0% found this document useful (0 votes)
191 views9 pagesCMD Virus Removal Guide
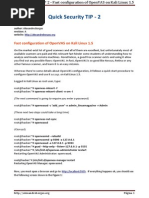
The document provides instructions for removing viruses from a computer using the Command Prompt (CMD). It describes using the ATTRIB command to display hidden and system files, which may reveal virus files. Suspicious files like "autorun.inf" should be deleted or renamed. The DEL and RENAME commands are used for this. The document also discusses recovering deleted files using shadow copies and the MKLINK command.
Uploaded by
mhiqbal20032003Copyright
© © All Rights Reserved
We take content rights seriously. If you suspect this is your content, claim it here.
Available Formats
Download as DOCX, PDF, TXT or read online on Scribd
0% found this document useful (0 votes)
191 views9 pagesCMD Virus Removal Guide
The document provides instructions for removing viruses from a computer using the Command Prompt (CMD). It describes using the ATTRIB command to display hidden and system files, which may reveal virus files. Suspicious files like "autorun.inf" should be deleted or renamed. The DEL and RENAME commands are used for this. The document also discusses recovering deleted files using shadow copies and the MKLINK command.
Uploaded by
mhiqbal20032003Copyright
© © All Rights Reserved
We take content rights seriously. If you suspect this is your content, claim it here.
Available Formats
Download as DOCX, PDF, TXT or read online on Scribd