Professional Documents
Culture Documents
CISO Mindmap-2023
Uploaded by
Rodrigo BenaventeOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
CISO Mindmap-2023
Uploaded by
Rodrigo BenaventeCopyright:
Available Formats
Security
Operations
Resilience
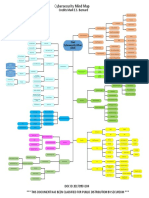
CISO MindMap 2023
Threat Prevention Threat Detection Incident Management
(NIST CSF Identify & Protect) (NIST CSF Detect) (NIST CSF Respond & Recover)
Network/Application Log Analysis/correlation/SIEM Create adequate
Firewalls Incident Response
Alerting (IDS/IPS, FIM, capability
Vulnerability WAF, Antivirus, etc)
What do Security Professionals Really do?
Management Media Relations
NetFlow analysis
Incident Readiness Assessment
DLP
Scope Forensic Investigation
Threat hunting and Insider threat
Data Breach
Operating Systems MSSP integration Preparation
Network Devices Threat Detection
capability assessment
Update and Test
Applications
Incident Response Plan
Databases Gap assessment Set Leadership
Code Review Expectations
Prioritization to fill gaps
Physical Security Business Continuity
Security Projects SOC Operations Plan
Cloud misconfiguration testing
Business Case Development Forensic and IR
Mobile Devices & Apps SOC Resource Mgmt Partner, retainer
Alignment with IT Projects
Attack surface management SOC Staff continuous training Adequate Logging
Balance FTE and contractors
IoT Shift management Breach exercises
Balancing budget for (e.g. simulations)
People, Trainings, and OT/SCADA SOC procedures
Tools/Technology Budget First responders
Identify SOC Metrics and Reports Training
CapEx and OpEx considerations
SOC and NOC Integration Ransomware
Cyber Risk Insurance
Periodic (or continuous) SOC Tech stack management
Technology amortization
Comprehensive Threat Intelligence Feeds Identify critical systems
Retire redundant & under utilized tools and proper utilization
Classify Perform ransomware BIA
SOC DR exercise
Tie with BC/DR Plans
Acquisition Risk Assessment Risk Based Approach Partnerships with ISACs
Devise containment
Long term trend analysis strategy
Network/Application/Cloud Integration Cost Prioritize
Mergers and Acquisitions Ensure adequate backups
Mitigation (Fix, verify) Unstructured data from IoT
Identity Management
Integrate new data Periodic backup test
Security tools rationalization Measure
sources (see areas
Offline backups in case
Multi-Cloud architecture under skills development)
backup is ransomed.
Baseline Skills Development
Strategy and Guidelines Mock exercises
Metric
Cloud Security Posture Management (CSPM) Implement machine
Application Machine Learning integrity checking
Ownership/Liability/Incidents Security Skill Development
Automation and SOAR
Vendor's Financial Strength
Understand
Algorithm Biases
SLAs Application Development
Standards Playbooks
IOT
Infrastructure Audit
Secure Code Supply chain incident mgmt
Autonomous
Proof of Application Security Training and Review Vehicles
SaaS Strategy
Disaster Recovery Posture Application Vulnerability Testing Drones Keep inventory
Cloud Computing of software
Application Architecture Change Control Medical Devices components
File Integrity Monitoring
Integration of Identity
Industrial Control Integrate into
Management/Federation/SSO Web Application Firewall Systems (ICS) vulnerability mgmt
SaaS Policy and Guidelines Integration to SDLC Blockchain & Integrate into
and Project Delivery Smart Contracts
Cloud log integration/APIs SDLC and risk
Inventory open source components mgmt process
VIrtualized security appliances MITRE ATT&CK
Source code supply chain security Managing relationships
Cloud-native apps security Soft skills with law enforcement
API Security Human experience
Containers-to-container communication security
IPS DevOps Integration
Service mesh, micro services
Identity Management Prepare for unplanned work
serverless computing security
DLP Use of AI and Data Analytics
Technology advancements
Anti Malware, Anti-spam
Lost/Stolen devices
Mobile Technologies Proxy/Content Filtering Use of computer
BYOD and MDM (Mobile Device Management)
vision in physical
DNS security/ filtering security
Mobile Apps Inventory
Patching Log Anomaly Detection
HR/On Boarding/Termination
Processes DDoS Protection ML model training, retraining
Business Partnerships
Hardening guidelines Red team/blue team exercises (and whatever you want to call them)
Agility, Business Continuity and Disaster Recovery Business Enablement
Desktop security Integrate threat intelligence platform (TIP)
Understand industry trends (e.g. retail, financials, etc)
Encryption, SSL Deception technologies
Evaluating Emerging Technologies (Quantum, Crypto, Blockchain etc.)
for breach detection
PKI
IOT Frameworks
Full packet inspection
Security Health Checks
Hardware/Devices security features
Detect misconfigurations
Public software repositories
IOT Communication Protocols
Device Identity, Auth and Integrity
Over the Air updates Identity Credentialing
Track and Trace Account Creation/Deletions
Condition Based Monitoring
IOT
Last update: March 25, 2023 Single Sign On (SSO, Simplified sign on)
Expiration date: June 30, 2024
Customer Experience Repository (LDAP/Active Directory, Cloud Identity, Local ID stores)
IOT Use cases
Smart Grid Federation, SAML, Shibboleth
Smart Cities / Communities
Others ...
Twitter: @rafeeq_rehman 2-Factor (multi-factor) Authentication - MFA
Role-Based Access Control
IoT SaaS Platforms Downloads: http://rafeeqrehman.com Ecommerce and Mobile Apps
Data Analytics Password resets/self-service
Augmented and Virtual Reality HR Process Integration
Train InfoSec teams Integrating cloud-based identities
Identity Management
Secure models IoT device identities
Securing training and test data IAM SaaS solutions
Adversarial attacks Artificial Intelligence Unified identity profiles
Chatbots and NLP InfoSec Professionals Password-less authentication
Voice signatures
Deep fakes
Responsibilities Face recognition
ChatGPT phenomenon IAM with Zero Trust technologies
Drones Privileged access management
5G use cases and security Use of public identity OAuth
(Google, FB etc.)
Edge Computing OpenID
Digital Certificates
Embedding security in Requirements
Design reviews Strategy and business alignment
Security Testing Project Delivery Lifecycle Security policies, standards
Certification and Accreditation COSO
COBIT
ISO
Traditional Network Segmentation
Risk Mgmt/Control Frameworks ITIL
Micro segmentation strategy
NIST - relevant NIST standards and guidelines
Application protection
FAIR
Defense-in-depth
Visibility across multiple frameworks
Remote Access
Resource Management
Encryption Technologies
Roles and Responsibilities
Backup/Replication/Multiple Sites Governance
Data Ownership, sharing, and data privacy
Cloud/Hybrid/Multiple Cloud Vendors Security Architecture
Conflict Management
Software Defined Networking
Operational Metrics
Network Function Virtualization
Metrics and Reporting Executive Metrics and Reporting
Zero trust models and roadmap
Validating effectiveness of metrics
SASE/SSE strategy, vendors
IT, OT, IoT/IIoT Convergence
Overlay networks, secure enclaves
Explore options for cooperative SOC, collaborative infosec
Multi-Cloud architecture
Tools and vendors consolidation
Evaluating control effectiveness
CCPA, GDPR & other data privacy laws
Maintaining a roadmap/plan for 1-3 years
PCI
SOX
Aligning with Corporate
HIPAA and HITECH
Objectives
Regular Audits
Compliance and Audits Continuous Mgmt Updates, metrics
SSAE 18
Innovation and Value Creation
NIST/FISMA
Expectations Management
Executive order on improving the Nation's Cybersecurity
Selling InfoSec (Internal Branding)
Build project business cases
Other compliance needs
Show progress/ risk reduction
ROSI
Data Discovery and Data Ownership
Vendor Contracts
Enable Secure Application access
Investigations/Forensics
Secure expanded attack surface
Attorney-Client Privileges Legal and Human Resources Work from Home
Security of sensitive data accessed from home
Data Retention and Destruction
Team development, talent management
Automate patching
Secure DevOps, DevSecOps
Physical Security
Embedding security tools in CI/CD pipelines
Vulnerability Management
Automate threat hunting
Ongoing risk assessments/pen testing
Automate risk scoring
Integration to Project Delivery (PMO)
Automation Automate asset inventory
Code Reviews
Security infrastructure as code
Use of Risk Assessment Methodology and framework
Automate API inventory
Policies and Procedures
Automate risk register
Testing effectiveness Phishing and Associate Awareness
Automate security metrics
Data Discovery
Data Classification
Focus Areas for 2023-24
Access Control
Data Centric
Data Loss Prevention - DLP Approach
Partner Access
Risk Management
Encryption/Masking
Monitoring and Alerting
Industrial Controls
1. Increase attention on resilience
Systems
PLCs
2. Reduce and consolidate security tools and vendors
3. Build a brand for security team
Operational Technologies
SCADA
HMIs
Integrate threat intelligence 4. Untangle application web of components
Vendor risk management
Cyber Risk Quantification (CRQ)
5. Build expertise in emerging technologies
Risk Register
Loss, Fraud prevention
6. Create a security automation role
© Copyright 2012-2023 - Rafeeq Rehman
You might also like
- Cybersecurity Mind Map V01R04 DOC ID 2017095Document1 pageCybersecurity Mind Map V01R04 DOC ID 2017095James HowlettNo ratings yet
- Ciso Mindmap PDFDocument1 pageCiso Mindmap PDFPalanichamy P ECE studentNo ratings yet
- CRISC BrochureDocument2 pagesCRISC BrochureSpipparisNo ratings yet
- Cyber Security Controls ChecklistDocument12 pagesCyber Security Controls ChecklistpopsalldayNo ratings yet
- 2020 Salary Survey Report PDFDocument42 pages2020 Salary Survey Report PDFMatthew Burke100% (1)
- DOCUMENT Information Systems Security Officer: Roles and ResponsibilitiesDocument19 pagesDOCUMENT Information Systems Security Officer: Roles and ResponsibilitiesmabesninaNo ratings yet
- The CISO Survival Guide 2018Document14 pagesThe CISO Survival Guide 2018Andrés AlmanzaNo ratings yet
- Four Ciso Tribes and Where To Find Them: Gary Mcgraw, Ph.D. Sammy Migues Brian Chess, PH.DDocument24 pagesFour Ciso Tribes and Where To Find Them: Gary Mcgraw, Ph.D. Sammy Migues Brian Chess, PH.Docruz80No ratings yet
- Investing in CybersecurityDocument78 pagesInvesting in CybersecurityKriminologinjaNo ratings yet
- Cybersecurity Domains 3.1Document1 pageCybersecurity Domains 3.1Shun KamNo ratings yet
- API Gateway SecurityDocument1 pageAPI Gateway Securityabhi4wit0% (1)
- How To Become Certified in Risk and Information Systems Control Cert Prep Guide Global Knowledge Us enDocument8 pagesHow To Become Certified in Risk and Information Systems Control Cert Prep Guide Global Knowledge Us entakundaNo ratings yet
- Some Thoughts On Taking The CISSPDocument6 pagesSome Thoughts On Taking The CISSPCarolina MarinangeliNo ratings yet
- The CISO's Guide To Your First 100 Days: Key FindingsDocument19 pagesThe CISO's Guide To Your First 100 Days: Key FindingsDhanysha PutriNo ratings yet
- ISF SOGP 2020 Executive Summary 1Document3 pagesISF SOGP 2020 Executive Summary 1El lomoNo ratings yet
- A Shift From Cybersecurity To Cyber Resilience: EbookDocument13 pagesA Shift From Cybersecurity To Cyber Resilience: EbookchuresashyNo ratings yet
- Cybersecurity Snapshot February 2022Document1 pageCybersecurity Snapshot February 2022Kiran KherNo ratings yet
- How to detect and avoid phishing scamsDocument1 pageHow to detect and avoid phishing scamsRonna Mae RedublaNo ratings yet
- EY Security Operations Centers Helping You Get Ahead of Cybercrime PDFDocument20 pagesEY Security Operations Centers Helping You Get Ahead of Cybercrime PDFLuis SosaNo ratings yet
- 2015 UW-Madison Cybersecurity Strategic Plan Final Jul-01-2015Document47 pages2015 UW-Madison Cybersecurity Strategic Plan Final Jul-01-2015Hiba AfanehNo ratings yet
- SANS CISO Scorecard v1.2Document1 pageSANS CISO Scorecard v1.2Shun KamNo ratings yet
- Company Profile Punggawa CybersecurityDocument25 pagesCompany Profile Punggawa CybersecurityRys YantiNo ratings yet
- Kaspersky Security Awareness Training BrochureDocument10 pagesKaspersky Security Awareness Training Brochurematar LONo ratings yet
- Cyber Security Planning GuideDocument92 pagesCyber Security Planning Guidesolo4000No ratings yet
- Google Cloud Platform SecurityDocument11 pagesGoogle Cloud Platform SecurityEna Popovska0% (1)
- Threat Modelling Vs Risk AssessmentDocument11 pagesThreat Modelling Vs Risk AssessmentAlexander OniNo ratings yet
- Cybersecurity Incident Response - How To Survive An AttackDocument26 pagesCybersecurity Incident Response - How To Survive An Attacka50% (2)
- Cyber Handbook EnterpriseDocument38 pagesCyber Handbook EnterprisehackerNo ratings yet
- The CISO ViewDocument18 pagesThe CISO ViewPradeep JoshiNo ratings yet
- Cisco Cybersecurity Innovation DayDocument1 pageCisco Cybersecurity Innovation DayYunus SubektiNo ratings yet
- The CIS Community Attack ModelDocument13 pagesThe CIS Community Attack Modela2304404No ratings yet
- Become A Next-Gen CISODocument33 pagesBecome A Next-Gen CISOjesus_yustasNo ratings yet
- How To Align Security With Your Strategic Business Objectives PDFDocument71 pagesHow To Align Security With Your Strategic Business Objectives PDFtenwa100% (1)
- Cybersecurity: Sector Update - April 2021Document30 pagesCybersecurity: Sector Update - April 2021Anurag MehtaNo ratings yet
- Security Awareness TrainingDocument25 pagesSecurity Awareness TrainingDaniel IdongesitNo ratings yet
- Forged by The Pandemic: The Age of Privacy: Cisco 2021 Data Privacy Benchmark StudyDocument23 pagesForged by The Pandemic: The Age of Privacy: Cisco 2021 Data Privacy Benchmark StudyJohn GlassNo ratings yet
- Solution Brief Managed Detection and Response MDR PDFDocument2 pagesSolution Brief Managed Detection and Response MDR PDFnicolepetrescuNo ratings yet
- Advancing Cyber Resilience Principles and Tools For BoardsDocument40 pagesAdvancing Cyber Resilience Principles and Tools For BoardsCristian VargasNo ratings yet
- CISSP Domain One: Security and Risk Management-What You Need To Know For The ExamDocument14 pagesCISSP Domain One: Security and Risk Management-What You Need To Know For The ExamLaptop salesNo ratings yet
- Inspira Coprorate Profile - Jan 2020Document36 pagesInspira Coprorate Profile - Jan 2020Sachin AnchalNo ratings yet
- Information Security Assessment ProcessDocument23 pagesInformation Security Assessment ProcessNarender KumarNo ratings yet
- Astra Security Sample VAPT ReportDocument28 pagesAstra Security Sample VAPT Reporthanuman1999No ratings yet
- Doug Murray USC CISO ResumeDocument6 pagesDoug Murray USC CISO ResumeashokNo ratings yet
- Microsoft Zero Trust Maturity Model - Oct 2019Document7 pagesMicrosoft Zero Trust Maturity Model - Oct 2019Javier MoralesNo ratings yet
- 2019 Cloud Security Report Sponsored by (ISC) .Document20 pages2019 Cloud Security Report Sponsored by (ISC) .qadir147No ratings yet
- ITA CertificationRoadmapDocument1 pageITA CertificationRoadmapgcinamNo ratings yet
- Robert Garigue CISO BriefingDocument63 pagesRobert Garigue CISO Briefingadityagour2394No ratings yet
- It Security Sample ResumeDocument2 pagesIt Security Sample ResumeMathewNo ratings yet
- Frank McGovern ResumeDocument2 pagesFrank McGovern ResumeJosué RombaNo ratings yet
- Microsoft Cybersecurity Solutions GroupDocument63 pagesMicrosoft Cybersecurity Solutions Grouprghr100% (1)
- In Cybersecurity, Best Practices Are The WorstDocument4 pagesIn Cybersecurity, Best Practices Are The WorstKelvin LamNo ratings yet
- Top 10 Privacy Risks Projects CountermeasuresDocument10 pagesTop 10 Privacy Risks Projects CountermeasuresJuan Carlos Giraldo VidalNo ratings yet
- Domain One QuestionsDocument22 pagesDomain One Questionsyogo camlusNo ratings yet
- Balbix New CISO Board DeckDocument42 pagesBalbix New CISO Board DeckSandesh RautNo ratings yet
- Cyber SecurityDocument22 pagesCyber SecurityAnkur GoelNo ratings yet
- Ey How Do You Protect Robots From Cyber AttackDocument17 pagesEy How Do You Protect Robots From Cyber AttackabgmNo ratings yet
- MSFT Cloud Architecture SecurityDocument9 pagesMSFT Cloud Architecture SecurityPratik KadamNo ratings yet
- Huntmetrics Deck v3Document15 pagesHuntmetrics Deck v3Sarah KhanNo ratings yet
- Itil Guide Cyber Resilience UpGuardDocument14 pagesItil Guide Cyber Resilience UpGuardEne Veber Raluca100% (1)
- ISO27001 and (VS) Cyber Essentials - (3p)Document3 pagesISO27001 and (VS) Cyber Essentials - (3p)Rodrigo BenaventeNo ratings yet
- Telework Cybersecurity Controls GuideDocument28 pagesTelework Cybersecurity Controls GuideRodrigo BenaventeNo ratings yet
- DevSecOps Fundamentals Guidebook 1671911603Document42 pagesDevSecOps Fundamentals Guidebook 1671911603Micael PNo ratings yet
- GDPR Accountability Checklist - (1p)Document1 pageGDPR Accountability Checklist - (1p)Rodrigo BenaventeNo ratings yet
- Data Protection Audit Manual - (173p)Document173 pagesData Protection Audit Manual - (173p)Rodrigo BenaventeNo ratings yet
- Types of Firewall - MoSDocument11 pagesTypes of Firewall - MoSEnrociNo ratings yet
- MoS - Step-By-Step Asset Based Risk Assessment - (11p)Document11 pagesMoS - Step-By-Step Asset Based Risk Assessment - (11p)Rodrigo Benavente100% (1)
- Business Impact Analysis BIA Information Security - (13p)Document13 pagesBusiness Impact Analysis BIA Information Security - (13p)Rodrigo BenaventeNo ratings yet
- ISO27001 Self-Assessment ChecklistDocument9 pagesISO27001 Self-Assessment ChecklistRodrigo Benavente100% (1)
- M-Trends 2023 Report - (108p)Document108 pagesM-Trends 2023 Report - (108p)Rodrigo Benavente100% (1)
- Getting Started in Cyber Field GuideDocument18 pagesGetting Started in Cyber Field GuideRodrigo BenaventeNo ratings yet
- DB - YS JaganDocument9 pagesDB - YS JaganskgconNo ratings yet
- NSS+Labs 2019+Advanced+Endpoint+Protection+Security+Value+MapDocument1 pageNSS+Labs 2019+Advanced+Endpoint+Protection+Security+Value+MapBilly ChristouNo ratings yet
- Cyber CrimeDocument4 pagesCyber CrimeVarshini PrabaharanNo ratings yet
- XVCBN Cyber HandbookDocument71 pagesXVCBN Cyber HandbookggcvbcNo ratings yet
- Fortisandbox: Third-Generation Sandboxing Featuring Dynamic Ai AnalysisDocument4 pagesFortisandbox: Third-Generation Sandboxing Featuring Dynamic Ai AnalysisRudi Arif candraNo ratings yet
- Day 1 Attacking The Web Application CTFDocument9 pagesDay 1 Attacking The Web Application CTFawcleaners.usNo ratings yet
- Running Head: Security Attack On Systems and Web Servers 1Document8 pagesRunning Head: Security Attack On Systems and Web Servers 1kim kimNo ratings yet
- Getting Started With JSSE and JCEDocument4 pagesGetting Started With JSSE and JCEafshar13505960No ratings yet
- Decentralized Access Control With Anonymous Authentication of Data Stored in CloudsDocument18 pagesDecentralized Access Control With Anonymous Authentication of Data Stored in CloudsShiva KrishnaNo ratings yet
- The Golden Tax Department and Emergence of Goldenspy MalwareDocument26 pagesThe Golden Tax Department and Emergence of Goldenspy MalwarerodrigoduocNo ratings yet
- Transport Level Security PresentationDocument30 pagesTransport Level Security PresentationAhimbisibwe BakerNo ratings yet
- Empowerment TechDocument49 pagesEmpowerment TechMarlene MahidlayonNo ratings yet
- Cyber Crime Forensic InvestigationDocument31 pagesCyber Crime Forensic InvestigationS.m. Jafar100% (1)
- ECIH Exam Blueprint v1Document3 pagesECIH Exam Blueprint v1dhazh0070% (1)
- JURNAL NSPS Russia - UNHANDocument21 pagesJURNAL NSPS Russia - UNHANSuspada SiswoputroNo ratings yet
- SecurEnvoy Infinigate DK PresentationDocument33 pagesSecurEnvoy Infinigate DK PresentationMeghana MadineniNo ratings yet
- Adware DescriptionDocument2 pagesAdware Descriptionsoumya giteNo ratings yet
- Lesson 6: Implementing Public Key InfrastructureDocument25 pagesLesson 6: Implementing Public Key InfrastructurePhan Sư ÝnhNo ratings yet
- Certifying AuthorityDocument25 pagesCertifying AuthorityMushtaq Ahmad100% (1)
- Windows Splunk Logging Cheat Sheet - Win 7 - Win2012: DefinitionsDocument14 pagesWindows Splunk Logging Cheat Sheet - Win 7 - Win2012: DefinitionsrxfcggNo ratings yet
- CEH v9 Notes - Dads Man CaveDocument17 pagesCEH v9 Notes - Dads Man CaveJeshal PatelNo ratings yet
- CS 651 Computer Systems Security - Individual Project Information Systems Security (ISS) Governance Committee Saurav Vaidya Jan 27, 2016Document10 pagesCS 651 Computer Systems Security - Individual Project Information Systems Security (ISS) Governance Committee Saurav Vaidya Jan 27, 2016ghiraulaNo ratings yet
- Zywall USG 100/200 DatasheetDocument4 pagesZywall USG 100/200 Datasheetview100% (1)
- The Evolution of Cybersecurity - Secure Mail Gateway QuizDocument2 pagesThe Evolution of Cybersecurity - Secure Mail Gateway Quizchhun25% (4)
- (Applicable From The Academic Session 2018-2019) : Syllabus For B. Tech in Computer Science & EngineeringDocument22 pages(Applicable From The Academic Session 2018-2019) : Syllabus For B. Tech in Computer Science & EngineeringAdhara MukherjeeNo ratings yet
- Information Technology Laws: International Co-Operation in Cyber Crime MitigationDocument14 pagesInformation Technology Laws: International Co-Operation in Cyber Crime MitigationVishalNo ratings yet
- AR Ponemon 2009 PCI DSS Compliance SurveyDocument20 pagesAR Ponemon 2009 PCI DSS Compliance SurveyKhadir FayazNo ratings yet
- Cyber Crime and Cyber Law's of IndiaDocument10 pagesCyber Crime and Cyber Law's of IndiaKhushraj SinghNo ratings yet
- Data Encryption Standard (DES) : DES Implementation in C++Document18 pagesData Encryption Standard (DES) : DES Implementation in C++rizwanNo ratings yet
- Siddaganga Institute of Technology, Tumkur - 572 103: Usn 1 S I ECEL26Document2 pagesSiddaganga Institute of Technology, Tumkur - 572 103: Usn 1 S I ECEL26aNo ratings yet