Professional Documents
Culture Documents
Ethical Hacking
Uploaded by
demon0 ratings0% found this document useful (0 votes)
13 views2 pagesEthical hacking roadmap
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentEthical hacking roadmap
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
13 views2 pagesEthical Hacking
Uploaded by
demonEthical hacking roadmap
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 2
Ethical Hacking & Cyber…
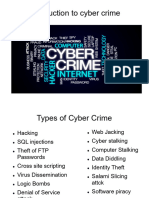
Topics under Ethical Hacking & Cyber Security
Cyber Security & Ethical Hacking
Need of cyber security
Ethical hacking
Types of hackers
Penetration Testing
Footprinting
Footprinting techniques
Cryptography
Types of Cryptography
Symmetric / Asymmetric
Digital Signatures
Hash functions
Computer Networks & Security
Computer Network Architecture; Layered Architecture
OSI Model
TCP / IP Model
Common Network Threats
Application & Web Security
Web server architecture & attacks
Web client architecture & attacks
Counter measures & patch management
Identity & Access Management (IdAM)
Authentication
Authorization
IdAM
Password protection
Identity threats
Vulnerability Analysis (VA) & System Hacking
VA Types
VA Lifecycle
VA Tools
Vulnerability scoring system
VA Report
System Hacking
Password cracking
Privilege escalation, hiding files, clearing logs
Sniffing & SQL Injection
Malware & its types
Sniffing attacks & its types
SQL injection & its types
Denial of Service (DoS) & Session Hijacking
DoS attacks & symptoms
DoS detection
System Hijacking
Session / Application level hijacking
Intrusion Detection Systems (IDS) & types
Firewalls & Types
Honeypots
Evading IDS
You might also like
- Certified Ethical Hacker v9Document9 pagesCertified Ethical Hacker v9JJ Asonyer100% (1)
- CEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021From EverandCEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021No ratings yet
- Hacking : Guide to Computer Hacking and Penetration TestingFrom EverandHacking : Guide to Computer Hacking and Penetration TestingRating: 4.5 out of 5 stars4.5/5 (3)
- Certified Information Security Expert (CISE Level 1 v2) Detailed Course ModuleDocument18 pagesCertified Information Security Expert (CISE Level 1 v2) Detailed Course ModuleAkhil SreenadhNo ratings yet
- Ethical Hacking Syllabus: Rooman Technologies PVT LTDDocument7 pagesEthical Hacking Syllabus: Rooman Technologies PVT LTDNepsonNo ratings yet
- CEHv10 Course OutlineDocument46 pagesCEHv10 Course OutlineNaitik Haiking0% (1)
- CYBER SECURITY HANDBOOK Part-2: Lock, Stock, and Cyber: A Comprehensive Security HandbookFrom EverandCYBER SECURITY HANDBOOK Part-2: Lock, Stock, and Cyber: A Comprehensive Security HandbookNo ratings yet
- The Certified Ethical Hacker Exam - version 8 (The concise study guide)From EverandThe Certified Ethical Hacker Exam - version 8 (The concise study guide)Rating: 3 out of 5 stars3/5 (9)
- Certified Ethical Hacker (CEH) Preparation Guide: Lesson-Based Review of Ethical Hacking and Penetration TestingFrom EverandCertified Ethical Hacker (CEH) Preparation Guide: Lesson-Based Review of Ethical Hacking and Penetration TestingRating: 5 out of 5 stars5/5 (4)
- CompTIA Security+ (SY0-601) LearnDocument81 pagesCompTIA Security+ (SY0-601) LearnbuntyhibuntyNo ratings yet
- Secure Web Application DevelopmentDocument3 pagesSecure Web Application DevelopmentMangesh AbnaveNo ratings yet
- CISA Exam-Intrusion Detection System (IDS) & Intrusion Prevention System (IPS)-Domain 5From EverandCISA Exam-Intrusion Detection System (IDS) & Intrusion Prevention System (IPS)-Domain 5No ratings yet
- CC Certified in Cybersecurity The Complete ISC2 Certification Study GuideFrom EverandCC Certified in Cybersecurity The Complete ISC2 Certification Study GuideNo ratings yet
- Ethical WnvHtmlToPdf - 230327 - 141029Document2 pagesEthical WnvHtmlToPdf - 230327 - 141029Rahul ChohanNo ratings yet
- Introduction To Ethical HackingDocument4 pagesIntroduction To Ethical HackingPreethi PreethiNo ratings yet
- Toc It SecurityDocument6 pagesToc It SecurityAbhinav Kumar MishraNo ratings yet
- Ethical Hacking V9: DescriptionDocument5 pagesEthical Hacking V9: DescriptionramanaNo ratings yet
- Cyber SecurityDocument2 pagesCyber SecuritySudheer RamakrishnaNo ratings yet
- Basic Topics: Introduction To Information SecurityDocument4 pagesBasic Topics: Introduction To Information SecurityTanujSoodNo ratings yet
- AISE SyllabusDocument1 pageAISE SyllabusShivam ChhabraNo ratings yet
- Ethical Hacking and Prevention Course Details in PDFDocument24 pagesEthical Hacking and Prevention Course Details in PDFK PraveenNo ratings yet
- Seminar On Ethical Hacking: Submitted To: Submitted byDocument28 pagesSeminar On Ethical Hacking: Submitted To: Submitted bySrinivas SrinivasNo ratings yet
- Ethical: Hacking andDocument4 pagesEthical: Hacking andSk InayathullaNo ratings yet
- Ethical Hacking and Prevention: Course ContentsDocument4 pagesEthical Hacking and Prevention: Course ContentsAsish PandaNo ratings yet
- Information About Ethical HackingDocument2 pagesInformation About Ethical HackingSoham SawantNo ratings yet
- Cyber Security CurriculumDocument2 pagesCyber Security CurriculumAnusha KoraboyinaNo ratings yet
- CISSP Fast Track Master: CISSP Essentials for Exam Success - Exam Cram Notes: 1st Edition - 2024From EverandCISSP Fast Track Master: CISSP Essentials for Exam Success - Exam Cram Notes: 1st Edition - 2024No ratings yet
- Cryptic NoriDocument8 pagesCryptic NoriAurelian Ionel CostinNo ratings yet
- International Journal On Cryptography and Information Security (IJCIS)Document2 pagesInternational Journal On Cryptography and Information Security (IJCIS)ijcisjournalNo ratings yet
- Cyber SecurityDocument18 pagesCyber SecurityAnshitha PANo ratings yet
- International Journal On Cryptography and Information Security (IJCIS)Document2 pagesInternational Journal On Cryptography and Information Security (IJCIS)ijcisjournalNo ratings yet
- Ethical HackerDocument26 pagesEthical HackerTanushri SuryawanshiNo ratings yet
- CAT 1 - IntroductionDocument89 pagesCAT 1 - IntroductionNikhil GaddamNo ratings yet
- International Journal On Cryptography and Information SecurityDocument2 pagesInternational Journal On Cryptography and Information SecurityijcisjournalNo ratings yet
- Ethical Hacking ModulesDocument21 pagesEthical Hacking Modulessarwarbilal523No ratings yet
- IJISADocument2 pagesIJISACS & ITNo ratings yet
- EHDFchapter 1 PPTDocument6 pagesEHDFchapter 1 PPTAhmad Raza AnsariNo ratings yet
- International Journal On Cryptography and Information Security (IJCIS)Document2 pagesInternational Journal On Cryptography and Information Security (IJCIS)ijcisjournalNo ratings yet
- CSE Ethical HackingDocument26 pagesCSE Ethical HackingParth SuraniNo ratings yet
- International Journal of Information Security and Applications (IJISA)Document2 pagesInternational Journal of Information Security and Applications (IJISA)CS & ITNo ratings yet
- Week 1 - Lecture - 1 - 2Document43 pagesWeek 1 - Lecture - 1 - 2Hasan AhmedNo ratings yet
- LG3 InfoSheet3.1 ServerSecurityDocument20 pagesLG3 InfoSheet3.1 ServerSecurityኣስፋ ሙሉNo ratings yet
- Cybersecurity SivaranjaniDocument10 pagesCybersecurity SivaranjaniAsarNo ratings yet
- Cybersecurity SivaranjaniDocument10 pagesCybersecurity SivaranjaniAsarNo ratings yet
- International Journal of Information Security and Applications (IJISA)Document2 pagesInternational Journal of Information Security and Applications (IJISA)CS & ITNo ratings yet
- Ethical Hacking: Presented By:-Shravan SanidhyaDocument29 pagesEthical Hacking: Presented By:-Shravan Sanidhyashubham anuragNo ratings yet
- International Journal of Information Security and Applications (IJISA)Document2 pagesInternational Journal of Information Security and Applications (IJISA)CS & ITNo ratings yet
- Certified Ethical HackingDocument5 pagesCertified Ethical HackingOwen MasiberahNo ratings yet
- Cyber Security.Document10 pagesCyber Security.Venkatram PailaNo ratings yet
- International Journal On Cryptography and Information Security (IJCIS)Document2 pagesInternational Journal On Cryptography and Information Security (IJCIS)ijcisjournalNo ratings yet
- Datapro Computers: Seminar On Ethical HackingDocument26 pagesDatapro Computers: Seminar On Ethical Hackingmuna cliffNo ratings yet
- Cyber Security IntroductionDocument20 pagesCyber Security IntroductionjilikajithendarNo ratings yet
- Your System's Sweetspots: CEO's Advice on Basic Cyber Security: CEO's Advice on Computer ScienceFrom EverandYour System's Sweetspots: CEO's Advice on Basic Cyber Security: CEO's Advice on Computer ScienceNo ratings yet
- Mastering Cyber Security A Comprehensive Guide: cyber security, #2From EverandMastering Cyber Security A Comprehensive Guide: cyber security, #2No ratings yet
- Cybersecurity and Ethical Hacking: Exploring the Dark Art of Ethical Hacking and Penetration TestingFrom EverandCybersecurity and Ethical Hacking: Exploring the Dark Art of Ethical Hacking and Penetration TestingNo ratings yet