Professional Documents
Culture Documents
Azure AD Best Practices Version 4.0
Uploaded by
al mailOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Azure AD Best Practices Version 4.0
Uploaded by
al mailCopyright:
Available Formats
PROOFPOINT
INTEGRATION –
MICROSOFT AZURE
USER IMPORTS AND AUTHENTICATION (SAML
2.0) FOR PROOFPOINT PROTECTION SERVER
© 2022 Proofpoint. All rights reserved. 1 of 29
Table of Contents
Overview ......................................................................................................................... 3
Integration Worksheet Template ..................................................................................... 4
Integration Worksheet Blank Template .................................................................... 4
Integration Worksheet Template Example ............................................................... 5
Microsoft Azure User Import ............................................................................................ 6
Microsoft Azure App Registration ........................................................................................... 6
Proofpoint – Azure Import/Auth Profile ..................................................................................13
Proofpoint – Importing Users from Azure ..............................................................................16
Microsoft Azure Single Sign-On .................................................................................... 18
Proofpoint – Gather settings ..................................................................................................18
Microsoft Azure – Configure Proofpoint on Demand Enterprise App .....................................21
Proofpoint – Complete Import/Auth profile .............................................................................25
Proofpoint - Enabling SSO for Administrator logon and/or End User Web logon ...................27
Enable SSO for Administrator logon: ..................................................................... 27
Testing SSO for Administrator Logon:.................................................................... 27
Enable SSO for End User Web logon: ................................................................... 28
Testing SSO for End User Web logon:................................................................... 29
© 2022 Proofpoint. All rights reserved. 2 of 29
Overview
You can integrate Microsoft Azure Active Directory with the Proofpoint On Demand
Email and Information Protection service for user synchronization and authentication via
Applications within Azure Active Directory. This document will go over the steps to
configure Azure Active Directory Apps and Proofpoint’s PPS import/auth profiles to
provide that functionality.
If you need assistance, contact Proofpoint Support and / or your Proofpoint Professional
Services consultant assisting you with implementation.
Update Window
We recommend only making changes during a well-planned change control window.
Disable Recipient Verification
If you are replacing an existing populated user repository, we recommend you
disable Recipient Verification until the Azure import is populating correctly.
Names May Change
This guide provides guidance. You may see different names or interfaces.
• Some of the Azure Active Directory (AD) features shown or listed are based on an
AD plan level.
Please refer to your Microsoft Azure AD documentation for more information
concerning your plan level.
• Microsoft Azure Active Directory’s administration interface can change; refer to
Microsoft
documentation for configuration details.
Nested groups are not compatible with PPS.
Users/Mailing Lists need to be a direct member of a group for PPS to be able to add
them to that group.
Groups within groups (nested groups) are not visible to PPS.
As-is Instructions
Because we do not directly support Microsoft Azure AD, these instructions are given
as-is.
© 2022 Proofpoint. All rights reserved. 3 of 29
Integration Worksheet Template
To simplify documenting and copying values between PPS/POD and Azure, we'll be
copying them first to the below template, and then to the appropriate location. Please
copy the blank template below to a text document. We will reference the values you
need to copy over to newly created text document in the steps below. After
configuration and successful testing please save that document in a secure place in
case you should need to recreate or reconfigure your Proofpoint Email Protection
Server and/or Microsoft Azure Services.
An example template (with sample values filled in) is available on the following page.
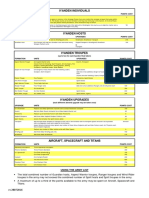
Integration Worksheet Blank Template
Copy the below template to a text document to record your Proofpoint and Azure values.
Azure App Registration Info for User Imports:
Values from Azure:
Tenant ID (Directory ID):
Client ID (Application ID):
Client Key (Client Key Value):
Azure Proofpoint on Demand Gallery App info for SAML Authentication:
Values from Proofpoint:
Sign-on URL:
Entity ID:
Consumer URL:
Values from Azure (Note differences between names between Proofpoint and Azure):
Login URL (Identity Provider URL):
Azure AD Identifier (Identity Provider Entity ID):
Certificate (Base64):
© 2022 Proofpoint. All rights reserved. 4 of 29
Integration Worksheet Template Example
This is an example for demonstration purposes only.
Azure App Registration Info for User Imports:
Values from Azure:
Tenant ID (Directory ID): 4c5938e3-3ea0-4964-820a-d44142e4c203
Client ID (Application ID): f4058901-6d93-4686-ad18-5788b9a23f9d
Client Key (Client Key Value): TW9c92ji6HS63x1hRmwcHiIKirLrzi+7hgbfFjzyWaU=
Azure Proofpoint on Demand Gallery App info for SAML Authentication:
Values from Proofpoint:
Sign-on URL: https://example.pphosted.com:10020/
Entity ID: https://saml-entity-id.proofpoint.com/example_hosted
Consumer URL: https://example.pphosted.com:10020/v1/samlauth/samlconsumer
Values from Azure (Note differences between names between Proofpoint and Azure):
Login URL (Identity Provider URL):
https://login.microsoftonline.com/4c5938e3- 3ea0-4934-820a-c17142e4c203/saml2
Azure AD Identifier (Identity Provider Entity ID):
https://sts.windows.net/4c5938e3-3ea0-4934-820a-c17142e4c203/
Certificate (Base64):
-----BEGIN CERTIFICATE-----
MIIC8DCCAdigAwIBAgIQZWlRziftGqJHrJoLMR+YxzANBgkqhkiG9w0BAQsFADA0MTIwMAYDVQQD
EylNaWNyb3NvZnQgQXp1cmUgRmVkZXJhdGVkIFNTTyBDZXJ0aWZpY2F0ZTAeFw0xOTAxMDMwMzEw
MzFaFw0yMjAxMDMwMzEwMzFaMDQxMjAwBgNVBAMTKU1pY3Jvc29mdCBBenVyZSBGZWRlcmF0ZWQg
U1NPIENlcnRpZmljYXRlMIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAqLW2HuZdhrmo
tcIVfcJT639eOgNDMoI8QwRKpq84QGHtqMXgcH3eABENf2WGZ1hHrjos74e8cSbzOzXFEEGq1YQT
fco3O5TBbFJlZhjQ3Hvrxmj3lO6xRrRV/N/Uxy+MJZIZKH6+B1ULEnxcsqPdPY9VHYbDvjNiodP0
astM/JoF1ZTvn7l+28lf2bLqW7kZ2BlYvJ6iiSZQEfKxBU3ZioVd+E16UbrJf5ssnO4YXktWk7Rp
HcokIcvSV3MYCyAdHomgb7umflOQSGCkOiMYMcn6RHn7zHoWT3YDCPn2jBK3kcew7tK18gi2joGZ
j86rTUTgL4Vvhx/nmU6yCyvYRwIDAQABMA0GCSqGSIb3DQEBCwUAA4IBAQCit9luZ71/0uFqZ8F/
/rzWM7u4y0IHpW39OSJ4ab2leACCFietSY8p7LxPiW4bKcjAOP1T8urfVBDg+ntlNTlBJyBMmx3p
xbmRfq1gmjdwN1o2oIoVo14rmklVcw+vEinbs0x0RxsqQCGLtZVYmt2xKpsEagvgo9eSkfvtx+GI
tbYYD4wn0dg1/swKHKA7lt3SED6PL8zM+OKqP1PKtPhYeUoCGwAZ9XD+l4FLieL2UC9IigF3jWtw
u+xtMnkMDW7gS00aDHjRDDugPOk0HOPzhlUIrMgt8AsvUWK/TeIYQtf7NvRoCLdhF5qFrJppKdVH
c3okfJTgn8kp1i4t9f07
-----END CERTIFICATE-----
© 2022 Proofpoint. All rights reserved. 5 of 29
Microsoft Azure User Import
Microsoft Azure App Registration
First, we’ll register the application on Azure to allow the Proofpoint Protection server
access to sync email objects and groups.
1. Log into the Azure Portal (https://portal.azure.com) then click Azure Active
Directory
2. Click App registrations from the menu on the left (you may need to expand the
menu to find the option)
3. Click New registration
© 2022 Proofpoint. All rights reserved. 6 of 29
4. Fill out Name as shown in the screenshot below and click Register.
5. Make note of your Application ID (Client ID) and the Directory ID (Tenant ID) in the
integration worksheet document mentioned previously.
© 2022 Proofpoint. All rights reserved. 7 of 29
6. Click API Permissions, then click Add a Permission.
7. Click APIs my organization uses and search for Windows Azure Active
Directory, then select Windows Azure Active Directory.
8. Select Application permissions.
© 2022 Proofpoint. All rights reserved. 8 of 29
9. Scroll down until you see Directory. Expand Directory and
select Directory.Read.All then click Add permissions.
NOTE: While the current version of the Azure user import uses the Azure Active
Directory Graph API, future versions will be moving to the Microsoft Graph API. The
next steps will provide permissions for use by future versions of user sync. We’ll add
them now, so they don’t need to be modified later to allow future versions to work
properly.
10. To add the Microsoft Graph API, again click Add a permission.
© 2022 Proofpoint. All rights reserved. 9 of 29
11. Click Microsoft Graph.
12. Click Application permissions.
13. Scroll down until you see Directory. Expand Directory and
select Directory.Read.All then click Add permissions.
14. Apply the permissions by clicking Grant admin consent. You may need to confirm
the changes.
© 2022 Proofpoint. All rights reserved. 10 of 29
15. Verify that permissions are properly granted, each should have a green check next
to it.
16. Click Certificates & secrets, make sure Client Secrets is selected, then click New
client secret.
17. Enter a description to identify the key and select an expiration time based on your
organizations policies, then click the Add button.
© 2022 Proofpoint. All rights reserved. 11 of 29
NOTE: The key will need to be updated before the expiration configured in the
previous step. At this time, Azure doesn’t send warnings prior to expiration, so it is
suggested that you set a reminder 30days or so before it expires to generate a new
key in Azure and copy the value to the Proofpoint Protection Server Import/Auth
profile.
18. Once your key is displayed, Copy the Key Value and document it to the Client Key
(Client Key Value) line in the integration worksheet document mentioned in the
previous section of this guide.
© 2022 Proofpoint. All rights reserved. 12 of 29
Proofpoint – Azure Import/Auth Profile
Next, we’ll create the import profile on the Proofpoint Protection Server. You will need
the Tenant ID, Client ID, and Client Key as documented to the integration worksheet
document in the previous section.
1. Log into the Proofpoint Admin Console and navigate to System (tab) -> User
Management (module) -> Import/Auth Profiles
2. Click the Add button at the top
3. On the Add Profile page, select Azure Active Directory as the Data Source
© 2022 Proofpoint. All rights reserved. 13 of 29
4. Enter a Profile Name, and Description, then enter the Tenant ID, Client ID,
and Client Key from the Integration Worksheet values obtained in the previous
section.
5. Verify Tenant ID, Client ID and Client Key are correct and click Test button. If
successful you will see: Successfully accessing <Your Tenant ID> at the top
of the page.
6. Then click the Advanced tab and set Allow Mailing Lists without Owner to
On. In the Command Options field, enter “-removeoldgroup” and “-report -to
<email@address>” to have import results delivered to the specified address.
7. Set Restrict Number of Profiles To Be Deleted To Less Than to well above
the number of deletions expected between imports. If unsure, 50% of the total
mail objects is a reasonable setting and can be adjusted later if necessary.
© 2022 Proofpoint. All rights reserved. 14 of 29
8. Click Save Changes to complete the configuration of the import profile
© 2022 Proofpoint. All rights reserved. 15 of 29
Proofpoint – Importing Users from Azure
The configuration to import mail objects from Azure should now be complete. Next,
we’ll initiate the import process, and optionally schedule the import to occur
automatically.
1. Log into the Proofpoint Admin Console and navigate to System (tab) -> User
Management (module) -> Import/Auth Profiles
2. Select the checkbox next to the newly created Azure Import/Auth profile, and
then click the Import button.
3. Click the Import Now button at the bottom of the pop-up window.
Depending on the browser you may not get visual feedback of the button being
pressed. The import window can be safely closed after ~30 seconds. The import
will continue in the background. Depending on the number of objects and groups
to be imported the process could take up to several hours to complete.
© 2022 Proofpoint. All rights reserved. 16 of 29
4. Once the import is complete it will send a notification email to the “-report -to”
address configured in the previous section. You can verify the status of the
import by reviewing the “Result:” line in the email, it should say “SUCCESS”.
If not Successful, verify Tenant ID, Client ID and Client Key, and refer to the
steps in the Proofpoint - Azure Import/Auth Profile section above
5. Once the import has been verified as successful, it can be scheduled. Click the
Schedule button for the AzureAD import profile to be scheduled
6. In the Type field, select Time. In the Time field, select the time you’d like to
schedule the import to run. In the Days field, select what days you’d like to run
the import (commonly Every Day or Weekdays Only)
7. Select >> to add the time to be scheduled and click Save Changes
8. Additional times can be scheduled by clicking on the scheduled time for the
profile. Please use caution to ensure that additional imports are not scheduled to
start before a previous import completes. The duration can be found in the
status email sent after each import to the “-report -to” address specified
© 2022 Proofpoint. All rights reserved. 17 of 29
Microsoft Azure Single Sign-On
NOTE: Only one SAML SSO profile can be configured on Proofpoint Protection
Server.
Proofpoint – Gather settings
First, we’ll gather the necessary values from the Import/Auth profile on your Proofpoint
Protection Server.
1. Log into the Proofpoint Admin Console and navigate to System (tab) -> End User
Services (module) -> Web Application
2. Make note of the End User Web Application - Access URL as the Sign-on URL:
in the integration worksheet document mentioned previously.
© 2022 Proofpoint. All rights reserved. 18 of 29
3. Navigate to System (tab) -> User Management (module) -> Import/Auth Profiles
4. Click the Add button at the top
5. In the Add Profile pop-up window, select SAML 2.0 for the Data Source
© 2022 Proofpoint. All rights reserved. 19 of 29
6. Enter a Name and Description to identify the Import/Auth profile. Make note of
your Entity ID: and Consumer URL: in the integration worksheet document
mentioned previously.
© 2022 Proofpoint. All rights reserved. 20 of 29
Microsoft Azure – Configure Proofpoint on Demand Enterprise
App
Next, we’ll use the previously collected values to configure an Enterprise App on Azure
and collect the necessary values to finish configuration of the Import/Auth profile on the
Proofpoint Protection Server. We’ll come back to the Add Profile pop-up window in the
next section.
1. Log into the Azure Portal (https://portal.azure.com) then click Azure Active
Directory
2. Click App registrations from the menu on the left (you may need to expand the
menu to find the option)
3. Click New Application
© 2022 Proofpoint. All rights reserved. 21 of 29
4. Search for Proofpoint on Demand, and select the Proofpoint on Demand app
5. Give the app a meaningful name, and click Create
6. Select Properties from the menu on the left, set Assignment required to No, then
click Save
© 2022 Proofpoint. All rights reserved. 22 of 29
7. Click Single sign-on from the menu on the left, and then select SAML
8. In the Basic SAML Configuration (section 1), click Edit
9. From the integration worksheet document mentioned previously:
In the Identifier (Entity ID) field, enter the Entity ID
In the Reply URL (Assertion Consumer Service URL) field, enter the Consumer
URL
In the Sign on URL field, enter the Sign-on URL
Then click Save
© 2022 Proofpoint. All rights reserved. 23 of 29
10. In SAML Signing Certificate (Section 3), Download the Certificate (Base64) to save
the certificate to your workstation
11. In the Set up <your app name> (Section 4), make note of the Login URL and Azure
AD Identifier in the integration worksheet document mentioned previously
© 2022 Proofpoint. All rights reserved. 24 of 29
Proofpoint – Complete Import/Auth profile
We should now have everything we need to complete the configuration on the
Proofpoint Protection Server Import/Auth profile.
If the Add Profile pop-up window is still open on your Proofpoint Protection Server,
continue with the steps below. If it’s been closed, please follow the steps in the
“Proofpoint – Gather Settings” section above and then continue with the steps below.
1. In the Add Profile pop-up window on your Proofpoint Protection Server, enter the
following values from the Integration Worksheet obtained in the previous section:
Add the Azure AD Identifier to the Identify Provider Entity ID field
Add the Login URL to the Identity Provider URL field
2. To import the certificate downloaded in the previous section, click the Browse
button, select the certificate, then click Upload. The certificate should now be
displayed in the Primary IdP Signing Certificate field.
© 2022 Proofpoint. All rights reserved. 25 of 29
3. Click Save Changes
© 2022 Proofpoint. All rights reserved. 26 of 29
Proofpoint - Enabling SSO for Administrator logon and/or End
User Web logon
Configuration of the SAML 2.0 profile is now complete. Next, we’ll set the Admin
Console, End User Web portal, or both, to use the newly created profile.
It is suggested that you be logged in with the podadmin account on POD or the admin
account on PPS for the below steps, so your session won’t be interrupted.
Enable SSO for Administrator logon:
Before completing this step, you must have an administrator account configured on the
Proofpoint cluster with an email address that matches the primary email address of the
user logging into Azure.
Once SAML is enabled for Administrator accounts, the Proofpoint Admin Console will
use port 10001 for SAML authentication. Port 10000 will still be used to log in with
podadmin.
1. Log into the Proofpoint Admin Console and navigate to System (tab) ->
Administrator (module) -> Password Policy
2. Select the newly created Import/Auth profile in the Authentication Profile –
Authentication field and click Save Changes
Testing SSO for Administrator Logon:
1. Open a new Private or Incognito browser tab (see help for your browser of choice
for assistance) or open a browser different from the one already logged into the
Proofpoint Admin Console.
© 2022 Proofpoint. All rights reserved. 27 of 29
2. Connect to your Proofpoint Admin Console, you should be presented with a login
prompt as the Private, Incognito, or different browser should not retain the
authentication from your existing logon to Azure nor Proofpoint.
If the Azure SSO session is properly configured, there should be a SAML Login
URL link below the Login and Password prompts. Click the link
3. Your browser will be directed to Azure to authenticate. Once logged in via Azure,
your browser should be directed back to your Proofpoint Protection Server, and
you will be taken to the Proofpoint Admin Console.
4. If you aren’t properly logged in, review the Microsoft Azure Single Sign-On
section, and/or contact your Support or Professional Services Consultant for
additional assistance.
Enable SSO for End User Web logon:
Before completing this step, you must have a user account configured on the Proofpoint
cluster with an email address that matches the primary email address of the user
logging into Azure.
1. Log into the Proofpoint Admin Console and navigate to System (tab) -> User
Management (module) -> Authentication
© 2022 Proofpoint. All rights reserved. 28 of 29
2. Select the newly created Import/Auth profile in the Authentication –
Authentication Source field and click Save Changes
Testing SSO for End User Web logon:
1. Open a new Private or Incognito browser tab (see help for your browser of choice
for assistance) or open a browser that is not currently logged into Azure nor
Proofpoint.
2. Connect to your Proofpoint End User Web portal via the Sign-on URL on the
Integration Worksheet
3. Your browser will be directed to Azure to authenticate. Once logged in via Azure,
your browser should be directed back to your Proofpoint Protection Server, and
you will be taken to the Proofpoint End User Web Portal
4. If you aren’t properly logged in, review the Microsoft Azure Single Sign-On
section, and/or contact your Support or Professional Services Consultant for
additional assistance.
© 2022 Proofpoint. All rights reserved. 29 of 29
You might also like
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (121)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (400)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (345)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Blood Angels Quick RefDocument3 pagesBlood Angels Quick Refal mailNo ratings yet
- V Anaheim Air Cav Quick RefDocument3 pagesV Anaheim Air Cav Quick Refal mailNo ratings yet
- Saim-Hann Individuals: Formation Units Points CostDocument4 pagesSaim-Hann Individuals: Formation Units Points Costal mailNo ratings yet
- War Horde Quick RefDocument3 pagesWar Horde Quick Refal mailNo ratings yet
- Tau Quick RefDocument3 pagesTau Quick Refal mailNo ratings yet
- Feral Orks Quick RefDocument3 pagesFeral Orks Quick Refal mailNo ratings yet
- Ulthwe Quick RefDocument4 pagesUlthwe Quick Refal mailNo ratings yet
- Death Korps Quick RefDocument3 pagesDeath Korps Quick Refal mailNo ratings yet
- White Scars Quick RefDocument3 pagesWhite Scars Quick Refal mailNo ratings yet
- Iyanden Quick RefDocument4 pagesIyanden Quick Refal mailNo ratings yet
- Biel Tan Quick RefDocument4 pagesBiel Tan Quick Refal mailNo ratings yet
- Baran Siegemasters Quick RefDocument3 pagesBaran Siegemasters Quick Refal mailNo ratings yet
- Ulani Tank Reg Quick RefDocument3 pagesUlani Tank Reg Quick Refal mailNo ratings yet
- Steel Legion Quick RefDocument3 pagesSteel Legion Quick Refal mailNo ratings yet
- Space Wolves Quick RefDocument3 pagesSpace Wolves Quick Refal mailNo ratings yet
- Dark Angels Quick RefDocument3 pagesDark Angels Quick Refal mailNo ratings yet
- Codex Astartes Quick RefDocument3 pagesCodex Astartes Quick Refal mailNo ratings yet
- Squat EpicDocument4 pagesSquat Epical mailNo ratings yet
- Epic OrkgargantDocument2 pagesEpic Orkgargantal mailNo ratings yet
- Spacemarinespec EpicDocument2 pagesSpacemarinespec Epical mailNo ratings yet
- Chaos EpicDocument4 pagesChaos Epical mailNo ratings yet
- Epic 40k 3rd Edition Imperial Army ListDocument13 pagesEpic 40k 3rd Edition Imperial Army Listal mailNo ratings yet
- Epic OrkDocument5 pagesEpic Orkal mailNo ratings yet
- Spacemarine EpicDocument2 pagesSpacemarine Epical mailNo ratings yet
- Imperial Guard EpicDocument6 pagesImperial Guard Epical mailNo ratings yet
- 06 - Tyranids v4.1Document23 pages06 - Tyranids v4.1al mailNo ratings yet
- Eldar EpicDocument4 pagesEldar Epical mailNo ratings yet