompletion of Audit Quiz ANSWERJenn DajaoNo ratings yet
- Salosagcol Auditing Theory Solution ManualDocument4 pagesSalosagcol Auditing Theory Solution ManualM.m. AntineroNo ratings yet
- Second Semester 2020 Second Year University of Assuit Faculty of Commerce English Program " Corporation" "Test Bank"Document10 pagesSecond Semester 2020 Second Year University of Assuit Faculty of Commerce English Program " Corporation" "Test Bank"Magdy KamelNo ratings yet
- Auditing Theory TEST BANKDocument23 pagesAuditing Theory TEST BANKGelyn CruzNo ratings yet
- Confidential: Section A - 20 Marks Scenario A. (3 Questions)Document4 pagesConfidential: Section A - 20 Marks Scenario A. (3 Questions)Otherr HafizNo ratings yet
- Auditing Theory MULTIPLE CHOICE. Read Carefully The Questions Below and Choose The Best Statement Among The ChoicesDocument12 pagesAuditing Theory MULTIPLE CHOICE. Read Carefully The Questions Below and Choose The Best Statement Among The ChoiceschimchimcoliNo ratings yet
- Theory of Accounts - ReviewerDocument24 pagesTheory of Accounts - ReviewerKristel OcampoNo ratings yet
- NCR Cup 2 Judges' Copy - Elimination RoundDocument17 pagesNCR Cup 2 Judges' Copy - Elimination RoundMich ClementeNo ratings yet
- Colegio de Dagupan Arellano Street, Dagupan City School of Business and Accountancy Final Examination Auditing and Assurance PrincipleDocument16 pagesColegio de Dagupan Arellano Street, Dagupan City School of Business and Accountancy Final Examination Auditing and Assurance PrincipleFeelingerang MAYoraNo ratings yet
- Prepare The Current Liabilities Section of The Statement of Financial Position For The Layla Company As of December 31, 2020Document1 pagePrepare The Current Liabilities Section of The Statement of Financial Position For The Layla Company As of December 31, 2020versNo ratings yet
- Auditing and Assurance Principles Final Exam Set ADocument11 pagesAuditing and Assurance Principles Final Exam Set APotato CommissionerNo ratings yet
- Auditing in Cis Prelim Exam Raquel Alvarez-De Castro, Cpa, Mba/Mpa I.QuestionsDocument3 pagesAuditing in Cis Prelim Exam Raquel Alvarez-De Castro, Cpa, Mba/Mpa I.QuestionsWenjunNo ratings yet
- Auditing Theory Test BankDocument10 pagesAuditing Theory Test BankLuisitoNo ratings yet
- Auditing Chapter 2 ReviewDocument21 pagesAuditing Chapter 2 ReviewYomna AttiaNo ratings yet
- CisDocument3 pagesCissara joyce pinedaNo ratings yet
- Auditing Theory The Impact of Information Technology On The Audit ProcessDocument14 pagesAuditing Theory The Impact of Information Technology On The Audit ProcessMark Anthony TibuleNo ratings yet
- Power: Contrasting Leadership and PowerDocument17 pagesPower: Contrasting Leadership and PowerPrasanna PrasannaNo ratings yet
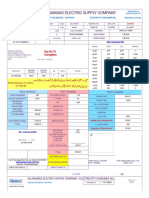
- Iesco Online BillDocument1 pageIesco Online BillRocky BhaiNo ratings yet
- 01 Assignment CVP Basics AnswerDocument8 pages01 Assignment CVP Basics AnswerKSNo ratings yet
- Hyperion 2 PDFDocument1 pageHyperion 2 PDFAbhishek Gite100% (1)
- Market Plan and Control: Submitted To: Prof. Ajay BansalDocument28 pagesMarket Plan and Control: Submitted To: Prof. Ajay BansalAkhil ThakurNo ratings yet
- Vendor: Cisco Exam Code: 300-375 Exam Name: Securing Wireless Enterprise NetworksDocument91 pagesVendor: Cisco Exam Code: 300-375 Exam Name: Securing Wireless Enterprise NetworksFrancisco CmxNo ratings yet
- Gatsby Engineering Level Guide - Engineering LevelsDocument1 pageGatsby Engineering Level Guide - Engineering LevelsHardikNo ratings yet
- Economic Order Quantity (EOQ) : Prepared By: Talha Majeed Khan (M.Phil) Lecturer, UCP, Faculty of Management StudiesDocument7 pagesEconomic Order Quantity (EOQ) : Prepared By: Talha Majeed Khan (M.Phil) Lecturer, UCP, Faculty of Management StudieszubairNo ratings yet
- ATHAL Public Relations & Marketing - PackagesDocument7 pagesATHAL Public Relations & Marketing - PackagesATHAL Public Relations & Marketing100% (1)
- Capa Site CAP 437 - Standards For Offshore Helicopter Landing AreasDocument1 pageCapa Site CAP 437 - Standards For Offshore Helicopter Landing AreasPierre CarvalhoNo ratings yet
- Employee Voice ThesisDocument6 pagesEmployee Voice Thesissusancoxarlington100% (2)
- Problem 5 Rental IncomeDocument2 pagesProblem 5 Rental IncomeStephen Jay RioNo ratings yet
- Potato Chip Case - Class Activity 2Document2 pagesPotato Chip Case - Class Activity 2Nadeem BashirNo ratings yet
- Impact A Guide To Business Communication Canadian 9th Edition Northey Solutions ManualDocument11 pagesImpact A Guide To Business Communication Canadian 9th Edition Northey Solutions ManualMarkJoneskjsme100% (13)
- Taipei GEAF MinisetDocument22 pagesTaipei GEAF MinisetPhilip ZhengNo ratings yet
- About Financial Statements: Prepared By: Mohammad Shahidul Islam MBA, ACADocument31 pagesAbout Financial Statements: Prepared By: Mohammad Shahidul Islam MBA, ACAShahid MahmudNo ratings yet
- TGKADocument129 pagesTGKADina sofianaNo ratings yet
- Reserve Bank of IndiaDocument46 pagesReserve Bank of Indiarafishaik786No ratings yet
- SBL BPP Kit-2019 Copy 454Document1 pageSBL BPP Kit-2019 Copy 454Reever RiverNo ratings yet
- Kerala Shops and Commercial Establishments Acts and RulesDocument34 pagesKerala Shops and Commercial Establishments Acts and RulesHR RecruiterNo ratings yet
- The Voucher System of ControlDocument32 pagesThe Voucher System of ControlNicole LaiNo ratings yet
- Sanjay Yadav - 1offer LetterDocument2 pagesSanjay Yadav - 1offer LetterSanjay yadavNo ratings yet
- The Stoic Investor: Possessed by Your PossessionsDocument6 pagesThe Stoic Investor: Possessed by Your PossessionspadmaniaNo ratings yet
- Why Does Trinidad and Tobago Need A Different Fiscal Regime For GasDocument7 pagesWhy Does Trinidad and Tobago Need A Different Fiscal Regime For GasAries SatriaNo ratings yet
- TD - Outsourcing PDFDocument17 pagesTD - Outsourcing PDFrajaNo ratings yet
- Junior Accountant Syllabus RajasthanDocument6 pagesJunior Accountant Syllabus RajasthanPriyanka JainNo ratings yet