Professional Documents
Culture Documents
The Published ISO27K About IT-Security
Uploaded by
Screamer Fever0 ratings0% found this document useful (0 votes)
17 views3 pagesOriginal Title
The published ISO27K about IT-Security
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
17 views3 pagesThe Published ISO27K About IT-Security
Uploaded by
Screamer FeverCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 3
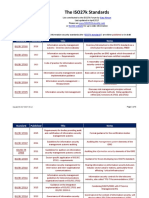
The published ISO27K standards related to "information technology -
security techniques":
1. ISO/IEC 27000 — Information security management systems — Overview and vocabulary
2. ISO/IEC 27001 — Information technology - Security Techniques - Information security
management systems — Requirements. The 2013 release of the standard specifies an
information security management system in the same formalized, structured and succinct
manner as other ISO standards specify other kinds of management systems.
3. ISO/IEC 27002 — Code of practice for information security controls - essentially a detailed
catalog of information security controls that might be managed through the ISMS
4. ISO/IEC 27003 — Information security management system implementation guidance
5. ISO/IEC 27004 — Information security management — Monitoring, measurement, analysis
and evaluation
6. ISO/IEC 27005 — Information security risk management
7. ISO/IEC 27006 — Requirements for bodies providing audit and certification of information
security management systems
8. ISO/IEC 27007 — Guidelines for information security management systems auditing
(focused on auditing the management system)
9. ISO/IEC TR 27008 — Guidance for auditors on ISMS controls (focused on auditing the
information security controls)
10. ISO/IEC 27009 — Essentially an internal document for the committee developing
sector/industry-specific variants or implementation guidelines for the ISO27K standards
11. ISO/IEC 27010 — Information security management for inter-sector and inter-organizational
communications
12. ISO/IEC 27011 — Information security management guidelines for telecommunications
organizations based on ISO/IEC 27002
13. ISO/IEC 27013 — Guideline on the integrated implementation of ISO/IEC 27001 and
ISO/IEC 20000-1 (derived from ITIL)
14. ISO/IEC 27014 — Information security governance. Mahncke assessed this standard in the
context of Australian e-health.
15. ISO/IEC TR 27015 — Information security management guidelines for financial services -
Now withdrawn
16. ISO/IEC TR 27016 — information security economics
17. ISO/IEC 27017 — Code of practice for information security controls based on ISO/IEC
27002 for cloud services
18. ISO/IEC 27018 — Code of practice for protection of personally identifiable information (PII)
in public clouds acting as PII processors
19. ISO/IEC TR 27019 — Information security for process control in the energy industry
20. ISO/IEC 27031 — Guidelines for information and communication technology readiness for
business continuity
21. ISO/IEC 27032 — Guideline for cybersecurity
22. ISO/IEC 27033-1 — Network security - Part 1: Overview and concepts
23. ISO/IEC 27033-2 — Network security - Part 2: Guidelines for the design and implementation
of network security
24. ISO/IEC 27033-3 — Network security - Part 3: Reference networking scenarios - Threats,
design techniques and control issues
25. ISO/IEC 27033-4 — Network security - Part 4: Securing communications between networks
using security gateways
26. ISO/IEC 27033-5 — Network security - Part 5: Securing communications across networks
using Virtual Private Networks (VPNs)
27. ISO/IEC 27033-6 — Network security - Part 6: Securing wireless IP network access
28. ISO/IEC 27034-1 — Application security - Part 1: Guideline for application security
29. ISO/IEC 27034-2 — Application security - Part 2: Organization normative framework
30. ISO/IEC 27034-6 — Application security - Part 6: Case studies
31. ISO/IEC 27035-1 — Information security incident management - Part 1: Principles of
incident management
32. ISO/IEC 27035-2 — Information security incident management - Part 2: Guidelines to plan
and prepare for incident response
33. ISO/IEC 27036-1 — Information security for supplier relationships - Part 1: Overview and
concepts
34. ISO/IEC 27036-2 — Information security for supplier relationships - Part 2: Requirements
35. ISO/IEC 27036-3 — Information security for supplier relationships - Part 3: Guidelines for
information and communication technology supply chain security
36. ISO/IEC 27036-4 — Information security for supplier relationships - Part 4: Guidelines for
security of cloud services
37. ISO/IEC 27037 — Guidelines for identification, collection, acquisition and preservation of
digital evidence
38. ISO/IEC 27038 — Specification for Digital redaction on Digital Documents
39. ISO/IEC 27039 — Intrusion prevention
40. ISO/IEC 27040 — Storage security
41. ISO/IEC 27041 — Investigation assurance
42. ISO/IEC 27042 — Analyzing digital evidence
43. ISO/IEC 27043 — Incident investigation
44. ISO/IEC 27050-1 — Electronic discovery - Part 1: Overview and concepts
45. ISO/IEC 27050-2 — Electronic discovery - Part 2: Guidance for governance and management
of electronic discovery
46. ISO/IEC 27701 — Information technology - Security Techniques - Information security
management systems — Privacy Information Management System (PIMS).
47. ISO 27799 — Information security management in health using ISO/IEC 27002 - guides
health industry organizations on how to protect personal health information using ISO/IEC
27002.
You might also like
- Manajemen Sistem Standard ISO 27000Document4 pagesManajemen Sistem Standard ISO 27000wahid100% (1)
- FamilyDocument11 pagesFamilypooku37No ratings yet
- Segu Info Familia Iso 27000Document4 pagesSegu Info Familia Iso 27000RobertoNo ratings yet
- ISO27k Standards ListingDocument6 pagesISO27k Standards ListingWervyan ShalannandaNo ratings yet
- Standar Dan Kerangka Kerja Keamanan Informasi: ISO 27000 Information Security Management SystemDocument16 pagesStandar Dan Kerangka Kerja Keamanan Informasi: ISO 27000 Information Security Management SystemDevianitaNo ratings yet
- Pecb 27001 Lead Auditor Presentation by PP PDF FreeDocument34 pagesPecb 27001 Lead Auditor Presentation by PP PDF FreeAbdoul Kader Mbang100% (1)
- Materi Training Awareness ISO 27001 2015 Indospring (Bu Putih Ayu)Document23 pagesMateri Training Awareness ISO 27001 2015 Indospring (Bu Putih Ayu)andhika025100% (1)
- ISO27k Standards ListingDocument2 pagesISO27k Standards Listingmax4oneNo ratings yet
- Examples StandardsDocument4 pagesExamples Standardsmulti media0% (1)
- ISO 27000 Szabványcsalád 20200114Document6 pagesISO 27000 Szabványcsalád 20200114Jeampierr JIMENEZ MARQUEZNo ratings yet
- Normas ISODocument4 pagesNormas ISOJavier Giovanni Jojoa OrbesNo ratings yet
- ISO2700Document1 pageISO2700madunixNo ratings yet
- ISO/IEC 27000 (Free) : 1 2018 Vocabulary StandardDocument28 pagesISO/IEC 27000 (Free) : 1 2018 Vocabulary Standardholamundo123No ratings yet
- ISACA ISO OverviewDocument13 pagesISACA ISO OverviewNitin MathurNo ratings yet
- ISO 27001 Controls – A guide to implementing and auditingFrom EverandISO 27001 Controls – A guide to implementing and auditingRating: 5 out of 5 stars5/5 (1)
- ISMS 27K StandardsDocument25 pagesISMS 27K StandardsS MehtaNo ratings yet
- Cybersecurity StandardsDocument7 pagesCybersecurity Standardsgilberto araujoNo ratings yet
- ISO/IEC Information & ICT Security and Governance Standards in PracticeDocument19 pagesISO/IEC Information & ICT Security and Governance Standards in PracticeJéferson LucasNo ratings yet
- ISO27k Standards Listing PDFDocument7 pagesISO27k Standards Listing PDFZulkkanNo ratings yet
- Iso27000 Isaca Feb 2008Document27 pagesIso27000 Isaca Feb 2008jiten76No ratings yet
- ISO 27001/ISO 27002: A guide to information security management systemsFrom EverandISO 27001/ISO 27002: A guide to information security management systemsNo ratings yet
- ISO StandardsDocument1 pageISO StandardsGaurav SharmaNo ratings yet
- Iso 27000 SeriesDocument1 pageIso 27000 Seriesnmukherjee20No ratings yet
- ISO 27000 Family of StandardsDocument15 pagesISO 27000 Family of Standardsyan100% (1)
- The ISO27k Standards: Gary HinsonDocument10 pagesThe ISO27k Standards: Gary HinsonKaran DeetNo ratings yet
- Iso 2007Document3 pagesIso 2007Tejendra GohilNo ratings yet
- Information Security StandardsDocument8 pagesInformation Security StandardsJournal of Mobile, Embedded and Distributed Systems (JMEDS)No ratings yet
- ISO27k ISMS 2 ISO27k Standards Listing 2023Document10 pagesISO27k ISMS 2 ISO27k Standards Listing 2023Bobby SharonNo ratings yet
- Iso 27001 PDFDocument7 pagesIso 27001 PDFMonica MoreiraNo ratings yet
- (IJCST-V5I2P72) :augustine O. Ugbari, Ikechukwu O. UcheDocument4 pages(IJCST-V5I2P72) :augustine O. Ugbari, Ikechukwu O. UcheEighthSenseGroupNo ratings yet
- PZ Step-By-step Guidance On How To Establish Implement and Operate ISMS Dec 2014Document12 pagesPZ Step-By-step Guidance On How To Establish Implement and Operate ISMS Dec 2014Bara DanielNo ratings yet
- Robert ChristianDocument18 pagesRobert ChristianChristen CastilloNo ratings yet
- Information Technology Standards GuidelinesDocument2 pagesInformation Technology Standards GuidelinesmanjarimaranNo ratings yet
- Standards Listing 2023Document10 pagesStandards Listing 2023kannadasNo ratings yet
- ISO 27k - Standards - Listing - 2022Document15 pagesISO 27k - Standards - Listing - 2022Hanan ZayedNo ratings yet
- ISO27k ISMS 2 ISO27k Standards Listing 2022Document10 pagesISO27k ISMS 2 ISO27k Standards Listing 2022sungrayNo ratings yet
- USQC OverviewDocument7 pagesUSQC OverviewMohammed YasserNo ratings yet
- Dokumen - Tips - Iso Iec 27004 DraftDocument37 pagesDokumen - Tips - Iso Iec 27004 Draftlinuxawy2_147783831No ratings yet
- ISO27k Standards ListingDocument6 pagesISO27k Standards ListingTikCGNo ratings yet
- Materi Training Awareness ISO 27001 2015 Indospring Bu Putih AyuDocument26 pagesMateri Training Awareness ISO 27001 2015 Indospring Bu Putih AyuinoktavNo ratings yet
- Sources of Guidance On Security in The Telecommunications SectorDocument14 pagesSources of Guidance On Security in The Telecommunications Sectorgeografie geografieNo ratings yet
- Introduction To Information Security and Information Security ManagementDocument33 pagesIntroduction To Information Security and Information Security ManagementGusti Arsyad100% (1)
- ISO27k ISMS 2 ISO27k Standards Listing 2024Document11 pagesISO27k ISMS 2 ISO27k Standards Listing 2024Natália DiasNo ratings yet
- Iso27002 PDFDocument12 pagesIso27002 PDFPablo Brito100% (3)
- ISO27k Standards ListingDocument6 pagesISO27k Standards ListingOrlando ContrerasNo ratings yet
- Webinar PrephandlingCrisisDocument18 pagesWebinar PrephandlingCrisisSabrina PutriNo ratings yet
- Information Security StandardsDocument8 pagesInformation Security StandardsCalperniaUSANo ratings yet
- ISO27k Standards Listing PDFDocument7 pagesISO27k Standards Listing PDFmamunurrahmanNo ratings yet
- Existingstandards SpreadsheetDocument19 pagesExistingstandards SpreadsheetZaidiNo ratings yet
- Australian Government Information Security Manual (February 2021)Document198 pagesAustralian Government Information Security Manual (February 2021)raedNo ratings yet
- Manual de Seguridad PDFDocument197 pagesManual de Seguridad PDFaalfonsopNo ratings yet
- Iso 27001Document3 pagesIso 27001nebojsami100% (1)
- IC ISO 27002 Information Security Guidelines Checklist 10838Document4 pagesIC ISO 27002 Information Security Guidelines Checklist 10838Nam NguyễnNo ratings yet
- Reports ISO 27001Document43 pagesReports ISO 27001Prashanti GaonkarNo ratings yet
- CT05 1 ISO 27001 Documentation KitDocument25 pagesCT05 1 ISO 27001 Documentation Kitfahrizal fatah100% (6)
- Iso 27001Document7 pagesIso 27001Sreekar80% (5)
- Infoturbest Küberturbe Halduseni - Lähenemine Vastavalt Standarditele ISO 27001 Ja 27032Document93 pagesInfoturbest Küberturbe Halduseni - Lähenemine Vastavalt Standarditele ISO 27001 Ja 27032excelencia5No ratings yet
- Seminar AbsDocument3 pagesSeminar AbsanujtewariiNo ratings yet
- ISMS Implementer Course - Module 2 - Introduction To ISO27001Document21 pagesISMS Implementer Course - Module 2 - Introduction To ISO27001Anil ChiplunkarNo ratings yet
- Scratch Paper (Business Plan)Document17 pagesScratch Paper (Business Plan)The Brain Dump PHNo ratings yet
- Sinking Fund and AmortizationDocument8 pagesSinking Fund and AmortizationMay Jovi JalaNo ratings yet
- Vip Service ContractDocument2 pagesVip Service ContractJames Lucas MooreNo ratings yet
- Literature ReviewDocument50 pagesLiterature ReviewMohmmedKhayyumNo ratings yet
- Education: ProfileDocument14 pagesEducation: ProfileRizky NafandyNo ratings yet
- KEVIN KIMUNGA KIMANI - MSC FINANCE RESEARCH PROJECTDocument52 pagesKEVIN KIMUNGA KIMANI - MSC FINANCE RESEARCH PROJECTabhijeet falaneNo ratings yet
- IFC Federal Bank India Case StudyDocument13 pagesIFC Federal Bank India Case StudyAnchal katiyarNo ratings yet
- Entrep PPT 1 StudentDocument15 pagesEntrep PPT 1 StudentShaina LuisNo ratings yet
- The 9000 Store: ISO 9001 Executive OverviewDocument17 pagesThe 9000 Store: ISO 9001 Executive OverviewGiovanniNo ratings yet
- Wat-Pi Kit - 2020-22KGPDocument9 pagesWat-Pi Kit - 2020-22KGPKanishka AdvaniNo ratings yet
- F8 BankDocument78 pagesF8 BankThanh Phạm100% (1)
- Rebates CalculationDocument5 pagesRebates CalculationSilviu JitianuNo ratings yet
- Career Air Force-India (Candidate Section)Document1 pageCareer Air Force-India (Candidate Section)Aditya GaurNo ratings yet
- Cover LetterDocument2 pagesCover LetterAnasAhmedNo ratings yet
- Amended Date of Board Resolution No 3Document1 pageAmended Date of Board Resolution No 3Kath LomibaoNo ratings yet
- PublicationDocument84 pagesPublicationandreiNo ratings yet
- Coursework PreparationDocument15 pagesCoursework PreparationabubakargorejaNo ratings yet
- Topic:: LESSON: Practice Occupational Health and SafetyDocument2 pagesTopic:: LESSON: Practice Occupational Health and SafetyJANICE RUBIALESNo ratings yet
- Smart Investment (E-Copy) Vol 15 Issue No. 44 (11th December 2022)Document81 pagesSmart Investment (E-Copy) Vol 15 Issue No. 44 (11th December 2022)MittapalliUdayKumarReddyNo ratings yet
- Documents of TitleDocument5 pagesDocuments of TitleNeil MayorNo ratings yet
- From Communication To Corporate Communication - A New Conceptual Framework Embodied in Strategic PlanningDocument7 pagesFrom Communication To Corporate Communication - A New Conceptual Framework Embodied in Strategic PlanningAnonymous lAfk9gNPNo ratings yet
- Zinc Payment Letter 04.12.2022Document3 pagesZinc Payment Letter 04.12.2022SHASHIKIRAN SNo ratings yet
- Ex01 - Cost Behavior - Cost-Volume-Profit Analysis XDocument18 pagesEx01 - Cost Behavior - Cost-Volume-Profit Analysis Xhanie lalaNo ratings yet
- Listening and Note-Taking Week 01Document6 pagesListening and Note-Taking Week 01AlvinPennNo ratings yet
- Multiple Choice Questions On Manufacturing Process and Production EngineeringDocument3 pagesMultiple Choice Questions On Manufacturing Process and Production EngineeringrahmaNo ratings yet
- Comparative Management EPHRAIMDocument3 pagesComparative Management EPHRAIMMohamed AhmedNo ratings yet
- Credence Quality in ServicesDocument38 pagesCredence Quality in Servicesshabraj79No ratings yet
- Exotic CuisineDocument5 pagesExotic CuisineHana Tarizkha CoganuliNo ratings yet
- Security Company Introduction LetterDocument21 pagesSecurity Company Introduction LetterNitesh GuptaNo ratings yet
- Product and Brand Management Notes-9-12Document4 pagesProduct and Brand Management Notes-9-12Makarand WathNo ratings yet