0% found this document useful (0 votes)
668 views18 pagesFireMon Overview
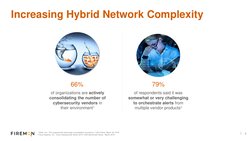
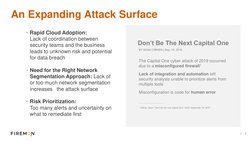
FireMon is a network security management company founded in 2003 with headquarters in the US. It has over 1,700 customers in 70 countries across various industries including federal government, enterprise, and MSPs. FireMon helps customers manage complex, hybrid network environments with multi-vendor firewalls and security tools. It provides visibility, automation, and compliance reporting to help customers address challenges around security operations, risk management, and regulatory compliance in today's rapidly changing threat landscape.
Uploaded by
Wesley WangCopyright
© © All Rights Reserved
We take content rights seriously. If you suspect this is your content, claim it here.
Available Formats
Download as PDF, TXT or read online on Scribd
0% found this document useful (0 votes)
668 views18 pagesFireMon Overview
FireMon is a network security management company founded in 2003 with headquarters in the US. It has over 1,700 customers in 70 countries across various industries including federal government, enterprise, and MSPs. FireMon helps customers manage complex, hybrid network environments with multi-vendor firewalls and security tools. It provides visibility, automation, and compliance reporting to help customers address challenges around security operations, risk management, and regulatory compliance in today's rapidly changing threat landscape.
Uploaded by
Wesley WangCopyright
© © All Rights Reserved
We take content rights seriously. If you suspect this is your content, claim it here.
Available Formats
Download as PDF, TXT or read online on Scribd