Professional Documents
Culture Documents
List of Documents ISO 27001 Documentation Toolkit en
Uploaded by
Rui GonzagaOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
List of Documents ISO 27001 Documentation Toolkit en
Uploaded by
Rui GonzagaCopyright:
Available Formats
This file has been cleaned of potential threats.
If you confirm that the file is coming from a trusted source, you can send the following SHA-256
hash value to your admin for the original file.
6dc9dadca7eb42632b2b656bdf496d9b8d75f6aa0bdf7b2f65991c8e93559ca5
To view the reconstructed contents, please SCROLL DOWN to next page.
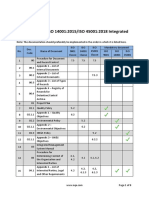
ISO 27001 Documentation Toolkit
https://advisera.com/27001academy/iso-27001-documentation-toolkit/
Note: The documentation should preferably be implemented in the order in which it is listed here.
The order of implementation of documentation related to Annex A is defined in the Risk Treatment
Plan.
Mandatory
Document Relevant clauses in
No. Document name according to
code ISO 27001
ISO 27001
01 Document Management
Procedure for Document and
1 01 7.5; A.5.33
Record Control
02 Preparations for the Project
2 02 Project Plan
03 Identification of Requirements
Procedure for Identification of
3 03 4.2; A.5.31
Requirements
Appendix 1 – List of Legal,
4 03.1 Regulatory, Contractual and Other 4.2; A.5.29; A.5.31 *
Requirements
04 ISMS Scope
5 04 ISMS Scope Document 4.3
05 General Policies
5.2; 5.3**; 6.2; 7.4;
6 05 Information Security Policy
A.6.3
Risk Assessment and Risk
06
Treatment
Risk Assessment and Risk Treatment
7 06 6.1.2; 6.1.3; 8.2; 8.3
Methodology
8 06.1 Appendix 1 – Risk Assessment Table 6.1.2; 8.2
9 06.2 Appendix 2 – Risk Treatment Table 6.1.3; 8.3
ver 1.0, 2022-06-08 Page 1 of 5
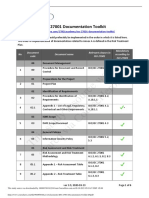
Mandatory
Document Relevant clauses in
No. Document name according to
code ISO 27001
ISO 27001
Appendix 3 – Risk Assessment and
10 06.3 8.2; 8.3
Treatment Report
07 Applicability of Controls
11 07 Statement of Applicability 6.1.3 d)
08 Implementation Plan
6.1.3; 6.2; 7.1; 8.3;
12 08 Risk Treatment Plan
9.1
09 Annex A – Security Controls
A.5.9; A.5.10;
A.5.11; A.5.14;
A.5.17; A.5.32;
A.6.7; A.7.7; A.7.9;
13 09.01 IT Security Policy *
A.7.10; A.8.1; A.8.7;
A.8.10; A.8.12;
A.8.13; A.8.19;
A.8.23
Clear Desk and Clear Screen Policy
14 09.02 (Note: This can be implemented as A.7.7; A.8.1
part of the IT Security Policy.)
Mobile Device, Teleworking and
Work from Home Policy (Note: This
15 09.03 A.6.7; A.7.9; A.8.1
can be implemented as part of the
IT Security Policy.)
Bring Your Own Device (BYOD)
16 09.04 A.5.14; A.6.7; A.8.1
Policy
Procedures for Working in Secure
17 09.05 A.7.4; A.7.6
Areas
A.5.9; A.5.10;
A.5.12; A.5.13;
18 09.06 Information Classification Policy *
A.5.14; A.7.10;
A.8.3; A.8.5; A.8.11
ver 1.0, 2022-06-08 Page 2 of 5
Mandatory
Document Relevant clauses in
No. Document name according to
code ISO 27001
ISO 27001
19 09.07 Inventory of Assets A.5.9
A.5.7; A.5.14;
A.5.37; A.7.10;
A.7.14; A.8.4; A.8.6;
A.8.7; A.8.8; A.8.9;
A.8.10; A.8.12;
Security Procedures for IT
20 09.08 A.8.13; A.8.15; *
Department
A.8.16; A.8.17;
A.8.18; A.8.20;
A.8.21; A.8.22;
A.8.23; A.8.31;
A.8.32
Change Management Policy (Note:
This can be implemented as part of
21 09.09 A.8.32
the Security Procedures for IT
Department.)
Backup Policy (Note: This can be
22 09.10 implemented as part of the Security A.8.13
Procedures for IT Department.)
Information Transfer Policy (Note:
This can be implemented as part of
23 09.11 A.5.14
the Security Procedures for IT
Department.)
Disposal and Destruction Policy
(Note: This can be implemented as A.7.10; A.7.14;
24 09.12
part of the Security Procedures for A.8.10
IT Department.)
25 09.13 Policy on the Use of Encryption A.5.31; A.8.24
A.5.15; A.5.16;
A.5.17; A.5.18;
26 09.14 Access Control Policy
A.8.2; A.8.3; A.8.4;
A.8.5; A.8.11
ver 1.0, 2022-06-08 Page 3 of 5
Mandatory
Document Relevant clauses in
No. Document name according to
code ISO 27001
ISO 27001
Password Policy (Note: This can be
A.5.16; A.5.17;
27 09.15 implemented as part of the Access
A.5.18
Control Policy.)
A.5.33; A.8.11;
A.8.25; A.8.26;
A.8.27; A.8.28;
28 09.16 Secure Development Policy *
A.8.29; A.8.30;
A.8.31; A.8.32;
A.8.33
Appendix 1 – Specification of
29 09.17 A.8.26
Information System Requirements
A.5.7; A.5.11;
A.5.19; A.5.20;
30 09.18 Supplier Security Policy A.5.21; A.5.22;
A.5.23; A.6.1; A.6.2;
A.6.3; A.8.30
Security Clauses for Suppliers and A.5.20; A.5.21;
31 09.19
Partners A.6.2; A.8.30
7.4; A.5.7; A.5.24;
A.5.25; A.5.26;
32 09.20 Incident Management Procedure *
A.5.27; A.5.28;
A.6.4; A.6.8
33 09.21 Appendix 1 – Incident Log A.5.27
7.4; A.5.29; A.5.30;
34 09.22 Disaster Recovery Plan
A.8.14
A.5.20; A.6.2; A.6.5;
35 09.23 Confidentiality Statement *
A.6.6
Statement of Acceptance of ISMS
36 09.24 A.6.2
Documents
10 Training & Awareness
37 10 Training and Awareness Plan 7.2; 7.3; 7.4; A.6.3
ver 1.0, 2022-06-08 Page 4 of 5
Mandatory
Document Relevant clauses in
No. Document name according to
code ISO 27001
ISO 27001
11 Internal Audit
9.2; A.5.30; A.5.35;
38 11 Internal Audit Procedure
A.8.34
Appendix 1 – Annual Internal Audit
39 11.1 9.2
Program
40 11.2 Appendix 2 – Internal Audit Report 9.2
Appendix 3 – Internal Audit
41 11.3 9.2
Checklist
12 Management Review
42 12.1 Measurement Report 6.2; 9.1
43 12.2 Management Review Minutes 9.3
13 Corrective Actions
44 13 Procedure for Corrective Action 10.1; A.5.27
45 13.1 Appendix 1 – Corrective Action Form 10.1; 10.2
*The listed documents are mandatory only if the corresponding controls are identified as applicable
in the Statement of Applicability.
**General roles and responsibilities are described in the Information Security Policy, whereas
detailed roles and responsibilities are specified in each document of this toolkit.
ver 1.0, 2022-06-08 Page 5 of 5
You might also like
- List of Documents ISO 27001Document5 pagesList of Documents ISO 27001Taraj O K100% (2)
- List of Documents ISO 27001 2022 Documentation Toolkit ENDocument5 pagesList of Documents ISO 27001 2022 Documentation Toolkit ENLETSOGILENo ratings yet
- List of Documents ISO 27001 2022 Documentation Toolkit ENDocument5 pagesList of Documents ISO 27001 2022 Documentation Toolkit ENzayadeen2003No ratings yet
- List of Documents ISO 27001 Documentation Toolkit ENDocument5 pagesList of Documents ISO 27001 Documentation Toolkit ENskyronight 420No ratings yet
- List of Documents ISO 27001 Documentation Toolkit enDocument6 pagesList of Documents ISO 27001 Documentation Toolkit enSon DepNo ratings yet
- Checklist of ISO 27001 Mandatory DocumentationDocument12 pagesChecklist of ISO 27001 Mandatory Documentationprtiamshah75% (4)
- Checklist of Mandatory Documentation Required by ISO/IEC 27001 (2013 Revision)Document12 pagesChecklist of Mandatory Documentation Required by ISO/IEC 27001 (2013 Revision)Lyubomir Gekov100% (1)
- ISMS Documented Information by Andrey Prozorov v.5.1 230305Document3 pagesISMS Documented Information by Andrey Prozorov v.5.1 230305kenyrNo ratings yet
- List of Documents ISO 13485 ISO 14971 Premium Documentation Toolkit enDocument4 pagesList of Documents ISO 13485 ISO 14971 Premium Documentation Toolkit enMichal KrawczynskiNo ratings yet
- Checklist of Mandatory Documentation Required by ISO 27001 2013 PDFDocument9 pagesChecklist of Mandatory Documentation Required by ISO 27001 2013 PDFKaran MehtaNo ratings yet
- Mandatory Document ISO 27001Document2 pagesMandatory Document ISO 27001Madhava TechnologyNo ratings yet
- 0 ISMS Documented Information RequirementsDocument6 pages0 ISMS Documented Information RequirementsCarlo San JuanNo ratings yet
- Checklist of ISO 27001 Mandatory Documentation ENDocument13 pagesChecklist of ISO 27001 Mandatory Documentation ENRoberto CezarNo ratings yet
- ISO 9001:2015/ISO 14001:2015 Integrated Documentation ToolkitDocument4 pagesISO 9001:2015/ISO 14001:2015 Integrated Documentation ToolkitDr. Naveen KumarNo ratings yet
- ISO 27001 MappingDocument17 pagesISO 27001 MappingNikolas Kyriakidis100% (1)
- List of Documents ISO 13485 Documentation ToolkitDocument4 pagesList of Documents ISO 13485 Documentation ToolkitGreeshma Certvalue100% (3)
- NQA List of Documents ISO 9001 14001 45001 Integrated PTDocument9 pagesNQA List of Documents ISO 9001 14001 45001 Integrated PTRia100% (1)
- ISO 9001:2015/14001:2015/45001:2018 ToolkitDocument9 pagesISO 9001:2015/14001:2015/45001:2018 ToolkitPaulino MutomboNo ratings yet
- List of Documents ISO 9001 ISO 14001 ISO 45001Document9 pagesList of Documents ISO 9001 ISO 14001 ISO 45001Karlita Marina Rengifo ReáteguiNo ratings yet
- List of Documents ISO 9001 ISO 14001 ISO 45001 Documentation Toolkit enDocument9 pagesList of Documents ISO 9001 ISO 14001 ISO 45001 Documentation Toolkit enAquino Sianipar67% (3)
- Framework Mapping: HITRUST CSF V9 TO ISO 27001/27002:2013Document11 pagesFramework Mapping: HITRUST CSF V9 TO ISO 27001/27002:2013vick_zoneNo ratings yet
- Document Clause Control - Mapping PDFDocument7 pagesDocument Clause Control - Mapping PDFamitom_pandey4974No ratings yet
- List of Documents ISO 45001 Documentation Toolkit EN PDFDocument2 pagesList of Documents ISO 45001 Documentation Toolkit EN PDFCiciaSalatinNo ratings yet
- List of Documents ISO 45001 Documentation Toolkit enDocument2 pagesList of Documents ISO 45001 Documentation Toolkit enCiciaSalatin100% (1)
- Checklist of ISO 27001 Mandatory Documentation enDocument9 pagesChecklist of ISO 27001 Mandatory Documentation enRoshan JayakodyNo ratings yet
- ISO 27001 Project Tasks and Status TrackingDocument85 pagesISO 27001 Project Tasks and Status TrackingMe100% (1)
- ISO 45001 Premium Documentation Toolkit: No. Doc. Code Document Name ISO 45001 Clause Mandatory DocumentDocument3 pagesISO 45001 Premium Documentation Toolkit: No. Doc. Code Document Name ISO 45001 Clause Mandatory Documentpaolino63No ratings yet
- List of Documents ISO 45001 Premium Documentation Toolkit enDocument3 pagesList of Documents ISO 45001 Premium Documentation Toolkit envirat100% (1)
- ISO 45001 Documentation Toolkit LightDocument1 pageISO 45001 Documentation Toolkit LightTuduran CameliaNo ratings yet
- ISO 27001 Documents and Records GuideDocument4 pagesISO 27001 Documents and Records Guidedeewanand60% (5)
- List of Documents ISO 13485Document3 pagesList of Documents ISO 13485Priya DasNo ratings yet
- List of Documents ISO 27001 ISO 27017 ISO 27018 Cloud-EnDocument13 pagesList of Documents ISO 27001 ISO 27017 ISO 27018 Cloud-EnseshaNo ratings yet
- ISO 9001 DocumentationDocument3 pagesISO 9001 DocumentationBogdan BătrânuNo ratings yet
- ISO 27001 Mandatory Docs List (40Document2 pagesISO 27001 Mandatory Docs List (40sibinsukumaranPsibi3No ratings yet
- IsoDocument4 pagesIsoTejendra GohilNo ratings yet
- ISO27001 Ver 2013Document43 pagesISO27001 Ver 2013zk55595559No ratings yet
- ISMS Audit v3Document53 pagesISMS Audit v3k sirisha100% (1)
- ISO27k Guideline On ISMS Audit v2Document52 pagesISO27k Guideline On ISMS Audit v2kingnachi100% (1)
- sp800 53r5 To Iso 27001 MappingDocument14 pagessp800 53r5 To Iso 27001 Mappingpioneers ksaNo ratings yet
- ISO27k Guideline On ISMS Audit v2Document57 pagesISO27k Guideline On ISMS Audit v2Fredy AvilaNo ratings yet
- Audit Question ListDocument38 pagesAudit Question ListelevendotNo ratings yet
- List of Documents ISO 27001 Documentation Toolkit EN PDFDocument5 pagesList of Documents ISO 27001 Documentation Toolkit EN PDFsaravanancs1986No ratings yet
- ISO 27001 BMS-2017 - ISO 27001 BMS-2017 - Document Jayesh TechnologiesDocument17 pagesISO 27001 BMS-2017 - ISO 27001 BMS-2017 - Document Jayesh TechnologiesAnil ThomasNo ratings yet
- Top 10 Entities and Controls from ISO 27001 DocumentationDocument51 pagesTop 10 Entities and Controls from ISO 27001 DocumentationTannyk Ponce100% (1)
- List of Documents ISO 9001 Documentation Toolkit Light EN PDFDocument1 pageList of Documents ISO 9001 Documentation Toolkit Light EN PDFgheoda8926No ratings yet
- Secure & Simple – A Small-Business Guide to Implementing ISO 27001 On Your Own: The Plain English, Step-by-Step Handbook for Information Security PractitionersFrom EverandSecure & Simple – A Small-Business Guide to Implementing ISO 27001 On Your Own: The Plain English, Step-by-Step Handbook for Information Security PractitionersNo ratings yet
- ISO 45001 Documentation Toolkit OverviewDocument2 pagesISO 45001 Documentation Toolkit Overviewvictor100% (1)
- ISO - 45001 Content PackageDocument2 pagesISO - 45001 Content PackageVictor Thembinkosi Makhubele100% (1)
- Control Mapping: ISO 27002:2013 TO ISO 27002:2022Document6 pagesControl Mapping: ISO 27002:2013 TO ISO 27002:2022Chi Jui Han100% (4)
- NIST SP 800-53 to ISO/IEC 27001 MappingsDocument15 pagesNIST SP 800-53 to ISO/IEC 27001 MappingsYuri Arcanjo100% (1)
- Getting Started with Building an ISO 27001 Compliant Cybersecurity ProgramDocument2 pagesGetting Started with Building an ISO 27001 Compliant Cybersecurity ProgramMarcio RodriguesNo ratings yet
- This Study Resource Was: ISO 27001 Documentation ToolkitDocument6 pagesThis Study Resource Was: ISO 27001 Documentation Toolkitfawas hamdiNo ratings yet
- IATF 16949 Documentation Toolkit GuideDocument4 pagesIATF 16949 Documentation Toolkit GuideOscar Solis MartirNo ratings yet
- IATF 16949 Documentation Toolkit GuideDocument4 pagesIATF 16949 Documentation Toolkit GuideRahul SharmaNo ratings yet
- FSSC 22000 FSMS Implementation Package V5.1 BrochureDocument44 pagesFSSC 22000 FSMS Implementation Package V5.1 BrochureSutha Tamil Nambe100% (1)
- ISO27001 Documentation EssentialsDocument29 pagesISO27001 Documentation EssentialsSanddy BlastNo ratings yet
- List of Documents EU GDPR ISO 27001 Integrated Documentation Toolkit enDocument7 pagesList of Documents EU GDPR ISO 27001 Integrated Documentation Toolkit enBogdan Cornea100% (4)
- Using Aspect-Oriented Programming for Trustworthy Software DevelopmentFrom EverandUsing Aspect-Oriented Programming for Trustworthy Software DevelopmentRating: 3 out of 5 stars3/5 (1)
- Establishing A CGMP Laboratory Audit System: A Practical GuideFrom EverandEstablishing A CGMP Laboratory Audit System: A Practical GuideNo ratings yet
- The KickbookDocument230 pagesThe KickbookreixelNo ratings yet
- Guidelines On Covid Vaccine For Persons Going AbroadDocument28 pagesGuidelines On Covid Vaccine For Persons Going AbroadVishnu MkNo ratings yet
- Communities of Practice and Knowledge NetworksDocument2 pagesCommunities of Practice and Knowledge Networksaprilrose gajetonNo ratings yet
- PID Controller - Wikipedia, The Free EncyclopediaDocument18 pagesPID Controller - Wikipedia, The Free EncyclopediaHarsha Chaitanya GoudNo ratings yet
- Everything You Need To Know About GradleDocument3 pagesEverything You Need To Know About GradlemahimaNo ratings yet
- Sample BOS IoT Lite BMS Topology DiagramDocument2 pagesSample BOS IoT Lite BMS Topology DiagramWalter BarbaNo ratings yet
- Advantages of Proposed SystemDocument3 pagesAdvantages of Proposed System4JN19CS408 Shreelakshmi cNo ratings yet
- Stinger Ref Guide PDFDocument330 pagesStinger Ref Guide PDFRODRIGO ALVES DA COSTANo ratings yet
- The Ten Commandments For Computer EthicsDocument9 pagesThe Ten Commandments For Computer Ethicsroshan kcNo ratings yet
- Prototype Exam QuestionsDocument3 pagesPrototype Exam QuestionsNnogge LovisNo ratings yet
- FANUC Series 0+-MODEL F CONNECTION MANUAL (FUNCTION) (Volume 2 of 3Document900 pagesFANUC Series 0+-MODEL F CONNECTION MANUAL (FUNCTION) (Volume 2 of 3SergioNo ratings yet
- DR-40 FW-Update enDocument1 pageDR-40 FW-Update enNacho RebaudengoNo ratings yet
- Anchor Bolt Design Example As Per Indian Code - Google SearchDocument2 pagesAnchor Bolt Design Example As Per Indian Code - Google Searchjebin_87No ratings yet
- Raciocínio Clínico Aplicado À Estética Corporal - Dr. João Tassinary PDFDocument231 pagesRaciocínio Clínico Aplicado À Estética Corporal - Dr. João Tassinary PDFLaura Tomazelli100% (1)
- Technical Seminar Child SecurityDocument20 pagesTechnical Seminar Child SecurityGeeta GiragaveNo ratings yet
- Standard Data Formats For Analytical Systems: Status and ChallengesDocument1 pageStandard Data Formats For Analytical Systems: Status and ChallengeschatNo ratings yet
- Domain 3 - Systems and Infrastructure Life Cycle ManagementDocument2 pagesDomain 3 - Systems and Infrastructure Life Cycle ManagementElizabeth PricilliaNo ratings yet
- DHS Study On Mobile Device SecurityDocument125 pagesDHS Study On Mobile Device Securitymaruka33No ratings yet
- Kyle Albert Chanchico Estoesta - Module 11 STS Activity SheetDocument4 pagesKyle Albert Chanchico Estoesta - Module 11 STS Activity SheetKyle Albert EstoestaNo ratings yet
- Vaporwave: Politics, Protest, and IdentityDocument20 pagesVaporwave: Politics, Protest, and IdentityjuanchoNo ratings yet
- OptiSwitch 900 Series User Manual (ML49175A, L2+ Ver. 2.1.6A, L3 Ver. 3.1.4, Rev. 09) - d48Document856 pagesOptiSwitch 900 Series User Manual (ML49175A, L2+ Ver. 2.1.6A, L3 Ver. 3.1.4, Rev. 09) - d48Carlos Alvarado Fernández100% (5)
- Radeus Labs BTR RL.3430-L3-v4 - WEBDocument2 pagesRadeus Labs BTR RL.3430-L3-v4 - WEBkailash khairnarNo ratings yet
- Technical Hands-on Practice set - 5 debugging codeDocument4 pagesTechnical Hands-on Practice set - 5 debugging codeBalaji BaoukNo ratings yet
- Simone's ResumeDocument4 pagesSimone's ResumeMorrisa AlexanderNo ratings yet
- BSBCMM201 Assessment A Multiple-Choice V1-0Document5 pagesBSBCMM201 Assessment A Multiple-Choice V1-0Spencer VelascoNo ratings yet
- OWN FullDocument352 pagesOWN FullMalek MohamedNo ratings yet
- RP58-Setting Integration Tool Manual (RT V1.0)Document22 pagesRP58-Setting Integration Tool Manual (RT V1.0)DP WijayaNo ratings yet
- Angular FinalDocument11 pagesAngular Finalachwek hariziNo ratings yet
- DS 2CD2720F IsDocument4 pagesDS 2CD2720F IsgohilnarendraNo ratings yet
- Quadratic Equation: Graphs of Quadratic PolynomialDocument12 pagesQuadratic Equation: Graphs of Quadratic PolynomialAnujeetMishraNo ratings yet