Professional Documents
Culture Documents
M6
Uploaded by
Aryan Panchal0 ratings0% found this document useful (0 votes)
12 views7 pagesDjsjwksj
Original Title
M6.pptx
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentDjsjwksj
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
12 views7 pagesM6
Uploaded by
Aryan PanchalDjsjwksj
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 7
Buffer Overflow
•Buffer overflow is a software coding error or vulnerability that can be
exploited by hackers to gain unauthorized access to corporate systems.
•It is one of the best-known software security vulnerabilities yet remains
fairly common.
•This is partly because buffer overflows can occur in various ways and the
techniques used to prevent them are often error-prone.
The software error focuses on buffers, which are sequential sections of
computing memory that hold data temporarily as it is transferred between
locations.
Also known as a buffer overrun, buffer overflow occurs when the
amount of data in the buffer exceeds its storage capacity.
That extra data overflows into adjacent memory locations and corrupts or
overwrites the data in those locations.
▪
•For example, a buffer for log-in credentials may be designed to expect
username and password inputs of 8 bytes, so if a transaction involves an
input of 10 bytes (that is, 2 bytes more than expected), the program may
write the excess data past the buffer boundary.
•Buffer overflows can affect all types of software. They typically result
from malformed inputs or failure to allocate enough space for the buffer.
If the transaction overwrites executable code, it can cause the program to
behave unpredictably and generate incorrect results, memory access
errors, or crashes.
▪
▪
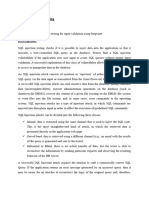
▪ SQL injection
▪A SQL injection attack consists of insertion or “injection” of a SQL
query via the input data from the client to the application.
▪ A successful SQL injection exploit can read sensitive data from the
database, modify database data (Insert/Update/Delete), execute
administration operations on the database (such as shutdown the
DBMS),
▪ recover the content of a given file present on the DBMS file
system and in some cases issue commands to the operating system.
▪SQL injection attacks are a type of injection attack, in which SQL
commands are injected into data-plane input in order to affect the
execution of predefined SQL commands.
▪
How and Why Is an SQL Injection Attack Performed
•To make an SQL Injection attack, an attacker must first find vulnerable
user inputs within the web page or web application. A web page or web
application that has an SQL Injection vulnerability uses such user input
directly in an SQL query. The attacker can create input content. Such
content is often called a malicious payload and is the key part of the
attack. After the attacker sends this content, malicious SQL commands
are executed in the database.
•SQL is a query language that was designed to manage data stored in
relational databases. You can use it to access, modify, and delete data.
Many web applications and websites store all the data in SQL databases.
In some cases, you can also use SQL commands to run operating system
commands. Therefore, a successful SQL Injection attack can have very
serious consequences.
•Attackers can use SQL Injections to find the credentials of other users in
the database. They can then impersonate these users. The impersonated
user may be a database administrator with all database privileges.
•SQL lets you select and output data from the database. An SQL Injection
vulnerability could allow the attacker to gain complete access to all data
in a database server.
•SQL also lets you alter data in a database and add new data. For example,
in a financial application, an attacker could use SQL Injection to alter
balances, void transactions, or transfer money to their account.
•You can use SQL to delete records from a database, even drop tables.
Even if the administrator makes database backups, deletion of data could
affect application availability until the database is restored. Also, backups
may not cover the most recent data.
•In some database servers, you can access the operating system using the
database server.
•This may be intentional or accidental. In such case, an attacker could use
an SQL Injection as the initial vector and then attack the internal network
behind a firewall.
•There are several types of SQL Injection attacks: in-band SQLi (using
database errors or UNION commands), blind SQLi, and out-of-band
SQLi.
You might also like
- Sqli AttacksDocument149 pagesSqli AttacksTarik AmezianeNo ratings yet
- Automated SQL Injection Detection Using Hash FunctionsDocument18 pagesAutomated SQL Injection Detection Using Hash FunctionsAayushiSwaroopNo ratings yet
- Task 12Document5 pagesTask 12Sridhar PNo ratings yet
- Auditing-Oracle-Database Joa Eng 1114Document7 pagesAuditing-Oracle-Database Joa Eng 1114roychabNo ratings yet
- Enhancing Database Security with Hill Cipher Encryption (IJEATDocument5 pagesEnhancing Database Security with Hill Cipher Encryption (IJEATRivalri Kristianto HondroNo ratings yet
- Injection Attacks SQL InjectionDocument6 pagesInjection Attacks SQL InjectionAkshat PattiwarNo ratings yet
- Mini Project On Information and Cyber Security: SQL (Structured Query Language) InjectionDocument9 pagesMini Project On Information and Cyber Security: SQL (Structured Query Language) Injectioncyan whiteNo ratings yet
- SQL Injection: What Is It?Document8 pagesSQL Injection: What Is It?Shabari GirishNo ratings yet
- Lectu Er TwoDocument32 pagesLectu Er TwoAbdurahman awilNo ratings yet
- Experiment 4Document4 pagesExperiment 4Kshitiz SharmaNo ratings yet
- DenverApril2012Meeting-WebGoat & WebScarabDocument33 pagesDenverApril2012Meeting-WebGoat & WebScarabNorma ArcosNo ratings yet
- Database Security & RecoveryDocument17 pagesDatabase Security & RecoveryAnchal MishraNo ratings yet
- Practical SQL Injection OverviewDocument6 pagesPractical SQL Injection OverviewAkash KataraNo ratings yet
- Practical Insight Into InjectionsDocument27 pagesPractical Insight Into InjectionsasdffNo ratings yet
- Injections 101: Understanding the Basics of SQL, Host Header, and SMTP InjectionsDocument27 pagesInjections 101: Understanding the Basics of SQL, Host Header, and SMTP InjectionsmarutidivekarNo ratings yet
- Unit 4Document45 pagesUnit 4AasmiNo ratings yet
- Session 1 Web Application SecurityDocument83 pagesSession 1 Web Application SecurityNick LoveNo ratings yet
- IBM Ssecurity SO#35163 E-Guide 080111updateDocument7 pagesIBM Ssecurity SO#35163 E-Guide 080111updateblackdaybrNo ratings yet
- Unit 4 1Document7 pagesUnit 4 1Mvk MvkNo ratings yet
- Bug ReportDocument5 pagesBug ReportIRFAN SADIK 222-15-6545No ratings yet
- Chapter 3Document8 pagesChapter 3jetowi8867No ratings yet
- Categories of FailureDocument6 pagesCategories of Failure001stylev001No ratings yet
- Vulnerability in The Security of Management SystemsDocument5 pagesVulnerability in The Security of Management SystemsJhonnatan RomayNo ratings yet
- OWASP Backend Security Project 1.0betaDocument184 pagesOWASP Backend Security Project 1.0betaMobile TesterNo ratings yet
- Other Attacks: Cyber Security Essential Jibril Dauda MuhammadDocument14 pagesOther Attacks: Cyber Security Essential Jibril Dauda MuhammadJibril Dauda MuhammadNo ratings yet
- SQLiDocument20 pagesSQLisumanxlataNo ratings yet
- Introduction to Application Penetration Testing TechniquesDocument26 pagesIntroduction to Application Penetration Testing TechniquesKarel GoldmannNo ratings yet
- Unit 5-DBPDocument37 pagesUnit 5-DBPHafiz RahmanNo ratings yet
- Web Server As A TargetDocument43 pagesWeb Server As A Targetjigsaw55555No ratings yet
- Web Server As A TargetDocument43 pagesWeb Server As A Targettohid_78692No ratings yet
- BufferoverflowDocument4 pagesBufferoverflowdanijali235No ratings yet
- Chapter 5Document70 pagesChapter 5masnun mareebNo ratings yet
- 6Document4 pages6mentalinsideNo ratings yet
- How To Hack DatabaseDocument45 pagesHow To Hack DatabasePrintesh PatelNo ratings yet
- Reference 1 - 2017Document13 pagesReference 1 - 2017abenezer ketemaNo ratings yet
- Report On OWASP What Is OWASP?: Deep Nandu BED-C-48Document4 pagesReport On OWASP What Is OWASP?: Deep Nandu BED-C-48deep nanduNo ratings yet
- Manual SQL InjectionDocument14 pagesManual SQL InjectionDigital WorldNo ratings yet
- Oracle Database Security OverviewDocument20 pagesOracle Database Security Overviewvipinsharma237440No ratings yet
- Lectre 13Document6 pagesLectre 13AkRajNo ratings yet
- Sub: Web Security Name: Shubham Sati ROLL NO: 17BCA1100 Class: Bca5CDocument7 pagesSub: Web Security Name: Shubham Sati ROLL NO: 17BCA1100 Class: Bca5CShubham SatiNo ratings yet
- Domain 4Document8 pagesDomain 4Hossam EissaNo ratings yet
- OWASP Top 10 Security Risks & Vulnerabilities ExplainedDocument25 pagesOWASP Top 10 Security Risks & Vulnerabilities ExplainedhariNo ratings yet
- Input Validation Testing AimDocument4 pagesInput Validation Testing AimAswathy L CNo ratings yet
- SQL Injection Detection and Prevention Techniques: University Technology MalaysiaDocument8 pagesSQL Injection Detection and Prevention Techniques: University Technology MalaysiaPramono PramonoNo ratings yet
- WP Real Time Database MonitoringDocument12 pagesWP Real Time Database MonitoringngvsonNo ratings yet
- OWASP top 10 2017 explainedDocument17 pagesOWASP top 10 2017 explainedAbdul Mateen UkkundNo ratings yet
- SQL - Injctions Loop JoksDocument35 pagesSQL - Injctions Loop JoksPratik BhoirNo ratings yet
- SecurityDocument4 pagesSecurityRavindra PawarNo ratings yet
- Detection of SQL Injection Using Machine Learning: A SurveyDocument8 pagesDetection of SQL Injection Using Machine Learning: A SurveyPramono PramonoNo ratings yet
- Sy DatabaseDocument6 pagesSy DatabaseAlhaji IdrisNo ratings yet
- Web Application Security - SQL Injection Attacks: For ExampleDocument2 pagesWeb Application Security - SQL Injection Attacks: For ExampleKhushal SinghNo ratings yet
- SQL SmugglingDocument9 pagesSQL Smugglingvendor26No ratings yet
- OWASP Backend SecurityDocument198 pagesOWASP Backend SecurityNano LimaNo ratings yet
- Incident HandlingDocument18 pagesIncident HandlingDijanaaaaaaNo ratings yet
- DMA Chapter No5Document15 pagesDMA Chapter No5Kiran KshirsagarNo ratings yet
- Threat For SQLServersDocument13 pagesThreat For SQLServersTú PhươngNo ratings yet
- Vulnerabilities and Thier Controls-V1Document4 pagesVulnerabilities and Thier Controls-V1B BasitNo ratings yet
- Ethics - Lect6 - SQL InjectionDocument19 pagesEthics - Lect6 - SQL Injectionomarnader16No ratings yet
- Packet SniiferDocument10 pagesPacket SniiferAryan PanchalNo ratings yet
- IPsec Encryption & Authentication ProtocolsDocument4 pagesIPsec Encryption & Authentication ProtocolsAryan PanchalNo ratings yet
- Dyna 85 KitDocument6 pagesDyna 85 KitAryan PanchalNo ratings yet
- What is PGP? Pretty Good Privacy Encryption ExplainedDocument9 pagesWhat is PGP? Pretty Good Privacy Encryption ExplainedAryan PanchalNo ratings yet
- Naquestionbank3 PDFDocument1 pageNaquestionbank3 PDFAryan PanchalNo ratings yet
- CamScanner Scans PDFs from PhotosDocument3 pagesCamScanner Scans PDFs from PhotosAryan PanchalNo ratings yet
- Motherboard Components: By:-Aryan Panchal Roll No: - 1881026Document10 pagesMotherboard Components: By:-Aryan Panchal Roll No: - 1881026Aryan PanchalNo ratings yet
- IBM System 360/370/390: Section 3.2 CISCDocument62 pagesIBM System 360/370/390: Section 3.2 CISCAryan PanchalNo ratings yet
- NotesDocument536 pagesNotesvaibhavNo ratings yet
- MB COMPONENTS GUIDEDocument10 pagesMB COMPONENTS GUIDEAryan PanchalNo ratings yet
- IBM System 360/370/390: Section 3.2 CISCDocument62 pagesIBM System 360/370/390: Section 3.2 CISCAryan PanchalNo ratings yet
- MB COMPONENTS GUIDEDocument10 pagesMB COMPONENTS GUIDEAryan PanchalNo ratings yet
- MB COMPONENTS GUIDEDocument10 pagesMB COMPONENTS GUIDEAryan PanchalNo ratings yet
- I 2int PDFDocument27 pagesI 2int PDFAryan PanchalNo ratings yet
- CSE 2016 Rev PDFDocument127 pagesCSE 2016 Rev PDFAryan Panchal0% (1)
- CSE 2016 Rev PDFDocument127 pagesCSE 2016 Rev PDFAryan Panchal0% (1)
- CSE 2016 Rev PDFDocument127 pagesCSE 2016 Rev PDFAryan Panchal0% (1)
- Chap 1 DhamdhereDocument84 pagesChap 1 DhamdhereVidya SisaleNo ratings yet
- PCI Compliance: Daniel SimonsDocument17 pagesPCI Compliance: Daniel Simonsdsimons1189No ratings yet
- CSS322Y12S2H02 Simplified AES Example PDFDocument5 pagesCSS322Y12S2H02 Simplified AES Example PDFDelmaNo ratings yet
- Blueprint Ceh v10Document3 pagesBlueprint Ceh v10Abdul KarimNo ratings yet
- PHP Login Form With Anti SQL Injection ScriptDocument6 pagesPHP Login Form With Anti SQL Injection ScriptRezy AltNo ratings yet
- DigitalSignature ForouzanDocument23 pagesDigitalSignature ForouzanShubham AgrawalNo ratings yet
- Cylance PROTECTDocument2 pagesCylance PROTECTNikesh dubeyNo ratings yet
- Avg Serial KeysDocument2 pagesAvg Serial Keysshahan5starNo ratings yet
- BSC-IT SEM 5 NETWORK SECURITY UNIT 1 (1) .PPSXDocument42 pagesBSC-IT SEM 5 NETWORK SECURITY UNIT 1 (1) .PPSXHusain PoonawalaNo ratings yet
- 10 Tips To Prevent Malware and Computer Viruses - Reader ModeDocument15 pages10 Tips To Prevent Malware and Computer Viruses - Reader Modeedward nodzoNo ratings yet
- Digital SignatureDocument26 pagesDigital SignatureNeha Dabhi100% (1)
- How To Implement SSH Decryption On A Palo Alto ... Palo Alto Networks LiveDocument3 pagesHow To Implement SSH Decryption On A Palo Alto ... Palo Alto Networks LiveChau NguyenNo ratings yet
- Instructure Canvas Security Summary 2014Document7 pagesInstructure Canvas Security Summary 2014SheloqNo ratings yet
- KB1598-Cifs Server Passthru Vs Net Logon Style AuthenticationDocument7 pagesKB1598-Cifs Server Passthru Vs Net Logon Style AuthenticationDon McCallNo ratings yet
- Web Security: FlipkartDocument9 pagesWeb Security: Flipkartmuhammad farhanNo ratings yet
- Introduction To Cryptography-AnswersDocument15 pagesIntroduction To Cryptography-AnswerskheyNo ratings yet
- Cybereason Cobalt Kitty - AnswersDocument15 pagesCybereason Cobalt Kitty - AnswersMuhammad AliNo ratings yet
- B How Drive Encryption Works WP 21275920Document8 pagesB How Drive Encryption Works WP 21275920Ciprian Laurentiu CazanelNo ratings yet
- Secure Coding Practices in Java: Challenges and VulnerabilitiesDocument13 pagesSecure Coding Practices in Java: Challenges and VulnerabilitiesPaolaNo ratings yet
- Salamat Aking Ina (Tula-Tulaan) - MODERNONGKABATAAN - WattpadDocument3 pagesSalamat Aking Ina (Tula-Tulaan) - MODERNONGKABATAAN - WattpadJomer Ruego0% (1)
- A Review Paper On Cyber Security: Saloni KhuranaDocument2 pagesA Review Paper On Cyber Security: Saloni KhuranaAtharva PatilNo ratings yet
- Bloqueo de Paginas WebDocument633 pagesBloqueo de Paginas WebkevinNo ratings yet
- 50akun Free FireDocument14 pages50akun Free FireIyz Haniuddin100% (5)
- Denial of Service AttackDocument3 pagesDenial of Service AttackSuryansh SinghNo ratings yet
- Cyber Security PolicyDocument21 pagesCyber Security Policydelhi guyNo ratings yet
- Top 10 Cybercrime Stories of 2018Document75 pagesTop 10 Cybercrime Stories of 2018Mine SweeperNo ratings yet
- Playfair Cipher 2Document19 pagesPlayfair Cipher 2Abhishek DaveNo ratings yet
- Configuring OAM 11g Server in CERT ModeDocument3 pagesConfiguring OAM 11g Server in CERT ModeDenem OrhunNo ratings yet
- Key Management and DistributionDocument12 pagesKey Management and DistributionVasantha KumariNo ratings yet