0% found this document useful (0 votes)
867 views37 pagesCyb 309 - Systems Security - Lecture I
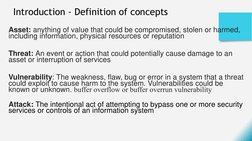
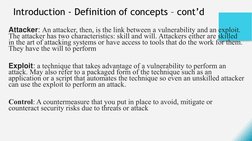
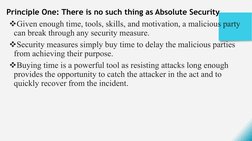
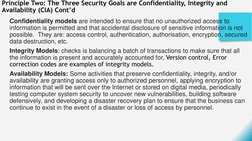
The document discusses security principles for cybersecurity. It defines key concepts like assets, threats, vulnerabilities and attacks. It also explains the three main security goals of confidentiality, integrity and availability. The document outlines principles like defense in depth strategy and that people are often the weakest link in security.
Uploaded by
akCopyright
© © All Rights Reserved
We take content rights seriously. If you suspect this is your content, claim it here.
Available Formats
Download as PDF, TXT or read online on Scribd
0% found this document useful (0 votes)
867 views37 pagesCyb 309 - Systems Security - Lecture I
The document discusses security principles for cybersecurity. It defines key concepts like assets, threats, vulnerabilities and attacks. It also explains the three main security goals of confidentiality, integrity and availability. The document outlines principles like defense in depth strategy and that people are often the weakest link in security.
Uploaded by
akCopyright
© © All Rights Reserved
We take content rights seriously. If you suspect this is your content, claim it here.
Available Formats
Download as PDF, TXT or read online on Scribd
- Introduction to System Security
- Information Security Principles
- Security Principles
- Account Security
- File System Security
- Risk Management