Professional Documents
Culture Documents
03 Analysis Part3
Uploaded by
Abdelzeam Rizk0 ratings0% found this document useful (0 votes)
8 views29 pagesOriginal Title
03-Analysis-Part3
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
8 views29 pages03 Analysis Part3
Uploaded by
Abdelzeam RizkCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 29
Faculty of Computers and Information
Menoufia University جامعة المنوفية
System Analysis and Design
3rd Year – Information System department
Course Content
• Chapter 1 - Introduction to Software Engineering
• Chapter 2 - Modeling with UML
• Chapter 3 - Project Organization and Communication
• Chapter 4 - Requirements Elicitation
• Chapter 5 - Analysis
• Chapter 6 - System Design: Decomposing the System
• Chapter 7 - System Design: Addressing Design Goals
• Chapter 8 - Object Design: Reusing Pattern Solutions
• Chapter 9 - Object Design: Specifying Interfaces
• Chapter 10 - Mapping Models to Code
• Chapter 11 - Testing
Agenda
• Chapter 5 - Analysis
– Introduction: An Optical Illusion
– An Overview of Analysis
– Analysis Concept
– Analysis Activities: From Use Cases to Objects
– Managing Analysis
– ARENA Case Study (Section Part)
Managing Analysis
• The primary challenge in managing the requirements in
multi-team development project is to maintain
consistency while using so many resources.
• We first describe a document template that can be used to
document the results of analysis.
• Next, we describe the role assignment to analysis. We
then address communication issues during analysis. Next,
we address management issues related to the iterative and
incremental nature of requirements.
Documenting Analysis
• The requirements elicitation and analysis activities are
documented in the Requirements Analysis Document
(RAD).
• RAD consists of four main sections: introduction, current
system, proposed system, and glossary.
• The information in RAD are collected and analyzed
incrementally.
• The requirement analysis document collects, organizes,
and tracks the project requirements from key
stakeholders. It guides project planning and ensures you
complete your projects aligned with stakeholder and
business goals.
Documenting Analysis
Requirements Analysis Document
1. Introduction
2. Current system
3. Proposed system
3.1 Overview
3.2 Functional requirements
3.3 Non-functional requirements
3.4 System models
3.4.1 Scenarios
3.4.2 Use case model
3.4.3 Object model
3.4.3.1 Data dictionary
3.4.3.2 Class diagrams
3.4.4 Dynamic models
3.4.5 User interfaces
4. Glossary
Documenting Analysis
• What are the difference between object models section
and dynamic model section in RAD?
– Object models section: documents in detail all the objects (i.e.,
entity, boundary, and control) identified, their attributes, and
operations. As each object is described with textual definitions,
relationships among objects are illustrated with class diagrams.
– Dynamic models section: documents the behavior of the object
model in terms of state machine diagrams and sequence
diagrams.
Assigning Responsibilities
• Analysis requires the participation of a wide range of
individuals, such as:
– The target user provides application domain knowledge.
– The client funds the project and coordinates the user side of the
effort.
– The analyst elicits application domain knowledge and
formalizes it.
– The developers provide feedback on feasibility and cost.
– The project manager coordinates the effort on the development
side.
• For large systems, many users, analysts, and developers
may be involved, which introduces additional challenges.
Assigning Responsibilities
• These challenges can be met by assigning well-defined
roles and scopes to individuals. There are three main
types of roles:
– Generation of information
– Integration
– Review
• Determine the role of each participant in system
analysis?
– The end user is the application domain expert who generates
information about the current system, the environment of the
future system, and the tasks it should support.
Assigning Responsibilities
– The client, an integration role, defines the scope of the system
based on user requirements. Different users may have different
views of the system, either because they will benefit from
different parts of the system or because the users have different
opinions or expectations about the future system. The client
serves as an integrator of application domain information and
resolves conflicts in user views.
– The analyst is the application domain expert who models the
current system and generates information about the future
system. The analysis will identify a number of objects, their
associations, and their attributes. The analyst is typically a
developer with broad application domain knowledge.
Assigning Responsibilities
– The architect, an integration role, unifies the use case and object
models from a system point of view. Different analysts may
have different styles of modeling and different views of the parts
of the systems. The role of the architect is to provide a system
philosophy and to identify omissions in the requirements.
– The document editor is responsible for the low-level integration
of the document and for the overall format of the document and
its index.
– The configuration manager is responsible for maintaining a
revision history of the document.
Assigning Responsibilities
– The reviewer validates and review the RAD for correctness,
completeness, consistency, and clarity. Users, clients,
developers, or other individuals may become reviewers during
requirements validation. Individuals that have not yet been
involved in the development represent excellent reviewers,
because they are more able to identify ambiguities and areas that
need clarification.
Communicating about Analysis
• The task of communicating information is most
challenging during requirements elicitation and analysis
due to the following factors:
– Different backgrounds of participants.
– Different expectations of stakeholders.
– New teams.
– Evolving system.
Communicating about Analysis
• Conflicting objectives and competition will always be part
of large development projects. A few simple guidelines,
however, can help in managing the complexity of
conflicting views of the system:
– Define clear territories ()منطقة أو مقاطعة.
– Define clear objectives and success criteria.
– Brainstorm.
Iterating over the Analysis Model
• Analysis occurs iteratively and incrementally, often in
parallel with other development activities such as system
design and implementation.
• Note, however, that the unrestricted modification and
extension of the analysis model can only result in chaos,
especially when a large number of participants are
involved.
• Iterations and increments must be carefully managed and
requests for changes tracked once the requirements are
base-lined.
Iterating over the Analysis Model
• The requirements activity can be viewed as several steps
converging toward a stable model:
– Brainstorming: Before any other development activity is
initiated, requirements is a brainstorming process. The objective
of a brainstorming process is to generate as many ideas as
possible without necessarily organizing them. During this stage,
iterations are rapid and far reaching.
– Solidification: Once the client and the developers converge on a
common idea, define the boundaries of the system, and agree on
a set of standard terms, solidification starts. Functionality is
organized into groups of use cases with their corresponding
interfaces. Groups of functionality are allocated to different
teams that are responsible for detailing their corresponding use
cases. During this stage, iterations are rapid but localized.
Iterating over the Analysis Model
– Maturity: Changes at the higher level are still possible but more
difficult, and thus, are made more carefully. Each team is
responsible for the use cases and object models related to the
functionality they have been assigned. A cross-functional team,
the architecture team, made of representatives of each team, is
responsible for ensuring the integration of the requirements
(e.g., naming).
Brainstorming Solidification Maturity
Client Sign-Off
• The client sign-off represents the acceptance of the
analysis model (as documented in RAD).
• The client and the developers converge on a single idea
and agree about the functions and features that the system
will have.
• In addition, they agree on:
1. A list of priorities
2. A revision process
3. A list of criteria that will be used to accept or reject the system
4. A schedule and a budget.
Client Sign-Off
• Prioritizing system functions allows the developers to
understand better the client’s expectations.
• It also allows developers to deliver the system in
incremental chunks: essential functions are delivered first,
additional chunks are delivered depending on the
evaluation of the previous chunk.
• Even if the system is to be delivered as a single, complete
package, prioritizing functions enables the client to
communicate clearly what is important to her and where
the emphasis of the development should be.
Client Sign-Off
• Requirements continue to change after the sign-off,
because of errors, omissions, changes in the operating
environment, changes in the application domain, or
changes in technology.
• The list of acceptance criteria is restated at sign-off, the
client ensures that the developers are updated about any
changes in client expectations.
• The acceptance of the requirements analysis document is
more critical than any other document, given that many
activities depend on the analysis model.
An example of a revision process of changing in requirement
Analysis Model Heuristics
Abbott’s Heuristics for Identifying Entity
Objects
• Heuristics are:
1. Terms that developers or users need to clarify in order to
understand the use case
2. Recurring nouns in the use cases (e.g., Incident)
3. Real-world entities that the system needs to track (e.g.,
FieldOfficer, Dispatcher, Resource)
4. Real-world activities that the system needs to track (e.g.,
EmergencyOperationsPlan)
5. Data sources or sinks (e.g., Printer).
Abbott’s Heuristics for Identifying Boundary
Objects
• Heuristics are:
1. Identify user interface controls that the user needs to initiate
the use case.
2. Identify forms the users needs to enter data into the system.
3. Identify notices and messages the system uses to respond to the
user.
4. When multiple actors are involved in a use case, identify actor
terminals to refer to the user interface under consideration.
5. Always use the end user’s terms for describing interfaces; do
not use terms from the solution or implementation domains.
Abbott’s Heuristics for Identifying Control
Objects
• Heuristics are:
1. Identify one control object per use case.
2. Identify one control object per actor in the use case.
3. The life span of a control object should cover the extent of the
use case or the extent of a user session. If it is difficult to
identify the beginning and the end of a control object
activation, the corresponding use case probably does not have
well-defined entry and exit conditions.
Abbott’s Heuristics for Drawing Sequence
Diagrams
• Heuristics are:
1. The first column should correspond to the actor who initiated
the use case.
2. The second column should be a boundary object (that the actor
used to initiate the use case).
3. The third column should be the control object that manages the
rest of the use case.
4. Control objects are created by boundary objects initiating use
cases.
5. Boundary objects are created by control objects.
6. Entity objects are accessed by control and boundary objects.
7. Entity objects never access boundary or control objects; this
makes it easier to share entity objects across use cases.
Abbott’s Heuristics for Identifying
Associations
• Heuristics are:
1. Examine verb phrases.
2. Name associations and roles precisely.
3. Use qualifiers as often as possible to identify key attributes.
4. Eliminate any association that can be derived from other
associations.
5. Too many associations make a model unreadable.
Abbott’s Heuristics for Identifying Attributes
• Heuristics are:
1. Examine possessive phrases.
▪ In particular, a noun phrase followed by a possessive phrase
(e.g., the description of an emergency) or an adjective phrase
(e.g., the emergency description) should be examined.
2. Represent stored state as an attribute of the entity object.
3. Describe each attribute.
4. Do not represent an attribute as an object; use an association
instead.
5. Do not waste time describing fine details before the object
structure is stable.
Thank You
You might also like
- SE - Unit 4Document79 pagesSE - Unit 4saket.internshipNo ratings yet
- Requirements Engineering Overview: The Importance of RequirementsDocument15 pagesRequirements Engineering Overview: The Importance of RequirementsYohannes TerfaNo ratings yet
- Software BasicDocument56 pagesSoftware BasicSarah ShelbyNo ratings yet
- Requirements Engineering in Software DevelopmentDocument38 pagesRequirements Engineering in Software DevelopmentJimmeyNo ratings yet
- Dcit 24 Lec 2Document25 pagesDcit 24 Lec 2jaesthminieNo ratings yet
- Module 1Document39 pagesModule 1Shweta SinghNo ratings yet
- 5.2 - System Analysis and DesignDocument19 pages5.2 - System Analysis and DesignPiyush SinghNo ratings yet
- Software Requirement understanding and analysis.pptxDocument24 pagesSoftware Requirement understanding and analysis.pptxgfdsa jklNo ratings yet
- Chapter 3 OoadDocument22 pagesChapter 3 Ooadsujitha14No ratings yet
- 3RD Module MisDocument17 pages3RD Module Mismuhammed.hazimkt.4No ratings yet
- LEC 3 Information System PlanningDocument6 pagesLEC 3 Information System PlanningJEMIMA MILES CASIBUANo ratings yet
- Classical Waterfall Model:: Mid Questions and Answers - 4sets PDF By: Venu GopalDocument22 pagesClassical Waterfall Model:: Mid Questions and Answers - 4sets PDF By: Venu Gopalspider dogNo ratings yet
- Session 10 and 11Document143 pagesSession 10 and 11KuldeepSinghDeoraNo ratings yet
- Information SystemDocument30 pagesInformation SystemNikitaNo ratings yet
- Introduction To System AnalysisDocument29 pagesIntroduction To System Analysisjheneryjane mariñoNo ratings yet
- Unit2 2Document101 pagesUnit2 2shriyaNo ratings yet
- Module 1 StudentDocument45 pagesModule 1 StudentRahul AgarwalNo ratings yet
- Answer 3Document5 pagesAnswer 3Shubham imtsNo ratings yet
- chapter 3Document26 pageschapter 3Jiru AlemayehuNo ratings yet
- Module 3Document12 pagesModule 3efrenNo ratings yet
- Module 5 - Reading1 - SystemDevelopmentDocument26 pagesModule 5 - Reading1 - SystemDevelopmentChristopher AdvinculaNo ratings yet
- SDLC Stages ExplainedDocument57 pagesSDLC Stages ExplainedAbdul MoizNo ratings yet
- BC0057 3rd ChapterDocument7 pagesBC0057 3rd ChapterbeforeRGNo ratings yet
- SAD Approaches To DesignDocument25 pagesSAD Approaches To Designkolakim75No ratings yet
- Structured Systems Analysis and Design MethodDocument3 pagesStructured Systems Analysis and Design MethodJACK ROLLERNo ratings yet
- Tools Methods and MethodologyDocument67 pagesTools Methods and MethodologyCarissa UrrizaNo ratings yet
- OOAD Chapter 1 Introduction to Object Oriented Analysis and DesignDocument5 pagesOOAD Chapter 1 Introduction to Object Oriented Analysis and DesignPriyanka Sharma100% (1)
- APSI-03. Information System DevelopmentDocument29 pagesAPSI-03. Information System DevelopmentBudi Purwoko SantosoNo ratings yet
- Chapter 3Document43 pagesChapter 3James MacalaladNo ratings yet
- CS 2Document26 pagesCS 2Srikesh NairNo ratings yet
- Object Oriented Analysis and DesignDocument59 pagesObject Oriented Analysis and DesigndeepakiimmNo ratings yet
- Software Development Process: IS 274: Object Oriented Analysis and DesignDocument44 pagesSoftware Development Process: IS 274: Object Oriented Analysis and DesignSTANLEY RICHARDNo ratings yet
- Analysis and Design: of E-Commerce SystemsDocument50 pagesAnalysis and Design: of E-Commerce Systemshamedsky100% (1)
- RE Process Overview - Discover, Document & Validate RequirementsDocument4 pagesRE Process Overview - Discover, Document & Validate RequirementsLokesh KCNo ratings yet
- Ch2 SW ProcessesDocument57 pagesCh2 SW ProcessesMohamud Ahmed AbdulleNo ratings yet
- Software EngineeringDocument63 pagesSoftware EngineeringShreya MukherjeeNo ratings yet
- Module 3Document31 pagesModule 3sasanaravi2020No ratings yet
- Software Requirements Analysis and Specifications GuideDocument64 pagesSoftware Requirements Analysis and Specifications GuideYaadviNo ratings yet
- The Systems Development EnvironmentDocument47 pagesThe Systems Development EnvironmentAditya BhusalNo ratings yet
- Oose 5Document62 pagesOose 5Habtamu YihuneNo ratings yet
- SDMDocument12 pagesSDMKhusiray KhusiNo ratings yet
- Chapter 02Document23 pagesChapter 02gfdsa jklNo ratings yet
- Software Requirements Analysis & Specifications: Requirement EngineeringDocument15 pagesSoftware Requirements Analysis & Specifications: Requirement EngineeringKashish AroraNo ratings yet
- 03 - Intro To SDLCDocument22 pages03 - Intro To SDLCNicoleNo ratings yet
- Introduction to Software EngineeringDocument7 pagesIntroduction to Software EngineeringMarlon BoucaudNo ratings yet
- Requirement Discipline and System Analysis ModelsDocument17 pagesRequirement Discipline and System Analysis ModelsIrog JeromeNo ratings yet
- Module-3 Analysis and Design: Software Development Process OverviewDocument50 pagesModule-3 Analysis and Design: Software Development Process OverviewAishwaryaNo ratings yet
- Lecture 14Document29 pagesLecture 14JAWAD GillaniNo ratings yet
- NotesDocument5 pagesNotesMUNEEBA GULNo ratings yet
- Chapter 4Document62 pagesChapter 4yola chattpgNo ratings yet
- Se Practical FileDocument58 pagesSe Practical FileDivya Gupta100% (1)
- Chapter 5Document37 pagesChapter 5The BigBradNo ratings yet
- Systems Development Life Cycle (SDLCDocument45 pagesSystems Development Life Cycle (SDLCCHRISTINE ANN AGUINALDONo ratings yet
- SAD Assignment AnswerDocument9 pagesSAD Assignment Answerchak.m.beyenaNo ratings yet
- SSADM Is A Waterfall Method by Which An Information System Design Can Be Arrived atDocument12 pagesSSADM Is A Waterfall Method by Which An Information System Design Can Be Arrived atAenna Orra100% (1)
- OODM Final SarojDocument33 pagesOODM Final SarojNabin TimsinaNo ratings yet
- SDLC Day1Document17 pagesSDLC Day1Aye Khaing Khaing MoeNo ratings yet
- Object-Oriented Analysis and Design for Information Systems: Modeling with BPMN, OCL, IFML, and PythonFrom EverandObject-Oriented Analysis and Design for Information Systems: Modeling with BPMN, OCL, IFML, and PythonNo ratings yet
- Software Testing Interview Questions You'll Most Likely Be AskedFrom EverandSoftware Testing Interview Questions You'll Most Likely Be AskedNo ratings yet
- Non-Deterministic AlgorithmDocument13 pagesNon-Deterministic AlgorithmDivy jainNo ratings yet
- Program For CalculatorDocument4 pagesProgram For CalculatorMounika 190BC028No ratings yet
- Vighnesh Rahul BavdekarDocument3 pagesVighnesh Rahul BavdekarVighneshNo ratings yet
- GIFT School of Engineering and Applied Sciences Fall 2021 CS-204 Data Structures and Algorithms Week-4 ManualDocument5 pagesGIFT School of Engineering and Applied Sciences Fall 2021 CS-204 Data Structures and Algorithms Week-4 ManualCh Salman AhsanNo ratings yet
- ML ProjectReport-Sonali JoshiDocument38 pagesML ProjectReport-Sonali Joshisonali100% (1)
- CSE-311 Microprocessor & Interfacing Course OutlineDocument2 pagesCSE-311 Microprocessor & Interfacing Course OutlineEngnrMemonNo ratings yet
- Programming Concepts and Constructs (C++ Language) : Selection Statements: SwitchDocument17 pagesProgramming Concepts and Constructs (C++ Language) : Selection Statements: Switchamin124010No ratings yet
- Sphero Lab ReportDocument4 pagesSphero Lab Reportapi-502122795No ratings yet
- Indian Institute of Technology, Kanpur: Department of Computer Science and Engineering Revision of Existing Course CS771Document2 pagesIndian Institute of Technology, Kanpur: Department of Computer Science and Engineering Revision of Existing Course CS771broken heartNo ratings yet
- General MaterialDocument16 pagesGeneral MaterialHariharan ShankarNo ratings yet
- Computer Science and EngineeringDocument358 pagesComputer Science and Engineeringvidhya_bineeshNo ratings yet
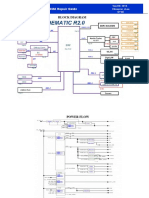
- Block Diagram: X453MA Repair GuideDocument5 pagesBlock Diagram: X453MA Repair GuideHAROL ALEXIS VALENCIA OSPINANo ratings yet
- Face Recognition Using AI Black Book Project For 3rd Year StudentsDocument104 pagesFace Recognition Using AI Black Book Project For 3rd Year Studentskingproduction880No ratings yet
- Relative Time Expressions in Flux Job SchedulerDocument1 pageRelative Time Expressions in Flux Job SchedulerLuca PilottiNo ratings yet
- Machine LearningDocument8 pagesMachine LearningRowa salmanNo ratings yet
- Data Structures in JavaDocument46 pagesData Structures in JavaMahesh Roy ChinnaNo ratings yet
- CS188 Bayes' Nets GuideDocument42 pagesCS188 Bayes' Nets GuideMd.Abu Rayhan AbirNo ratings yet
- C programming exercises solutionsDocument11 pagesC programming exercises solutionsRana ZuhaibNo ratings yet
- Ui22 Lab1Document5 pagesUi22 Lab1dattpatel2020No ratings yet
- HRDC JNTUH RC AI and MLDocument2 pagesHRDC JNTUH RC AI and MLmohanNo ratings yet
- 30-Longest Sequence of 1 After Flipping A Bit-25-05-2023Document16 pages30-Longest Sequence of 1 After Flipping A Bit-25-05-2023Rahul LokeshNo ratings yet
- TCS BookDocument589 pagesTCS BookNavnath Auti100% (1)
- Assignment-2 3Document4 pagesAssignment-2 3botiwaNo ratings yet
- Object Oriented Programming Lab ManualDocument27 pagesObject Oriented Programming Lab ManualY RohitNo ratings yet
- Syllabus For M.sc. (CS) Cbcs Based21!22!24.12.21Document34 pagesSyllabus For M.sc. (CS) Cbcs Based21!22!24.12.21Nikita BadhaiNo ratings yet
- C++ Lab Worksheet 6.1Document15 pagesC++ Lab Worksheet 6.1Aryaman SharmaNo ratings yet
- Heap SortDocument40 pagesHeap SortRushil ShahNo ratings yet
- Cheat Sheet Unit Testing 1635173296Document1 pageCheat Sheet Unit Testing 1635173296Chandra Sekhar RoutNo ratings yet
- 19it428 2it09 Lab Manual 07052021Document43 pages19it428 2it09 Lab Manual 07052021IT booksNo ratings yet
- QueueDocument6 pagesQueuerajeshchoudharyNo ratings yet