Professional Documents
Culture Documents
Calendar For Net and Csec 2014
Calendar For Net and Csec 2014
Uploaded by
Special operations Countries0 ratings0% found this document useful (0 votes)
2 views1 pageThis document outlines the topics and key dates for a course on network and computer security. The course covers 25 class sessions on topics such as encryption, hashing, digital signatures, zero-knowledge proofs, and security of voting. Students are assigned 5 problem sets and work on a final project over the course of the semester, with drafts, reviews, and a final due date. Quizzes and exams are also administered to assess student learning.
Original Description:
Original Title
Calendar for net and csec 2014
Copyright
© © All Rights Reserved
Available Formats
DOCX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThis document outlines the topics and key dates for a course on network and computer security. The course covers 25 class sessions on topics such as encryption, hashing, digital signatures, zero-knowledge proofs, and security of voting. Students are assigned 5 problem sets and work on a final project over the course of the semester, with drafts, reviews, and a final due date. Quizzes and exams are also administered to assess student learning.
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
2 views1 pageCalendar For Net and Csec 2014
Calendar For Net and Csec 2014
Uploaded by
Special operations CountriesThis document outlines the topics and key dates for a course on network and computer security. The course covers 25 class sessions on topics such as encryption, hashing, digital signatures, zero-knowledge proofs, and security of voting. Students are assigned 5 problem sets and work on a final project over the course of the semester, with drafts, reviews, and a final due date. Quizzes and exams are also administered to assess student learning.
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
You are on page 1of 1
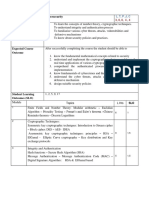
SES
# TOPICS KEY DATES CHECK
1 Introduction Done
2 Security Mechanisms and Principles Problem set 1 Out
3 Encryption, Perfect Secrecy, One-Time Pad
4 Cryptographic Hash Functions
5 Hashing Applications and Constructions
6 Bitcoin Problem set 1 Due, Problem set 2 Out
7 Secret Sharing
8 Block Ciphers
9 Block Cipher Modes
10 Message Authentication Codes Problem set 2 Due, Project Ideas Due, Problem set 3 Out
11 Prime Finding and other “Crypto” Math
12 Diffie-Hellman Key Exchange and Crypto Groups
13 Pedersen Commitment, PK Encryption, DDH Project Draft Due
14 Malleability of El Gamal, IND-CCA2 Problem set 3 Due, Problem set 4 Out
15 Digital Signatures
16 DSA, Gap Groups Project Progress Review
17 Gap Groups, Bilinear Maps, and Applications
18 Zero-Knowledge Proofs Problem set 4 Due
19 No Lecture (Quiz) Quiz
20 Security of Voting Problem set 5 Out, Project Progress Review
21 Security of Voting (cont.)
22 Project Presentations
23 Project Presentations (cont.) Problem set 5 Due
24 Project Presentations (cont.)
25 Project Presentations (cont.)
26 No Class Final Project Due
https://ocw.mit.edu/courses/6-857-network-and-computer-security-spring-2014/pages/
You might also like
- DIS10.1 Ethical Hacking and CountermeasuresDocument14 pagesDIS10.1 Ethical Hacking and CountermeasuresJaspal Singh RanaNo ratings yet
- IT-312-course OutlineDocument3 pagesIT-312-course OutlineWaleed HussainNo ratings yet
- Information and Network SecurityDocument4 pagesInformation and Network SecurityMananNo ratings yet
- ITM-214-course OutlineDocument3 pagesITM-214-course OutlineWaleed HussainNo ratings yet
- CY5001 - Information SecurityDocument5 pagesCY5001 - Information SecurityabcNo ratings yet
- Cisco Certified Support Technician Cybersecurit Workbook D1Document40 pagesCisco Certified Support Technician Cybersecurit Workbook D1James MurphyNo ratings yet
- Unit1 RoshanJameelDocument104 pagesUnit1 RoshanJameelSarfirey GamersNo ratings yet
- Security Trends, Legal, Ethical and Professional Aspects of SecurityDocument3 pagesSecurity Trends, Legal, Ethical and Professional Aspects of SecurityArul SenthilNo ratings yet
- NIS Micro Project List CDocument2 pagesNIS Micro Project List CHrx XNo ratings yet
- B.Tech. Computer: Uka Tarsadia UniversityDocument6 pagesB.Tech. Computer: Uka Tarsadia UniversityPatelNo ratings yet
- 05 Ad8602 Dis Unit 5Document70 pages05 Ad8602 Dis Unit 5BRINDHANo ratings yet
- Table of Figures 4 5 2.0 Project Description 6Document42 pagesTable of Figures 4 5 2.0 Project Description 6atul gaikwadNo ratings yet
- 04 Ad8602 Dis Unit 4Document95 pages04 Ad8602 Dis Unit 4BRINDHANo ratings yet
- Syllabus For Cyber Security.Document3 pagesSyllabus For Cyber Security.Roushan GiriNo ratings yet
- Syllabus CM2025 CSDocument6 pagesSyllabus CM2025 CSPrasannaNo ratings yet
- NIS Microproject EditDocument18 pagesNIS Microproject Editsanketbiradar1312No ratings yet
- 01 Ad8602 Dis Unit 1Document78 pages01 Ad8602 Dis Unit 1BRINDHANo ratings yet
- Document 11Document4 pagesDocument 11Md. Nazmus SakibNo ratings yet
- UT Dallas Syllabus For cs6324.001 05f Taught by Hsingmean Sha (Edsha)Document3 pagesUT Dallas Syllabus For cs6324.001 05f Taught by Hsingmean Sha (Edsha)UT Dallas Provost's Technology GroupNo ratings yet
- Course Syllabus Systems Security Certified Professional (SSCP)Document3 pagesCourse Syllabus Systems Security Certified Professional (SSCP)Johnson MukadiNo ratings yet
- IT602-N Information SecurityDocument3 pagesIT602-N Information Securityjainam acharyaNo ratings yet
- Information Security and Cryptography Updated SyllabusDocument4 pagesInformation Security and Cryptography Updated SyllabusShivani DimriNo ratings yet
- Free Download Design and Analysis of Security Protocol For Communication First Edition Dinesh Goyal Full Chapter PDFDocument51 pagesFree Download Design and Analysis of Security Protocol For Communication First Edition Dinesh Goyal Full Chapter PDFanthony.bright301100% (16)
- UntitledDocument89 pagesUntitledSNEHA SNEHA .MNo ratings yet
- CPP Final Project AvishakerDocument54 pagesCPP Final Project AvishakerkhenatavishkarNo ratings yet
- Fall 2021 SyllabusDocument8 pagesFall 2021 SyllabusPalash SharmaNo ratings yet
- Datamine Manual Mineria Subterranea 2 4D PDFDocument127 pagesDatamine Manual Mineria Subterranea 2 4D PDFAgus A MarsaolyNo ratings yet
- Cryptography and Network SecurityDocument2 pagesCryptography and Network SecurityVishwa Pratap SinghNo ratings yet
- CSC121 Scheme of WorkDocument2 pagesCSC121 Scheme of WorkMELISSA SOFIA SHAHRANNo ratings yet
- Cloud Native Security Whitepaper v2 (May 2022)Document55 pagesCloud Native Security Whitepaper v2 (May 2022)Vlad VikernesNo ratings yet
- UntitledDocument155 pagesUntitledChetan DhandreNo ratings yet
- Silabus MKKDDocument10 pagesSilabus MKKDKadongNo ratings yet
- 077 Sandeep NairDocument37 pages077 Sandeep NairyazirmkNo ratings yet
- Live WireDocument2 pagesLive Wireharshada kavdeNo ratings yet
- Amritsar Website IndexDocument2 pagesAmritsar Website IndexRohit SharmaNo ratings yet
- CNCF - Cloud Native Security Whitepaper May2022 v2Document55 pagesCNCF - Cloud Native Security Whitepaper May2022 v2Shantanu GudihalNo ratings yet
- Comprehensive Exam Question Format CryptographyDocument5 pagesComprehensive Exam Question Format Cryptographyneetika guptaNo ratings yet
- Master PDFDocument36 pagesMaster PDFAshrafNo ratings yet
- PDF Ceh V10 Certified Ethical Hacker Study Guide 1St Edition Ric Messier Ebook Full ChapterDocument53 pagesPDF Ceh V10 Certified Ethical Hacker Study Guide 1St Edition Ric Messier Ebook Full Chaptergeoffrey.radsky250100% (2)
- Ce348: Information Security: Teaching Scheme Theory Practical Tutorial Total CreditDocument5 pagesCe348: Information Security: Teaching Scheme Theory Practical Tutorial Total CreditAaliya SharmaNo ratings yet
- CSE4003 Cyber-Security ETH 1 AC41Document8 pagesCSE4003 Cyber-Security ETH 1 AC41govindNo ratings yet
- Security Attacks in Cloud ComputingDocument39 pagesSecurity Attacks in Cloud Computingbabupradhan452No ratings yet
- Network CsDocument5 pagesNetwork Csnotsubhash2000No ratings yet
- Implementation of Cryptographic Algorithms and 4Document61 pagesImplementation of Cryptographic Algorithms and 4Kk sdNo ratings yet
- Ce348: Information Technology: Credits and Hours: Teaching Scheme Theory Practical Tutorial Total CreditDocument4 pagesCe348: Information Technology: Credits and Hours: Teaching Scheme Theory Practical Tutorial Total CreditChandresh PadmaniNo ratings yet
- IT502 - Information SecurityDocument3 pagesIT502 - Information SecurityNader AzalNo ratings yet
- REPORTDocument37 pagesREPORTDeepanshu TyagiNo ratings yet
- Sat - 65.Pdf - Providing Security and Clustering For Bigdata in CloudDocument11 pagesSat - 65.Pdf - Providing Security and Clustering For Bigdata in CloudVj KumarNo ratings yet
- Unit 4 CryptographyDocument106 pagesUnit 4 CryptographyRαndσm thíngsNo ratings yet
- 4 (6) 87syllabusDocument2 pages4 (6) 87syllabuskstu1112No ratings yet
- Sat 21.PDF Secure VaultDocument11 pagesSat 21.PDF Secure VaultVj KumarNo ratings yet
- DSM ReportDocument60 pagesDSM ReportMalik GoharNo ratings yet
- Course Code Course Title Credits PSCSP4022 Practical Course On Specialization: Cyber & Information Security (Cryptography and Crypt Analysis) 02Document1 pageCourse Code Course Title Credits PSCSP4022 Practical Course On Specialization: Cyber & Information Security (Cryptography and Crypt Analysis) 02vipulsalujaNo ratings yet
- Unit5 CryptographyDocument156 pagesUnit5 CryptographyRαndσm thíngsNo ratings yet
- Network Security Mgmt.Document9 pagesNetwork Security Mgmt.Dayanand Gowda Kr0% (1)
- Othp 67Document50 pagesOthp 67Behnam NejatiyanNo ratings yet
- Cryptography, Information Theory, and Error-Correction: A Handbook for the 21st CenturyFrom EverandCryptography, Information Theory, and Error-Correction: A Handbook for the 21st CenturyNo ratings yet
- CISSP Exam Study Guide For Security Professionals: NIST Cybersecurity Framework, Risk Management, Digital Forensics & GovernanceFrom EverandCISSP Exam Study Guide For Security Professionals: NIST Cybersecurity Framework, Risk Management, Digital Forensics & GovernanceRating: 5 out of 5 stars5/5 (1)
- Numerical Simulations and Case Studies Using Visual C++.NetFrom EverandNumerical Simulations and Case Studies Using Visual C++.NetNo ratings yet