Professional Documents
Culture Documents
Devoir SQL
Uploaded by
Mohamed Chiheb Ben chaâbaneOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Devoir SQL
Uploaded by
Mohamed Chiheb Ben chaâbaneCopyright:
Available Formats
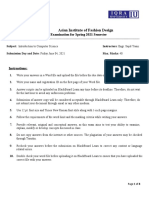
Answer Justification is not mandatory unless demanded
In the QUIZ part, just put the correct letter(s), no justification needed
PART A : QUIZ
PART B : NoSQL USE CASES
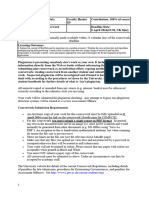
A Digital Marketing agency is investigating about anonymous spam infiltration on its own social
media networks.
What is the most suitable data type to store the investigation results ?
a. Key/Value
b. Document
c. Object
d. Graph
e. Column-Wide
f. Time-Series
An enterprise wants to detect unauthorized access from external users to its private resources
(servers, websites, ..).
What is the most suitable data type to record all unauthorized access initiatives ?
a. Key/Value
b. Document
c. Object
d. Graph
e. Column-Wide
f. Time-Series
A geological centre is monitoring realtime volcanic activity.
What is the most suitable data type to record it ?
a. Key/Value
b. Document
c. Object
d. Graph
e. Column-Wide
f. Time-Series
An internet agency is dealing with DNS servers as follows:
IP URL
172.16.20.3 www.test1Fin.com
10.2.100.1 www.commerce.rnu.tn
10.2.100.2 www.googler.tn
199.45.63.1
4 www.livreFR.net
What is the most suitable data type to store DNS informations ?
a. Key/Value
b. Document
c. Object
d. Graph
e. Column-Wide
f. Time-Series
A library is designing a data store that contains all Book informations as follows:
Book ID Book information
Title : Finance HandBook
Pages : 325
120-1588-251 Price : 14 DT
Title : Finance Crisis
Pages : 630
Price : 54 DT
120-1588-222
Editor : Huffman
Title : Finance Crisis
Pages : 630
Price : 54 DT
120-1588-444
Stock : Available
What is the most suitable data type to store Book informations ?
a. Key/Value
b. Document
c. Object
d. Graph
e. Column-Wide
f. Time-Series
PART C : SQL QUERYING + NON-RELATIONAL DATA
Part C.1 : SQL QUERYING
A Book Library needs to manage its IT System through an RDBMS approach. For dealing with that
concept, let’s consider the tables mentioned below :
Book(ISBN, title, NumberOfPages, price, DateOfPulishing, #IdEditor)
Customer(Reference, Name, Address, Email, Age, Tel)
Purchase(Quantity, DateOfPurchase, #ISBN, #Reference)
Editor(IdEditor, label, Fax, Telephone, website)
1. Draw the Relational Schema (as in Access DBMS)
2. Why the table Purchase does not contain any Primary key?
3. What kind of field is #IdEditor ? Why we use it ?
With SQL language, determine these queries:
a. Insert data into table Editor
b. Insert data into table Customer
c. Insert data into table Book
d. Insert data into table Purchase
e. Display the table Customer (All Data)
f. Diplay the title and NumberOfPages of all Books
g. Display the Sum of Prices’ Books
h. Display the Average of Customer’s Age
i. Display all Customers living in Tunis
j. Display all Customers living in Tunis sorted by name
k. Display all Customers living in Tunis whom name begins by ‘A’
l. Display all Customers living in Tunis whom the 3rd letter of their name is ‘B’
m. Display all Customers living in Tunis whom email end by ‘gmail.com’
n. Display all Customers living in Tunis and Sfax
o. Display all Books published before 2013
p. Display all Books published between 2012 and 2015
Part C.2 : NoSQL & Data
By the evolution of IT technologies, this Book Library decides to optimize the purchase rate. So,
it implements a Digital Marketing Strategy on Social Media websites (Facebook, Twitter, ..) and
secures purchasing via Blockchain Technology.(Web 3.0)
4. Is the RDBMS approach still suitable for this implementation ? if NO, What the most suitable
approach? Justify.
Let’s assume that a Customer is characterized by these items :
Customer(Reference, Name, Address, Email, Age, Tel, PersonalPhoto, Self_Video)
5. What type of NoSQL is convenient for these changes ?
6. Can CosmosDB be the right choice as a DBMS ? Justify.
After many years, this Book Library turns into a big holding (like Amazon) and becomes
widespread all over the world. So, it makes a decision to reduce its Capex charges.
7. What is the key solution for that situation ? Justify.
PART C : SQL QUERYING + NON-RELATIONAL DATA
Part C.1 : SQL QUERYING
An Academic institution needs to manage its IT System through an RDBMS approach. For dealing
with that concept, let’s consider the tables mentioned below :
Course(NumberC, title, NumberOfHours, Classroom, Genre, # IdTeacher)
Student(Id, Name, Address, Email, Age, Tel)
Learning(Status, DateOfClass, # NumberC, #Id)
Teacher(IdTeacher, FullName, YearsOfExperience, Telephone)
1. Draw the Relational Schema (as in Access DBMS)
2. Why the table Learning does not contain any Primary key ?
3. What kind of field is #IdTeacher ? Why we use it ?
With SQL language, determine these queries :
a. Insert data into table Teacher
b. Insert data into table Student
c. Insert data into table Course
d. Insert data into table Learning
e. Display the table Student (All Data)
f. Diplay the title and NumberOfHours of all Courses
g. Display the Sum of NumberOfHours for all Courses
h. Display the Average of Student’s Age
i. Display all Students living in Tunis
j. Display all Students living in Tunis sorted by name
k. Display all Students living in Tunis whom name begins by ‘N’
l. Display all Students living in Tunis whom the 4th letter of their name is ‘C’
m. Display all Students living in Tunis whom email end by ‘gmail.com’
n. Display all Students living in Tunis and Bizerte
o. Display all Courses learned before 2020
p. Display all Courses learned between 2012 and 2015
Part C.2 : NoSQL & Data
By the evolution of IT technologies, this Book Library decides to optimize the purchase rate. So,
it implements a Digital Marketing Strategy on Social Media websites (Facebook, Twitter, ..) and
secures purchasing via Blockchain Technology.
4. Is the RDBMS approach still convenient for this implementation ? if NO, What the most
suitable approach? Justify.
InfluxDB is a _______________ NoSQL type
a. Object
b. Column-Wide
c. Time-Series
MongoDB is a _______________ NoSQL type
a. Object
b. Column-Wide
c. Document
You might also like
- Ace the Trading Systems Developer Interview (C++ Edition) : Insider's Guide to Top Tech Jobs in FinanceFrom EverandAce the Trading Systems Developer Interview (C++ Edition) : Insider's Guide to Top Tech Jobs in FinanceRating: 5 out of 5 stars5/5 (1)
- 3 FINANCE Homework Assessment Digital Skills - Answer KEYSDocument9 pages3 FINANCE Homework Assessment Digital Skills - Answer KEYSSaadaoui MayssaNo ratings yet
- Itis 2P91 Midterm QuestionDocument28 pagesItis 2P91 Midterm QuestionnguyentamNo ratings yet
- College of Accountancy and Business Administration: Data, Information, and KnowledgeDocument2 pagesCollege of Accountancy and Business Administration: Data, Information, and Knowledgejelyn bermudezNo ratings yet
- Database Coursework ExamplesDocument5 pagesDatabase Coursework Examplesphewzeajd100% (2)
- Data Warehousing and Business Intelligence DS-3003 Assignment # 1Document6 pagesData Warehousing and Business Intelligence DS-3003 Assignment # 1I211381 Eeman IjazNo ratings yet
- DD1 Practice Activities - AnswersDocument3 pagesDD1 Practice Activities - Answersgery sumualNo ratings yet
- Practice Lab QuestionsDocument4 pagesPractice Lab QuestionsRAJA.S 41No ratings yet
- 5 Sess Prac MTDocument5 pages5 Sess Prac MTblazeNo ratings yet
- Ctai Midterm QuizDocument26 pagesCtai Midterm Quizmoncarla lagonNo ratings yet
- B.E / B.Tech./B.Arch. Practical End Semester Examinations, April / May 2021Document5 pagesB.E / B.Tech./B.Arch. Practical End Semester Examinations, April / May 2021Ramkumar RamakrishnanNo ratings yet
- Internet Technology Question PaperDocument3 pagesInternet Technology Question PaperAbhishek Acharya50% (2)
- Kids Camp Innovative Learning Academy: First Quarter Examination Ict 9Document4 pagesKids Camp Innovative Learning Academy: First Quarter Examination Ict 9Ar LouNo ratings yet
- Asian Institute of Fashion DesignDocument8 pagesAsian Institute of Fashion DesignNabeel NesaarNo ratings yet
- Thesis Paper On Big DataDocument7 pagesThesis Paper On Big DataJoe Osborn100% (2)
- TTT 8Document2 pagesTTT 8Proficient WritersNo ratings yet
- Thesis o MeterDocument6 pagesThesis o Meterzeh0silun0z2100% (2)
- E21 Quest Set2Document9 pagesE21 Quest Set2Logesh LogeshNo ratings yet
- Cls 8 Term1 PortionDocument12 pagesCls 8 Term1 PortionThilagavathi SekkizharNo ratings yet
- B.E / B.Tech./B.Arch. Practical End Semester Examinations, April / May 2019Document6 pagesB.E / B.Tech./B.Arch. Practical End Semester Examinations, April / May 2019graciaNo ratings yet
- IMDB Scraping & AnalysisDocument5 pagesIMDB Scraping & Analysisvarun goelNo ratings yet
- CS8481 - File-1.0Document5 pagesCS8481 - File-1.04021 MAHESWARAN GNo ratings yet
- FM 124-Paper ModellDocument8 pagesFM 124-Paper ModellManjula Gayan JayawardenaNo ratings yet
- CS8481 - Set2Document5 pagesCS8481 - Set2ffffffffffffffffNo ratings yet
- Quiz Bank (1-17)Document101 pagesQuiz Bank (1-17)Donnie Zha100% (1)
- ID 16545 Final ExamDocument17 pagesID 16545 Final ExamAmmar Ali KhanNo ratings yet
- AIS QuesDocument13 pagesAIS QuesNguyễn Hương QuỳnhNo ratings yet
- MCQs - Big Data Analytics - FundamentalsDocument14 pagesMCQs - Big Data Analytics - FundamentalsZuniButtNo ratings yet
- Utoronto Thesis SubmissionDocument6 pagesUtoronto Thesis Submissionafjryccau100% (1)
- Q.1 (A) Give Full Form of Following AcronymDocument16 pagesQ.1 (A) Give Full Form of Following AcronymsvNo ratings yet
- Aditya Sharma - Untitled DocumentDocument14 pagesAditya Sharma - Untitled DocumentAditya SharmaNo ratings yet
- Ict Coursework DatabaseDocument6 pagesIct Coursework Databasexmufyevcf100% (2)
- CS8481 - 18.2Document5 pagesCS8481 - 18.2sandhiya35% (26)
- 2015 E-Commerce Strategies Syllabus - v2Document12 pages2015 E-Commerce Strategies Syllabus - v2Anjali RoyNo ratings yet
- Myra Tle 7 3RD Quarter Long TestDocument4 pagesMyra Tle 7 3RD Quarter Long TestMichael Angelo BandalesNo ratings yet
- Vinoth Kumar ResumeDocument5 pagesVinoth Kumar ResumeVinoth KumarNo ratings yet
- Vinoth Kumar ResumeDocument5 pagesVinoth Kumar ResumeVinoth KumarNo ratings yet
- Manav Rachna International Institute of Research and StudiesDocument5 pagesManav Rachna International Institute of Research and StudiespriyankaNo ratings yet
- AWS CP QuestionDocument5 pagesAWS CP QuestionitsmathanjoeNo ratings yet
- g064 Ict Coursework ExampleDocument6 pagesg064 Ict Coursework Exampleafjwdbaekycbaa100% (2)
- Doing Business OnlinedocDocument3 pagesDoing Business OnlinedocVarga CasianaNo ratings yet
- Computer Assignment 2015 Second Semester STD ViiiDocument9 pagesComputer Assignment 2015 Second Semester STD Viiiapi-235229818No ratings yet
- CT101 - Midterm ExamDocument8 pagesCT101 - Midterm ExamPrincess Ira SantillanNo ratings yet
- Igcse Computer Coursework SampleDocument6 pagesIgcse Computer Coursework Samplef633f8cz100% (2)
- Time Series DatabasesDocument81 pagesTime Series DatabasesEl Presidente100% (2)
- All Multiple Choice Without AnswerDocument26 pagesAll Multiple Choice Without Answersiyun ZhangNo ratings yet
- Webpage Design MODULEDocument129 pagesWebpage Design MODULEJanine CallanganNo ratings yet
- CS413 Q&aDocument31 pagesCS413 Q&adean odeanNo ratings yet
- 12th - Commerce - Prelim Paper1Document7 pages12th - Commerce - Prelim Paper1SALMA ANSARINo ratings yet
- 2024 COMP1702CourseWorkDocument5 pages2024 COMP1702CourseWorkpratati.assurex1288No ratings yet
- Materials Today: ProceedingsDocument5 pagesMaterials Today: Proceedings76lunaluNo ratings yet
- Privacy and Security Combine Assignment 2023Document49 pagesPrivacy and Security Combine Assignment 2023heydev975No ratings yet
- Lesson 3 Chapter WorkDocument2 pagesLesson 3 Chapter WorkSarahNo ratings yet
- Name: - Score: - Grade & Section: - Date: - AnswerDocument4 pagesName: - Score: - Grade & Section: - Date: - AnswerLeonard GuevarraNo ratings yet
- Cape Notes Unit 2 Database ManagementDocument3 pagesCape Notes Unit 2 Database ManagementPratimaNo ratings yet
- A. Write A 500-Word Article On Trending IT Technologies in 2023Document5 pagesA. Write A 500-Word Article On Trending IT Technologies in 2023Hanwant Singh CharanNo ratings yet
- ICT Final Exam DoneDocument6 pagesICT Final Exam DoneAzka RivanNo ratings yet
- Data Description For Data MiningDocument7 pagesData Description For Data MiningKimondo KingNo ratings yet
- Getting Structured Data from the Internet: Running Web Crawlers/Scrapers on a Big Data Production ScaleFrom EverandGetting Structured Data from the Internet: Running Web Crawlers/Scrapers on a Big Data Production ScaleNo ratings yet
- ICDL Project Planning 2013 1.0Document116 pagesICDL Project Planning 2013 1.0Akshit100% (1)
- Com - Cherisher.beauty - Camera.videocall LogcatDocument24 pagesCom - Cherisher.beauty - Camera.videocall Logcatbh4240103No ratings yet
- Vision To Reality Experience: Tareq Amin Rakuten Mobile - Chief Technology OfficerDocument23 pagesVision To Reality Experience: Tareq Amin Rakuten Mobile - Chief Technology OfficerVSG EnergiaNo ratings yet
- MINI-LINK 6352 Eband - CommissioningDocument23 pagesMINI-LINK 6352 Eband - CommissioningmohaelexNo ratings yet
- Descriptive QuestionsDocument13 pagesDescriptive QuestionsRohain KoulNo ratings yet
- Fortios v6.0.9 Release NotesDocument37 pagesFortios v6.0.9 Release NotesM3iatNo ratings yet
- Revit Pure BASICS RailingsDocument35 pagesRevit Pure BASICS RailingsWunNa100% (1)
- Cifx API PR 05 ENDocument118 pagesCifx API PR 05 ENjulio perezNo ratings yet
- HP Disk Drive Replacement Instructions: About This DocumentDocument5 pagesHP Disk Drive Replacement Instructions: About This DocumentsteveNo ratings yet
- 067232153X C# and The .NET Framework The C++ Perspective (Powell & Weeks 2001-10-06) (28B5A6A0)Document636 pages067232153X C# and The .NET Framework The C++ Perspective (Powell & Weeks 2001-10-06) (28B5A6A0)Yan MikhlinNo ratings yet
- 50 Challenging Problems in ProbabilityDocument96 pages50 Challenging Problems in ProbabilityJohn Romer GarciaNo ratings yet
- Primavera P6: by Biplab MondalDocument20 pagesPrimavera P6: by Biplab MondalBiplab233No ratings yet
- Technical Information Letter: GE PowerDocument5 pagesTechnical Information Letter: GE PowerAbelNo ratings yet
- Group Asg - HostedSP - GatoradersDocument19 pagesGroup Asg - HostedSP - GatoradersĐặng Hưng100% (2)
- TCL 40fs3800 Spec SheetDocument2 pagesTCL 40fs3800 Spec Sheettony castilloNo ratings yet
- EmTech Module 2Document45 pagesEmTech Module 2Frantiska FartelióNo ratings yet
- Introduction To SIS-LMSDocument9 pagesIntroduction To SIS-LMSMayom MabuongNo ratings yet
- System Requirements (iTWO Costx Client)Document7 pagesSystem Requirements (iTWO Costx Client)John michael Del rosarioNo ratings yet
- 1.GxP Assessment Document of SCADA System FormDocument9 pages1.GxP Assessment Document of SCADA System FormFurquan KhanNo ratings yet
- Engineering Design Review and ChecklistDocument40 pagesEngineering Design Review and ChecklistwnaciNo ratings yet
- Saketh ResumeDocument2 pagesSaketh ResumeugiyuNo ratings yet
- Afifarm 5.2 InstallationDocument57 pagesAfifarm 5.2 InstallationlegarciNo ratings yet
- CSC 223 NotesDocument20 pagesCSC 223 NotesDerayo OkunadeNo ratings yet
- Core Value Activity/ies Description Partner Venue/Platform RemarksDocument3 pagesCore Value Activity/ies Description Partner Venue/Platform RemarksMaria Leira Calubayan Laurel100% (8)
- MCA 2-Year Syllabus - (Session) 2020-22Document67 pagesMCA 2-Year Syllabus - (Session) 2020-22kavitadagarNo ratings yet
- User Manual For Benz NTG 5 - 0Document18 pagesUser Manual For Benz NTG 5 - 0David SchapiroNo ratings yet
- Caso The Iphone at IVKDocument3 pagesCaso The Iphone at IVKEdgardoNo ratings yet
- Sniffer Pro HowtoDocument80 pagesSniffer Pro Howto林庭No ratings yet
- SmileMakers Canada - PRD - W2 - Report - 2023-07-15 - 17-25-36Document3 pagesSmileMakers Canada - PRD - W2 - Report - 2023-07-15 - 17-25-36ashok_abclNo ratings yet
- Control 4 EA3 Installation ManualDocument2 pagesControl 4 EA3 Installation ManualNida FloresNo ratings yet