Professional Documents
Culture Documents
E123262-1665585623602-188547-E123262-Fudhail Faizal-Security-Assignment01
Uploaded by
fudhailfaizalOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
E123262-1665585623602-188547-E123262-Fudhail Faizal-Security-Assignment01
Uploaded by
fudhailfaizalCopyright:
Available Formats
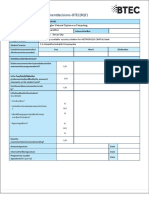
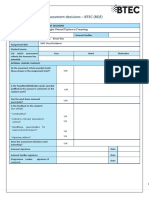
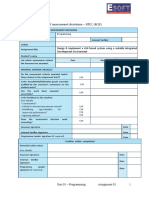
Higher Nati onals
Internal verification of assessment decisions – BTEC (RQF)
INTERNAL VERIFICATION – ASSESSMENT DECISIONS
Programme title BTEC Higher National Diploma in Computing
Assessor Internal Verifier
Unit 05: Security
Unit(s)
EMC Cyber
Assignment title
Student’s name
List which assessment Pass Merit Distinction
criteria the Assessor has
awarded.
INTERNAL VERIFIER CHECKLIST
Do the assessment criteria awarded
match those shown in the assignment
brief? Y/N
Is the Pass/Merit/Distinction grade
awarded justified by the assessor’s
Y/N
comments on the student work?
Has the work been assessed
accurately? Y/N
Is the feedback to the student:
Give details:
• Constructive?
Y/N
• Linked to relevant assessment
criteria? Y/N
• Identifying opportunities for
improved performance?
Y/N
• Agreeing actions? Y/N
Does the assessment decision need
amending? Y/N
Assessor signature Date
Internal Verifier signature Date
Programme Leader signature (if
required) Date
E123262 – Fudhail Faizal – Security Assignment 01
Confirm action completed
Remedial action taken
Give details:
Assessor signature Date
Internal Verifier
signature Date
Programme Leader signature
(if required) Date
E123262 – Fudhail Faizal – Security Assignment 01
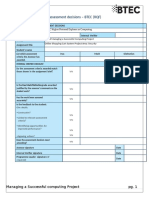
Higher Nationals - Summative Assignment Feedback Form
Student Name/ID
Unit 05: Security
Unit Title
Assignment Number 1 Assessor
Date Received
Submission Date 1st submission
Date Received 2nd
Re-submission Date submission
Assessor Feedback:
LO1. Assess risks to IT security
Pass, Merit & Distinction P1 P2 M1 D1
Descripts
LO2. Describe IT security solutions.
Pass, Merit & Distinction P3 P4 M2 D1
Descripts
LO3. Review mechanisms to control organisational IT security.
Pass, Merit & Distinction P5 P6 M3 M4 D2
Descripts
LO4. Manage organisational security.
Pass, Merit & Distinction P7 P8 M5 D3
Descripts
Grade: Assessor Signature: Date:
Resubmission Feedback:
Grade: Assessor Signature: Date:
Internal Verifier’s Comments:
Signature & Date:
E123262 – Fudhail Faizal – Security Assignment 01
* Please note that grade decisions are provisional. They are only confirmed once internal and external moderation has taken place and grades decisions have
been agreed at the assessment board
Pearson
Higher Nationals in
Computing
Unit 5 : Security
E123262 – Fudhail Faizal – Security Assignment 01
5
E123262 – Fudhail Faizal – Security Assignment 01
General Guidelines
1. A Cover page or title page – You should always attach a title page to your assignment. Use previous page as
your cover sheet and make sure all the details are accurately filled.
2. Attach this brief as the first section of your assignment.
3. All the assignments should be prepared using a word processing software.
4. All the assignments should be printed on A4 sized papers. Use single side printing.
5. Allow 1” for top, bottom , right margins and 1.25” for the left margin of each page.
Word Processing Rules
1. The font size should be 12 point, and should be in the style of Time New Roman.
2. Use 1.5 line spacing. Left justify all paragraphs.
3. Ensure that all the headings are consistent in terms of the font size and font style.
4. Use footer function in the word processor to insert Your Name, Subject, Assignment No, and Page Number
on each page. This is useful if individual sheets become detached for any reason.
5. Use word processing application spell check and grammar check function to help editing your assignment.
Important Points:
1. It is strictly prohibited to use textboxes to add texts in the assignments, except for the compulsory
information. eg: Figures, tables of comparison etc. Adding text boxes in the body except for the before
mentioned compulsory information will result in rejection of your work.
2. Carefully check the hand in date and the instructions given in the assignment. Late submissions will not be
accepted.
3. Ensure that you give yourself enough time to complete the assignment by the due date.
4. Excuses of any nature will not be accepted for failure to hand in the work on time.
5. You must take responsibility for managing your own time effectively.
6. If you are unable to hand in your assignment on time and have valid reasons such as illness, you may apply
(in writing) for an extension.
7. Failure to achieve at least PASS criteria will result in a REFERRAL grade .
8. Non-submission of work without valid reasons will lead to an automatic RE FERRAL. You will then be asked
to complete an alternative assignment.
9. If you use other people’s work or ideas in your assignment, reference them properly using HARVARD
referencing system to avoid plagiarism. You have to provide both in-text citation and a reference list.
10. If you are proven to be guilty of plagiarism or any academic misconduct, your grade could be reduced to A
REFERRAL or at worst you could be expelled from the course
E123262 – Fudhail Faizal – Security Assignment 01
Student Declaration
I hereby, declare that I know what plagiarism entails, namely to use another’s work and to present it as my own
without attributing the sources in the correct way. I further understand what it means to copy another’s work.
1. I know that plagiarism is a punishable offence because it constitutes theft.
2. I understand the plagiarism and copying policy of the Edexcel UK.
3. I know what the consequences will be if I plagiarize or copy another’s work in any of the assignments for this
programme. .
4. I declare therefore that all work presented by me for every aspects of my programme, will be of my own,
and where I have made use of another’s work, I will attribute the source in the correct way.
5. I acknowledge that the attachment of this document, signed or not, constitutes a binding agreement
between myself and Pearson UK.
6. I understand that my assignment will not be considered as submitted if this document is not attached to the
main submission.
Student’s Signature: Date:
(Provide E-mail ID) (Provide Submission Date)
E123262 – Fudhail Faizal – Security Assignment 01
Assignment Brief
Student Name /ID Number
Unit Number and Title Unit 5- Security
Academic Year 2020/2021
Unit Tutor
Assignment Title EMC Cyber
Issue Date
Submission Date
IV Name & Date
Submission Format:
The submission should be in the form of an individual written report written in a concise, formal business style
using single spacing and font size 12. You are required to make use of headings, paragraphs and subsections as
appropriate, and all work must be supported with research and referenced using Harvard referencing system.
Please provide in- text citation and an end list of references using Harvard referencing system.
Section 4.2 of the assignment required to do a 15 minutes presentation to illustrate the answers.
Unit Learning Outcomes:
LO1 Assess risks to IT security.
LO2 Describe IT security solutions.
LO3 Review mechanisms to control organisational IT security.
LO4 Manage organisational security.
E123262 – Fudhail Faizal – Security Assignment 01
Assignment Brief and Guidance:
Scenario
‘EMC Cyber’ is a reputed cyber security company based in Colombo Sri Lanka that is delivering
security products and services across the entire information technology infrastructure. The company
has a number of clients both in Sri Lanka and abroad, which includes some of the top-level companies
of the world serving in multitude of industries. The company develops cyber security software
including firewalls, anti-virus, intrusion detection and protection, and endpoint security. EMC Cyber is
tasked with protecting companies’ networks, clouds, web applications and emails. They also offer
advanced threat protection, secure unified access, and endpoint security. Further they also play the
role of consulting clients on security threats and how to solve them. Additionally the company follows
different risk management standards depending on the company, with the ISO 31000 being the most
prominent.
One of the clients of EMC Cyber, Lockhead Aerospace manufacturing which is a reputed aircraft
manufacturer based in the US, has tasked the company to investigate the security implications of
developing IOT based automation applications in their manufacturing process. The client has
requested EMC to further audit security risks of implementing web based IOT applications in their
manufacturing process and to propose solutions. Further, Lockhead uses ISO standards and has
instructed EMC to use the ISO risk management standards when proposing the solution.
The director of the company understands such a system would be the target for cyber-attacks. As you
are following a BTEC course which includes a unit in security, the director has asked you to investigate
and report on potential cyber security threats to their web site, applications and infrastructure. After
the investigation you need to plan a solution and how to implement it according standard software
engineering principles.
E123262 – Fudhail Faizal – Security Assignment 01
Activity 01
Assuming the role of External Security Analyst, you need to compile a report focusing on following
elements to the board of EMC Cyber’;
1.1 Identify the CIA Triad concept and evaluate why and how the CIA Triad could be utilize to EMC
Cyber in order to improve the organization’s security.
1.2 Identify types of security risks EMC Cyber is subject to its present setup and the impact that they
would make on the business itself. Evaluate at least three physical and virtual security risks identified
and suggest the security measures that can be implemented in order to improve the organization’s
security.
1.3 Develop and describe security procedures for EMC Cyber to minimize the impact of issues
discussed in section (1.1) by assessing and rectifying the risks.
Activity 02
2.1 Identify how EMC Cyber and its clients will be impacted by improper/ incorrect configurations
that are applicable to firewalls and VPN solutions. IT security can include a network monitoring
system. Discuss how EMC cyber can benefit by implementing a network monitoring system with
supporting reasons.
2.2 Explain how the following technologies would benefit EMC Cyber and its Clients by facilitating a
‘trusted network’. (Support your answer with suitable examples).
i) DMZ
ii) Static IP
iii)NAT
2.3 Identify and evaluate the tools that can be utilized by EMC cyber to improve the network and
10
E123262 – Fudhail Faizal – Security Assignment 01
security performance without compromising each other. Evaluate at least three virtual and physical
security measures that can be implemented by EMC to uphold the integrity of organization’s IT
policy.
Activity 03
3.1 Discuss suitable risk assessment integrated enterprise risk management procedures for EMC
Cyber solutions and the impact an IT security audit will have on safeguarding organization and its
clients. Furthermore, your discussion should include how IT security can be aligned with an
organizational IT policy and how misalignment of such a policy can impact on organization’s security.
(This can include one or more of the following: network change management, audit control, business
continuance/disaster recovery plans, potential loss of data/business, intellectual property, Data
Protection Act; Computer Misuse Act; ISO 31000 standards.)
3.2 Explain the mandatory data protection laws and procedures which will be applied to data storage
solutions provided by EMC Cyber. You should also summarize ISO 31000 risk management
methodology.
Activity 04
4.1 Design an organizational security policy for EMC Cyber to minimize exploitations and misuses
while evaluating the suitability of the tools used in an organizational policy.
4.2 Develop and present a disaster recovery plan for EMC Cyber according to the ISO/IEC 17799:2005
or similar standard which should include the main components of an organizational disaster recovery
plan with justifications. Discuss how critical the roles of the stakeholders in the organization to
successfully implement the security policy and the disaster recovery plan you recommended as a part
11
E123262 – Fudhail Faizal – Security Assignment 01
of the security audit.
(Students should produce a 15 minutes PowerPoint presentation which illustrates the answer for
this section including justifications and reason for decisions and options used).
12
E123262 – Fudhail Faizal – Security Assignment 01
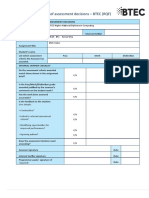
Grading Rubric
Grading Criteria Achieved Feedback
LO1 Assess risks to IT security
P1 Identify types of security risks to organisations.
P2 Describe organizational security procedures.
M1 Propose a method to assess and treat IT security risks.
LO2 Describe IT security solutions
P3 Identify the potential impact to IT security of incorrect
configuration of firewall policies and thirparty VPNs.
P4 Show, using an example for each, how implementing a DMZ, static
IP and NAT in a network can improve Network Security.
M2 Discuss three benefits to implement network monitoring systems
with supporting reasons.
D1 Evaluate a minimum of three of physical and virtual security
measures that can be employed to ensure the integrity of
organisational IT security.
LO3 Review mechanisms to control organisational IT
security
13
E123262 – Fudhail Faizal – Security Assignment 01
P5 Discuss risk assessment procedures.
P6 Explain data protection processes and regulations as applicable to
an organisation.
M3 Summarise the ISO 31000 risk management methodology and its
application in IT security.
M4 Discuss possible impacts to organizational security resulting from
an IT security audit.
D2 Consider how IT security can be aligned with organisational
policy, detailing the security impact of any misalignment.
LO4 Manage organizational security
P7 Design and implement a security policy for an organisation.
P8 List the main components of an organisational disaster recovery
plan, justifying the reasons for inclusion.
M5 Discuss the roles of stakeholders in the organisation to implement
security audit recommendations.
D3 Evaluate the suitability of the tools used in an organisational policy.
14
E123262 – Fudhail Faizal – Security Assignment 01
Pearson Higher
Nationals in
Computing
Unit 05: Security
Assignment 01
Fudhail Faizal
Contents
Activity 1......................................................................................................................................................
15
E123262 – Fudhail Faizal – Security Assignment 01
1.1 How CIA Triad could be used in EMC Cyber.......................................................................................
1.2 Potential Security risks EMC Cyber is subjected to............................................................................
Physical and Virtual Attacks.....................................................................................................................
1.3 Security Procedure to minimize the impact of these threats............................................................
What is a Risk, Vulnerability and a Threat?...........................................................................................
Activity 2....................................................................................................................................................
2.1 What is a Firewall?...........................................................................................................................
What is a VPN........................................................................................................................................
How EMC Cyber Will Benefit from installing a network monitoring system and How EMC Cyber
and its clients will be impacted by improper configuration...................................................................
2.2 How implementing a ‘trusted network’ will benefit EMC Cyber and its Clients..............................
DMZs.....................................................................................................................................................
Static IP..................................................................................................................................................
NAT........................................................................................................................................................
2.3 Tools to improve network and security performance......................................................................
Activity 3....................................................................................................................................................
3.1 Enterprise Risk Management Procedures (ERM).............................................................................
Impact of an IT security Audit................................................................................................................
How misalignment of such a policy can impact an organization’s security...........................................
3.2 Mandatory Data Protection laws and Procedures...........................................................................
ISO 31000..............................................................................................................................................
Activity 4....................................................................................................................................................
4.1..........................................................................................................................................................
References.................................................................................................................................................
Activity 1
1.1 How CIA Triad could be used in EMC Cyber
What is the CIA Triad
The CIA triad, which is frequently referred to as availability, confidentiality, and integrity, is in fact a
concept developed to guide security procedures inside a company. This paradigm is frequently
16
E123262 – Fudhail Faizal – Security Assignment 01
referred to as the AIC (Availability, Integrity, and Consistency), which was developed to prevent
conflicts from the Central Intelligence Agency.
triad of confidentiality. Three of the most fundamental and important cybersecurity components
make up the CIA triad.
analysts argue that it needs to be updated to remain useful.
Throughout this case, the terms "availability" and "confidentiality" relate to systems of rules that
limit access to data and the assurance that data will be available for use by those who are
authorized.
Understanding the Three Principles of the CIA Triad:
Confidentiality
This principle emphasizes the need to prevent unauthorized access to private, sensitive information.
Financial information, business plans, personally identifiable information (PII), such as a Social
Security Number (SSN) or date of birth, password-protected records, email records, payment
information (including credit/debit card information), and protected health information are just a
few examples.
Data must be separated based on how important it is to your organization and access rights must be
set limits in order to ensure the confidentiality of particular sorts of information. A proactive
approach to restricting access by unauthorized people may also be necessary.
The following techniques are used to manage data confidentiality: access control lists, role-based
access control (RBAC), volume/file encryption, file permissions, encryption of data in process, in
transit, and in storage.
Access control lists, role-based access control (RBAC), volume/file encryption, file permissions,
encryption of data in process, in transit, and in storage, remote wipe capabilities, education and
training for all people with access to protected data are some of the techniques used to manage
data confidentiality.
Integrity
This part of the CIA trinity makes sure the information is accurate, real, and trustworthy. In other
words, it guarantees that the data is trustworthy and hasn't been tampered with. Regardless of
whether the data is stored in a laptop, storage device, data center, or the cloud, it must be
safeguarded while it is in use, during transit, and when it is stored.
17
E123262 – Fudhail Faizal – Security Assignment 01
You must make sure that your data is shielded from alteration and deletion by unauthorized parties,
as well as from modifications that an authorized person may make accidentally.
Through encryption, hashing, digital signatures, digital certificates, intrusion detection systems,
auditing, version control, authentication, and access controls, data integrity can be maintained.
Availability
This concept guarantees that systems, applications, and data are readily available and reachable by
authorized users at the appropriate time. To guarantee that crucial business processes continue
without interruption, networks, systems, and applications must be continuously available.
Human error, hardware failure, software failure, network failure, power outages, natural disasters,
and cyberattacks can all affect how accessible your data systems are.
Redundancy (in servers, networks, applications, and services), fault tolerance (in hardware), regular
software patches and system upgrades, keeping backups and backup copies, and disaster recovery
are some of the techniques used to ensure data and application availability.
Importance of CIA Triad For EMC Cyber
The primary framework for creating security systems and guidelines for organizations is the CIA
triad. As a result, the CIA trinity is essential to protecting your data from evolving cyberthreats. An
organization is said to have failed in properly adopting one or more of these principles if a security
incident—such as data theft or a security breach—occurs. The CIA trinity is essential to information
security because it improves security posture, assists enterprises in maintaining compliance with
complicated requirements, and guarantees business continuity.
This "triad" model, which integrates all three components, could help guide how EMC develops data
protection. When assessing the needs for potential new products and innovations, such as their new
project with Lockheed Aerospace production, this trio can help EMC by offering specific questions
about how the benefit is achieved in some of those three essential areas.
Confidentiality for EMC Cyber
To protect the secrecy of the information, specialized preparation may be necessary for people who
have access to secret materials. Training that increases employees’ awareness of danger signs and
how to avoid them is advantageous to qualified personnel. To prevent users from violating data
management standards with good intentions but potentially disastrous results, training sessions may
18
E123262 – Fudhail Faizal – Security Assignment 01
also cover password protection and log-in guidelines that include understanding of social
engineering tactics.
A great example of a tactic used to safeguard confidentiality is asking for bank account information
or credit card information when conducting online banking. Cryptography is a well-liked method for
keeping information secret. Although the use of login names and passwords is traditional, two-factor
authentication (2FA) is becoming more and more common.
Additional options include key security devices, soft tokens, and biometric authentication tokens.
Customers can also take security precautions to minimize the areas where the results are shown and
the number of times it is moved around to complete a required operation. Extremely sensitive
content may only be kept in physical copies or on space machines, unconnected memory sticks, or
other forms of protection, depending on how confidential the documents are.
Integrity for EMC Cyber
These defenses include system files and user account limitations. System configuration can be used
to prevent authorized users from committing errors or unintentionally removing items.
Companies must also set up a system for detecting information changes that may result from non-
human events like electromagnetic pulses (EMPs) or system failures.
To ensure the accuracy of the data, checksums, particularly digital checksums, could be used.
To restore the affected data to its original state, duplicates and redundancies must be available.
Electronic signatures can also offer strong non-repudiation measures, making it impossible to
contest evidence of authentications, communications transferred, document management reads,
and electronic information dissemination.
Availability for EMC Cyber
The best way to achieve this is to keep all equipment in excellent working order, make any necessary
repairs as soon as they arise, and maintain a conflict-free, efficient operating system (OS)
environment. Additionally, keeping up with any necessary software upgrades is crucial. Avoiding
congestion and having enough transmission capacity are both essential strategies. Replication,
19
E123262 – Fudhail Faizal – Security Assignment 01
dropout, RAID, and occasionally even rising clusters could lessen the severity of any equipment
issues.
Quick but flexible contingency planning is essential for the worst-case scenarios; however, this
capability depends on the presence of a comprehensive DR strategy. It is important to include
unanticipated events like wildfires and ecological catastrophes in the protection against information
leaks or connectivity problems. To prevent information loss in the event of certain events, a
duplicate can be kept in a remote location, perhaps even inside a watertight, fireproof safe. Proxy
servers and security systems, for instance, are enhanced security tools or programs that can protect
against malicious DoS attacks, unauthorized network intrusions, and missing or unavailable data.
1.2 Potential Security risks EMC Cyber is subjected to
Physical and Virtual Attacks
What are physical Attacks?
Physical threats include a subset of physical attacks. Attack denotes the presence of an attacker and
his desire to harm or cause damage.
Some instances:
Attacks by terrorists (also against data center).
hostile military assault (for example against command and control center).
every physical assault on a person (also again IT staff or users).
Bites, bruises, injuries, dislocations, fractures, and punches (including IT staff).
Armed theft.
stealing from a person (USB).
Theft (including the computer, paper documents).
Sabotage or vandalism
Access to facilities, tools, and resources without authorization (for example intruder in
case of espionage).
What Are Virtual Attacks?
A Virtual attack is an attempt to take control of computers, steal data, or use a computer system that
has been compromised to launch other attacks. Malware, phishing, ransomware, man-in-the-middle
attacks, and other tactics are used by cybercriminals to launch cyberattacks.
20
E123262 – Fudhail Faizal – Security Assignment 01
Natural Disasters
Businesses must prioritize practical cybersecurity more highly in order to protect their resources
and workforce. Mortality from natural disasters has dropped by about three times.
However, there are still problems with the current system that delay the staff's ability to quickly
receive these alert messages and make preparations.
Social Engineering
Manipulation of employees is the cornerstone of social engineering strategies. Hackers
frequently imitate others using information that con artists have amassed. One of the most
common forms of social engineering is the "coffee trick"—screening an office door while holding
a cup of coffee in each hand.
Tailgating
Tailgating is the practice of accompanying an assignee into a secure area when they have not
been invited to do so. Tailgating is the practice of having multiple people pass through the doors
at once while only the person in front of you needs to present an ID card or magnetic card. It is
simple for outsiders to enter because people simply follow visitors after them.
Purchasing office doors that can withstand a break-in is a smart move if you want to move to a
new place of business. Installations may be expensive but are worthwhile if a business decides
not to be monitored once people leave the current facility.
Documental Theft
Confidential documents can easily vanish and wind up in the wrong hands.
If they aren't removed from the workplace, visitors may occasionally disclose information that
the company would prefer someone not specifically see.
Implementing a clean space policy is one of the best ways to ensure that your employees' papers
are kept securely. Make sure that any personal documents the staff members have that are no
longer needed are destroyed. When there is a clear workstation policy in place, important
information is less likely to be left in dangerous places.
File Sharing
Sharing private information through folder applications makes it more likely that it will be
intercepted or used improperly. The loss of crucial corporate data can lead to security incidents
such as data leaks, information theft, and malware attacks, to name a few.
Phishing Attacks
21
E123262 – Fudhail Faizal – Security Assignment 01
Phishing attacks take place when a perpetrator poses as a trustworthy source and persuades the
victim to download malware, open a malicious attachment, or divulge personal information.
Phishing is to blame for 90% of data breaches that organizations experience and for up to $12
billion in losses to companies.
Phishing attacks have become significantly more sophisticated in recent years. Phishing attacks
can be technologically thwarted, though.
1.3 Security Procedure to minimize the impact of these threats
What is a Security Procedure?
A security procedure is a predetermined flow of steps that must be taken in order to carry out a
particular security task or function. In order to achieve a goal, procedures are typically composed of
a series of steps that must be carried out repeatedly and consistently. Security procedures offer a set
of established actions for managing the organization's security affairs once they are put into place,
which will aid in training, process auditing, and process improvement. In order to implement the
consistency required to reduce variation in security processes and increase control of security within
22
E123262 – Fudhail Faizal – Security Assignment 01
the organization, procedures provide a starting point. Another effective strategy for cutting waste,
raising quality, and boosting productivity in the security division is to reduce variation.
Natural Disaster
In the event of bad weather, businesses must have both business continuity and recovery plans.
Advanced indicators may be used by some solutions to identify such events, alert businesses, and
efficiently connect with staff members to carry out preexisting emergency rescue plans. To protect
their employees, businesses may make advance preparations for disasters.
Social Engineering
Conducting a thorough physical security risk evaluation is the first step. The majority of risks
associated with social engineering cannot be easily avoided. It is crucial to inform the staff of the
risks associated with social engineering so that they are vigilant for any unusual activity or contacts.
Tailgating
Staff members must be urged to inform security personnel of any frequency they observe. Offering
business security training programs is yet another way to reduce monitoring.
A strict physical security protocol must be put in place, including not leaving doors open to visitors,
to increase staff knowledge.
File Exchange
In order to prevent document theft, access control must be implemented, and unauthorized people
must be prevented from entering the business.
Phishing Attacks
By using a strong email security gateway, phishing emails can be stopped before they reach the
inboxes of company employees. Cloud-based email security providers like IRONSCALES may protect
the business.
What is a Risk, Vulnerability and a Threat?
Risk
Anything that could jeopardize the availability, confidentiality, or integrity of sensitive data.
This could involve threats to physical records, digital assets, servers, and systems, as well as
incidents involving the loss, theft, or temporary inaccessibility of information.
Although that is a good general summary, the reality is more complex than that, and complexity is
crucial if you want to adequately address information security risks.
The adverse consequences that result from a threat to the confidentiality, integrity, or availability of
information are a more accurate definition of information security risk.
23
E123262 – Fudhail Faizal – Security Assignment 01
We need to examine risk in the context of the trifecta that also includes threats and vulnerabilities in
order to comprehend why that is the case.
Vulnerability
An exploitable flaw known as a vulnerability can be used to compromise or harm sensitive data
These frequently involve software bugs and how malicious hackers can use them to perform
functions they weren't designed for. Inherent human flaws like our susceptibility to phishing scams
or the likelihood that we'll misplace a sensitive file are also examples of physical vulnerabilities.
In a nutshell, vulnerabilities are the ways in which data security can be undermined.
Threat
When an actor takes advantage of or is a victim of a vulnerability, a threat occurs. In light of the
aforementioned examples, threats could consist of a hacker using a software bug to his or her
advantage or a fake email to trick a worker.
Threats are, in other words, the behaviors that lead to the compromise of information.
Information security risks are the results of a threat using a vulnerability, which you reach at the
end.
When a hacker preys on an employee, there is a chance that they will gain access to the employee's
work account and steal private data. This may lead to monetary losses, privacy invasion, harm to
one's reputation, and regulatory action.
Activity 2
2.1 What is a Firewall?
It serves as a network security device. It keeps track of incoming and outgoing network traffic to
decide whether to permit or block data packets in accordance with its security policies.
Its goal is to establish a barrier between traffic coming into your internal network and traffic coming
from outside sources, such as the rest of the internet. This prevents traffic from hackers, viruses, and
other bad actors.
In order to shield your network from attacks, there are pre-set rules to analyze and filter traffic,
rerouting data that originates from dubious or unsecure sources.
Your website is protected by firewalls from the following:
Hackers who use brute force techniques to try hundreds of username and password
combinations in an effort to find your login information.
24
E123262 – Fudhail Faizal – Security Assignment 01
DDoS attacks: An attempt to bring down your website by flooding servers with
thousands (or even millions) of fictitious packets.
Unauthorized users who attempt to access your computer or server are known as
intrusions.
Attackers who aim to infect your server or device with malware, which can damage your
computer, steal your personal information, and even spread to other devices.
Types of Firewalls
Software Firewall
This kind of firewall is a computer program that you install. It will control traffic through ports and
applications to manage users, create logs, and block applications, among other functions.
Hardware Firewall
Between the gateway and your network is actual hardware that serves as this type of physical
firewall. A hardware firewall is something like your router, though there are more specialized
devices for more extensive uses.
Packet Filtering Firewalls
Data that travels between your computer and a server is contained in packets. When you visit a
website and load a web page, the server sends a packet to your computer, just as it does when you
send an email, upload a file, or click a link.
Packet-filtering firewalls examine packets (specifically the designation and source IP addresses) and
prevent packets from passing through if the packets don't match the pre-set rules. Therefore, in
order to protect you, your computer won't load a website that has been reported to be malicious.
Even though next-generation firewalls (which we'll discuss next) are more effective, this type of
firewall is still not the most popular. Because the firewall only scans the request itself and not its
contents, it can very well allow a malicious request from a source it trusts to pass through, limiting
the protection provided.
Use a different, more sophisticated type of firewall in addition to your current packet-filtering
firewall, at the very least. However, if you're using a more recent firewall, you probably won't need
to do this since it should already come with this kind of security.
Next Generation Firewalls
The protection of your device and network is much better provided by next-generation firewalls, or
NGFWs. What these firewalls offer is as follows:
- monitoring of antivirus applications
- In-depth packet analysis
- traffic inspection with encryption
- prevention of intrusion
25
E123262 – Fudhail Faizal – Security Assignment 01
To make sure nothing malicious is attempting to get through, the request's data, not just the request
itself, is inspected.
Proxy Firewalls
A proxy firewall serves as a bridge between end systems, filtering traffic at the application level. The
firewall receives a request from the client, which is then evaluated in light of the security policies
and either approved or rejected. The most common use of proxy firewalls is to track traffic for layer
protocols (FTP and HTTP, for example).
Network Address Translation Firewalls
Network Address Translation Firewalls, also known as NATs, enable multiple devices with unique
network addresses to connect to the internet using a single IP address while maintaining the privacy
of the individual IP addresses. This prevents an attacker from learning information about every
online device when they scan a network for IP addresses. Similar to how proxy firewalls work, NATs
act as a bridge between traffic and a collection of computers.
Stateful Multilayer Inspection Firewall
Firewalls that perform stateful multilayer inspection, also known as stateful firewalls or SMLIs, filter
packets at the application, network, and transport layers. Each packet is thoroughly examined, and if
it complies with the security requirements, it is only permitted to pass through each layer one at a
time. Stateful firewalls also identify patterns, making it simpler to block unauthorized traffic.
Contrary to packet-filtering firewalls, which are sometimes referred to as "stateless," this technology
maintains state. The fact that stateful firewalls store and analyze so much more packet data makes
them more demanding on your device.
What is a VPN
Virtual private networks, or VPNs, are among the best tools for protecting your online privacy. When
you browse, shop, or conduct online banking, a VPN encrypts your connection and keeps you
anonymous.
Microsoft created the virtual private network for the first time in 1996 so that remote workers could
safely access the company's internal network. Once it doubled business productivity, other
businesses started implementing the strategy. Corporate VPNs that enable remote work are now a
common sight in the world of business.
Then, developers understood that the average person could use this safe "tunnel" to safely connect
to the world wide web, the largest network on the planet. In the consumer sector, VPNs are now the
pillar of online privacy.
What does a VPN Do?
A VPN first routes your traffic through a VPN server before sending your internet traffic—such as
your online searches, uploads, and downloads—directly to your Internet Service Provider (ISP). In
this manner, your data appears to have originated from the VPN server and not your personal device
when it is finally transmitted to the internet.
26
E123262 – Fudhail Faizal – Security Assignment 01
Without a VPN, the internet can see your IP address, a distinctive number specific to your home
network. By serving as an intermediary and rerouting your traffic, a VPN hides your IP address. As
you connect, it also adds encryption, or a tunnel around your identity. The combination of the VPN
server and the encryption tunnel blocks your ISP, governments, hackers, and anyone else from
spying on you as you navigate the web
How EMC Cyber Will Benefit from installing a network monitoring system and How
EMC Cyber and its clients will be impacted by improper configuration.
Organizations must have a secure network infrastructure, which necessitates monitoring router,
switch, and other network device activity closely. Threats to your perimeter security, such as
unauthorized configuration changes, suspicious logon attempts, and scanning threats, must be able
to be quickly identified and investigated. For instance, if you don't promptly identify improper
changes to the configurations of your network device, your network will be open to intrusion and
even takeover by attackers.
Network Visibility
Users must be able to monitor every component of the network. which includes all of the network's
connected devices and all traffic patterns. It is the best method for keeping an eye on the network's
health and identifying performance gaps.
Simply maintaining the network's count of anything could be challenging. As part of network
monitoring, sophisticated network modeling solutions can give users an in-depth view of some of
the most complex environments.
Upholding Compliance
Businesses that need to maintain compliance must have access to the appropriate network
monitoring technologies. To comply with PCI DSS, HIPAA, FISMA, SOX, and other regulations,
network monitoring is necessary in addition to almost any distributed monitoring safeguards.
Prevent Downtime
Production is killed by costly downtime. The most recent survey found that 40% of business
organizations believed disruption could cost them between $1 million and $5 million per hour.
By monitoring, unplanned outages can be prevented. A key element of the system monitoring
systems is the detection of warning signs that could indicate a hardware failure or networking issue.
That helps troubleshoot issues and keeps businesses from experiencing interruptions.
Performance measurement gives IT teams the ability to increase efficiency for much more
productive operations in addition to preventing disruption.
Recognizing problems and solving them quickly
27
E123262 – Fudhail Faizal – Security Assignment 01
When a problem arises, network monitoring makes it easier to isolate it quickly. Network mapping
can help administrators quickly identify the problem's root cause, which could be a traffic variation,
a setup mistake, or something more serious. Networking automation tools, which are merely a part
of the surveillance system, may enable quick resolution of a number of problems.
Reduced Mean Time to Repair (MTTR) allows the IT staff to focus on other issues, which lessens the
impact of downtime or subpar network performance.
Identification of Security Threats
Network monitoring's primary objective is to monitor system stability, but it can also be used to
uncover potential risks that are concealed. By routinely looking out for odd or suspicious behavior, it
might be able to spot even the smallest dangers before they grow to be the biggest ones.
For instance, ransomware or viruses might not be immediately apparent, but the network
monitoring system may spot strange behaviors like dubious use of network resources. The initiative-
taking detection of security risks like DDoS attacks or unauthorized downloads is also conceivable.
Monitoring the Bandwidth Usage
When a company's bandwidth is overloaded, users have irate employees and customers. So can
monitor bandwidth usage to determine when things start to slow down. When bandwidth usage
reaches critical levels, one will be alerted so they can adjust any quality of service (QoS) protocols
and take other performance-improving actions.
Capacity Management
Furthermore, user demands are constantly shifting. As a result, it might be difficult to predict how
and where customers will use networking resources in the future. As demand increases, it is
essential to make plans for additional equipment and the capacity to meet this requirement.
2.2 How implementing a ‘trusted network’ will benefit EMC Cyber and its Clients
DMZs
A demilitarized zone (DMZ) is a physical or logical subnet in computer networks that isolates a local
area network (LAN) from other untrusted networks, typically the public internet. Perimeter networks
and screened subnetworks are other names for DMZs.
Any service offered to internet users should be situated in the DMZ network. There are typically
servers, resources, and services that are accessible from the outside. Web, email, domain names,
File Transfer Protocol, and proxy servers are some of the most popular of these services.
The rest of the internal LAN cannot be reached, but servers and resources in the DMZ are reachable
from the internet. This method increases the LAN's security by preventing hackers from accessing
internal servers and data from the internet directly.
28
E123262 – Fudhail Faizal – Security Assignment 01
The systems that are running services on DMZ servers are accessible to hackers and cybercriminals.
Those servers need to be reinforced so they can withstand ongoing attacks. The geographic buffer
zone that was established between North Korea and South Korea following the Korean War is where
the term "DMZ" originates.
Why are DMZs Important?
Network segmentation on the level provided by DMZs aids in the defense of internal corporate
networks. By limiting remote access to internal servers and resources, these subnetworks make it
more difficult for intruders to access the internal network. This tactic works well for both small and
large businesses.
A DMZ is used by businesses to isolate internet-facing servers and applications from the internal
network. These resources are isolated by the DMZ, making it less likely that an attack will expose
them to harm, loss, or damage.
How does a DMZ work?
DMZs serve as a buffer zone between the private network and the public internet. Between two
firewalls is where the DMZ subnet is installed. Before reaching the servers housed in the DMZ, all
incoming network packets are then screened using a firewall or another security appliance.
Threat actors who are better prepared must first get past the first firewall in order to access the
DMZ services without authorization. These systems are probably fortified against such assaults.
Finally, even if well-funded threat actors manage to take control of a system located in the DMZ,
they will first need to get past the internal firewall in order to access sensitive enterprise resources.
Even the most secure DMZ architecture can be breached by determined attackers. But when a DMZ
is attacked, alarms go off, giving security experts enough time to stop a full intrusion into their
organization.
Benefits of using a DMZ
The main advantage of a DMZ is that it keeps a barrier between users of the public internet and the
private internal network while providing them access to some secure services. This buffer offers
several security advantages, including the following:
Access Control
Services accessed from the internet but located outside of an organization's network perimeters are
controlled by a DMZ network. The amount of network segmentation that is simultaneously added
raises the barriers a user must overcome in order to access a company's private network. Some DMZ
configurations include a proxy server, which centralizes internal internet traffic (typically employee
traffic) and makes recording and monitoring that traffic easier.
Network Reconnaissance Prevention
29
E123262 – Fudhail Faizal – Security Assignment 01
An attacker is also prevented from scouting out potential targets on the network by a DMZ. The
internal firewall safeguards the private network, keeping it separate from the DMZ even if one of the
DMZ's systems is compromised. Active external reconnaissance is made more challenging by this
configuration. Although the servers in the DMZ are visible to the public, they are supported by an
additional level of security. The internal private network's data is hidden from attackers by the
DMZ's visible surface. Even if hackers are able to take control of the DMZ's servers, they are still cut
off from the private network by the internal DMZ barrier.
Protection Against IP Spoofing
Attackers occasionally try to get around access control limitations by spoofing an authorized IP
address in order to pass as another network device. While another service on the network confirms
the legitimacy of the IP address by determining whether it is reachable, a DMZ can stop potential IP
spoofers.
What Are DMZs used for?
For nearly as long as firewalls have been in use, DMZ networks have played a significant role in
enterprise network security. They are used for similar purposes: to safeguard delicate organizational
resources and systems. The following are frequent applications for DMZ networks:
Reduce and manage external users' access to potential target systems by isolating and keeping them
apart from internal networks, hosting corporate resources so that some of them are accessible to
authorized external users, and so on.
Enterprises have more recently chosen to use virtual machines or containers to isolate particular
applications or portions of the network from the rest of the corporate environment. Many
businesses no longer need to have internal web servers thanks to cloud computing. most of the
infrastructure that faces the outside once located in the enterprise DMZ has migrated to the cloud,
such as software-as-a service apps.
Static IP
A computer's static IP address is a 32-bit number that serves as its internet address. Usually, an
internet service provider will provide this number, which looks like a dotted quad (ISP).
An internet-connected device's IP address, or "internet protocol address," serves as a special
identification number. Similar to how people use phone numbers to locate and communicate with
one another on the phone, computers use IP addresses to locate and communicate with one
another online. An IP address can reveal details about the hosting company and location
information.
As an illustration, when a user tries to access WhatIs.com, their computer queries a domain name
system (DNS) server, which is comparable to a telephone information operator, for the right dotted
quad number. An IP address is required to uniquely identify a device with a network protocol, and
the DNS maps the domain name to the IP address. Your computer uses the response it receives to
connect to the WhatIs.com server in this scenario. The DNS server links the quad number, which is
similar to a phone number.
30
E123262 – Fudhail Faizal – Security Assignment 01
How Static IPs work
If a person or organization wants a static IP address, they must first call their ISP and ask them to
give their device — such as a router, for example — a static IP address. Static IP addresses are not
typically provided by most ISP companies by default. They will need to restart their device once it is
configured with a new, permanent IP address. The same IP address will be used by computers and
other hardware behind the router. Once the IP address is set up, it doesn't need to be managed
because it stays the same.
However, there is a cap on the number of static IP addresses that can be requested, so doing so
frequently results in a fee. To circumvent this problem, consider using IPv6. Since there are many
more IP addresses available thanks to IPv6's lengthening of IP addresses from 32 bits to 128 bits (16
bytes), static IP addresses are now simpler and less expensive to acquire and maintain. Although a
sizable portion of internet traffic still uses IPv4, IPv6 is increasingly being used, so both are still in use
today.
Up to 340 undecillion different IP addresses can be used with IPv6. To put that into perspective,
there are currently 340 trillion, trillion, trillion unique IP addresses that can be assigned, which is 340
followed by a total of 36 zeros. This increase in the total number of IP addresses enables significant
future expansion of the internet and alleviates what was anticipated to be a future shortage of
network addresses.
Advantages To Static IPs
Businesses can have a single, static address if they use IP addresses for mail, FTP, and
web servers.
Games, VPNs, and voice over IP services should all be hosted on static IP addresses
In the event of a connectivity outage, they may be more stable, preventing the loss of
packet exchanges.
They enable faster file uploads and downloads on file servers.
Any geolocation service will find it simpler to access a device's location if it has a static
IP.
For remote access to a computer, static IPs work better.
It is not necessary for a device with a static IP address to send renewal requests.
When servers are running, network administrators may find it easier to maintain static
IP addresses.
And tracking internet traffic is simpler for administrators, assigning access to users
based on their IP addresses.
Disadvantages to Static IPs
31
E123262 – Fudhail Faizal – Security Assignment 01
The number of IP addresses is restricted. Even when the device is turned off and not in
use, a static IP address assigned to a device or website is occupied until otherwise noted.
Nowadays, most people do not require a static IP address.
A static IP address is more vulnerable to hackers or follow-up attacks because it is
constant and difficult to change.
Manually configuring a static IP can be challenging.
If an old static IP device becomes unusable, it might be challenging to transfer server
settings to a new one.
It is simpler to track devices with a static IP address.
Because an ISP typically requires static IP users to sign up for a commercial account and
pay one-time fees, static IPs are more expensive. The cost of internet service may
increase monthly as well.
Implementing router firewalls, utilizing a VPN, or utilizing an internet security suite can
all be used to address security issues with both static and dynamic IP addresses.
Although they cannot completely ensure security, these can be an immense help.
NAT
A single IP address space can be transformed into a global one using the NAT (Network Address
Translation) process. This functions with a firewall or router that connects two networks. With the
aid of a single public address, we are able to connect numerous network address translations into an
intranet. The main purpose of this method's introduction is to avoid address space exhaustion.
Because they wanted multiple devices to share a single IP address, many organizations used NAT. It
addresses translation and doubles the security of its features in networking systems. We will benefit
from it in some situations, while others won't.
Benefits of a NAT
You can obtain the private IP address using it.
By dividing the internal network from the external network, it has strong security
features that improve the security of private networks.
It aids in IP address space conservation. A small IP address can be used to connect a
large number of hosts to the worldwide internet.
2.3 Tools to improve network and security performance
SolarWinds Network Performance Monitor
32
E123262 – Fudhail Faizal – Security Assignment 01
You can view and analyze the performance, traffic, and configuration details of your network devices
using SolarWinds Network Performance Monitor (NPM). NPM is made to gather data from
environments that are cross-hybrid, hosted in the cloud, or on-premises. Diagnose and fix problems
across your network quickly to reduce downtime and solve issues without interfering with normal
business operations.
Automated maps that visualize network traffic patterns are supported by NPM, allowing you to find
performance metrics and potential problems. NPM is able to produce intelligent maps of intricate IT
infrastructures utilizing Cisco ACI, Microsoft Azure, and Nexus systems.
When using NPM as your network monitor, you can enable customizable alerts, allowing you to
produce alerts based on general or specific trigger conditions. These alerts are intended to keep the
appropriate team members informed of important network metrics, reducing the amount of time
needed for problem diagnosis and repair. For deeper discoveries, reports can also be produced.
With SolarWinds NPM, you can more quickly identify and treat serious network problems and
implement smarter management.
ManageEngine OpManager
ManageEngine OpManager is made to keep track of network devices, gather important performance
metrics, and then find important trends and patterns in network performance. This information
might consist of errors, discards, CPU and memory storage, DB count, and disk utilization.
OpManager supports SNMP monitoring and can receive syslogs, traps, and additional network data.
OpManager is designed to automatically identify network devices and then logically and clearly map
them. Through OpManager, you can program automatic network discovery; on custom
ManageEngine dashboards, you can view scheduled and on-demand network maps.
Use this ManageEngine feature to track, examine, and resolve current and potential network issues.
DataDog Network Performance Monitoring
A network topology diagram can be created using the cloud-based tool Datadog after discovering
network devices and their connections. Use this map to quickly identify data changes and
inconsistencies.
The Datadog network performance management tool also lets you capture packets, view real-time
device statuses, and perform utility analysis. Datadog has auto-discovery features that create device
inventories and create indexes of your most important tasks. These are made to automatically adapt
to changes in the network, keeping you current.
You can store traffic for historical analysis on a cloud server with Datadog. This could allow you to
look into the underlying causes of issues after they have been fixed and help guide the application of
preventative measures. You can also create alerts with Datadog based on automatically updated
thresholds which are automatically collected and adjusted through machine learning.
33
E123262 – Fudhail Faizal – Security Assignment 01
Paessler PRTG Network Monitor
Paessler PRTG is cutting-edge network performance management software made to gather network
data from all of your network's gadgets, systems, and programs. PRTG is designed to present this
data in a hierarchical view for the highest level of organization.
Use the PRTG map designer to create detailed visualizations that integrate every network
component for in-depth analysis. These visualizations come in the form of graphs, lists, charts, and
more, all with distinguishable icons. Without additional plug-ins, PRTG is made to support these
visuals in their entirety.
Through PRTG, you can enable alerts and push notifications for continuous insight. To make network
performance management and collaboration easier, PRTG also supports comprehensive reports that
you can schedule, run on-demand, or export as PDF or HTML documents, among other formats.
Progress WhatsUp Gold
Progress WhatsUp Gold is made to use SNMP to monitor important metrics. The WhatsUp Gold
network performance management tool gathers status reports or MIBs to learn about the devices
and connections that are currently present in your network. You can maintain a completely accurate
view of network performance thanks to the constant updating of this information.
Device dependencies are automatically discovered and displayed by WhatsUp Gold on unified
dashboards. Use this data to visualize your IT environment, find and fix problems, and foresee
potential issues in the future. Topology maps are useful for important tasks like creating SLA action
policies.
With WhatsUp Gold, which sends trap messages when issues are discovered or when a device's
status changes, real-time alerts can be produced. These notifications are made to be sent straight to
the appropriate IT administrator for immediate response and action.
GFi Kerio Control
A smart Next-Generation Firewall (NGFW) called GFI KerioControl keeps a close eye on your
networks for malware, viruses, and other threats. For small and medium-sized businesses, it is a
complete yet cost-effective solution.
The network security solution from KerioControl inspects each packet of data that enters and leaves
your network. In order to detect any deviations from the established traffic rules, it compares the
packets and raises alerts.
Using content, application, and URL filtering, KerioControl also recognizes threats and prevents them
from accessing your network. Additionally, its cutting-edge VPN technology secures your office
connections quickly using industry-standard VPN protocols.
The data flow in your network is something you can continuously watch over and manage. This
network security tool, in particular, guards against bandwidth hogging and supports internet load
balancing for continuous productivity.
34
E123262 – Fudhail Faizal – Security Assignment 01
As an added bonus, you can use the user-friendly dashboard to manage or restrict access to more
than 100 applications.
GFI KerioControl is a sophisticated and cutting-edge network security program overall. It keeps an
eye on your network and gives you visibility and command over it. Additionally, you can create
network status reports using templates that come pre-built. Additionally, it guarantees adherence to
industry standards.
Zscaler Cloud Firewall
Zscaler Cloud Firewall examines both web and non-web traffic on your network to provide
comprehensive support and security for your vital assets.
All of the devices, applications, and users in your network are secured using the cloud-native
Security Service Edge (SSE) platform. It is quick, greatly scalable, flexible, and dependable.
Additionally, if your company encourages remote working, you'll find it appropriate.
The zero-trust approach to security that Zscaler Cloud Firewall takes is a standout feature. Before
accessing the network, each device and user must authenticate themselves. Predetermined access
controls are also necessary for access.
Zscaler doesn't require a complicated setup because it is cloud-delivered. The always-on feature also
shields your system from malicious data packets and users.
Furthermore, it has dashboard updates and real-time notifications to give your IT team complete
visibility and control.
When it comes to protecting your network and the assets on it, Zscaler performs consistently.
CrowdStrike Falcon
End-to-end security is handled by CrowdStrike Falcon, an endpoint identity protection platform.
It is a comprehensive platform that keeps an eye on user activity, endpoint activity, and your
network to spot threats before they affect your data center.
Therefore, if a vulnerability is found, Falcon offers simple, effective, and quick solutions to address
the problem.
CrowdStrike Falcon's additional modules for dealing with particular security issues, like mobile
endpoint protection, automated malware analysis, etc., are a standout feature. These modules can
be added based on your security requirements.
In general, CrowdStrike is a scalable and adaptable platform for network and endpoint monitoring.
35
E123262 – Fudhail Faizal – Security Assignment 01
OSSEC
OSSEC is a reliable Host Intrusion Detection System (HIDS) that runs smoothly on Windows, Solaris,
macOS, and Linux. It is free and open-source.
Numerous monitoring and analytics tasks, including log analysis, Windows registry monitoring,
automated threat remediation, and other security operations, are carried out by it.
The biggest benefit of OSSEC is that it can be tailored to fit the needs of your business. Additionally,
it aids businesses in adhering to rules like the PCI DSS.
If you're looking for a unique network monitoring solution, OSSEC is a good option. For businesses
that can benefit from its customization, it's also a better option.
The essential features outlined earlier are present in all of the tools mentioned in the article. The
needs of your organization should therefore come first when selecting one of these.
Activity 3
3.1 Enterprise Risk Management Procedures (ERM)
Procedures and resources for enterprise risk management
The term "Enterprise Risk Management" (ERM) is used in business to refer to risk management
techniques used by organizations to identify and reduce risks that could negatively impact the
enterprise. What are the main risks that could prevent us from completing the mission, is the
straightforward question that ERM practitioners try to answer.
The JLA research team examined the risk types of 76 S&P 500 companies in 2004 where there had
been a market value decline of 30% or more. They discovered that strategic risks accounted for 61%
of incidents, operational risks for 30%, and financial risks for 9%.
Risks that pose a significant threat to life, health, or property are referred to as hazard
risks.
Risks that are directly related to money are referred to as financial risks. They include
monetary repercussions like rising expenses or declining revenues.
36
E123262 – Fudhail Faizal – Security Assignment 01
Risks associated with or produced by strategic business decisions are referred to as
strategic risks.
Risks that materially impact an organization are referred to as operational risks.
Risk Response Strategies for Enterprise Risk Management
To address the risks they have identified, management chooses one of the five appropriate risk
response strategies listed below:
Eliminating risks or actions that could negatively affect an organization's assets is known
as risk avoidance. An example would be the suspension or cancellation of a planned
production or product line.
Risk mitigation or loss severity limitation is the reduction of risk. For instance,
management can schedule frequent visits to their key suppliers to spot potential issues
before they arise.
Alternative course of action: Considering additional potential risk-reduction measures.
Transferring risks to third parties, such as insurance companies, is referred to as sharing
or insuring. Purchasing, for instance, an insurance policy that would protect the
company from any unforeseen loss
Acceptance of risk: The recognition of the risks that have been identified and the
readiness to accept their effects. Typically, risk acceptance is defined as any loss
resulting from a risk that is not covered or avoided.
Core Elements of an ERM Process
To ensure financial security for businesses, ERM employs a very clear and continuous process that
actively identifies and reassesses the various strategic and major risks. There are five distinct
components to the process:
Understanding the business's strategies and associated risks is a strategy/objective
setting.
Identify the key risks that could have a negative impact on the company's overall
financial health.
Risk assessment: Identified risks are thoroughly examined to ascertain their potential
as well as likelihood.
37
E123262 – Fudhail Faizal – Security Assignment 01
Risk response: Take into account different risk response strategies and pick the best
course of action to match identified risks with management's risk tolerance.
Communication and monitoring: It is crucial to continuously monitor and
communicate pertinent data and information to all levels of a department.
Enterprise Risk Management Process
Consider Tesla, a publicly traded company that primarily operates in the automotive and
energy generation sectors. During the strategy/objective setting in this example, ERM
will start by taking into account the factors that contribute to the company's value. The
competitive advantage of Tesla, new strategic initiatives, important product lines, or an
acquisition are a few examples.
Risk evaluation: The ERM process will start the risk identification process after the key
drivers have been identified by assessing pertinent risks that could potentially impede
the success of each key driver.
Risk assessment: The risks must then be carefully examined from multiple departments'
perspectives.
Executives will think about the best risk response strategy after upper management has
finished discussing and acknowledging the potential risks.
Finally, upper management will use any key risk indicators deemed useful by that
organization to measure, monitor, and communicate the effectiveness of the risk
response strategies.
Impact of an IT security Audit
What is an IT audit?
A thorough evaluation of an organization's IT infrastructure and security posture is known as an IT
security audit. Organizations can identify and evaluate the vulnerabilities present in their IT
networks, connected devices, and applications by conducting an IT security audit. You have the
chance to achieve compliance and close security gaps.
Among these are measures like vulnerability scans, which look for security gaps in IT systems. or
running penetration tests to gain unapproved access to the networks, systems, and applications.
Finally, the organization receives the penetration testing reports created after carrying out all
required steps for further analysis and action.
38
E123262 – Fudhail Faizal – Security Assignment 01
The physical component is also included in an IT security audit. The auditor checks the physical
hardware access to make sure it complies with security and other administrative requirements.
Organizations can benefit from performing an IT security audit by receiving information about the
risks related to their IT networks. Finding security gaps and potential weaknesses in their system can
also be aided by it. preventing hackers from accessing them by promptly applying patches.
Benefits of IT security audit
An IT security audit identifies hidden security risks and vulnerabilities in an organization's IT assets.
However, identifying risks has a positive knock-on effect that improves the organization's overall
security. How? Here is a breakdown of each one:
evaluates your current security setup and protocols, and uses the audit findings to
help you set a standard for your business.
reduces hacker risks by early detection of security holes and possible hacker entry
points.
enables you to comply with regulations by confirming that your IT infrastructure
complies with the highest regulatory bodies.
helps you make well-informed decisions for the improvement of your organization's
security awareness and training by identifying gaps in these areas.
Importance of an IT Security Audit
a security audit of IT systems is crucial
protects an organization's vital data resources.
maintains the organization's compliance with different security certifications.
discovers security flaws before hackers do.
updates the organization on security precautions.
determines the weak points in the physical security.
helps the organization create new security policies.
enables the organization to be ready to act quickly in the event of a cybersecurity
breach.
How IT security can be aligned with organizational IT Policies
Anyone handling or using an organization's IT assets and services must adhere to the security
policy's outlined policies and procedures. So why are IT security protocols required? Such network
security protocols aim to address potential risks and strategies to lessen IT security weaknesses, as
well as ways to recover from a cyberattack. Rules also provide guidelines for what employees should
39
E123262 – Fudhail Faizal – Security Assignment 01
do and should not do. Rules outline who has access to what information and what happens if they
are broken. Regardless of its size, every company should have formal IT security policies in place to
protect its data and other crucial assets.
How misalignment of such a policy can impact an organization’s security.
Impacts of not having a Disaster Recovery Plan
Complete Loss of Data
Data is essential in a time when most businesses rely heavily on their information technology
infrastructure. Organizations can lose their data in an infinite number of ways, such as through a
natural disaster, human error, security breaches, etc. No company is immune to all these situations;
in 2019, 42% of companies experienced data loss. Up to 72% of businesses that experience a major
data loss shut down permanently within 24 months, according to a study by the Diffusion Group.
According to a related study by the British Chambers of Commerce, 93% of businesses that have lost
access to their data for more than 10 days declare bankruptcy within a year, while 50% do so right
away. Even for companies that don't do not close down, the loss of data triggers a snowball effect
that typically would cost a lot depending on the size and type of operation.
Business Interruption
You are losing money whenever your company is not operating to its full potential. Along with losing
money, you also lose productivity from the workforce. You will lose money and employee
productivity if your company does not have a disaster recovery plan to enable a prompt return to
normal operations, in the same location or elsewhere, in the event of any disaster, no matter how
minor. A disaster recovery plan gives organizations a seamless and coordinated way to handle any
type of disaster so that business can resume or go on as usual in the shortest amount of time.
Loss of clients
Information security is more widely understood than ever before. Your customers will want to know
where their information has gone, even though they may be understanding and unmoved by the fact
that you had a data breach. They will also inquire about your return to regular business hours.
Customers trust you because you assist them in fulfilling their needs. They won't want to hear that
you can't fulfill their requirements or that you have to start from scratch.
As a result, the majority of clients will want to know in advance that you have painstakingly created
a disaster recovery strategy that ensures you will continue to provide your services. Customers will
gravitate toward businesses that can ensure their continued service and information security.
Damaged Reputation
40
E123262 – Fudhail Faizal – Security Assignment 01
A company's reputation can be enhanced or damaged depending on how it responds to a crisis. Even
years after the initial disaster, poor disaster management can still have a significant and long-lasting
effect. Real-world examples of this include the Volkswagen emissions scandal and allegations of
fraudulent customer accounts at Wells Fargo. The initial harm caused by inadequate disaster
management was a major stain on these organizations' reputations for a while, even though they
later made up for their earlier errors. Any organization can experience such events, and failing to
have a proper response plan can negatively affect your finances, drive away qualified candidates,
jeopardize future investments, and obstruct other opportunities.
Business Failure
An organization could be completely taken over by a significant and widespread disruption in its
technology infrastructure. Unfortunately, no organization is impervious to such a catastrophic
disruption, no matter how tech-savvy or secure. However, an organization can survive a catastrophic
disaster with a proper disaster recovery plan that includes steps like data backup and a secondary
data center. It's also critical to remember that a company does not necessarily fail if it lacks a DRP.
Records can be recovered, rebuilt, and recreated. The underlying assumption is that the vast
majority of institutional knowledge, including processes, that keeps a business productive over time
is stored electronically. It could take a company months or even years to recover its institutional
knowledge and return to its prior state of productivity. Some companies don't have the luxury of
performing below their potential, which is why they fail.
Impact of Improper Audit Control
-Signs
Internal controls were first defined by the American Institute of Accountants in 1949. Internal checks
and balances make sure that authorized transactions are carried out, recorded, accessed, and
examined. Employees perform job duties in a setting where personal safety is not guaranteed when
a company runs without an efficient system of internal controls. High levels of employee
dissatisfaction, absenteeism, and low levels of employee retention result from this. Then, employers
regularly spend needless time and energy on hiring, training, and conducting interviews for new
hires. Business partners and stakeholders, such as investors, frequently cast doubt on the accuracy
of financial records and managerial reports. When a business violates laws, regulations, and other
requirements, it damages its reputation and may even face legal action.
-Symptoms
When a business appears to be operated without regard for internal controls, customers take notice.
High customer dissatisfaction rates, weak sales, and a lack of profitable business alliances reveal a
company that lacks focus and direction. Poor business practices and ineffective management are
generally shown by waste, inefficient resource use, poor management decisions, high rates of
product errors, loss of records, carelessness, and errors.
-Results
Lack of internal controls frequently makes it impossible to compare performance to plans, forecasts,
and budgets. Privacy issues result from a lack of attention to information security. Security breaches
41
E123262 – Fudhail Faizal – Security Assignment 01
and compromised accounts occur as a result of unauthorized access to sensitive information
contained in customer and financial records. Employee asset theft or misappropriation, which may
involve record-keeping fraud, is included in illegal transactions. Employees may accept bribes in
order to cover up theft.
-Remedies
A business can lessen the negative effects of prior internal control deficiencies by implementing a
thorough set of policies and procedures. Transactions are carried out in a trustworthy manner by
holding each employee accountable for moral conduct, high standards for business conduct, and
adherence to the law. Errors, irregularities, and fraud can be avoided by making sure that only
competent, dependable, trained personnel perform tasks. Monitoring and upkeep of internal control
systems are required. Compliance with internal and governmental regulations is ensured by
independent audits.
How can potential Data Loss impact an organization
Data loss is a serious inconvenience that prevents any information-based business from operating
normally on a daily basis. Your company must spend time and money recreating or recovering these
files when crucial files and documents are lost in order to fill the gaps left by the loss. While you
might be able to find hard copies of the information, they might not be as current as the lost digital
copies. Data loss brought on by viruses or corruption presents particular challenges because it's not
always easy to gauge the full extent of the damage. Your company may have to spend money
repairing and removing damaged files.
When data loss is accompanied by security breaches, productivity timelines are also pushed back
and you risk losing customers. Your business must notify customers when sensitive data is lost or
compromised, costing you their trust and respect. Even if your business is able to bounce back from
the data loss, you will need to spend time mending fences with customers.
When a significant amount of data is lost, the inconvenience can have even greater effects on your
business:
94% of businesses that suffer severe data loss fail to recover.
Within two years of the data loss, 51% of these businesses shut down.
43 percent of these businesses close their doors permanently.
70 percent of small businesses fail within a year of a significant data loss incident.
The average cost of a data breach to a U.S. company, according to an IBM study, was $8.6 million,
the highest cost in the world. Leaving data unprotected is a costly risk to take. The same study
discovered that locating and containing a data breach could take 280 days, or more than nine
months.
42
E123262 – Fudhail Faizal – Security Assignment 01
Impact of Computer Misuse
Computer-related injuries result from misuse of computers. Office workers who frequently use
computers are reported to have a high incidence of computer-related injuries (CRIs). This study aims
to determine the prevalence of computer-related accidents in a workplace where computers are
used by the majority of workers. In this study, 120 office workers were chosen at random to
participate in a survey. Distributing a self-administered survey was used to gather the data. The
findings indicated that office workers suffered from musculoskeletal disorders like neck, shoulder,
and waist pain as well as computer-related injuries like computer vision syndrome (eye strain,
blurred vision, watery eyes, and headache). It is strongly advised that the organization conduct
routine ergonomic training by the organization to reduce the incidence of CRIs among office
personnel.
3.2 Mandatory Data Protection laws and Procedures
Data protection necessitates a comprehensive approach to system design that combines a range of
legal, administrative, and technical safeguards, as discussed in Section III. Privacy & Security. To
begin with, legal frameworks that protect user rights, personal information, and privacy should serve
as the foundation for ID systems. The ID system and other government or private-sector initiatives
that process personal data are covered by general data protection and privacy laws that many
nations have adopted. These laws typically include broad provisions and principles specific to the
gathering, storing, and use of personal information, in accordance with international standards on
privacy and data protection such as:
Purpose Limitation
Personal data should only be collected and used for the following reasons: (1) those that are
permitted by law and thus should, in theory, be known to the data subject at the time of collection;
or (2) those that the data subject has authorized.
Proportionality and minimization
To prevent unneeded data collection and "function creep," both of which can pose privacy risks, the
data collected must be in proportion to the goal of the ID system. This is frequently stated as
necessitating the collection of "minimum necessary" data, which includes transaction metadata, in
order to achieve the desired results.
Lawfulness
43
E123262 – Fudhail Faizal – Security Assignment 01
Personal data should only be collected and used on the basis of legal justifications, such as consent,
contractual necessity, legal compliance, protection of vital interests, public interest, and/or
legitimate interest.
Fairness and Transparency
Personal information should be gathered and used fairly and openly.
Accuracy
Personal information must be current and accurate, and any errors must be quickly fixed.
Storage Limitations
Transaction metadata should not be retained for any longer than is required to fulfill the purposes
for which it was collected and processed. People may be given a choice regarding the retention
period for transaction metadata.
Privacy-enhancing technologies (PETs)
Requirements to use privacy-protecting technologies, such as the tokenization of unique identity
numbers, which reduce or eliminate the collection of personal data, stop it from being processed
inadvertently or unnecessarily, and make it easier to comply with data protection laws.
Accountability
An appropriate, independent oversight authority and the data subjects themselves should keep an
eye on how their personal information is processed in accordance with the aforementioned
principles.
ISO 31000
What Are ISO standards
The International Standards Organization is referred to as ISO. They are an independent organization
made up of a vast network of people with a variety of specialties. This enables them to combine and
share their experience and expertise across a variety of fields to identify best practices and crucial
safety information to define the best way to complete particular tasks or processes.
In essence, an ISO standard is a procedure that is accepted around the world. It implies that
everyone adheres to the same set of rules regardless of where they are based, producing a safer,
more reliable outcome. Both the business and the client, or end user, win from this. Companies can
feel secure knowing that this standard is upheld and respected worldwide. For customers, they
know they are getting a product or service which is safe, good quality and trustworthy
What is ISO 31000?
The International Organization for Standardization's ISO 31000 Risk Management Framework is a
global standard that offers organizations principles and guidelines for risk management. Initiatives to
ensure compliance with regulations are typically applicable to businesses of a certain size or those
44
E123262 – Fudhail Faizal – Security Assignment 01
operating in a particular industry and are country-specific. However, ISO 31000 is created to be
applied in any size of organization. Its ideas are applicable to both the public and private sectors, as
well as nonprofit organizations and businesses of all sizes.
Framework and rules of ISO 31000
There are six key components that make up the risk management framework:
Leadership. To ensure that ISO 31000 is adopted and used in a way that is consistent
with the organization's culture and business goals, leaders within the organization must
take the initiative
Integration. While it is crucial to incorporate risk reduction into as many organizational
processes as possible, it is equally crucial to avoid creating operational snags or
impeding the execution of crucial business operations.
Design. Based on their needs, organizations will need to create a risk management
strategy that works for them.
Implementation: During this phase, business procedures are integrated with the
organization's risk management strategy. Implementation is frequently a formal process
with predetermined goals, due dates, and reporting obligations.
Evaluation. The design is evaluated to see what is effective and what might need to be
improved.
Improvement. Organizations should always be looking for ways to implement ISO 31000
more effectively.
Benefits of ISO 31000 standard
effective results. Numerous organizations use ISO 31000 because it is a globally
acknowledged standard. This indicates that ISO 31000 has undergone extensive testing
and been shown to be efficient.
less risk of legal action. Organizations may be able to lessen their legal exposure and the
risks associated with litigation by identifying key drivers.
Consider risks using a standardized approach. When properly implemented, ISO 31000
can serve as a template for businesses to use when identifying the main risk factors. It
establishes risk criteria and risk management strategies in a uniform manner.
Establish a culture of risk reduction. Employees will become accustomed to the concept
of identifying and possibly mitigating risks by incorporating risk mitigation into nearly all
business processes.
Boost the company's profitability. By minimizing unneeded risks, an organization also
lessens the likelihood that related events will result in financial loss.
Make use of what is already established. One of many ISO standards is ISO 31000. The
different standards are made to cooperate, so businesses may be able to incorporate
the work they have already completed into their ISO 31000 strategy.
45
E123262 – Fudhail Faizal – Security Assignment 01
An organization may become more proactive as a result. A successful ISO 31000
implementation can assist a company in moving away from a reactive to a more
proactive approach to risk reduction.
It might make getting funding for the company easier. Banks and investors frequently
avoid taking risks. Investors may be more likely to approve an investment if they believe
that a company is committed to identifying and reducing risks.
Activity 4
4.1 Organizational Security Policy to minimize exploitation and misuses
The Acceptable Use Policy specifies how computer components should be used properly (AUP).
Unsuitable behavior that might also have criminal repercussions could compromise the network
infrastructure. A user is using a business computer improperly when they force it to browse data for
activities unrelated to their job.
Security education and awareness guidelines
Employees are required to sign a non-disclosure agreement and provide proof of completion after
completing the course. Leadership believes that users need to be instructed on the current security
policy. The strategy must address workplace upkeep, email policies, Internet connectivity
requirements, and cybersecurity definition.
Policy for Change Management
Only the modification management policy ensures the administration, approval, and tracking of
changes to something like a company's information network.
This strategy should ensure that any changes are implemented carefully to minimize any negative
effects on the clients and services.
Essential elements of change management include providing accurate and timely documentation,
ongoing oversight, and a formal and transparent procedure.
Policy For incident Response
Such a system's business continuity plan includes incident response processes.
explains a company's response to a data security issue.
The policy must include information on the incident response team, those responsible for reviewing
the strategy, as well as the procedures followed and the resources and tools used.
Policy on Remote Access
The remote access policy is designed to lessen the possibility of suffering harm from unauthorized
resource use. Every employee must receive a copy of the policy, which must address both sending
46
E123262 – Fudhail Faizal – Security Assignment 01
and receiving emails as well as access to network resources. It must also have the requirements for
VPN connectivity and data encryption.
Policy For managing and creating passwords
Passwords, which are used to validate usernames and passwords, control access to corporate data
or networks. This policy needs to address public awareness of the importance of choosing a secure
password. It really ought to include instructions for updating current passwords as well as warnings
against using old passwords again.
Policy for network security
A thorough networking security plan ensures the same confidentiality, integrity, and accessibility of
information on corporate networks.
According to the regulation, devices must make use of the appropriate hardware, software, or
procedural auditing measures. Failures in authentication attempts, logging in or out, as well as the
use of access privileges, are all instances that can be audited.
Administration of Identity Entry, Alteration and Access Authorization
Businesses must follow the Principle of Least Privilege when using access authorization (PoLP).
This explains the idea that businesses and customers should only have access to the data they need
to perform their specific tasks.
HR and Now it must consider sharing accounts, group affiliations, special rights, temporary or visitor
identities, and more.
Policy on Data Retention
The data retention policy specifies the kinds of information that a company should keep on file for
how long. Eliminating duplicate and outdated data will free up more storage space. This policy
details how long the data will be kept for and how it will be disposed of. It is essential for companies
that store sensitive information.
What is a security Policy
Senior management creates and supports policies as formal statements.
They may be system-specific, issue-specific, or organization-wide. The goals of your information
security program—information protection, risk management, and infrastructure security—should be
reflected in your organization's policies. Your policies ought to be durable and resistant to erosion,
like a solid foundation for a building.
business goals-driven and express the level of risk that senior management is willing
to take.
The intended reader will find this information simple to understand.
47
E123262 – Fudhail Faizal – Security Assignment 01
created with the intention of staying in place for a number of years, reviewed
frequently, and updated as necessary with approved changes.
Importance of a security policy
Because they safeguard an organization's physical and digital assets, security policies are crucial.
They list every resource owned by the business as well as any threats to it.
A company's physical assets, including its buildings and equipment, including computers and other IT
hardware, are protected by physical security policies. Intellectual property is shielded from
expensive occurrences like data breaches and data leaks by data security policies.
What are security standards
A set of guidelines for goods or procedures that promotes efficiency, accountability, and consistency
are known as security standards. Standards are intended to provide a repeatable method of doing
things, much like policies govern people's behavior. Utilizing written standards may be based on best
practices and compliance. This makes it possible for businesses to implement security devices with
objectivity.
Without standards, it is challenging to define the procedures for where and why security devices
ought to be installed in a consistent manner. As a result, many decisions regarding the use and
implementation of security technology are made purely on the basis of budget or in response to an
incident. From a "standard-of-care" standpoint, it is essentially impossible to defend against a
negligent security tort as a result of this reactive response. There are two requirements that need to
be met. The first is "Do we implement electronic security equipment consistently?" "Can we
articulate our position for use?" is the second. Sharing of information and best practices is also made
easier by security standards. They aid in ensuring that concepts, terms, and definitions are
understood by all, which avoids mistakes.
Standards are frequently created based on "the way we've always done it" becoming accepted
practice. Standards based on product usage aid in ensuring that installations and products are in line
with the organization's goals. Standards also help to guarantee the compatibility and functionality of
products.
Types of Security Standards
- Data Protection Regulation, generally (GDPR)
Since 2018, all European businesses that process and handle data must comply with GDPR, the
European Union's framework for data protection. GDPR compliance is demonstrably possible, but
certification is not required.
Documenting all data processing activities, putting in place data protection measures like policies,
training, and audits, and, when appropriate, appointing a Data Protection Officer are all ways that
businesses can demonstrate compliance with GDPR (DPO). These will be regarded by the
Information Commissioner's Office (ICO). Businesses may be subject to hefty fines of up to 4% of
annual turnover if a GDPR violation is suspected and if compliance is not maintained.
48
E123262 – Fudhail Faizal – Security Assignment 01
It is important to note that, as a result of Brexit, GDPR is no longer in effect domestically in the UK.
Instead, it has its own version, known as the UK-GDPR, which sits alongside an amended Data
Protection Act 2018.
- Cyber Essentials
In order to provide small- to medium-sized businesses with a straightforward and affordable means
of achieving a high standard of cybersecurity, the UK Government created the Cyber Essentials
program in 2014. Cyber Essentials, which consists of five essential technical controls, can assist
businesses in defending against 80% of common cyberattacks.
There are two levels of certification: Basic, which enables an organization to review and attest to
their compliance through an online self-assessment, and Plus, which entails a technical audit of your
systems by a qualified assessor to ensure alignment with the standard's controls.
- ISO 27000 Series
The ISO (International Organization for Standardization) standards, which cover a range of
cybersecurity methods and best practices, are widely acknowledged. The requirements for a high-
level Information Security Management System are listed in ISO 27001, the most well-known and
frequently requested standard by businesses.
Businesses of all sizes and industries can reduce information security and privacy risks by developing
efficient risk management processes and policies through the establishment of an information
security management system. Achieving this certification also enables companies to show that they
are in compliance with DPA2018 and other data protection laws, such as the UK-GDPR.
- NIST
All organizations can seek guidance from the National Institute of Standards and Technology's (NIST)
Cybersecurity Framework as they work to achieve a high level of cybersecurity and resilience.
Identify, Protect, Detect, Respond, and Recover are the five core branches that make up NIST's
framework. Businesses can show that they are skilled at identifying and addressing cyber risks by
coordinating policies and procedures within these functions.
- HIPAA
A specific industry is the target of particular standards. For instance, the Health Insurance Portability
and Accountability Act (HIPAA) serves as the benchmark for healthcare organizations, particularly
those in the USA, when it comes to the protection of patient data.
HIPAA, a law passed in the United States in 1996, mandates compliance with the physical and
cybersecurity measures outlined by the standard for all parties involved in the sector. Failure to do
so can result in fines that can be very expensive for these organizations. HIPAA enforcers claim that
in 2019, the typical monetary fine exceeded $1.2 million.
Importance of Security Standards
49
E123262 – Fudhail Faizal – Security Assignment 01
For your business to be successfully managed and run without hiccups, information security is
essential. Your organization will benefit from following a Standard in managing and safeguarding its
priceless data and information assets.
Standards give us a shared set of benchmarks that we can use to assess whether an organization has
policies, procedures, and other controls in place that adhere to a set minimum standard. Customers,
suppliers, and business partners have more faith in an organization's ability to deliver to a certain
standard if it is compliant with or meets that standard. Additionally, it may give a company a
competitive edge over rival companies. An organization that complies with security standards, for
instance, might have an advantage over a rival who does not when customers are evaluating their
products or services.
What is a security procedure
Procedures are in-depth, step-by-step instructions for carrying out a specific objective or mandate.
They should follow strict change control procedures because they are typically designed for internal
departments. As you go, procedures can be created. If your organization decides to go this route, it
is essential to have thorough and consistent documentation of the procedures you are creating.
frequently serve as the "cookbook" that staff members refer to when completing a
repeatable process.
sufficient in detail but not so complex that only a small group (or one person) will
comprehend it
Examples of procedures include installing operating systems, backing up a system,
granting access rights to a system, and creating new user accounts.
What is a security Guideline?
In situations where specific standards do not apply, guidelines are recommendations to users.
According to the best practices, guidelines are created to simplify specific processes. By their very
nature, guidelines should be open to interpretation and not be strictly adhered to.
than specific ones, are more general rules.
Be adaptable to unforeseen circumstances.
NOT to be mixed up with official policy statements.
Are all these the same?
You can see that policies, procedures, standards, and guidelines are distinct from one another. Each
has a purpose and meets a particular need.
Use the other tools to build on the policies, which are the data security anchor.
Remember that developing a program for information security takes time. It is a deliberate
organization-wide process that calls for participation from all levels. The IT department shouldn't be
the only one in charge of developing your program; most problems arise there.
50
E123262 – Fudhail Faizal – Security Assignment 01
Everyone must be in agreement.
The everyday tasks that must be completed in order to run your business make it more difficult to
achieve organization-wide consensus on policies, standards, procedures, and guidelines.
Disaster Recovery Plan
EMC Cyber
Last edited on 12-10-2022
51
E123262 – Fudhail Faizal – Security Assignment 01
Table of Contents
Recovery Time Objective and Recovery Point objective..........................................................................
EMC Cyber IT Disaster Recovery Plan Revision History............................................................................
Information Technology Statement of Intent..........................................................................................
Policy Statement......................................................................................................................................
Objectives................................................................................................................................................
Key Personnel Contact Information.........................................................................................................
Notification Calling tree...........................................................................................................................
Inventory Profile......................................................................................................................................
Miscellaneous inventory..........................................................................................................................
1. Plan Overview......................................................................................................................................
1.1 Plan Updating................................................................................................................................
1.2 Plan Documentation Storage.........................................................................................................
1.3 Backup Strategy.............................................................................................................................
1.4 Risk Management........................................................................................................................
2 Emergency..........................................................................................................................................
2.1 Plan Triggering events.................................................................................................................
2.2 Assembly Points...........................................................................................................................
2.3 Activation of Emergency Response Teams..................................................................................
2.3 Disaster Recovery Team...............................................................................................................
2.4 Emergency Alert, Escalation and DRP Activation.........................................................................
2.5 Emergency Alert..........................................................................................................................
2.6 DR Procedures for Management.................................................................................................
2.7 Contact with Employees..............................................................................................................
2.8 Backup Staff.................................................................................................................................
2.9 Recorded Messages/Updates......................................................................................................
2.10 Alternate Recovery Facilities/Hot Site.......................................................................................
2.11 Personnel and Family Notification.............................................................................................
3 Disaster Recovery Procedures............................................................................................................
3.1 Disaster Action Checklist..............................................................................................................
3.2 Emergency Response Procedures................................................................................................
3.3 Backup Operations Procedures....................................................................................................
52
E123262 – Fudhail Faizal – Security Assignment 01
3.4 Recovery Actions Procedures......................................................................................................
3.4.1 Recovery Plan for Mobile Site...................................................................................................
3.4.2 Recovery Plan for Hot site........................................................................................................
4. Disaster Recovery Drill.......................................................................................................................
5. DRP Exercising...................................................................................................................................
53
E123262 – Fudhail Faizal – Security Assignment 01
Business is negatively impacted by disasters. Business planning aims to minimize service and product
delivery interruptions caused by disasters to the greatest extent possible. The main issue is business
continuity.
The cornerstone of a comprehensive business continuity plan is an IT disaster recovery strategy.
Additionally, the goal of business continuity is to keep at least a basic level of service while returning
the organization to normal operations. When a disaster strikes, a company that hasn't established a
disaster recovery plan runs the risk of losing clients to rival businesses, not receiving funding, and
having the need for its goods and services reevaluated and deemed unnecessary.
Recovery Time Objective and Recovery Point objective
Date RTO RPO
12-10-2022 30 Minutes 2 Hours of Data
EMC Cyber IT Disaster Recovery Plan Revision History
Revision Date Name Description
1.0.0 11/10/2022 James Arthur Updated the RTO
54
E123262 – Fudhail Faizal – Security Assignment 01
Information Technology Statement of Intent
This document outlines our policies and practices for technology disaster recovery as well as our
process-level plans for restoring the telecommunications infrastructure and critical technology
platforms. This document lists our suggested procedures. In the event of an actual emergency,
changes to this a document could be created to guarantee the physical security of our users,
systems, and data.
Our goal is to guarantee information system availability, data integrity, and company continuity
Policy Statement
The following policy statement has been authorized by corporate management:
• A formal risk assessment shall be conducted to identify the needs for the disaster
recovery plan, and the company shall develop a thorough IT disaster recovery plan.
• In accordance with key business activities, the disaster recovery plan should cover all
essential and critical infrastructure components, including systems and networks.
• To make sure that the disaster recovery plan can be implemented in emergency
situations and that the management and staff understand how to execute it, it
should be periodically tested in a simulated environment.
• The disaster recovery plan must be explained to all employees, along with their
individual responsibilities.
• The disaster recovery plan must be updated to reflect any changes in the
environment.
Objectives
The main goal of the disaster recovery program is to create, test, and document a well-organized,
simple-to-understand plan that will aid the business in recovering as quickly and effectively as
possible from an unanticipated emergency or disaster that disrupts information systems and
business operations. These additional goals are included:
The following requirements must be met:
• Ensuring that all employees understand their roles in putting this plan into action;
• Ensuring that operational guidelines are followed in all planned activities;
• Ensuring that proposed contingency plans are cost-effective; and • Considering the
effects on other company sites.
• Disaster recovery capabilities as they relate to important clients, suppliers, and
others
Key Personnel Contact Information
Name, Title Contact Option Contact Detail
55
E123262 – Fudhail Faizal – Security Assignment 01
Bruce Wayne, IT manager Work 1234567890
Alternate 1234567890
Mobile 1234567890
Home 1234567890
Email Address btmn@dc.com
Alternate Email rbn@dc.com
Peter Parker, Branch Head Work 1234567890
Alternate 1234567890
Mobile 1234567890
Home 1234567890
Email Address spdr@qny.com
Alternate Email parkr@fnsm.com
Martin Garrix, Senior Work 1234567890
Manager
Alternate 1234567890
Mobile 1234567890
Home 1234567890
Email Address mrtn@gmail.com
Alternate Email grx@gmail.com
Dua Lipa, Inventory Work 1234567890
Department
Alternate 1234567890
Mobile 1234567890
Home 1234567890
Email Address Lipalipa@gmail.com
Alternate Email DuaLi@gmail.com
Olajide Olatunji, Finances Work 1234567890
Dpt
Alternate 1234567890
Mobile 1234567890
Home 1234567890
Email Address riplogn@ksi.com
Alternate Email noLedge@ksi.com
Tony Stark, Lead PM Work 1234567890
Alternate 1234567890
Mobile 1234567890
Home 1234567890
Email Address strk@pots.com
Alternate Email theIronMan@TSI.com
Fudhail Faizal, CEO Work 1234567890
Alternate 1234567890
Mobile 1234567890
Home 1234567890
56
E123262 – Fudhail Faizal – Security Assignment 01
Email Address fuds@hehe.com
Alternate Email no@gmail.com
Peter Griffin, HR Work 1234567890
Alternate 1234567890
Mobile 1234567890
Home 1234567890
Email Address griffs@quahog.com
Alternate Email petrcools@quahog.com
Notification Calling tree
Inventory Profile
57
E123262 – Fudhail Faizal – Security Assignment 01
Critical Assets Important Assets Unimportant Assets
assets without which your applications that are used at applications that are used
business cannot operate least once per day and can less frequently than once per
disrupt normal operations day
Manufacturer Description Quantity Model Serial Own or Cost
Number leased
Corsair CPU with built in 8 123Cx23 12345 Own $4000
RAM, GPU, UPS,
storage, and Cooling
fans
Kingston Hard Drives located 100 SATA 12345 Own $200
Technology in the servers and Kingston
the employees CPUs 120GB
SSD Hard
Disk Drive
RDM Workstation supplies 16 54321 12345 Own $800
Industrial
Products INC.
Sri Lanka Telephones and 4 Alcatel 12345 Leased $56
Telecom Telephone lines T28 Basic
Telephon
e
Haier Industrial Air 8 4-WAY 12345 Own $4000
conditioning and CASSETTE
heater units
HP Office Printer 2 HP Smart 12345 Leased $800
Tank 7301
All-in-One
Printer
Samsung Displays and Backup 12 S60UA 12345 Own $4200
Monitors 27”
Ridg-U-Rak Racks for files, 6 Rk1232 12345 Own $500
servers, and storage
Philips Air Humidifier 2 2000 12345 Own $500
Series
Miscellaneous inventory
Description Quantity Comments
58
E123262 – Fudhail Faizal – Security Assignment 01
OS Software for Machines Windows OS or MacOS As the employee requests,
the OS will be installed and
provided on their work
machines.
Other PC software Installed for all Machines Software used to complete
company tasks, antiviruses
and company tools
Printer Supplies As required for 2 office A4 paper packs and ink
printers cartridges based on the
usage.
59
E123262 – Fudhail Faizal – Security Assignment 01
1. Plan Overview
1.1 Plan Updating
The DRP updating procedure must be carefully planned out and managed.
Every time a change is made to the plan, it must be thoroughly tested, and the training materials
must be updated appropriately. The IT Director will be in charge of using formalized change control
procedures in this situation.
1.2 Plan Documentation Storage
Hard copies, CDs, and copies of this plan will all be kept in secure locations that the company will
specify. A CD and hard copy of this plan will be given to each senior management member to keep at
home. This plan will be distributed on CD and in hard copy to each member of the Disaster Recovery
Team and the Business Recovery Team. A master protected copy will be kept on particular resources
set up for this function.
1.3 Backup Strategy
Below is a list of important business processes along with the established backup plan for each.
The plan selected calls for a fully mirrored recovery site at the business' offices in Sri Lanka, Japan,
United States, Norway.
Maintaining a fully mirrored duplicate site as part of this strategy will allow for instantaneous
switching between the live site (headquarters) and the backup site.
Key Business Process Backup Strategy
IT Operations Fully mirrored recovery site
Tech Support – Hardware Fully mirrored recovery site
Tech Support – Software Fully mirrored recovery site
Facilities Management Fully mirrored recovery site
Email Fully mirrored recovery site
Purchasing Fully mirrored recovery site
Disaster Recovery Fully mirrored recovery site
Finance Fully mirrored recovery site
Contracts Admin Fully mirrored recovery site
Warehouse & Inventory Fully mirrored recovery site
Product Sales Fully mirrored recovery site
Maintenance Sales Fully mirrored recovery site
Human Resources Off-site data storage facility
Testing Fully Mirrored Recovery Site Fully mirrored recovery site
Workshop Fully Mirrored Recovery Site Fully mirrored recovery site
Call Center Fully mirrored recovery site
Web Site Fully mirrored recovery site
60
E123262 – Fudhail Faizal – Security Assignment 01
1.4 Risk Management
There are numerous potential disruptive threats that could happen at any time and interfere with
daily business operations. This section contains the conclusions of our considerations of a wide
range of potential threats. Every potential environmental emergency or disaster has been looked at.
Here, the level of business disruption that could result from each type of disaster is the main focus.
The following potential catastrophes have been rated:
Potential Disaster Probability Impact Brief Description Of Potential
Rating Rating Consequences & Remedial Actions
Flood 2 4 Install flood detection sirens and shift
sensitive inventory and databases
above the ground floor
Fire 3 4 FM200 suppression system installed
in main computer centers. Fire and
smoke detectors on all floors.
Tornado 3 4 Ensure Employees are indoors when
there are signs of a Tornado. Have
the company updated on the current
and future weather predictions.
Windows can be completely sealed
upon closing them, avoiding any dust
or debris entering.
Electrical Storms 2 3 Earth wire installed on the roof of the
building. The main power line will
immediately shut off in case of a
heavy lightning strike, protecting the
electrical equipment at the Building
Terrorist Attacks 1 1 The Employees and managements life
will be at risk, install ID scanners
upon entry of the building and
Employ armed security personnel.
Act of Sabotage 1 1 Ensure the dismissed or redundant
employee has been rid of all his
identity at the company, including
the work numbers and work email as
it could be used against the
organization
Electrical power 4 4 Redundant UPS array together with
failure auto standby generator that is tested
weekly & remotely monitored 24/7.
UPSs also remotely monitored.
Loss of 4 4 Two diversely routed T1 trunks into
communication building. WAN redundancy, voice
network services network resilience
Probability: 5=Very High, 1=Very Low Impact: 1=Destruction to the Organization, 5=Minor
annoyance
2 Emergency
2.1 Plan Triggering events
The following are major triggers at headquarters that would cause the DRP to go into effect:
61
E123262 – Fudhail Faizal – Security Assignment 01
• Complete loss of all communications
• Complete loss of power
• Flooding of the premises
2.2 Assembly Points
The DRP invocation plan designates two evacuation assembly points when the premises must be
evacuated:
Primary: The far end of the main parking lot; Alternate: The business parking lot across the street.
2.3 Activation of Emergency Response Teams
The Emergency Response Team (ERT) must be activated when an incident occurs.
The extent to which the DRP must be used will then be decided by the ERT. To be used in the event
of a disaster, each employee must be given a Quick Reference card with the contact information for
the ERT.
The ERT's responsibilities include:
In the event of a disaster, act quickly and contact emergency services; determine the disaster's
scope and its effects on the company, data center, etc.;
• Immediately alert emergency services to a potential disaster;
• Determine the disaster's scope and the effects it will have on the company, data
center, etc.;
• Select the DR Plan's components that need to be activated;
• create and oversee a team for disaster recovery to maintain essential services and
resume regular operations;
• Make sure employees are informed, and assign tasks and responsibilities as
necessary.
2.3 Disaster Recovery Team
The ERT will get in touch with the team and put it together. The team's duties include:
• Setting up facilities for an emergency level of service within two business hours;
• restoring key services within four business hours of the incident;
• returning to normal operations between eight and twenty-four hours after the
incident; and
• coordinating efforts with the disaster recovery team, first responders, etc.
2.4 Emergency Alert, Escalation and DRP Activation
This policy and procedure has been established to guarantee that personnel will have a clear
understanding of who should be contacted in the event of a disaster or crisis. In order to ensure that
62
E123262 – Fudhail Faizal – Security Assignment 01
communications can be quickly established while disaster recovery is activated, procedures have
been addressed.
The DR plan will primarily rely on important management and staff members who will offer the
technical and management skills required to achieve a seamless technological and commercial
recovery. As the company resumes normal business operations, suppliers of essential products and
services will continue to support recovery of business operations.
2.5 Emergency Alert
In the order listed, the person who discovers the incident dials one of the Emergency Response
Team members:
Emergency Response Team
• Bruce Wayne
• Dua Lipa
If not available, try these instead:
• Peter Parker
• Peter Griffin
For the disasters listed in this plan, as well as for any other circumstance that impairs the business'
ability to operate normally, the Emergency Response Team (ERT) oversees activating the DRP.
Notifying the Disaster Recovery Team (DRT) that an emergency has occurred is one of the duties
during the early stages of the emergency. The notification will include enough details in order to
effectively communicate the DRT members' request to gather at the problem's location. Senior
representatives from the key business departments will make up the Business Recovery Team (BRT).
A senior member of the company's management team, the BRT Leader will be in charge of taking
overall control of the situation and ensuring that business operations resume as soon as possible.
2.6 DR Procedures for Management
The names and phone numbers of each employee in each department will be kept on file by
members of the management team. If the corporate headquarters is inaccessible, useless, or
destroyed, the management team will also have a hard copy of the organization's disaster recovery
and business continuity plans on file in their homes.
2.7 Contact with Employees
The focal points for each department will be the managers, who will also make calls to other
employees to discuss the crisis or disaster and the company's immediate plans. Employees are
advised to call the emergency contact listed for any staff members they are unable to reach in order
to inform them of the disaster.
63
E123262 – Fudhail Faizal – Security Assignment 01
2.8 Backup Staff
If a manager or employee designated to notify other employees is unable to do so or becomes ill,
the designated backup employee will handle notification responsibilities.
2.9 Recorded Messages/Updates
Staff members can call a toll-free hotline listed in the DRP wallet card to get the most recent
information on the disaster and the organization's response. Information on the disaster's scope,
meeting locations, and updates on the start of new work will all be included in messages.
2.10 Alternate Recovery Facilities/Hot Site
In the event that it becomes necessary, SunGard's hot site will be activated, and notice will be given
via recorded messages or through conversations with managers. For the first 24 hours, the hot site
will only be staffed by members of the disaster recovery team, with additional staff members joining
as needed.
2.11 Personnel and Family Notification
It will be necessary to quickly notify the employee's immediate family members if the incident has
led to a situation that would worry the employee's immediate family, such as the hospitalization of
injured people.
3 Disaster Recovery Procedures
3.1 Disaster Action Checklist
Plan Initiation
1. Make senior management aware.
2. Set up a disaster recovery team by contacting them.
3. determine the disaster's severity
4. Implement a suitable application recovery strategy based on the disaster's scope.
5. Establish schedules, contact a backup site, and track progress
64
E123262 – Fudhail Faizal – Security Assignment 01
6. Contact all other personnel who may be required for user and data processing.
7. Contact hardware and software vendors.
8. Inform users of the service disruption
Follow Up checklist
1. List the teams and their respective tasks.
2. Obtain emergency funds, and if necessary, arrange transportation to and from the
backup location.
3. Install housing, if necessary
4. Create dining facilities as necessary.
5. List every employee's name and phone number.
6. Create a plan for user participation.
7. Set up the mail delivery and receipt.
8. assemble backup office supplies
9. according to need, rent or buy equipment
10. Choose which applications to run and in what order.
11. Determine the necessary number of workstations.
12. Examine any required offline hardware for each application.
13. Verify the paperwork required for each application.
14. Before leaving, verify all data being transferred to the backup location, and leave the
inventory profile in place.
15. Establish key vendors to help with issues that arise during emergencies
16. Make transportation arrangements for any extra items required at the backup
location.
17. Follow the road signs to the backup site.
18. If necessary, look for additional magnetic tapes or optical media.
19. Make copies of the procedure manuals, operational documentation, and system
documentation.
20. Make sure that everyone involved is aware of their duties.
21. Make insurance companies aware
3.2 Emergency Response Procedures
1. Active Shooting
- Exit the building if it is safe to do so; if not, lock or barricade yourself inside a room.
- Lay down on the floor, close and lock any windows, and turn off the lights.
- If possible, flee the scene if the shooter(s) leaves. Have a plan or route for escaping in
mind. Keep your hands out in front of you and obey any commands from law
enforcement.
65
E123262 – Fudhail Faizal – Security Assignment 01
- When it is safe to do so, dial 911. Maintain composure, speak quietly, and give as much
information as you can (such as your name and location, the number and nature of
injuries, and specifics about the shooter(s)—such as their appearance and weaponry).
- Keep the line open if you are unable to speak so that the dispatcher can listen and try to
locate you.
- If law enforcement personnel approach you, stop and raise your arms with your palms
facing the officer.
- When you have reached a secure area, remain there until a police officer or a recognized
safety official issue the "all clear."
2. Bomb Threats
- DO NOT touch, tamper with, or move a suspicious object; instead, report it to the
organization’s Safety if you see one.
- NONE of your electronic devices, including phones, laptops, radios, tablets, etc., should
be used near the suspicious package or object.
- Keep the caller on the line if you receive a telephone alert about a bomb in a building. If
they hang up, DO NOT cut the call; instead, move to another phone and dial 911,
followed by 1243657809, which you can use to report the incident to office safety.
- If an evacuation is necessary, follow the standard procedures and DON'T try to enter a
building again until emergency personnel have given the go-ahead. Additionally, if you
are aware of a disabled or injured person who requires assistance, call emergency
services right away.
- Query the caller about the location of the bomb. When is it scheduled to go off? How
does it appear? Which type of bomb is that? Did you put it there? Why? Which address
do you have? Describe yourself.
- Pay close attention to the caller's precise language, voice, and speaking style. Try to
ascertain the caller's gender, race/ethnicity, and age. Listen for any background noises.
3. Building Lockdown
- When instructed to do so, start the lockdown/shelter-in-place procedure right away.
Until it is terminated by Office Safety or emergency response personnel, the lockdown
order will be in place.
- Keep your composure and stick with your group of visitors, faculty, or students.
- When the building is on lockdown, avoid leaving the space. Lock the windows and doors
to the room, and immediately draw the blinds.
- Keep people away from windows and doors and in silence. Consider people with
disabilities who might require assistance.
66
E123262 – Fudhail Faizal – Security Assignment 01
- Keep everyone as close to the floor as possible and as hidden behind/under furniture in
the room as you can if a gunshot is heard. If running is required, do so in a zigzag pattern
rather than a straight line.
4. Earthquakes
- If you're indoors, duck, cover, and hold under a desk or table. You can also stand in a
doorway or where two walls meet, away from windows and potentially falling objects. If
you're outside, stay in a clear area far from any trees, buildings, power lines, or other
structures. If you're driving, stop and pull over far from any overhead power lines.
- After the shock wears off, go outside to a spacious area.
- NEVER use an elevator to leave a building.
- Observe the guidance given by emergency service personnel.
- If you are aware of a disabled person or someone who needs assistance, call emergency
services right away.
5. Evacuations
- An evacuation will be announced verbally by a professor, an office Safety officer, or
another branch representative, through the public address system, and/or by flashing
lights and audible alarms.
- To an evacuation site, proceed to the nearest exit by walking—DO NOT RUN—there.
- AVOID using elevators.
- obey the emergency personnel's instructions.
- Any disabled or injured people who require assistance should be reported to emergency
personnel right away. If you are hurt or disabled, you should SEEK HELP until you are
rescued.
- Prior to being told you can leave the area by emergency personnel, stay inside the
building with the group you were with.
6. Fires and Fire Evacuations
- When a fire is discovered, call 911 right away, then the Department of Organization
Safety at 1243126587, or utilize one of the Code Blue boxes scattered around the
building.
- If a fire alarm goes off, leave the building right away. DO NOT use the elevators.
- To the nearest exit, WALK, DO NOT RUN, while announcing the fire to others. For more
information, go to the designated evacuation site.
- DO NOT RUN if your clothing starts to burn. ROLL, DROP, and STOP.
- If you believe someone may be trapped inside the structure, alert emergency personnel
on the scene right away.
67
E123262 – Fudhail Faizal – Security Assignment 01
7. Flood
- Go to a higher location.
- Avoid being near trees during thunderstorms as they may attract lightning.
- Even when driving a car, stay away from fast-moving water.
- Stay off the flooded ground (water depth is not always obvious).
- Avoid using and encountering electrical equipment.
- Keep an eye out for high water at night because other dangers may be hidden by the
darkness.
8. Hazardous Materials Leaks/ Spills
- Contain the spill, leak, fumes, or fire by leaving the area and closing the door if there is a
fire involving hazardous material (flammable, toxic, corrosive, oxygen, or cryogenic).
Keep your distance from the material. Find the Material Safety Data Sheets (MSDS) for
any identifiable materials, if time permits.
- Set off the building's fire alarm to signal the start of the evacuation.
- Call the Department of Organization Safety at 1243126587 or one of the Code Blue call
boxes scattered around the building after pressing 911. Name, department, emergency
location, incident type, and material description should all be provided.
- Go to the designated area for evacuation. Remain outside the building until told it is safe
to enter again.
- even thought to be dangerous materials, leaks, or suspicious odors should be reported
to the buildings Safety so appropriate action can be taken.
9. Medical Emergencies
- Check for symptoms like chest pain, difficulty breathing, excessive or uncontrollable
bleeding, unconsciousness, and life-threatening injuries to determine what constitutes a
true medical emergency (severe head injuries, severe burns, etc.)
- Call 911, then Organization Safety, and let them know what kind of illness or injury you
have, your name, where the injury occurred, and your phone number.
- Provide first aid (if you are trained AND permission is granted by the injured)
- Send rescue workers and medical staff to the area.
- Continue to be with the victim until help arrives.
10. Power/ Utility Outage
- Employees should, whenever possible, check with their supervisor before leaving their
workstation and students should remain in their living area.
- Use stairs rather than elevators if going from one floor to another is necessary.
- Use battery-operated lights instead of candles, please.
- If at all possible, turn off electronic devices and refrain from using the university phone
system to save battery life for official use.
- Follow the instructions of the building coordinators and emergency personnel, and use
caution when handling valuables.
-
68
E123262 – Fudhail Faizal – Security Assignment 01
3.3 Backup Operations Procedures
1. Offline Backups
- Activate or terminate all active transactions.
- All database writing is halted.
- Insist on a checkpoint. Checkpoints has more information.
- Your container files should all be copied to the backup location.
- Be aware though, that only having all of your log files will allow you to backup just
the modified databases. Because you might not be alerted to a database file that
was modified, using can result in an unrecoverable backup if you have been
removing log files for any reason.
- To your backup location, copy the most recent log file. The filename extension for
your logs is log.xxxxxxxxxx, where xxxxxxxxxx is a sequential number. The log file
with the highest number is the most recent one.
2. Hot Backup
- You don't need to halt database operations in order to create a hot backup. You
could be writing to your database at the time of the backup while transactions are
still in progress. This has the drawback that it leaves you uncertain as to the precise
state of your database at the time of the backup.
- A hot backup can be made using the db hotbackup command-line tool. This program
copies all required files to a target directory after running a checkpoint, which is
optional.
- Additionally, you can develop your own hot backup system by employing the DB
ENV->backup() method.
- As an alternative, you can do a hot backup by hand as follows:
- Your container files should all be copied to the backup location.
- To your backup location, copy all logs.
3. Incremental Backups
You can make incremental backups after you have created a full backup, which can be an offline or
online backup. Simply copy all of your currently present log files to your backup location to
accomplish this.
You don't have to perform a checkpoint or stop container write operations in order to perform
incremental backups.
It's crucial to be aware that an incremental backup can no longer be used to restore a database copy
made before a bulk loading event if your application makes use of the transactional bulk insert
optimization. This is true because some record insertions made during bulk loading are not logged,
69
E123262 – Fudhail Faizal – Security Assignment 01
making it impossible for recovery to roll back these insertions. It is advised to plan a full backup for
after a bulk loading event.
When using incremental backups, keep in mind that a longer recovery time will result from your
backup having more log files. Run complete backups at regular intervals, followed by incremental
backups at less frequent intervals. Your application's sensitivity to prolonged recoveries and the rate
at which your containers change will determine how frequently you need to run a full backup
(should one be required).
Running recovery against the backup as you make each incremental backup will also speed up
recovery. If you perform recovery as you go, BDB XML will have less work to do if you ever need to
restore your environment from a backup.
3.4 Recovery Actions Procedures
Notify Disaster Recovery Services that you need their services and that you have chosen a recovery
plan.
Note: The countdown to the guaranteed delivery time starts as soon as Peter Griffin is informed of
the choice of the recovery plan.
Dial 1234567890 or 0987654321 to report a disaster.
These phone numbers are available Monday through Friday from 12 am to 11 pm.
Number for disaster notifications 1324576809
On weekends and public holidays, as well as after regular business hours, this phone number is
available for disaster notification. Please only use this number to notify of actual disasters.
Give Tony Stark the address of the site where the equipment will be delivered (if applicable), a
contact, a backup contact, and phone numbers at which the contacts can be reached whenever
needed.
Schedule any required service connections by contacting the providers of the electricity and
telephone services.
Inform Bruce Wayne right away if any related plans should change.
3.4.1 Recovery Plan for Mobile Site
1. Inform Bruce Wayne of the disaster's specifics and the requirement to choose a mobile
site plan.
2. Within 48 hours of the telephone notification, confirm in writing to Peter Griffin the
details of the notification.
3. Verify that the backup machine is loaded with all necessary backup media.
4. To pay for the use of backup equipment, prepare a purchase order.
5. Notify Peter Parker of the location and plans for a trailer.
70
E123262 – Fudhail Faizal – Security Assignment 01
6. Notify the telephone company SLT Mobitel of any potential changes to the emergency
line, depending on your communication needs.
7. Start setting up communications and power.
8. When the trailer arrives, power and communications are already set up and ready to
connect.
9. Break the current connection to the administration controllers at the location where the
telephone lines enter the structure.
10. These lines are switched over to those that lead to the mobile website. The mobile site's
modems are connected to them.
11. The mobile unit would then be connected to the lines currently running from Sri Lanka
to USA via modems.
12. In the event of a disaster, this might necessitate that lines at the IT complex be diverted
to a location that is more secure.
13. Connect to power and perform any necessary inspections when the trailer arrives.
14. Connect to the communication lines and perform the required checks.
15. start restoring the system from backups.
16. Start your normal business as soon as you can:
- daily tasks
- weekly savings
- daily savings
17. Set up a backup schedule so you can restore the system on a computer at home when a
site becomes available. (Use routine system backup techniques.)
18. Distribute keys as needed and secure the mobile site.
19. Keep a record of your mobile equipment's maintenance.
3.4.2 Recovery Plan for Hot site
1. Inform Bruce Wayne of the disaster's specifics and its need for a hot site.
2. To facilitate communication, request an air shipment of modems to. (For
communications regarding the hot site, see.)
3. Within 48 hours of the telephone notification, confirm the written notification to .
4. Make the operations team's necessary travel arrangements to the destination.
5. Verify that you have enough save media and that it is shipped-ready before you attempt
a backup system restore.
71
E123262 – Fudhail Faizal – Security Assignment 01
6. To pay for the use of the backup system, prepare a purchase order.
7. Before leaving for the hot site, check the checklist to make sure you have all the
necessary supplies.
8. Make certain the disaster recovery team at the disaster site has the information it needs
to start the site's restoration.
9. Allow for travel costs (cash advance).
10. Contact home base to establish communications protocols after reaching the hot site.
11. Verify the completeness of the materials brought to the hot site.
12. Start the system's loading process from the save media.
13. Start your normal business as soon as you can:
daily tasks
weekly savings
daily savings
14. Make a schedule for backing up the hot-site system so you can restore it on your
computer at home.
4. Disaster Recovery Drill
Disaster Drills will be conducted twice every month as per the organizational agreement.
5. DRP Exercising
Exercises for disaster recovery plans are a crucial step in creating the plan.
No one passes or fails in a DRP exercise; instead, everyone who takes part learns from exercises
what needs to be improved and how improvements can be made. Emergency teams should practice
their plans to make sure they are familiar with their tasks and, more importantly, that they are
confident in their abilities.
When necessary, successful DR plans go into action quickly and efficiently. This can only occur if each
person who has a part to play in the plan has practiced that part at least once. Additionally, the plan
needs to be verified by simulating the conditions under which it must operate and observing the
results.
References
1. UNITRENDS The CIA Triad and Its Importance in Data Security [Online].
Available at: https://bit.ly/3y1WUCr
[Accessed 26th September 2022]
2. Jeff Melnick (January 29th 2019) Why Monitoring of Network Devices Is Critical for
Network Security [Online].
Available at: https://bit.ly/3UHVFlD
[Accessed 26th September 2022]
72
E123262 – Fudhail Faizal – Security Assignment 01
3. Jeff Edwards (August 16th 2018) Managing Network Configuration Changes: Five Best
Practices [Online].
Available at: https://bit.ly/3dO5XQB
[Accessed 26th September 2022]
4. Fortinet DMZ [Online].
Available at: https://www.fortinet.com/resources/cyberglossary/what-is-dmz
[Accessed 26th September 2022]
5. Ben Lutkevich (July 2021) DMZ in Networking [Online].
Available at: https://bit.ly/3E0NeMm
[Accessed 26th September 2022]
6. Mishal Root (September 7th 2021) 7 Advantages and Disadvantages of Static IP Address |
Drawbacks & Benefits of Static IP Address [Online].
Available at: https://bit.ly/3xYfg7f
[Accessed 26th September 2022]
7. Alexander S. Gills (March 2020) static IP address [Online].
Available at: https://www.techtarget.com/whatis/definition/static-IP-address
[Accessed 26th September 2022]
8. Geeksforgeeks (18th October 2021) Advantages and Disadvantages of NAT [Online].
Available at: https://www.geeksforgeeks.org/advantages-and-disadvantages-of-nat/
[Accessed on 26th September 2022]
9. Staff Contributor (24th June 2021) 5 Network Performance Management Tools and Guide
[Online].
Available at: https://www.dnsstuff.com/network-performance-management
[Accessed on 26th September 2022]
10. Lavanya Rathnam (26th August 2022) Top 5 Network Security Tools
Available at: https://techgenix.com/expert-recommended-network-security-tools/
[Accessed on 26th September 2022]
11. CGMA (11th June 2013) Enterprise Risk Management (ERM)
Available at: https://bit.ly/3ShVQCw
[Accessed on 26th September 2022]
12. Oliver Peterson (1st July 2019) Basics of Enterprise Risk Management(ERM): How to Get
Started [Online].
73
E123262 – Fudhail Faizal – Security Assignment 01
Available at: https://www.process.st/enterprise-risk-management/
[Accessed on 26th September 2022]
13. CFI Team (21st February 2021) Enterprise Risk Management (ERM) [Online].
Available at: https://bit.ly/3RkvxdM
[Accessed on 26th September 2022]
14. Jinson Varghese (26th September 2022) IT Security Audit: Importance, Types, and
Methodology [Online].
Available at: https://www.getastra.com/blog/security-audit/it-security-audit/
[Accessed on 26th September 2022]
15. Amy Larsen DeCarlo (December 2018) How can organizations improve their network
change management? [Online].
Available at: https://bit.ly/3dOL87C
[Accessed on 26th September 2022]
16. Silvia Bitchkei (19th June 2018) Cybersecurity Challenges & Organizational Change
Management [Online].
Available at: https://bit.ly/3LSdhan
[Accessed on 26th September 2022]
17. Sam Erdheim (19th August 2013) Using Firewall Change Management to Align Security
with the Business [Online].
Available at: https://bit.ly/3Chzyvk
[Accessed on 26th September 2022]
18. Dr. Blake Curtis (10th June 2020) The Impact of Poor IT Audit Planning and Mitigating
Audit Risk [Online].
Available at: https://bit.ly/3fkfAH7
[Accessed on 26th September 2022]
19. AdEPT (9th October 2020) What are the Risks of Not Having a Disaster Recovery Plan?
[Online].
Available at: https://www.adept.co.uk/what-are-the-risks-of-not-having-a-disaster-
recovery-plan/
[Accessed on 26th September 2022]
20. Data Protection and Privacy Laws [Online].
Available at: https://id4d.worldbank.org/guide/data-protection-and-privacy-laws
[Accessed on 26th September 2022]
21. Brien Posey (November 2021) ISO 31000 Risk Management [Online].
Available at: https://www.techtarget.com/searchsecurity/definition/ISO-31000-Risk-
Management
[Accessed on 27th September 2022]
74
E123262 – Fudhail Faizal – Security Assignment 01
22. Ideagen (14th December 2021) What are ISO standards? [Online].
Available at: https://www.ideagen.com/thought-leadership/blog/what-are-iso-standards
[Accessed on 27th September 2022]
23. Eric Lachapelle (1st September 2015) ISO 31000 Risk Management – Principles and
Guidelines [Online].
Available at: https://bit.ly/3Rk9q7l
[Accessed on 27th September 2022]
24. Mike Ward (20th September) If they haven’t got it, they cant flaunt it: Access
Management [Online].
Available at: https://bit.ly/3SER6qw
[Accessed on 27th September 2022]
25. Helen A. Munter (9th September 2015) Importance of Audits of Internal Controls
[Online].
Available at: https://bit.ly/3dMexiH
[Accessed on 27th September 2022]
26. Reinhard Schrank (22nd November 2020) The Impact of Damage Apportionment on
Internal Control System Quality and Financial Reporting Accuracy [Online].
Available at: https://onlinelibrary.wiley.com/doi/full/10.1111/abac.12204
[Accessed on 27th September 2022]
27. Dan ( 28th August 2019) What Happens When Companies Don’t Have Internal Controls
[Online].
Available at: https://bit.ly/3UI8dcO
[Accessed on 27th September 2022]
28. Tara Duggan Signs & Symptoms of a Lack of Internal Control of a Business [Online].
Available at: https://bit.ly/3EgsJvt
[Accessed on 27th September 2022]
29. Lely Lubna Alaydrus (23rd April 2020) Impact of Computer Misuse in the Workplace
[Online].
Available at: https://knepublishing.com/index.php/KnE-Social/article/view/6838
[Accessed on 27th September 2022]
30. Knowww What is a physical attack in security? [Online].
Available at: https://knowww.eu/nodes/5bd5bfdd7bb7bca48fe42d18
[Accessed on 27th September 2022]
31. Imperva Cyber Attack [Online].
75
E123262 – Fudhail Faizal – Security Assignment 01
Available at: https://www.imperva.com/learn/application-security/cyber-attack/
[Accessed on 27th September 2022]
32. Luke Irwin (20th January 2022) What Is Information Security Risk? Definition and
Explanation [Online].
Available at: https://bit.ly/3E7BHe2
[Accessed on 27th September 2022]
33. Lindsay Pietroluongo (9th December 2021) What is a Firewall? Understanding What They
Are and Which Type is Right For You [Online].
Available at: https://bit.ly/3dMz1YN
[Accessed on 27th September 2022]
34. Avast What Is a VPN & How Does It Work? [Online].
Available at: https://www.avast.com/c-what-is-a-vpn
[Accessed on 27th September 2022]
35. Coudian 4 Disaster Recovery Plan Examples and 10 Essential Plan Items [Online].
Available at: https://bit.ly/3rPtEeB
[Accessed on 29th September 2022]
36. Jaspreet Singh (October 22, 2021) Understanding RPO and RTO [Online].
Available at: https://www.druva.com/blog/understanding-rpo-and-rto/
[Accessed on 29th September 2022]
37. IBM Example: Disaster Recovery plan [Online].
Available at: https://www.ibm.com/docs/en/i/7.2?topic=system-example-disaster-
recovery-plan
[Accessed on 29th September 2022]
76
E123262 – Fudhail Faizal – Security Assignment 01
77
E123262 – Fudhail Faizal – Security Assignment 01
78
E123262 – Fudhail Faizal – Security Assignment 01
You might also like
- Unit 6 Managing A Successful Computing Project 2021Document62 pagesUnit 6 Managing A Successful Computing Project 2021ishan maduahanka0% (2)
- 2640-1665054891113-Unit - 05 - SecurityDocument52 pages2640-1665054891113-Unit - 05 - SecurityHasantha Indrajith100% (2)
- Internal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsDocument33 pagesInternal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsU & Me100% (2)
- Unit 05 - Security - Holistic AssignmentDocument20 pagesUnit 05 - Security - Holistic AssignmentRangana Perera100% (1)
- ProDocument131 pagesProvbr businessNo ratings yet
- Btec HND Unit 5 Security New PDFDocument46 pagesBtec HND Unit 5 Security New PDFronica100% (1)
- 203-1540467331035-Unit 5 Security 2018.07.03Document13 pages203-1540467331035-Unit 5 Security 2018.07.03SajithNo ratings yet
- Unit - 05 - Security AssignmentDocument96 pagesUnit - 05 - Security AssignmentsachinNo ratings yet
- MSCP SampleDocument41 pagesMSCP SampleRomali KeerthisingheNo ratings yet
- ASTM B201 (2014r)Document3 pagesASTM B201 (2014r)PubcrawlNo ratings yet
- Security AssignmentDocument114 pagesSecurity AssignmentLenovo LegionNo ratings yet
- Unit 05 - Security Reworded 2021 Bhanuka PereraDocument69 pagesUnit 05 - Security Reworded 2021 Bhanuka PereraThejanu BandaraNo ratings yet
- SecurityDocument72 pagesSecurityravindupanduwawala321No ratings yet
- Female Assignment ExampleDocument143 pagesFemale Assignment ExampleHarry potterNo ratings yet
- A-067880-1628317685222-92301-G.K Ashen - 97 - Security - Unit 05Document86 pagesA-067880-1628317685222-92301-G.K Ashen - 97 - Security - Unit 05Harry potterNo ratings yet
- Security Reworded 2021vyenuDocument93 pagesSecurity Reworded 2021vyenuCool MarttNo ratings yet
- Sec Udesh AssignmentDocument82 pagesSec Udesh Assignmentudesh ishankaNo ratings yet
- 788-1601897459456-Unit 05 - Security - 2020Document14 pages788-1601897459456-Unit 05 - Security - 2020Career and EducationNo ratings yet
- 1155-1619623492920-Security Reworded 2021Document34 pages1155-1619623492920-Security Reworded 2021Cool MarttNo ratings yet
- Internal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsDocument14 pagesInternal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsmahdiNo ratings yet
- Unit - 05 - SecurityDocument13 pagesUnit - 05 - SecuritycmlunoufgroupNo ratings yet
- Security AssignmentDocument127 pagesSecurity AssignmentShrawan Shraw100% (1)
- A 019730 1636705235242 114189 W.M.supun Anjana Jayasinghe Security Reworded 2021Document68 pagesA 019730 1636705235242 114189 W.M.supun Anjana Jayasinghe Security Reworded 2021Dishan SanjayaNo ratings yet
- SecurityDocument41 pagesSecurityMaster GamerNo ratings yet
- 50 SecurityDocument43 pages50 SecurityMohamed SahlNo ratings yet
- Security AssaignmentDocument53 pagesSecurity Assaignmentkaruna niluNo ratings yet
- Security AssaignmentDocument55 pagesSecurity Assaignmentkaruna niluNo ratings yet
- Security Yohan PDFDocument71 pagesSecurity Yohan PDFCool MarttNo ratings yet
- Internal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsDocument54 pagesInternal Verification of Assessment Decisions - BTEC (RQF) : Higher Nationalsrivindu ranasinghe100% (2)
- Security AssignmentDocument37 pagesSecurity AssignmentRajesh PrabhakarNo ratings yet
- Irani - Kan-1661451330426-158199-Security Unit 5Document114 pagesIrani - Kan-1661451330426-158199-Security Unit 5safwan ramzeenNo ratings yet
- Higher Nationals: Internal Verification of Assessment Decisions - BTEC (RQF)Document52 pagesHigher Nationals: Internal Verification of Assessment Decisions - BTEC (RQF)diniya.ranaNo ratings yet
- KANA 013536 P.V.Godrick Naveen (Security Assignment)Document34 pagesKANA 013536 P.V.Godrick Naveen (Security Assignment)Rajesh PrabhakarNo ratings yet
- ProgrammingDocument37 pagesProgrammingMaster GamerNo ratings yet
- Unit 17 - Network SecurityDocument12 pagesUnit 17 - Network SecuritychaNo ratings yet
- Unit 17 - Network Security - AssignmentDocument70 pagesUnit 17 - Network Security - AssignmentNithya JayawardhanaNo ratings yet
- NETWORKINGDocument19 pagesNETWORKINGihlastraveleasyNo ratings yet
- AssignmentDocument136 pagesAssignmentMohamed SabrinNo ratings yet
- Grifindo Toys DocumentDocument45 pagesGrifindo Toys DocumentC. GrinathNo ratings yet
- Unit 02 Networking M.I.P. PamodDocument167 pagesUnit 02 Networking M.I.P. Pamodpamodp67No ratings yet
- Programming AssignmentDocument42 pagesProgramming AssignmentkaushalyasasithNo ratings yet
- E156915-1700413212347-330783-Unit 45 - Emerging - Technologies - Reworded - 2021Document41 pagesE156915-1700413212347-330783-Unit 45 - Emerging - Technologies - Reworded - 2021muheedhmuheedhboyNo ratings yet
- A-004481-1621430211522-88406-Net Assignment (ESOFT-4481)Document127 pagesA-004481-1621430211522-88406-Net Assignment (ESOFT-4481)Ishrak IchiNo ratings yet
- E114910-1659288515980-150975-1151-1619622564463-Unit 02 Networking - Reworded - 2021Document72 pagesE114910-1659288515980-150975-1151-1619622564463-Unit 02 Networking - Reworded - 2021isumkNo ratings yet
- Sample Programming Assignment PDFDocument106 pagesSample Programming Assignment PDFIshani Puvimannasinghe100% (1)
- Ruzan Programming Final Assignment - 082943Document72 pagesRuzan Programming Final Assignment - 082943starelike002No ratings yet
- NetworkingDocument86 pagesNetworkingMaster GamerNo ratings yet
- Unit 34 - System Analysis & Design Reworded 2021-MergedDocument65 pagesUnit 34 - System Analysis & Design Reworded 2021-MergedROSHEN ANTHONYNo ratings yet
- MSCPDocument83 pagesMSCPLenovo LegionNo ratings yet
- Higher Nationals: Internal Verification of Assessment Decisions - BTEC (RQF)Document121 pagesHigher Nationals: Internal Verification of Assessment Decisions - BTEC (RQF)msc2020uom batchNo ratings yet
- M.M Rishad-Unit-01 Programming AssignmentDocument30 pagesM.M Rishad-Unit-01 Programming AssignmentRishad JobbsNo ratings yet
- 4548-1688753552722-Unit 31 ForensicsDocument12 pages4548-1688753552722-Unit 31 ForensicsSatkunanathan VidurshkaNo ratings yet
- ProgrammingDocument64 pagesProgrammingRUSHINI THASHMILA FERNANDONo ratings yet
- MM234Document96 pagesMM234thiwankaamila75No ratings yet
- Unit-01 ProgrammingDocument51 pagesUnit-01 ProgrammingDPereraNo ratings yet
- Unit 01 - Programming AssignmentDocument82 pagesUnit 01 - Programming AssignmentThushan Lakshitha0% (1)
- Unit 06 Managing A Successful Research Project 2018.10.23Document14 pagesUnit 06 Managing A Successful Research Project 2018.10.23Thab ThabNo ratings yet
- Unit 1 MS Office 2023.05.30Document6 pagesUnit 1 MS Office 2023.05.30Ahmed NadhaNo ratings yet
- MAS. Abdhullah Shufaiq - Unit-01 Programming Assignment-Holistic Final CorectedDocument110 pagesMAS. Abdhullah Shufaiq - Unit-01 Programming Assignment-Holistic Final CorectedThayalan OdnielNo ratings yet
- Higher NationalsDocument82 pagesHigher NationalsRaishaNo ratings yet
- Problem SolvingDocument5 pagesProblem SolvingfudhailfaizalNo ratings yet
- Verbal Communication by Group 3Document3 pagesVerbal Communication by Group 3fudhailfaizalNo ratings yet
- Request LetterDocument1 pageRequest LetterfudhailfaizalNo ratings yet
- Python Practical Questions For HND PearsonDocument7 pagesPython Practical Questions For HND PearsonfudhailfaizalNo ratings yet
- CRP BriefDocument2 pagesCRP BrieffudhailfaizalNo ratings yet
- Class - 20200904 Restore - Recovery Using Keystore (My Practice)Document23 pagesClass - 20200904 Restore - Recovery Using Keystore (My Practice)RaihanNo ratings yet
- IAS 37 Quizzes (Updated Aug 2021) - Attempt ReviewDocument11 pagesIAS 37 Quizzes (Updated Aug 2021) - Attempt ReviewNguyễn Hữu ThọNo ratings yet
- Hydrogen Power Handbook (3206)Document34 pagesHydrogen Power Handbook (3206)cesar baranda100% (2)
- Recruitment and Recruitment Process in Mahindra Two Wheelers Ltd.Document54 pagesRecruitment and Recruitment Process in Mahindra Two Wheelers Ltd.Anonymous oBv3VW8No ratings yet
- Mutual Fund Term PaperDocument20 pagesMutual Fund Term PaperManish GuptaNo ratings yet
- Free Tests - Kap-Test & Princeton Review PDFDocument3 pagesFree Tests - Kap-Test & Princeton Review PDFAbhiroop AjithNo ratings yet
- Marketing Plan Project of NLC Pearl..Document22 pagesMarketing Plan Project of NLC Pearl..King KafeelNo ratings yet
- Berico vs. CADocument2 pagesBerico vs. CAKirsten Denise B. Habawel-VegaNo ratings yet
- API 653 - ASME Section V - NDE Practice Questions - 68 TermsDocument7 pagesAPI 653 - ASME Section V - NDE Practice Questions - 68 TermsSERFORTEC CIA. LTDA.No ratings yet
- DRAFT CIOB Code of Quality ManagementDocument98 pagesDRAFT CIOB Code of Quality ManagementKeith Cubero100% (1)
- Karlos KarlinaDocument2 pagesKarlos KarlinaTip RendahNo ratings yet
- DBA ChecklistDocument3 pagesDBA ChecklistBhuvnesh PandeyNo ratings yet
- Jdthomas 7 ADocument22 pagesJdthomas 7 AJeffrey ThomasNo ratings yet
- Fisa Tehnica Contact Magnetic SM35Document2 pagesFisa Tehnica Contact Magnetic SM35Alin ChiperNo ratings yet
- SM-T587P (Phonelumi Com)Document81 pagesSM-T587P (Phonelumi Com)Tomaso SulisNo ratings yet
- MF TyreMF Swift6.2 InstallationGuideDocument20 pagesMF TyreMF Swift6.2 InstallationGuidetrisinoNo ratings yet
- Dennis Funa Vs The Chairman, Comission On Audit, Reynaldo Villar GR 192791 (April 24, 2012)Document2 pagesDennis Funa Vs The Chairman, Comission On Audit, Reynaldo Villar GR 192791 (April 24, 2012)Lu Cas100% (1)
- 4769 10 LedDocument3 pages4769 10 LedAlejandro Paez DiazNo ratings yet
- Statics All in OneDocument120 pagesStatics All in OneSaad Salman100% (1)
- Evraz Highveld SteelDocument6 pagesEvraz Highveld SteelCaio VaccariNo ratings yet
- STP For Rural MarketsDocument16 pagesSTP For Rural MarketsGowri Sankar100% (5)
- Amc 12a8 SpecsheetDocument9 pagesAmc 12a8 SpecsheetElectromateNo ratings yet
- Crimes Commited by Public OfficersDocument51 pagesCrimes Commited by Public OfficersJaime M. Palattao Jr.100% (1)
- Report Project ManagementDocument36 pagesReport Project ManagementVarun Mathur100% (1)
- US Certified Management Accountant (CMA)Document8 pagesUS Certified Management Accountant (CMA)HussainNo ratings yet
- Course of Study - Högskolan I GävleDocument1 pageCourse of Study - Högskolan I GävlekamranNo ratings yet
- The Theory of Stock Market EfficiencyDocument21 pagesThe Theory of Stock Market EfficiencyMario Andres Rubiano RojasNo ratings yet
- Microprocessors Lab Manual 408331: Hashemite UniversityDocument63 pagesMicroprocessors Lab Manual 408331: Hashemite UniversitytargetNo ratings yet
- Cushman & Wakefield - Data Center Global Cloud Report Summer 2020Document4 pagesCushman & Wakefield - Data Center Global Cloud Report Summer 2020HashNo ratings yet