Professional Documents
Culture Documents
Ds Cyber Physical Threat Intelligence
Uploaded by
abdel taibOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Ds Cyber Physical Threat Intelligence
Uploaded by
abdel taibCopyright:
Available Formats
data sheet
Cyber Physical
Threat Intelligence
Zero in on attacks against complex, interconnected,
software-managed physical systems
The increasing importance of communication technologies across different
industries has driven a growing integration of digital features that support
the control and maintenance of physical processes. This intersection of the
virtual and the physical has led to not only revolutionary connectivity and
instrumentation, but also to significant safety and security risks.
It is becoming more important to proactively learn and share technical
HIGHLIGHTS vulnerabilities and viable threat actor tactics, techniques and procedures
• Analysis and reporting on (TTPs), so that cyber physical attacks can be anticipated and prevented.
cyber physical vulnerabilities
FireEye Cyber Physical Threat Intelligence is a subscription service that
• Technical analysis of cyber
provides context, data and actionable analysis around threats to cyber-physical
physical-focused threat
actor TTPs systems, including operational technology, industrial control systems, Internet of
Things and other equipment used to support physical processes in, for example,
• All-source intelligence analysis the telecommuncation and medical sectors.
of cyber physical threats
What Your Subscription Offers
• Analysis of operational
For organizations tasked with maintaining the security and continuity of
technology-focused news
and research these systems, Cyber Physical Intelligence provides early warning on critical
vulnerabilities, as well as the threat campaigns and adversaries targeting them.
• Access to educational content With Cyber Physical Intelligence, security teams can stay ahead of attackers
to increase security awareness
and make better-informed decisions about the security posture of their cyber
across your team
physical systems.
The Cyber Physical Intelligence subscription includes in-depth reporting
on cyber physical-focused malware and malicious tactics, techniques and
procedures, threat actors, threat activity, vulnerabilities and strategic insights.
Table 1 lists the critical coverage areas where FireEye provides in-depth
intelligence for teams tasked with defending these systems.
DATA SHEET | FIREEYE INTELLIGENCE CYBER PHYSICAL THREAT INTELLIGENCE
Table 1. Coverage areas of FireEye Cyber Physical Threat Intelligence.
Coverage Area Description
Current Intelligence Tactical and strategic analysis of threat activity, derived from FireEye Mandiant engagements, deployed
FireEye technology and extensive network of FireEye sensors deployed worldwide.
Cyber Physical Reference Review of terminology, network architecture, ICS ports and protocol security and cyber physical-focused
threat actors.
Cyber Physical Vulnerabilities Tactical reporting on ICS vulnerabilities.
ICS Network Activity Analysis of network traffic on ICS ports based on firewall logs data.
ICS Security Roundup Collection, analysis and implications of ICS publications in media.
FireEye Mandiant-Sourced Ongoing review of Mandiant engagements that examines trending data and security best practices.
Tools and Research Research and analysis of ICS-focused reconnaissance and attack tools.
Stay Ahead of the Next Generation of Threats
Cyber physical systems come with a complex set of benefits and risks. To anticipate and block threats that target cyber
physical systems, you must maintain current information on the unique security requirements of these technologies:
• Increase awareness of relevant cyber physical security • Make better-informed decisions about your evolving
vulnerabilities and support vulnerability management cyber physical security program and controls.
efforts through FireEye vulnerability scoring and analysis • Get actionable intelligence to help evolve your
of remediation options. cyber physical risk management posture from reactive
• Gain situational awareness of threats, campaigns and to proactive.
actors targeting your cyber physical systems.
• Educate your internal teams and external stakeholders
with in-depth reference material and topical event
coverage tailored to the cyber physical world.
For more information about how FireEye Cyber Physical Intelligence can help your security
team make better-informed security decisions, www.FireEye.com
FireEye, Inc. About FireEye, Inc.
601 McCarthy Blvd. Milpitas, CA 95035 FireEye is the intelligence-led security company.
408.321.6300/877.FIREEYE (347.3393) Working as a seamless, scalable extension of customer
info@FireEye.com security operations, FireEye offers a single platform
that blends innovative security technologies, nation-
state grade threat intelligence, and world-renowned
©2019 FireEye, Inc. All rights reserved. FireEye is Mandiant® consulting. With this approach, FireEye
a registered trademark of FireEye, Inc. All other eliminates the complexity and burden of cyber security
brands, products, or service names are or may be
trademarks or service marks of their respective
for organizations struggling to prepare for, prevent and
owners. I-EXT-DS-US-EN-000258-01 respond to cyber attacks.
You might also like
- Tinas Resturant AnalysisDocument19 pagesTinas Resturant Analysisapi-388014325100% (2)
- Cash Flow Statement and Balance Sheet of A Solar Power Plant in APDocument35 pagesCash Flow Statement and Balance Sheet of A Solar Power Plant in APSriharsha Vavilala100% (1)
- Auditing Case 3Document12 pagesAuditing Case 3Kenny Mulvenna100% (6)
- BSBXCS402 PresentationDocument27 pagesBSBXCS402 PresentationAlejandro Bejarano GarciaNo ratings yet
- Cyber Security PDFDocument16 pagesCyber Security PDFSucharita Sarkar100% (1)
- CSMS. Cyber Security Management System. Conformity Assessment SchemeDocument8 pagesCSMS. Cyber Security Management System. Conformity Assessment Schemeabdel taibNo ratings yet
- HMSWeb - Handover Management SystemDocument21 pagesHMSWeb - Handover Management SystemGG GRNo ratings yet
- Security Tactics For People, Processes, and TechnologyDocument6 pagesSecurity Tactics For People, Processes, and TechnologyAleir PinsalaNo ratings yet
- Security Threat Intelligence May2018Document2 pagesSecurity Threat Intelligence May2018Thanh Tu NguyenNo ratings yet
- Cyber Law Cyber Crime & IPR NotesDocument33 pagesCyber Law Cyber Crime & IPR NotesPRAVEEN M RNo ratings yet
- Cyber Security Digital Forensics WorkDocument6 pagesCyber Security Digital Forensics Workokware brianNo ratings yet
- Head of Information SecurityDocument2 pagesHead of Information SecurityazzuNo ratings yet
- SB Network SecurityDocument4 pagesSB Network SecurityScribdUser4321No ratings yet
- CS Ca2Document10 pagesCS Ca2Ayushi PaulNo ratings yet
- An Investigation On Cyber Security Threats, Taxonomy and ChallengesDocument12 pagesAn Investigation On Cyber Security Threats, Taxonomy and Challengeszeenia ahmedNo ratings yet
- Bitdefender Advanced Threat Intelligence DatasheetDocument2 pagesBitdefender Advanced Threat Intelligence Datasheettoretta1984No ratings yet
- Ics Cybersecurity For The C-Level: Six Questions Every C-Level Executive Should Be AskingDocument2 pagesIcs Cybersecurity For The C-Level: Six Questions Every C-Level Executive Should Be AskingAvinash ChoudhariNo ratings yet
- IBM I2 Enterprise Insight Analysis For Cyber Threat HuntingDocument8 pagesIBM I2 Enterprise Insight Analysis For Cyber Threat HuntingmaxventoNo ratings yet
- Fundamental of Computer SecurityDocument8 pagesFundamental of Computer SecuritymichealNo ratings yet
- Cyber Snapshot Issue 4Document39 pagesCyber Snapshot Issue 4Bekim KrasniqiNo ratings yet
- Defining Threat Intelligence Analysis SlidesDocument16 pagesDefining Threat Intelligence Analysis SlideswaruenkNo ratings yet
- Part 1 Cybersecurity - Competency - Guide - Cyber Security Regulatory Context and and Practice Standards Day 1 by MITDocument100 pagesPart 1 Cybersecurity - Competency - Guide - Cyber Security Regulatory Context and and Practice Standards Day 1 by MITJason KingNo ratings yet
- AUDCIS Information SecurityDocument21 pagesAUDCIS Information SecurityBea GarciaNo ratings yet
- Avasant Cybersecurity ServicesDocument29 pagesAvasant Cybersecurity Services19. meilina salsabilaNo ratings yet
- Cyber Security Masterclass Venue Birchwood Hotel 18th-22nd FebruaryDocument4 pagesCyber Security Masterclass Venue Birchwood Hotel 18th-22nd FebruaryUlisses TembeNo ratings yet
- Fortiguard Labs: Threat Intelligence and Research at FortinetDocument7 pagesFortiguard Labs: Threat Intelligence and Research at FortinetjohnNo ratings yet
- Cyber-Security-Infographic - FCADocument1 pageCyber-Security-Infographic - FCAMousumi Utkarsh RayNo ratings yet
- Prevent Security Threats with Effective Cyber Defence ControlsDocument8 pagesPrevent Security Threats with Effective Cyber Defence ControlsOfrates SiringanNo ratings yet
- Cyber Security Lesson 2Document26 pagesCyber Security Lesson 2Ushna AbrarNo ratings yet
- CT Report2Document38 pagesCT Report2narayan.barmanNo ratings yet
- Transforming Cyber Defense: With 360 Degree MDR ServicesDocument14 pagesTransforming Cyber Defense: With 360 Degree MDR ServicesRamesh KumarNo ratings yet
- BAE Systems Cyber Threat Intelligence BrochureDocument12 pagesBAE Systems Cyber Threat Intelligence BrochureIslahNo ratings yet
- Cyber Security Process and TechnologiesDocument8 pagesCyber Security Process and TechnologiesSyeda Narjis BatoolNo ratings yet
- Endpoint Security Safeguarding The Digital PerimeterDocument10 pagesEndpoint Security Safeguarding The Digital PerimeterfindinngclosureNo ratings yet
- Introduction To CybersecurityDocument15 pagesIntroduction To CybersecurityJozebel Cardoso100% (1)
- 146.editedDocument11 pages146.editedTonnie KiamaNo ratings yet
- Ds Threat Intel FoundationsDocument3 pagesDs Threat Intel FoundationsDORGNo ratings yet
- Cyber-Security ReviewerDocument3 pagesCyber-Security ReviewerEmmanuel AlcantaraNo ratings yet
- Extending Security Intelligence With Big Data SolutionsDocument8 pagesExtending Security Intelligence With Big Data SolutionsYashNo ratings yet
- Running Head: CYBERSECURITY 1Document11 pagesRunning Head: CYBERSECURITY 1Tonnie KiamaNo ratings yet
- CS - AI Improved Presentation V2Document22 pagesCS - AI Improved Presentation V2Tzar UmangNo ratings yet
- Introduction To Network SecurityDocument8 pagesIntroduction To Network Security1032210345No ratings yet
- Cybersecurity Incident Response - How To Survive An AttackDocument26 pagesCybersecurity Incident Response - How To Survive An Attacka50% (2)
- InsiderThreatCyberFrameworkWebtool Paper V22Document10 pagesInsiderThreatCyberFrameworkWebtool Paper V22Mogabs MogabsNo ratings yet
- Cybriant Partner Partner Program White Label MaterialsDocument7 pagesCybriant Partner Partner Program White Label MaterialsL CaroliNo ratings yet
- 6169 1 SMDocument4 pages6169 1 SMas1as2as3No ratings yet
- Cyber Security Risk Assessment and ManagementDocument30 pagesCyber Security Risk Assessment and ManagementoinkNo ratings yet
- White Paper - Defending InfrastructureDocument20 pagesWhite Paper - Defending InfrastructureDan McClintockNo ratings yet
- Ds Threat Intelligence JumpstartDocument2 pagesDs Threat Intelligence JumpstartDORGNo ratings yet
- Matter CtiDocument29 pagesMatter CtiNaina NNo ratings yet
- E-Brochure Schneider Electric's Cybersecurity ServicesDocument8 pagesE-Brochure Schneider Electric's Cybersecurity ServicesGiovane PucciNo ratings yet
- Technical and Organizational MeasuresDocument9 pagesTechnical and Organizational MeasuressilveR staRNo ratings yet
- Rapid7 Penetration Testing Service BriefDocument2 pagesRapid7 Penetration Testing Service BrieftonerangerNo ratings yet
- FTP InfoDocument5 pagesFTP Infomel adamsNo ratings yet
- Coi On Singhealth Cyber Attack 201901Document10 pagesCoi On Singhealth Cyber Attack 201901magicuser21No ratings yet
- CBTS Penetration Testing Security IFS 230223Document2 pagesCBTS Penetration Testing Security IFS 230223adminakNo ratings yet
- Catalogue 2017 Css enDocument28 pagesCatalogue 2017 Css enhangtuah79No ratings yet
- Compromise Assessment - Datasheet_ControlledDocument2 pagesCompromise Assessment - Datasheet_Controlleddigitlabs.marketingNo ratings yet
- OT For Industry 4.0Document26 pagesOT For Industry 4.0Febryn Pradana Rifanda PutraNo ratings yet
- Bitdefender GravityZone Business Security Premium Datasheet enDocument2 pagesBitdefender GravityZone Business Security Premium Datasheet enHalaNo ratings yet
- The Significance of Cybersecurity in Somali Businesses and Government OrganizationsDocument21 pagesThe Significance of Cybersecurity in Somali Businesses and Government OrganizationsHussein SabrieNo ratings yet
- Chapter 1 Information Assurance and SecuDocument73 pagesChapter 1 Information Assurance and SecuCAPINPIN SerelynNo ratings yet
- Cdccont 0900aecd80272e64Document9 pagesCdccont 0900aecd80272e64api-26244718No ratings yet
- CYBER SECURITY HANDBOOK Part-2: Lock, Stock, and Cyber: A Comprehensive Security HandbookFrom EverandCYBER SECURITY HANDBOOK Part-2: Lock, Stock, and Cyber: A Comprehensive Security HandbookNo ratings yet
- CompTIA CySA+ Certification The Ultimate Study Guide to Practice Questions With Answers and Master the Cybersecurity Analyst ExamFrom EverandCompTIA CySA+ Certification The Ultimate Study Guide to Practice Questions With Answers and Master the Cybersecurity Analyst ExamNo ratings yet
- QNAP NAS Vs HVE NASDocument1 pageQNAP NAS Vs HVE NASabdel taibNo ratings yet
- SY-5005005 HMI EngineersManualDocument136 pagesSY-5005005 HMI EngineersManualabdel taibNo ratings yet
- b0193df MDocument182 pagesb0193df MFrancis RodríguezNo ratings yet
- LB Cybersecurity WEB PDFDocument172 pagesLB Cybersecurity WEB PDFaminymohammedNo ratings yet
- Sns-En-Cli Console SSH Commands Reference Guide-V3Document97 pagesSns-En-Cli Console SSH Commands Reference Guide-V3abdel taibNo ratings yet
- Geh 6859Document18 pagesGeh 6859abdel taibNo ratings yet
- Geh 4839 PDFDocument2 pagesGeh 4839 PDFabdel taibNo ratings yet
- TS 883xu RP E2124 8GDocument2 pagesTS 883xu RP E2124 8Gabdel taibNo ratings yet
- b0700sz CDocument70 pagesb0700sz Cabdel taibNo ratings yet
- BHCS38951 Nexus Controls OTArmor Cyber Asset Protection Factsheet - R1Document4 pagesBHCS38951 Nexus Controls OTArmor Cyber Asset Protection Factsheet - R1abdel taibNo ratings yet
- Cyber Security Implications of SIS Integration With Control NetworksDocument34 pagesCyber Security Implications of SIS Integration With Control Networksabdel taibNo ratings yet
- b0860rg BDocument34 pagesb0860rg Babdel taibNo ratings yet
- b0860rr BDocument28 pagesb0860rr Babdel taibNo ratings yet
- b0860rn BDocument16 pagesb0860rn Babdel taibNo ratings yet
- b0860rw ADocument22 pagesb0860rw Aabdel taibNo ratings yet
- b0700sn HDocument60 pagesb0700sn Habdel taibNo ratings yet
- Foxboro Evo™ Process Automation System: Product SpecificationsDocument8 pagesFoxboro Evo™ Process Automation System: Product Specificationsabdel taibNo ratings yet
- b0700sn GDocument62 pagesb0700sn Gabdel taibNo ratings yet
- Asa 5512xDocument12 pagesAsa 5512xabdel taibNo ratings yet
- H92 Current CablingDocument9 pagesH92 Current Cablingabdel taibNo ratings yet
- H92 Archival CablingDocument5 pagesH92 Archival Cablingabdel taibNo ratings yet
- Cisco ASA ASDM Configuration: SearchDocument4 pagesCisco ASA ASDM Configuration: Searchabdel taibNo ratings yet
- DLP 9.3P5 On ePO 5.3.0 Installation DocumentDocument3 pagesDLP 9.3P5 On ePO 5.3.0 Installation Documentabdel taibNo ratings yet
- I/A Series System V8.2 Release Notes and Installation ProceduresDocument182 pagesI/A Series System V8.2 Release Notes and Installation Proceduresabdel taibNo ratings yet
- Lead Instrument System AnalystDocument1 pageLead Instrument System Analystabdel taibNo ratings yet
- Global insurance capital standard FAQs updated July 2017Document9 pagesGlobal insurance capital standard FAQs updated July 2017abdel taibNo ratings yet
- Rare Case of Dunbar SyndromeDocument3 pagesRare Case of Dunbar Syndromeabdel taibNo ratings yet
- Ds Epolicy OrchestratorDocument7 pagesDs Epolicy Orchestratorabdel taibNo ratings yet
- Prison Architect Calculator (V2.0)Document11 pagesPrison Architect Calculator (V2.0)freakman89No ratings yet
- BTP Presentation - Sem 8Document24 pagesBTP Presentation - Sem 8Nihal MohammedNo ratings yet
- CRAPAC Monthly JanDocument4 pagesCRAPAC Monthly JanJasonMortonNo ratings yet
- Experiment No. 5 BCD To 7-Segment Decoder/Driver: I.ObjectivesDocument9 pagesExperiment No. 5 BCD To 7-Segment Decoder/Driver: I.ObjectivesJun TobiasNo ratings yet
- Petition For ReviewDocument18 pagesPetition For ReviewJay ArNo ratings yet
- The Influence of Culture Subculture On Consumer BehaviorDocument55 pagesThe Influence of Culture Subculture On Consumer Behaviorvijendra chanda100% (12)
- Davall Stock Gears Worm Wheel Gear Sets 17pages PDFDocument17 pagesDavall Stock Gears Worm Wheel Gear Sets 17pages PDFharish ahireNo ratings yet
- Comments PRAG FinalDocument13 pagesComments PRAG FinalcristiancaluianNo ratings yet
- RAN15.0 Feature ListDocument34 pagesRAN15.0 Feature ListmyososNo ratings yet
- DMT L4.Technical English & Communication (Information & Assignment)Document80 pagesDMT L4.Technical English & Communication (Information & Assignment)Eng Teik PhungNo ratings yet
- SQL Server Management Studio Database Engine Query Editor Window - Microsoft DocsDocument6 pagesSQL Server Management Studio Database Engine Query Editor Window - Microsoft DocsAchamyeleh TamiruNo ratings yet
- 12.CEH Module 3 Assignment 3.1Document7 pages12.CEH Module 3 Assignment 3.1piyuhNo ratings yet
- Irrigation Management and Development PlanDocument5 pagesIrrigation Management and Development PlanRTL JRNo ratings yet
- MCP Lab Manual C-16Document62 pagesMCP Lab Manual C-16siri.pogula67% (6)
- People V VillanuevaDocument2 pagesPeople V VillanuevaLavernaNo ratings yet
- Incidentrequest Closed Monthly JunDocument250 pagesIncidentrequest Closed Monthly Junأحمد أبوعرفهNo ratings yet
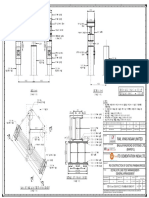
- Routine Pile Load Test-Ga-13.04.2021Document1 pageRoutine Pile Load Test-Ga-13.04.2021Digambar JadhavNo ratings yet
- Auditing Theory - Audit ReportDocument26 pagesAuditing Theory - Audit ReportCarina Espallardo-RelucioNo ratings yet
- Sjzl20061019-ZXC10 BSCB (V8.16) Hardware ManualDocument69 pagesSjzl20061019-ZXC10 BSCB (V8.16) Hardware ManualAhmadArwani88No ratings yet
- Gek 106852aDocument10 pagesGek 106852awednetoxNo ratings yet
- AfghanistanLML OnlinDocument117 pagesAfghanistanLML Onlinعارف حسینNo ratings yet
- PE6705 Water Flooding and Enhanced Oil Recovery L T P C 3 0 0 3 Objective: Unit I 9Document6 pagesPE6705 Water Flooding and Enhanced Oil Recovery L T P C 3 0 0 3 Objective: Unit I 9Prince ImmanuelNo ratings yet
- JBNBNBNBNBNBDocument4 pagesJBNBNBNBNBNBmaheshNo ratings yet
- Baja2018 Unisa Team3 Design ReportDocument23 pagesBaja2018 Unisa Team3 Design ReportDaniel MabengoNo ratings yet
- Veritas d1.6.1 FinalDocument28 pagesVeritas d1.6.1 FinalgkoutNo ratings yet
- Operating Instructions MA 42 - Maico Diagnostics PDFDocument28 pagesOperating Instructions MA 42 - Maico Diagnostics PDFJuan PáezNo ratings yet