Professional Documents
Culture Documents
1510 r2012 Semviii Comp Cpe8034 DF QP
Uploaded by
Gajanan Deutkar0 ratings0% found this document useful (0 votes)
5 views2 pagesOriginal Title
1510 r2012 Semviii Comp Cpe8034 Df Qp
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
5 views2 pages1510 r2012 Semviii Comp Cpe8034 DF QP
Uploaded by
Gajanan DeutkarCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 2
Scheme R 2012
Semester VIII
Course Code CPE8034
Course
Name Digital Forensics
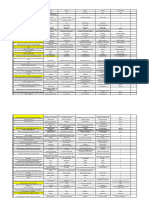
Question No. Question a b c d
Which of the following is repeated harassing and threatening behavior by one Stalking Light figure of crime Crime typology
individual against another, aspects of which may be planned or carried out in Dark figure of crime
1 secret?
Choose the term which describes Digital forensics. process of Chasing the Process of punishing the preservation filtering and
Science of collecting and
criminal culprit organization of evidence
analyzing evidence
2
Which of the following describes malicious computer programs such as viruses, Malware Larceny Arson
Software piracy
3 worms, and Trojan horses?
Which of the following is involved in forensic examination? Assessment, Seizure and preservation Recovery, harvesting, experimentation,
experimentation, fusion, filtering, organization, preservation filtering and
correlation, and and search organization
4 validation
Choose the role of Computers in a crime: Evidence, Object, evidence, and Symbol, instrumentality,
Target, object, and instrumentality, tool and source of evidence
subject contraband, or fruit of
5 crime
Which one of the following stores the boot sector and additional details about At offset 0x300 from the The last sector of the CMOS
The first sector of the
the volume? beginning of the drive volume
volume
6
7 Which one of the following is used to create an hash of file? MD5 DD DoD Wireshark
8 Which one of the following is used for encrypted data transfer? netstat cryptcat md5sum netcat
9 Which one of the following is nothing but volatile data ? Live data Hard disk data File data Folder data
What is the use of dcfldd ? Defense computer disk destroyer disk dynamics disk doodler
forensics lab disk
10 duplicator
What is used to validate the tools and verify the evidence integrity? steganography watermarks digital certificates
hashing algorithms
11
Choose the command that shows all Registry data in real time on a Windows RegMon RegExplorer RegHandle
PsReg
12 computer.
Choose the process model whose goal is to completely describe the flow of The Staircase Model The Evidence Flow Model The Subphase Model
information in a digital investigation. The Physical Model
13
Which of following is not a rule of digital forensics? A copy is made onto The copy of the evidence The examination must
An examination should forensically sterile must be an exact, bit-by- be conducted in such a
be performed on the media. New media bit copy way as to prevent any
original data should always be used if modification of the
14 available. evidence.
15 What is the most significant legal issue in computer forensics? Admissibility of Evidence Seizing Evidence Discovery of Evidence Preserving Evidence
Which challenge is faced for controlling access to a digital crime scene ? Information may be The computer may be The computer case may The computer not
stored on Internet shared. be locked. working
servers in different
16 locations.
Which of the following is NOT an artifact that will be irrevocably lost if the
Running processes
17 computer is shut down? Open network ports Data stored in memory System date and time
18 Evidence collected from network device logs are known as. Flow analysis Active Acquisition Modes of detection Packet analysis
Although it was not designed with evidence collection in mind, which software
19 can still be useful for examining network traffic. EnCase FTK Wireshark CHKDSK
Distort or falsify
Declare any confidential To respect the privacy of Uphold any relevant education, training,
20 Which of following is a NOT unethical norm for Digital Forensics Investigation? matters or knowledge others evidence credentials.
A part of overall legal system that deals with cyberspace and there respective
21 legal issues. Cyber law Industrial law Business law Commercial Law
22 Which of the following is not an example of a computer as weapon cyber-crime? Credit card fraudulent Spying someone using IPR Violation Pornography
23 Which of the following is not done by cyber criminals? Unauthorized account Mass attack using Email spoofing and Report vulnerability in
24 What is the name of the IT law that India is having in the Indian legislature India’s Technology (IT) India’s Digital India’s Information The Technology Act,
25 Which tool is used for analysis of forensic image? FTK Imager Flawfinder Nessus Openstego
You might also like
- Cyber Forensics 12-SeptDocument13 pagesCyber Forensics 12-SeptArun KrishnanNo ratings yet
- Practical 9 ToolsDocument4 pagesPractical 9 ToolsTing Zhi Peng (Ethan)No ratings yet
- Question Bank 1Document6 pagesQuestion Bank 1siri chandanaNo ratings yet
- 1-Reference Material I Cse4004 Digital-Forensics Eth 1.1 47 Cse4004Document10 pages1-Reference Material I Cse4004 Digital-Forensics Eth 1.1 47 Cse4004Nigel JohnNo ratings yet
- Cyber Threat IntelligenceDocument41 pagesCyber Threat Intelligencekt06121999No ratings yet
- Digiital Forensic Part 1Document41 pagesDigiital Forensic Part 1DSEU Campus GBPIT OkhlaNo ratings yet
- Modul 01 - Computer Forensics FundamentalsDocument52 pagesModul 01 - Computer Forensics Fundamentalspaulusosvaldo0382003No ratings yet
- Cyber Forensics and Privacy Tools: Shantilal Shah Engineering CollegeDocument20 pagesCyber Forensics and Privacy Tools: Shantilal Shah Engineering CollegeDeep ChhatbarNo ratings yet
- Malware DetectionDocument29 pagesMalware DetectionShahab KarimNo ratings yet
- Poster Coolest-Careers v0423 WEBDocument1 pagePoster Coolest-Careers v0423 WEBrida.me99No ratings yet
- Threadsanitizer - Data Race Detection in Practice: Konstantin Serebryany Timur IskhodzhanovDocument10 pagesThreadsanitizer - Data Race Detection in Practice: Konstantin Serebryany Timur Iskhodzhanovmichel_r_91No ratings yet
- Digital Forensics Lab Manual-Converted-CompressedDocument44 pagesDigital Forensics Lab Manual-Converted-Compressednaman sethiNo ratings yet
- Week 6 AY2021-2022 The Role of Advanced Technology in Forensic Investigations V2.0Document37 pagesWeek 6 AY2021-2022 The Role of Advanced Technology in Forensic Investigations V2.0Chloe NgNo ratings yet
- Memory Forensic: Acquisition and Analysis of Memory and Its Tools ComparisonDocument6 pagesMemory Forensic: Acquisition and Analysis of Memory and Its Tools ComparisonRakib AhmedNo ratings yet
- Research PaperDocument8 pagesResearch PaperAnishNo ratings yet
- 2022 Cyber Defenders PlaybookDocument22 pages2022 Cyber Defenders PlaybookPathum Fernando100% (2)
- Digital Forensics Random Access Memory Using Live Technique Based On Network AttackedDocument6 pagesDigital Forensics Random Access Memory Using Live Technique Based On Network AttackedJYOTI SAXENANo ratings yet
- Analysis of Tools For Detecting Rootkits and Hidden ProcessesDocument17 pagesAnalysis of Tools For Detecting Rootkits and Hidden ProcessesJonathan JaegerNo ratings yet
- Gavril Ut 2009Document7 pagesGavril Ut 2009Tanvi DhingraNo ratings yet
- Incident Response Play BookDocument21 pagesIncident Response Play BookUmoora MinhajiNo ratings yet
- Software Testing For R3 Corda Blockchain: Iosif Itkin, CEO and Co-Founder, ExactproDocument48 pagesSoftware Testing For R3 Corda Blockchain: Iosif Itkin, CEO and Co-Founder, ExactproAshish MathurNo ratings yet
- System MemoryDocument4 pagesSystem MemorySADRONUNo ratings yet
- Digital Forensics, Investigation, and ResponseDocument804 pagesDigital Forensics, Investigation, and ResponseMorgan HollingsNo ratings yet
- Digital Forensic ScienceDocument42 pagesDigital Forensic ScienceAisya Nadya DamarchaNo ratings yet
- 7 Best Computer Forensics Tools (Updated 2021) - Infosec ResourcesDocument6 pages7 Best Computer Forensics Tools (Updated 2021) - Infosec ResourcesgramaxoneNo ratings yet
- Jaipur Engineering College and Research CenterDocument24 pagesJaipur Engineering College and Research CenterSrishti HasijaniNo ratings yet
- CHFI Computer Hacking Forensic InvestigatorDocument17 pagesCHFI Computer Hacking Forensic InvestigatorChristian DuranNo ratings yet
- Eroraha Memory ForensicsDocument24 pagesEroraha Memory ForensicsAdriana HernandezNo ratings yet
- Sec535 PR PDFDocument23 pagesSec535 PR PDFFREDDY ALLAN PALACIOS GONZÁLEZNo ratings yet
- Cyber U-4 One Shot NotesDocument32 pagesCyber U-4 One Shot Notesv.c cNo ratings yet
- Windows Forensic Investigations Using PowerForensics ToolDocument7 pagesWindows Forensic Investigations Using PowerForensics Toollissette0191No ratings yet
- Cyber Forensics - Lab ManualDocument36 pagesCyber Forensics - Lab Manualashutosh.bhattarao100% (2)
- Memory Forensics In-Depth: Who Should AttendDocument2 pagesMemory Forensics In-Depth: Who Should AttendAmil AkhundzadaNo ratings yet
- Aquisition and Analysis of EvidencesDocument8 pagesAquisition and Analysis of Evidencesprabhakar kumarNo ratings yet
- Kaspersky Lab Whitepaper Machine LearningDocument17 pagesKaspersky Lab Whitepaper Machine LearningCristian SalazarNo ratings yet
- Analysis of Ransomware BinariesDocument19 pagesAnalysis of Ransomware BinariesAjmul IndiaNo ratings yet
- A Behavior-Based Approach For Malware DetectionDocument15 pagesA Behavior-Based Approach For Malware DetectionEsraa odatNo ratings yet
- Digital ForensicsDocument50 pagesDigital ForensicsRiftNo ratings yet
- Enterprise Data Exfiltration Detection and Prevention: Pratyusa K. ManadhataDocument28 pagesEnterprise Data Exfiltration Detection and Prevention: Pratyusa K. ManadhataEric ChanNo ratings yet
- SOC PlaybooksDocument13 pagesSOC PlaybooksMJ100% (2)
- CFPPTDocument22 pagesCFPPTManju AllagiNo ratings yet
- Chfi Computer Hacking Forensic Investigator Ec ChfiDocument4 pagesChfi Computer Hacking Forensic Investigator Ec ChfiEng SaraNo ratings yet
- New Delhi 31072015 CMA Amit Kumar 1Document52 pagesNew Delhi 31072015 CMA Amit Kumar 1DINGDINGWALANo ratings yet
- A Comparative Analysis of OS Forensics ToolsDocument11 pagesA Comparative Analysis of OS Forensics ToolsIJRASETPublicationsNo ratings yet
- Malware AnalysisDocument33 pagesMalware AnalysispjaironNo ratings yet
- Sensors: Deep Feature Extraction and Classification of Android Malware ImagesDocument29 pagesSensors: Deep Feature Extraction and Classification of Android Malware ImagesHải NguyễnNo ratings yet
- Early-Stage Malware Prediction Using Recurrent Neural NetworksDocument17 pagesEarly-Stage Malware Prediction Using Recurrent Neural Networkspuneeth sNo ratings yet
- MalwareAnalysis Report2S17Document15 pagesMalwareAnalysis Report2S17itcom068No ratings yet
- DigitalForensics IntroductionDocument19 pagesDigitalForensics IntroductionMahadev ThukaramNo ratings yet
- Digital Forensics GH in HindiDocument19 pagesDigital Forensics GH in HindirearNo ratings yet
- WWW Hackingarticles inDocument21 pagesWWW Hackingarticles inHUMANICONo ratings yet
- 805-Article Text-3656-1-10-20220310Document16 pages805-Article Text-3656-1-10-20220310abolfazlshamsNo ratings yet
- Detecting Malware Using Process Tree and Process Activity DataDocument5 pagesDetecting Malware Using Process Tree and Process Activity DataNicolae BerendeaNo ratings yet
- 1634566604muschetto Dragos Platform Threat and Visibility Pdf1634566604Document11 pages1634566604muschetto Dragos Platform Threat and Visibility Pdf1634566604Ronald N Meza CNo ratings yet
- A3-Static Malware Analysis To Identify Ransomware PropertiesDocument8 pagesA3-Static Malware Analysis To Identify Ransomware PropertiesAleja MoraNo ratings yet
- An To Cybersec and CTFS: D4Rkc0De Mehul (Sociallyencrypted)Document18 pagesAn To Cybersec and CTFS: D4Rkc0De Mehul (Sociallyencrypted)ArnavNo ratings yet
- The Curious Case of Machine Learning in Malware Detection: Sherif Saad, William Briguglio and Haytham ElmiligiDocument9 pagesThe Curious Case of Machine Learning in Malware Detection: Sherif Saad, William Briguglio and Haytham ElmiligiTuan Anh NguyenNo ratings yet
- Defining Digital Forensic Examination and Analysis Tools Using Abstraction LayersDocument12 pagesDefining Digital Forensic Examination and Analysis Tools Using Abstraction LayersAnonymous SHWg30No ratings yet
- LaRon Walker - Computer Forensic ToolsDocument9 pagesLaRon Walker - Computer Forensic ToolsLaRon WalkerNo ratings yet
- Managek15 227678Document9 pagesManagek15 227678Hrx XNo ratings yet
- 12186Document2 pages12186Harsh BhatiaNo ratings yet
- 12186Document2 pages12186Harsh BhatiaNo ratings yet
- Microproject FORMAT MADDocument15 pagesMicroproject FORMAT MADGajanan DeutkarNo ratings yet
- Syllabi of Diploma CSTDocument46 pagesSyllabi of Diploma CST2132 CO Rohit TandelNo ratings yet
- MML3 Journal To CapcomDocument103 pagesMML3 Journal To CapcomFer BarcenaNo ratings yet
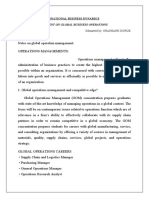
- INTERNATIONAL BUSINESS DYNAMIC (Global Operation MGT)Document7 pagesINTERNATIONAL BUSINESS DYNAMIC (Global Operation MGT)Shashank DurgeNo ratings yet
- Faculty of Business and Law Assignment Brief Mode E and R RegulationsDocument4 pagesFaculty of Business and Law Assignment Brief Mode E and R RegulationsSyeda Sana Batool RizviNo ratings yet
- E OfficeDocument3 pagesE Officeஊக்கமது கைவிடேல்No ratings yet
- 16 Easy Steps To Start PCB Circuit DesignDocument10 pages16 Easy Steps To Start PCB Circuit DesignjackNo ratings yet
- Immovable Sale-Purchase (Land) ContractDocument6 pagesImmovable Sale-Purchase (Land) ContractMeta GoNo ratings yet
- DFUN Battery Monitoring Solution Project Reference 2022 V5.0Document50 pagesDFUN Battery Monitoring Solution Project Reference 2022 V5.0A Leon RNo ratings yet
- DevelopersDocument88 pagesDevelopersdiegoesNo ratings yet
- Ambient Lighting Vol 6 CompressedDocument156 pagesAmbient Lighting Vol 6 Compressedadvait_etcNo ratings yet
- Catalogue of The Herbert Allen Collection of English PorcelainDocument298 pagesCatalogue of The Herbert Allen Collection of English PorcelainPuiu Vasile ChiojdoiuNo ratings yet
- Shares and Share CapitalDocument50 pagesShares and Share CapitalSteve Nteful100% (1)
- Modal Case Data Form: GeneralDocument4 pagesModal Case Data Form: GeneralsovannchhoemNo ratings yet
- Sewing Machins Operations ManualDocument243 pagesSewing Machins Operations ManualjemalNo ratings yet
- Theories of Economic Growth ReportDocument5 pagesTheories of Economic Growth ReportAubry BautistaNo ratings yet
- China Ve01 With Tda93xx An17821 Stv9302a La78040 Ka5q0765-SmDocument40 pagesChina Ve01 With Tda93xx An17821 Stv9302a La78040 Ka5q0765-SmAmadou Fall100% (1)
- TokyoDocument6 pagesTokyoMarcio BonziniNo ratings yet
- Fire and Life Safety Assessment ReportDocument5 pagesFire and Life Safety Assessment ReportJune CostalesNo ratings yet
- Ril Competitive AdvantageDocument7 pagesRil Competitive AdvantageMohitNo ratings yet
- Nguyen Dang Bao Tran - s3801633 - Assignment 1 Business Report - BAFI3184 Business FinanceDocument14 pagesNguyen Dang Bao Tran - s3801633 - Assignment 1 Business Report - BAFI3184 Business FinanceNgọc MaiNo ratings yet
- HW4 Fa17Document4 pagesHW4 Fa17mikeiscool133No ratings yet
- AN610 - Using 24lc21Document9 pagesAN610 - Using 24lc21aurelioewane2022No ratings yet
- Teralight ProfileDocument12 pagesTeralight ProfileMohammed TariqNo ratings yet
- It14 Belotti PDFDocument37 pagesIt14 Belotti PDFHolis AdeNo ratings yet
- Ting Vs Heirs of Lirio - Case DigestDocument2 pagesTing Vs Heirs of Lirio - Case DigestJalieca Lumbria GadongNo ratings yet
- Media SchedulingDocument4 pagesMedia SchedulingShreyansh PriyamNo ratings yet
- Double Inlet Airfoil Fans - AtzafDocument52 pagesDouble Inlet Airfoil Fans - AtzafDaniel AlonsoNo ratings yet
- S 101-01 - PDF - User Interface - Computer MonitorDocument130 pagesS 101-01 - PDF - User Interface - Computer Monitormborghesi1No ratings yet
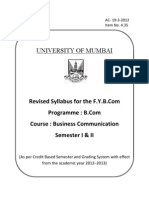
- SyllabusDocument9 pagesSyllabusrr_rroyal550No ratings yet
- Global Review Solar Tower Technology PDFDocument43 pagesGlobal Review Solar Tower Technology PDFmohit tailorNo ratings yet
- Is 778 - Copper Alloy ValvesDocument27 pagesIs 778 - Copper Alloy ValvesMuthu KumaranNo ratings yet