Professional Documents
Culture Documents
Cyber-Recovery 19.248416 48416 Setup-Guide40
Uploaded by
Marcelo MafraOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Cyber-Recovery 19.248416 48416 Setup-Guide40
Uploaded by
Marcelo MafraCopyright:
Available Formats
Dell PowerProtect Cyber Recovery Solution
Configuring and Hardening the Cyber Recovery Vault
PowerProtect DD System
November 2022
H18480.4
Configuration Guide
Abstract
This configuration guide describes how to configure PowerProtect DD
systems used with the Dell PowerProtect Cyber Recovery solution.
Dell Technologies Solutions
Copyright
The information in this publication is provided as is. Dell Inc. makes no representations or warranties of any kind with respect
to the information in this publication, and specifically disclaims implied warranties of merchantability or fitness for a particular
purpose.
Use, copying, and distribution of any software described in this publication requires an applicable software license.
Copyright © 2020 - 2022 Dell Inc. or its subsidiaries. Published in the USA 11/22 Configuration Guide H18480.4.
Dell Inc. believes the information in this document is accurate as of its publication date. The information is subject to change
without notice.
2 Dell PowerProtect Cyber Recovery Solution
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Contents
Contents
Chapter 1 Introduction 5
Overview ...............................................................................................................6
Terminology ..........................................................................................................6
We value your feedback ........................................................................................6
Chapter 2 PowerProtect DD Configuration 7
DD ports for replication and administration ............................................................8
DD system summary ...........................................................................................11
Switch port requirements.....................................................................................12
Verify the management network connection ........................................................12
Verify the data path .............................................................................................12
Chapter 3 DD Hardening 14
Review settings ...................................................................................................15
Follow best practices...........................................................................................16
Set a valid system passphrase .........................................................................17
Multifactor authentication for sysadmin and security-officer authorization .........18
Set access controls .............................................................................................18
Review access control security .........................................................................19
Configure SSH and UI access timeout ..............................................................19
Access control ..................................................................................................20
User authorization.............................................................................................20
Secure login through HTTPS ............................................................................20
NTP services ....................................................................................................21
Securing the air gap ............................................................................................23
Minimum required DD ports ..............................................................................23
Data security control .........................................................................................26
Other security settings ......................................................................................29
Perform hardening procedures ............................................................................30
Configure administrator access.........................................................................30
Follow password policy .....................................................................................30
Set up accounts ................................................................................................31
Configure authentication settings ......................................................................31
Configure mail server settings...........................................................................31
Configure IPMI settings.....................................................................................32
Dell PowerProtect Cyber Recovery Solution 3
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Contents
4 Dell PowerProtect Cyber Recovery Solution
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 1: Introduction
Chapter 1 Introduction
This chapter presents the following topics:
Overview ..............................................................................................................6
Terminology ........................................................................................................6
We value your feedback .....................................................................................6
Dell PowerProtect Cyber Recovery Solution 5
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 1: Introduction
Overview
The PowerProtect Cyber Recovery solution maintains mission-critical business data and
technology configurations in a secure, air-gapped 'vault' environment that can be used for
recovery or analysis. The Cyber Recovery Vault (CR Vault) is physically isolated from an
unsecure system or network.
The Cyber Recovery solution uses DD systems to replicate data from the production
system to the CR Vault through a dedicated replication data link.
Terminology
The following table provides definitions for some of the terms that are used in this
document.
Table 1. Terminology
Term Definition
Cyber Recovery Vault (CR Secure location, which is the target for DD MTree replication.
Vault) The CR Vault requires at least one DD and a dedicated
network.
Source DD system The production DD system that is outside of the CR Vault.
Target DD system The DD system in the CR Vault.
We value your feedback
Dell Technologies and the authors of this document welcome your feedback on the
solution and the solution documentation. Contact the Dell Technologies Solutions team by
email.
6 Dell PowerProtect Cyber Recovery Solution
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 2: PowerProtect DD Configuration
Chapter 2 PowerProtect DD Configuration
This chapter presents the following topics:
DD ports for replication and administration......................................................8
DD system summary.........................................................................................11
Switch port requirements .................................................................................12
Verify the management network connection ..................................................12
Verify the data path ...........................................................................................12
Dell PowerProtect Cyber Recovery Solution 7
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 2: PowerProtect DD Configuration
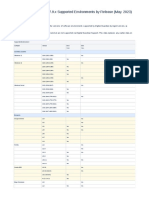
DD ports for replication and administration
The DD system in the CR Vault uses:
• 1 GB/s or 10 GB/s interfaces to connect to the management network, which
provides connectivity to the Cyber Recovery management host by using a direct
connection or through a switch
• 10/25/100 GB/s interfaces to connect to the replication network, which provides
connectivity to the source DD system
Use 10 GbE and 25 GbE network interface cards for the slots available in the DD system
models, as shown in the following tables:
Table 2. DD3300 configuration slot assignments
Description Slot
2 X 10 GBE NIC 1 (top)
4 x 16 Gbps FC module 1 (middle)
4 x 10 GbE RJ-45 6
Serial port 9
iDRAC9 dedicated management port 10
Table 3. DD6400 configuration slot assignments
Description Slot
QLogic 2692, 2 x 16G FC, PCIe, full height 1
Intel XXV710, 2 x 10/25GbE SFP28, PCIe, full 5, 7, 8
height
Intel X710, 4 x 10GbE SFP+, PCIe, full height 5, 7, 8
Intel X710, 4 x 10GBT, PCIe, full height 5, 7, 8
iDRAC9 dedicated Dell EMC Cavium/CN72xx, 2
16 GB NVRAM, PCIe, full height management
port
Broadcom LSI 9300-8e, 2 x 12 Gbps SAS, 3
PCIe, low profile (external SAS)
Intel Lewisberg, QAT, PCIe, full height 4
Broadcom LSI 9300-8e, 2 x 12 Gbps SAS, 6
PCIe, low profile (internal SAS)
8 Dell PowerProtect Cyber Recovery Solution
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 2: PowerProtect DD Configuration
Table 4. DD6900 configuration slot assignments
Description Slot
QLogic, 41164 4 port, 10 GbE SFP+ PCIe, full height 5, 8, 1
QLogic, 41164 4 port, 10 GBASE-T PCIe, full height 5, 8, 1
QLogic, 41164 4 port, 10 GBASE-T PCIe, low profile 6
QLogic, 41262 2 port, 25 Gb SFP28 PCIe, full height 5, 8, 1
QLogic, 41262 2 port, 25 Gb SFP28 PCIe, low profile 6
HBA330 SAS controller 12 Gbps MiniCard Mini/mono
QAT, INTEL, 8970, FH, Avnet p/n 1QA89701G1P5 4
PM8072, SAS12, 4P, FH, MicroSemi 2295200-R 3, 7, 5
FC16, QLE2694-DEL-BK, TRG, QP, FH 5, 8, 1
16 GB NVRAM, FH 3
Table 5. DD9400 configuration slot assignments
Description Slot
QLogic, 41164 4 Port, 10 GbE SFP+ PCIe, full height 5, 8, 1
QLogic, 41164 4 Port, 10 GBASE-T PCIe, full height 5, 8, 1
QLogic, 41164 4 Port, 10 GBASE-T PCIe, low profile 6
QLogic, 41262 2 Port, 25 Gb SFP28 PCIe, full profile 5, 8, 1
QLogic, 41262 2 Port, 25 Gb SFP28 PCIe, low profile 6
HBA330 SAS controller 12 Gbps MiniCard Mini/mono
QAT, INTEL, 8970, FH, Avnet p/n 1QA89701G1P5 4
PM8072, SAS12, 4P, FH, MicroSemi 2295200-R 3, 7, 5
FC16, QLE2694-DEL-BK, TRG, QP, FH 5, 8, 1
16 GB NVRAM, FH 2
Dell PowerProtect Cyber Recovery Solution 9
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 2: PowerProtect DD Configuration
Table 6. DD9900 configuration slot assignments
Description Slot
QLogic, 41164 4 Port, 10 GbE SFP+ PCIe, full height 6, 8, 4, 10, 3, 13, 5
QLogic, 41164 4 Port, 10 GBASE-T PCIe, full height 8, 4, 3
QLogic, 41162 2 Port, 25 Gb SFP28 PCIe, full height 6, 8, 4, 10, 3, 13, 5
Mellanox CX-5 2 x 100 GbE QSFP28 PCIe, FH 8, 3, 4, 13, 10
PERC H330+ SAS RAID Adapter, FH 1
HBA330 SAS controller 12 Gbps MiniCard Mini/mono
QAT, INTEL, 8970, FH, Avnet p/n 1QA89701G1P5 2, 7
PM8072, SAS12, 4P, FH, MicroSemi 2295200-R 9, 12, 5
FC16, QLE2694-DEL-BK, TRG, QP, FH 5, 6, 8, 4, 10, 3, 13
16 GB NVRAM, FH 11
Note: For information about cabling and the SFP module requirements, see the setup and
installation guide for the specific DD system model.
10 Dell PowerProtect Cyber Recovery Solution
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 2: PowerProtect DD Configuration
DD system summary
Complete the following table to list the target DD system summary:
Table 7. Target DD summary
Component Notes
Location
Name
Serial number
Domain name
DDOS version
Model number
Default gateway
Primary DNS Recommended for setting up an isolated DNS server in the CR Vault; not shared with other
environments
Secondary DNS Optional; not shared with other environments
NTP server Optional; if used, ensure that it is isolated and not shared with other environments
Interface name Ifgroup (Default)
ethMa ethMb ethMc ethMd
IP address
Netmask
Duplex Full
Media Fiber
Speed 10 GB/s
Interface name Ifgroup (IF10GC)
ethMe ethMf
IP address
Netmask
Duplex Full
Media Fiber
Speed 10 GB/s
Interface Ifgroup (IF10GF)
eth0a eth0b
IP address
Netmask 255.255.255.0
Duplex Full
Dell PowerProtect Cyber Recovery Solution 11
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 2: PowerProtect DD Configuration
Component Notes
Media Fiber
Speed 10 GB/s
Switch port requirements
The network switch ports must provision the following VLANs:
• DD replication VLAN between the source and target DD systems
• CR Vault trusted high-speed data VLAN
• CR Vault trusted management VLAN
Use separate routable or nonroutable subnets for each VLAN.
Verify the management network connection
Verify the management network connection:
1. Log in to the CR Vault management host.
2. From the command-line interface (CLI), do the following:
a. Verify that the management host IP address is on the same management
VLAN or network:
# ip addr | grep inet
b. Verify that there is SSH connectivity from the Cyber Recovery management
host to the target DD system:
# ssh sysadmin@<CR Vault DD management IP address>
We do not recommend a firewall on the isolated management network. All IP ports are
accessible when the connection is verified.
Verify the data path
Verify the data path network connection to the source DD connection.
From the CLI on the target DD system:
1. Confirm that the target DD system can connect to the source DD system.
Note: Optionally, you can use a firewall, a bi-directional data diode, or Unisys Stealth
software on the replication path. Only replication port 2051 must be open between the
source and target DD systems.
12 Dell PowerProtect Cyber Recovery Solution
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 2: PowerProtect DD Configuration
2. Confirm that port net filters are open for MTree replication by using elevated
privileges:
# priv set se
# se telnet <source Data Domain address> 2051
3. Confirm that the connection refused message is not displayed.
Dell PowerProtect Cyber Recovery Solution 13
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 3: DD Hardening
Chapter 3 DD Hardening
This chapter presents the following topics:
Review settings .................................................................................................15
Follow best practices ........................................................................................16
Set access controls ..........................................................................................18
Securing the air gap..........................................................................................23
Perform hardening procedures ........................................................................30
14 Dell PowerProtect Cyber Recovery Solution
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 3: DD Hardening
Follow the recommendations in this section to harden the target DD system in the CR
Vault.
For information that provides background knowledge for hardening the target DD system
in the CR Vault, see the DD OS, PowerProtect DD Virtual Edition, and PowerProtect DD
Management Center Security Configuration Guide.
Review settings
For hardening the target DD system, be familiar with the following:
• System passphrase
• Access control settings
• Log settings
• Communication security settings
• Data security settings
• Secure serviceability settings
• Dell Secure Remote Services
• Security alert system settings
• System hardening (to comply with the DISA STIG standards)
See the DD OS, PowerProtect DD Virtual Edition, and PowerProtect DD
Management Center Security Configuration Guide for both the hardening
procedures and the mitigation steps to comply with federal Defense Information
Systems Agency (DISA) Security Technical Implementation Guides (STIGs) on the
DD system.
Dell PowerProtect Cyber Recovery Solution 15
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 3: DD Hardening
Follow best practices
Follow these best practices and precautions when hardening the DD OS:
• When configuring a client list, do not use a wildcard character that enables access
for any user. Type individual IP addresses or client names.
• The DD system must use a FIPS 140-2 approved cryptographic hashing algorithm
for generating account password hashes. Systems must employ cryptographic
hashes for passwords using the SHA-2 family of algorithms or FIPS 140-2
approved successors. The use of unapproved algorithms can result in weak
password hashes that are more vulnerable to compromise.
Note: The DD OS Command Reference Guide describes how to use the adminaccess
option set password- hash {md5 | sha512} command to set FIPS 140-2-
approved cryptographic hashing. Changing the hash algorithm does not change the hash
value for existing passwords. Any existing passwords that were hashed with MD5 still have
MD5 hash values after changing the password-hash algorithm to SHA512. These
passwords must be reset to compute a new SHA512 hash value.
• Enable HTTPS and disable HTTP.
• Do not enable Telnet.
Note: You can remove Telnet. Run the adminaccess uninstall telnet from the DD
system. However, if you remove Telnet, you cannot add it back to the system.
• Use strong passwords.
• If the SSH client does not comply with the ciphers that are supported by default,
use the CLI to add the additional ciphers so that the SSH client can connect to the
system.
• Change the default SSH port.
If you change the SSH port, be aware of the following:
The Admin interface enables only port 22 and port 443. If the ports change,
there is no way to change the ports of the Admin interface and they are left
exposed. To avoid this exposure, assign the Admin interface to a temporary
interface. Then, bring that interface down so that there are no processes
listening to the old port numbers.
The default filter function for SSH is 22 and can be disabled. In SE mode, add a
new port number by using the se net filter add operation. Identify
specific addresses that can access the new port number and a specific
interface. When you add the filter function, the common operations, such as
enable, disable, add, and delete, apply.
If the SSH port changes, the net filter blocks the port unless the auto detection
option is enabled. (While this option is enabled by default, we recommend that
you disable it in a secure environment by using the net filter auto-list
delete ports all command.) The only way to enable the new port without
auto is through SE mode.
16 Dell PowerProtect Cyber Recovery Solution
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 3: DD Hardening
Set a valid The passphrase is used to encrypt the encryption keys, cloud access, secure keys,
system imported host certificate private keys, and DD Boost token keys. It enables a system to be
passphrase transported with encryption keys on the system but without the passphrase being stored
on it. The system uses the passphrase to encrypt imported host private keys and DD
Boost token keys. If the system is stolen in transit, an attacker cannot easily recover the
data, and at most, they can recover the encrypted user data and the encrypted keys.
Data at rest encryption keys require this passphrase, and therefore, the use of a stronger
passphrase is mandatory. A valid passphrase must contain:
• A minimum of nine characters
• A minimum of one lowercase character
• A minimum of one uppercase character
• A minimum of one numeral
• A minimum of one special character
• No spaces
DD OS supports a passphrase of up to 1024 characters.
Passphrase security
The passphrase is encrypted and stored in a file on the head unit of the DD or
PowerProtect system. The encryption key that is used to encrypt the passphrase is hard
coded.
Note: If the system is configured to not store the passphrase, there is no way to recover it if it is
lost.
Use the following hidden sysadmin command to choose to not store the passphrase on
disk:
system passphrase option set store-on-disk no
Then, change the passphrase after running the command.
A side-effect of not storing the passphrase is that you must unlock the file system every
time that you reboot the system. Until the file system is unlocked, all backup jobs and
replication are impacted.
Note: If multifactor authentication is enabled, the security officer must enter an RSA SecurID
token after their password.
If there is no concern that an attacker can gain physical access to the appliance in the
environment, then store the passphrase on disk.
Dell PowerProtect Cyber Recovery Solution 17
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 3: DD Hardening
Multifactor The system requires additional authorization for certain commands to promote better
authentication security and protection. Therefore, sysadmin or security-officer credentials are required to
for sysadmin run these commands.
and security-
officer When multifactor authentication (MFA) is enabled, the system prompts for the MFA
authorization passcode in addition to sysadmin or security-officer credentials for certain commands to
promote better security and protection. An MFA passcode is usually a time-based one-
time password (TOTP) that changes every 30 or 60 seconds.
Different MFA providers support different ways of generating TOTP. Common MFA
providers include RSA SecurID, Google Authenticator/ Microsoft Authenticator, and Authy.
DD supports RSA SecurID as the MFA provider.
The following CLIs are protected with MFA and require sysadmin or security-officer
authorization:
• filesys destroy
• cloud unit delsystem sanitize
• authentication mfa rsa-securid disable
• filesys encryption lock (also supported through the UI)
• system passphrase option set store-on-disk no
Set access controls
Access control settings enable the protection of resources against unauthorized access.
This section lists the security items that you must check on each target DD system.
18 Dell PowerProtect Cyber Recovery Solution
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 3: DD Hardening
Review access Use the following table to verify and record the access control security settings for the DD
control security system.
Table 8. Access control security qualification matrix
Configuration Yes No Notes
Are session timeouts configured
for SSH?
Are session timeouts configured
for HTTPS?
Have host-based access lists
been created?
Are ACLs set up for file shares?
Has the default sysadmin
account password changed?
Are users’ accounts defined for We recommend that you create separate Admin and
each user? Security Officer accounts to manage the DD system in the
CR Vault. Do not share the same accounts for production or
other environments. Do not use the sysadmin, SE, or root
account to manage any DD environment.
Document accounts in the Account Details table.
Is there a syslog server? Forward the syslog to the management host. Use VPN or
another secured mechanism such as a data diode or Unisys
Stealth to push the logs from the target DD system to the
secured external management host.
Are logs being sent to the syslog
server?
Is there strong password policy
in place?
How is the system passphrase • Who knows it?
protected?
• Is it stored securely?
• Who knows how to access it?
Is an encryption key manager in If the target DD system has several MTrees and uses
the CR Vault design? encryption, consider using RSA Data Protection Manager
(DPM) or a similar product in the CR Vault to manage
encryption keys.
Configure SSH By default, SSH, HTTP, and secure browsing (HTTPS) are enabled on the DD system.
and UI access
timeout We recommend that you:
• Disable SSH access to target DD systems for all clients except Cyber Recovery
Management host using
• We recommend that you disable HTTP by running the adminaccess disable
http command from the CLI.
• Use an imported certificate to log in to the DD UI using a jump box.
• Configure session timeout values to ensure that users are automatically logged out
of the system after the session is over.
Dell PowerProtect Cyber Recovery Solution 19
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 3: DD Hardening
# adminaccess ssh option set session-timeout <timeout-in-seconds>
We recommend a session timeout maximum of 5 minutes.
Access control Access control and user authentication to the DD system is controlled by either local
users, NIS environments, LDAP, or in an AD domain environment. Ensure that you add
only trusted domain accounts and local users to the target DD system.
User User authorization settings control rights or permissions that are granted to a user for
authorization accessing a resource that manages the target DD system. The following roles are
available for DD users:
• admin
• limited-admin
• user
• security officer
• backup-operator
• none
• tenant-admin
• tenant-user
Note: Certain user accounts are created on the target DD system to enable implementation of the
Cyber Recovery software. We recommend that you do not create additional roles. If additional
roles are necessary, ensure that you follow the principles of least privilege.
Secure login Secure login with HTTPS requires a digital certificate to validate the identity of the DD OS
through HTTPS system and to support bi-directional encryption between DD System Manager and a
browser. DD OS includes a self-signed certificate and allows you to import your own
certificate.
To enhance security, allow only adminaccess by using HTTPS to a single IP or host in the
CR Vault. Add a single host in the CR Vault, or add Jumpbox IP or host details to ensure
that only a single machine can securely log in to DD System Manager:
# adminaccess https add <host>
Add one or more hosts to the HTTP or HTTPS list. You can identify a host using a fully
qualified hostname, an IPv4 address, or an IPv6 address
20 Dell PowerProtect Cyber Recovery Solution
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 3: DD Hardening
Configure certificate login
To log in to the target DD system using a certificate, you must have authorization
privileges on the target DD system. The target system must trust the CA certificate. Use
the DD username in the common-name field in the CA certificate.
1. Ensure that you have a user account on the target DD system. You can use either
a local user or a name service user (NIS/AD). For a name service user, configure
your group-to-role mapping on the protection system.
2. Import the public key from the CA that issued the certificate:
adminaccess certificate import ca application login-auth
3. Load the certificate in PKCS12 format in your browser.
When the target system trusts the CA certificate, a Log in with certificate link is
displayed on the login screen.
4. Click Log in with certificate and choose the certificate from the list of certificates
prompted by the browser.
The system validates the user certificate against the trust store. Based on authorization
privileges that are associated with your account, a DD System Manager session is
created for you.
Note: Using certificates to log in to the DD system is optional and is not implemented as a
standard practice. This option is only valid for login to the target DD system.
Two-factor authentication
Ensure that you have a user account on the target system. You can use either a local user
or a name service user (NIS/AD). For a name service user, configure your group-to-role
mapping on the protection system.
Common Access Card (CAC)/Personal Information Verification (PIV) cards offer two
factor authentication. A plug-in extracts the user certificate from the CAC card and into the
browser. It also provides the password to access the CAC card. When the user certificate
is loaded into the browser, log in to DD System Manager by using the certificates.
Note: Using two-factor authentication to log in to the DD system is optional and is not
implemented as a standard practice. This option is only valid for login to the target DD system.
NTP services Network Time Protocol (NTP) provides an automated method of managing and
coordinating system clocks. Computer clocks can drift over time, and having clocks
synchronized between systems is crucial to transaction processing systems. The
requirement for NTP in the CR Vault is limited. It is used as a time source for the compute
resources, scheduling, password expiration, and Retention Lock.
Note: You must have sysadmin and security officer credentials to add an NTP server.
In a traditional NTP infrastructure, local NTP servers service local time requests. Local
NTP servers connect to regional public servers as a time authority to guard against the
time drift of local NTP servers. The use of an NTP Server that connects outside the CR
Dell PowerProtect Cyber Recovery Solution 21
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 3: DD Hardening
Vault opens a potential attack vector and is potentially vulnerable to denial of service
attacks.
In terms of risk, a nefarious actor might mimic public NTP servers and force the CR Vault
hardware clocks to advance and force Retention Locks to expire. There is limited risk as
the DD does not allow the system clock to advance by more the 14 days. However, if the
CR Vault maintains less than 14 days of data, a rogue actor can force the deletion of the
CR Vault data. Also, multiple incremental clock advancements over time present a risk of
negating Retention Locks set in the CR Vault.
System time hardening
System time hardening controls the time change limit (the amount of time change) and
time change frequency (the number of times that the system time can be set).
Alerts are raised for the following:
• An attempt to change the NTP server
• The time drift exceeds a configurable amount
• Time changes
Note: Retention Lock-compliant locked copies are susceptible to deletion if time is moved forward.
Configure the system-enforced interval between system time and date changes, and the
maximum allowed amount to advance the system time and date. These values can be set
before enabling DD Retention Lock Compliance and only take effect after DD Retention
Lock Compliance is enabled. A time or date change requires admin and security officer
credentials.
Run the system set date-change-frequency command to set the allowed interval
between system time and date changes:
system set set date-change-frequency [ <number of days> | reset]
Run the system set date-change-limit command to set the maximum allowed
advance for a single system time and date change operation:
system set set date-change-limit [ hh:mm | reset]
When the date change limit is set, the system generates an alert when the clock skew
exceeds half of the date change limit. If the alert is displayed, fix the system time and
clear the alert manually. If the alert is not cleared, it is updated for any further increase in
the clock skew (when the clock skew increases by at least half of the system date change
limit).
Typically, a local pool of NTP servers is used to provide high availability (HA), although
you can provision one NTP server with an HA backup. VMware with HA can be used to
host and NTP server. See VMware KB1002864 Using an ESX host as and NTP server for
details about setting up an NTP server on ESX.
22 Dell PowerProtect Cyber Recovery Solution
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 3: DD Hardening
NTP options include:
• Do not provision an NTP server in the CR Vault or configure an NTP server on the
target DD system.
• Provision local NTP servers that are not connected to the public NTP server
network; that is, the local NTP server is isolated to the CR Vault.
• Follow Dell Technologies recommended best practice and provision a local NTP
server that has an external GPS “Stratum 0” time provider. External GPS USB
solutions can be provisioned at a relatively low price. Raspberry Pi-based and
Secure Spectracom Network time server solutions are available.
• Provision local NTP servers that are connected to the public NTP server network. If
you choose this option, provision a firewall with port 123 open.
If you do not have an external GPS time provider or do not connect to the NTP public
server network, periodically monitor the time on the target DD systems and manually reset
them if needed. If you choose this option, we highly recommend appropriate controls and
governance. Regardless of the chosen option, randomly audit the time-of-day clocks
periodically.
Securing the air gap
Minimum For replication traffic between the DD systems, open replication port 2051.
required DD
ports The following table lists the minimum open inbound ports required on the target DD
system in the CR Vault:
Table 9. DD minimum required enabled ports
Inbound ports Notes
TCP ports
22 Required so that the Cyber Recovery software
can access the target DD system
111 For the rpcbind utility, which is used by the
portmapper service
2049 For NFS for DD File System (DDFS); used
when a copy is mounted to the CyberSense
host for analyze operations
2051 The only port that must be open between the
source and target DD systems for replication
3009 For SMS, which receives CLI and other
requests from the DD systems
UDP ports
123 For ntpd
2052 For the NFS mountd service
Dell PowerProtect Cyber Recovery Solution 23
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 3: DD Hardening
All other ports must be accessible for other operations within the CR Vault. For example,
to create a copy and set a lock, the copy must be mounted on the Cyber Recovery host.
Therefore, the NFS port must be accessible between the Cyber Recovery host and that
target DD system.
Disabling SSH on the replication interface
To restrict SSH inbound access for the Cyber Recovery management host, log in to the
target DD system and run the following command:
adminaccess ssh add <hostname>
where <hostname> is the Cyber Recovery management hostname.
Disable inbound and outbound ports using net filter
The net filter functionality on the target DD system can be used to allow only the
required ports. There are default rules on the system that you can modify. Disable the
default rules and enable only the required rules.
Run the following command to show the default rules on the system:
net filter show seq-id-list all
Then, for example, disable a specific seq-id or all default seq-ids.
net filter disable <seq-id> | all | default
To disable all auto system filters, run the following command:
net filter auto-list delete ports all
Use the net filter command, using role admin or limited admin, to add a set of
iptables rules on the target DD system:
net filter add [seq-id <n>]
operation {allow | block}
[protocol {tcp [ports <port>] [except-ports <port>]
[src-ports <port>] [except-src-ports <port>]|
udp [ports <port>] [except-ports <port>]
[src-ports <port>] [except-src-ports <port>]|
[<iana-protocol>] }]
[clients {<host-list> | <ipaddr-list>}]
[except-clients {<host-list> | <ipaddr-list>}]
[interfaces {<ifname-list> | <ipaddr-list>}]
[except-interfaces {<ifname-list> | <ipaddr-list>}]
[ipversion {ipv4 | ipv6}]
The following is an example of the command, which only allows the Cyber Recovery
management host to use SSH to the target DD system on management interface ethV0:
net filter add seq-id 1 operation block protocol tcp ports 22
interfaces ethV0 ipversion ipv4 except-clients <crHostIP>
24 Dell PowerProtect Cyber Recovery Solution
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 3: DD Hardening
Similarly, to disable SSH on the replication interface of the target DD system, run the
following command:
net filter add seq-id 2 operation block protocol tcp ports 22
interfaces ethV1 ipversion ipv4
The following example enables replication port 2051 between the source and target DD
system on replication interface ethV1:
net filter add seq-id 3 operation allow protocol tcp ports 2051
clients <srcDD> interfaces ethV1 ipversion ipv4
Communications control
Use the following table to verify the open and closed ports on the DD system:
Table 10. Communication security qualification matrix
Protocol and port ON OFF Notes
FTP – Port 21 Port must be OFF; use FTPS or SCP for file transfer.
SSH – Port 22 Change when hardening the SSH.
Telnet – Port 23 Telnet must be OFF.
HTTP – Port 80 HTTP must be OFF.
NTP – Port 123 Not recommended.
CIFS(NETBIOS Name Service) Port must be OFF, unless CIFS is being used for validation
– UDP Port 137 or recovery.
CIFS(NETBIOS Datagram Port must be OFF unless CIFS is being used for validation or
Service) – UDP Port 138 recovery.
CIFS (NETBIOS Session Port must be OFF unless CIFS is being used for validation or
Service) – TCP Port 139 recovery.
SNMP – Port 161 Recommendation: Disable SNMP.
HTTPS – Port 443 Recommendation: disable and use the CLI.
CIFS (Microsoft-DS) – Port 445 Port must be OFF unless CIFS is being used for validation or
recovery.
DD Boost/NFS – Port 2049 Port must be ON; Retention Lock scripts rely on NFS.
Replication – Port 2051 Port must be ON, if performing replication.
NFS – Port 2052 Port must be ON if NFS is being used: use Kerberos with
NFS.
DDMC – Port 3009 Do not install DDMC in the CR Vault. Dell Technologies
does not recommend that you install DDMC.
Dell PowerProtect Cyber Recovery Solution 25
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 3: DD Hardening
Data security Use the following table to verify and document the data security controls (described in the
control following sections) on the DD system:
Table 11. Data security qualification matrix
Configuration Yes No Notes for Dell Technologies personnel
Data at rest encryption We recommend that you enable data at rest encryption
using the Key Manager in the CR Vault.
Is Retention Lock enabled? This option is required for target DD systems in the CR
Vault. For systems outside of the CR Vault, set this option
according to business requirements.
Is SNMP V3 implemented? Only if SNMP is activated.
Is DD in-flight encryption We recommend that you enable in-flight encryption between
enabled? the production and target DD systems.
Are externally signed SSL
certificates installed?
Data at rest encryption
For a Cyber Recovery instance, protect the DD data by using encryption of data at rest.
Enable encryption while implementing the solution for enhanced security.
DD Encryption software encrypts all incoming data before it writes the data to the physical
storage media. The data is physically stored in an encrypted manner and cannot be
accessed on the existing system or in any other environment without decrypting it first.
Encryption of all data at rest helps satisfy IT governance and compliance.
DD Encryption is designed such that if an intruder circumvents other network security
controls and gains access to encrypted data, the data is unreadable and unusable without
the proper cryptographic keys.
Configure encryption
1. Add the encryption license key.
2. Enable the encryption feature:
Important: You are prompted for a passphrase. Do not lose or forget this passphrase.
DD support cannot recover the passphrase. Without the passphrase, you cannot change
encryption configuration without a USB installation, which deletes all data.
# filesys encryption enable
Enter new passphrase:
Re-enter new passphrase:
Passphrases matched.
The passphrase is set.
The encryption feature is now enabled.
The filesystem must be restarted to effect this change.
3. Restart DDFS to physically enable encryption of newly written data:
# filesys restart
26 Dell PowerProtect Cyber Recovery Solution
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 3: DD Hardening
4. Change the encryption algorithm:
# filesys encryption algorithm set {aes_128_cbc |
aes_256_cbc | aes_128_gcm | aes_256_gcm}
If the algorithm is changed from the default, another file system restart is required for
DDFS to start using the new algorithm.
Encrypt pre-existing data
Force DDFS to encrypt pre-existing data after encryption is enabled:
# filesys encryption apply-changes
Note: This step makes the next clean cycle considerably longer and more resource intensive.
Only perform this step on systems with plenty of free space, otherwise the DD system might
become full before the cleaning completes.
Enable security user authorizations
Enable security user authorizations, which are required for functionality such as locking
the file system during transit:
1. Create a user with role security:
# user add secuser role security
Enter new password:
Re-enter new password:
Passwords matched.
User "secuser" added.
2. Log in as the new user and enable security user authorizations:
secuser@ > authorization policy set security-officer enabled
Runtime authorization policy has been enabled.
Replication encryption
Enable the Replication Encryption option in the CR Vault. This option ensures that data
that is replicating to the target DD system is encrypted over the network. If data is already
encrypted on the source DD system, enabling Replication Encryption adds another layer
of encryption before it transmits the data over the network. For environments that do not
use a VPN for secure connections between sites, it can securely encapsulate its
replication payload over SSL with AES 256-bit encryption for secure transmission. This
process is also known as encrypting data in flight.
To enable replication encryption on the source DD system, run the following command:
# replication modify rctx://<context number on the Source DD>
encryption enabled
If replication is already running, disable replication on the source and target DD systems
before modifying the encryption setting.
Modify the replication contexts so that they are protected by the Cyber Recovery software
and Replication Encryption.
Dell PowerProtect Cyber Recovery Solution 27
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 3: DD Hardening
If both the DD Encryption software and the over-the-wire encryption feature are enabled
on both the source and destination DD systems, the encrypted data is encrypted a second
time by the DD Replicator before it is replicated over the network.
On the target DD system, the DD Replicator removes one layer of encryption. The data is
stored on disk in an encrypted format by using the encryption key on the target DD
system.
Secure replication over the Internet
Secure replication over the public Internet is designed to protect against a man in the
middle (MITM) attack, which allows unauthorized access to data. It is based on secure
authentication using secure sockets layer (SSL) certificate-related information about the
source and destination DDRs.
Configure authentication in one of the following modes:
• Anonymous mode—No authentication is applied to connections.
• One-way mode—Only the destination SSL certificate is certified.
• Two-way mode—Both source and destination SSL certificates are certified.
Two-way authentication is considered the most secure. We recommend two-way
authentication if the security of replicated data is a concern.
To use two-way authentication, ensure that port 3009 and replication Port 2051 are open
between the DD systems:
1. Confirm that the hostname of the remote system can be resolved or contacted:
# net ping <hostname of remote DDR>
2. Establish mutual trust with the remote system:
# adminaccess trust add host <hostname of remote DDR> type mutual
3. Restart DDFS on both the source and target DD systems to ensure that mutual
trust is fully established:
# filesys restart
Note: This step causes a short outage to services on each DD system.
4. On the source and the destination systems, run the following command to enable
two-way authentication along with encryption while adding replication context:
# replication add source mtree://[source DD host name]/data/col1/[source mtree
name] destination mtree://[destination DD host name]/data/col1/[destination mtree
name] encryption enabled authentication mode {anonymous | one-way | two-way}
28 Dell PowerProtect Cyber Recovery Solution
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 3: DD Hardening
Retention Lock
DD Retention Lock software provides immutable file locking and secure data retention
capabilities to meet both corporate governance and compliance standards, such as SEC
17a-4(f). DD Retention Lock Governance edition and DD Retention Lock Compliance
edition can co-exist on the same DD system to enable different retention periods for
different classes of archive data.
For a Cyber Recovery deployment, we recommend that you set Retention Lock
Compliance for additional security. Compliance mode is stricter and adheres to several
common regulatory standards. For example:
• Locks against files cannot be reverted.
• The DDR must be configured with a “security officer” user who must authenticate
certain commands
• There are various restrictions on other functionality to prevent locked data from
being removed or locks being reverted early.
Dual sign-on requirement
When DD Retention Lock Compliance is enabled on a DD system, additional
administrative security is provided in the form of “dual” sign-on. Dual sign-on requires
sign-on by the system administrator and sign-on by a second authorized authority (the
security officer). The dual sign-on mechanism of the DD Retention Lock Compliance
edition acts as a safeguard against any actions that can compromise the integrity of
locked files before the expiration of the retention period.
Secure system clock
DD Retention Lock Compliance implements an internal security clock to prevent malicious
tampering with the system clock. The security clock closely monitors and records the
system clock. If there is an accumulated two-week skew within a year between the
security clock and the system clock, DDFS is disabled. Only the security officer can
enable DDFS.
Consider a process to protect the security officer password through a shared secret
scheme, in which a single person does not know or have access to the password.
Other security The following table is used to verify and document miscellaneous security settings for the
settings DD system:
Table 12. Other security settings matrix
Configuration Yes No Notes
Is the DD system configured to use the
SRS gateway?
Is Single User Bootable Mode enabled?
Is the password change policy enabled?
Is password aging enabled?
Are current security updates installed on
the DD system?
Dell PowerProtect Cyber Recovery Solution 29
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 3: DD Hardening
Secure the system passphrase
As a best practice, we recommend that you install a secure safe at the CR Vault location
to store the DD system passphrase, encryption keys, and an emergency access sysadmin
password.
Alternatively, if corporate security policy allows, store passwords in a cloud-based
password manager such as Dashlane or in a local password manager such as Keypass.
Before choosing a cloud-based or local password manager, ensure that your organization
performs thorough security and risk management evaluation of the password manager.
Perform hardening procedures
Perform hardening procedures on the target DD system.
Configure To set connection access, go to Administration > Access > Administrator Access and
administrator apply the following settings:
access
• FTP—Disabled
• FTPS—Disabled
• HTTP—Disabled
• HTTPS—Disabled (We recommend using the CLI through SSH connections;
enable if you do not want to use the CLI exclusively.)
• SCP—Disabled (shares the same port with SSH)
• SSH—Enable (Allow only Cyber Recovery management host access)
• Telnet—Disable
Follow password Use AD to maintain all users other than sysadmin, ddboost, and security officer. The
policy following recommended rule settings apply to the sysadmin, ddboost, and security officer
login IDs.
Go to Administration > Access > More Tasks > Change Login Options and apply the
following settings:
• Minimum Days between Change—0
• Maximum Days between change—30 (or as appropriate)
• Warn Days before Expire—7
• Disable Days after Expire—Never (or as appropriate)
• Minimum Length of Password—16
• Minimum Number of Character Classes—3
• Lowercase character Requirement—Enable
• Uppercase character Requirement—Enable
• One Digit Requirement—Enable
30 Dell PowerProtect Cyber Recovery Solution
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 3: DD Hardening
• Special Character Requirement—Enabled (recommended)
• Max Consecutive Character Requirement—Disable
• Number of Previous Passwords to Block—12
For login options, apply the following settings:
• Maximum login attempt—5
• Unlock timeout (seconds)—300
Set up accounts Go to Administration > Access > Local Users and refer to the following table, which
lists account details:
Table 13. Account details
Username Management role Notes
sysadmin admin Update the password to be 20 characters long. Passwords must be
20 characters in length, containing a combination of numbers, letters
(upper and lower case), and symbols. You can generate a password
by going to http://passwordsgenerator.net.
Keep the password in a secure safe and ensure that it is accessible
only to designated personnel (see Secure the system passphrase).
Do not use this account for day-to-day operations so you can identify
who accesses the DD system.
ddboost None The DD Boost account is only used for authentication.
security security Required for Retention Lock compliance
Other users admin Users managing the target DD system must have their own accounts.
This account is used to add the target DD system to the CR Vault.
Configure Go to Administration > Access > Authentication and apply the following settings:
authentication
• Activity Directory/Kerberos Authentication—Disabled (default)
settings
• Workgroup Authentication—Enabled (default)
• LDAP Authentication—Disabled (default)
• Single Sign-On—Disabled (default)
• NIS Authentication—Disabled (default)
Configure mail Go to Administration > Settings and apply the following settings:
server settings
• Mail Server—Complete this setting because email notification is key for detecting
issues. Configure the local mail server in the CR Vault or use data diodes or Unisys
Stealth software to send email notifications outside the CR Vault to a secured
external management host.
• Time and Date—Provide a reliable NTP server for time synchronization.
• System Properties—Set the appropriate values.
• SNMP—Disable if not required in the Cyber Recovery environment.
Dell PowerProtect Cyber Recovery Solution 31
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
Chapter 3: DD Hardening
Configure IPMI Go to Maintenance > IPMI and apply the following settings:
settings
1. Disable IPMI if not in use.
2. If IPMI is used, connect it to an isolated network switch dedicated for OOB (out-of-
band) management traffic only.
3. Set up an IPMI user account for each user and ensure that the password is 20
characters.
4. Change the sysadmin password to 20 characters and store it in the secure safe.
32 Dell PowerProtect Cyber Recovery Solution
Configuring and Hardening the Cyber Recovery Vault PowerProtect DD System
Configuration Guide
You might also like
- Information Storage and Management: Storing, Managing, and Protecting Digital InformationFrom EverandInformation Storage and Management: Storing, Managing, and Protecting Digital InformationEMC Education ServicesNo ratings yet
- Dell Emc Powerprotect DD Virtual Edition On Microsoft Azure: Technical White PaperDocument28 pagesDell Emc Powerprotect DD Virtual Edition On Microsoft Azure: Technical White PaperRatnodeep RoyNo ratings yet
- h17670 Cyber Recovery SGDocument32 pagesh17670 Cyber Recovery SGSutajiTarNo ratings yet
- DD 7-7-1-0 Release NotesDocument30 pagesDD 7-7-1-0 Release NotesAndreaNo ratings yet
- Dell Emc Powerprotect Ddve in The Azure Cloud: Installation and Administration GuideDocument49 pagesDell Emc Powerprotect Ddve in The Azure Cloud: Installation and Administration GuideRatnodeep RoyNo ratings yet
- Microsoft Storage Ready Node r740xd - Users Guide - en UsDocument68 pagesMicrosoft Storage Ready Node r740xd - Users Guide - en UsСергей КовалевNo ratings yet
- Dell PowerProtect DD Concepts and Features - Participant GuideDocument76 pagesDell PowerProtect DD Concepts and Features - Participant GuideMWANAHAWA BAKARINo ratings yet
- Data Domain Solutions Design: Downloadable ContentDocument36 pagesData Domain Solutions Design: Downloadable ContentGreivin ArguedasNo ratings yet
- Cyber Recovery Simple Support MatrixDocument9 pagesCyber Recovery Simple Support Matrixmummy206No ratings yet
- 680-028-022 Dell Storage Manager 2016 R2 Installation GuideDocument44 pages680-028-022 Dell Storage Manager 2016 R2 Installation GuideLenin KumarNo ratings yet
- Data Domain Boost Integration GuieDocument210 pagesData Domain Boost Integration GuieerickNo ratings yet
- Dell EMC Unity: Dynamic Pools: Technical White PaperDocument40 pagesDell EMC Unity: Dynamic Pools: Technical White Papermerz asmaNo ratings yet
- h13514 Integrating Symantec Netbackup Data Domain Secure Multi TenancyDocument52 pagesh13514 Integrating Symantec Netbackup Data Domain Secure Multi TenancyBill BrittonNo ratings yet
- Dell Compellent Storage Center Oracle Best PracticesDocument30 pagesDell Compellent Storage Center Oracle Best Practicesvladimirmarkovski8119No ratings yet
- Docu 89912Document64 pagesDocu 89912Moumita PramanickNo ratings yet
- Scality Storage sd630 S - Deployment Guide - en UsDocument31 pagesScality Storage sd630 S - Deployment Guide - en UsAnthony ThomasNo ratings yet
- h14232 Oracle Database Backup Recovery Vmax3Document114 pagesh14232 Oracle Database Backup Recovery Vmax3joneberNo ratings yet
- Surveillance Dell EMC Storage With Genetec Security Center: Reference ArchitectureDocument28 pagesSurveillance Dell EMC Storage With Genetec Security Center: Reference Architecturebedjoe jrNo ratings yet
- Docu85859 - NetWorker 9.2 Data Domain Boost Integration GuideDocument204 pagesDocu85859 - NetWorker 9.2 Data Domain Boost Integration Guidemerz asmaNo ratings yet
- Dell EMC Integrated Data Protection Appliance 2.4 Getting Started GuideDocument52 pagesDell EMC Integrated Data Protection Appliance 2.4 Getting Started GuideEmre Halit POLATNo ratings yet
- S Solution Resources - White Papers108 - en UsDocument16 pagesS Solution Resources - White Papers108 - en UsSohel AhmedNo ratings yet
- Data Domain - Installation Procedure by Hardware Model-DD6300 Installation ProceduresDocument124 pagesData Domain - Installation Procedure by Hardware Model-DD6300 Installation ProceduresTakieddine ahmed DekkarNo ratings yet
- Hardware Installation and Troubleshooting GuideDocument62 pagesHardware Installation and Troubleshooting GuideAdam Van HarenNo ratings yet
- NetWorker 19.1.x Data Domain Boost Integration GuideDocument208 pagesNetWorker 19.1.x Data Domain Boost Integration GuidePedro LuisNo ratings yet
- H19048 Tanzugreenplum On Powerflex Ra Final1 PDFDocument45 pagesH19048 Tanzugreenplum On Powerflex Ra Final1 PDFJhonnyMorenoNo ratings yet
- h19639 Powerprotect DD Commvault Configuration WPDocument50 pagesh19639 Powerprotect DD Commvault Configuration WPemcviltNo ratings yet
- Storage Center Replication and Oracle Data Guard Dell 2015 (2080 BP O)Document32 pagesStorage Center Replication and Oracle Data Guard Dell 2015 (2080 BP O)Shyamji VijayNo ratings yet
- Data Protection Product GuideDocument78 pagesData Protection Product GuideSajan NairNo ratings yet
- Module 10-Data Protection - Participant GuideDocument89 pagesModule 10-Data Protection - Participant GuidesgjkyNo ratings yet
- Global Deduplication Array Administration Guide: DD OS 5.0Document70 pagesGlobal Deduplication Array Administration Guide: DD OS 5.0Rajesh KumarNo ratings yet
- Openmanage Plugin Nagios Core v30 - Users Guide - en Us PDFDocument47 pagesOpenmanage Plugin Nagios Core v30 - Users Guide - en Us PDFPera CigaNo ratings yet
- s4048 On User Guide11Document1,237 pagess4048 On User Guide11JavierNo ratings yet
- Ddve 7.6 Install Admin For AwsDocument56 pagesDdve 7.6 Install Admin For AwsTomm LeeNo ratings yet
- Data Domain® DD IntegrationDocument205 pagesData Domain® DD IntegrationRizwan KhanNo ratings yet
- All-Products Esuprt Solutions Int Esuprt Solutions Int Solutions Resources S-Solution-Resources White-Papers3 En-UsDocument125 pagesAll-Products Esuprt Solutions Int Esuprt Solutions Int Solutions Resources S-Solution-Resources White-Papers3 En-UsMarzan koesNo ratings yet
- DDBoost Admin Guide 759-0017-0002 Rev A 2.5 PDFDocument114 pagesDDBoost Admin Guide 759-0017-0002 Rev A 2.5 PDFMansoorNo ratings yet
- Powervault-Md3460 Deployment Guide En-UsDocument28 pagesPowervault-Md3460 Deployment Guide En-UsVenkatesan ManiNo ratings yet
- Dell Compellent Storage Center and Microsoft SQL Server: A Dell Best Practices GuideDocument22 pagesDell Compellent Storage Center and Microsoft SQL Server: A Dell Best Practices GuideBrad BarbeauNo ratings yet
- Data Domain and Oracle RMAN 12c Integration GuideDocument22 pagesData Domain and Oracle RMAN 12c Integration GuideFarha AzadNo ratings yet
- h16289 Dell Unity Dynamic PoolsDocument43 pagesh16289 Dell Unity Dynamic PoolsLaboratorio BlueNo ratings yet
- Dell EMC CommVaultDocument55 pagesDell EMC CommVaultlureparuNo ratings yet
- All-Products Esuprt Solutions Int Esuprt Solutions Int Solutions Resources Enterprise-Solution-Resources White-Papers10 En-UsDocument27 pagesAll-Products Esuprt Solutions Int Esuprt Solutions Int Solutions Resources Enterprise-Solution-Resources White-Papers10 En-UsrichardduarteNo ratings yet
- Dell Emc Powervault Me4024 and Vmware Horizon View With 1,300 Persistent Vdi UsersDocument21 pagesDell Emc Powervault Me4024 and Vmware Horizon View With 1,300 Persistent Vdi UsersBla bla blaNo ratings yet
- Docu79370 - ECS 3.0 Security Configuration Guide PDFDocument26 pagesDocu79370 - ECS 3.0 Security Configuration Guide PDFvenkatcms7637No ratings yet
- VNX - VNX 5400 Procedures-Adding A 2U or 3U Disk EnclosureDocument19 pagesVNX - VNX 5400 Procedures-Adding A 2U or 3U Disk EnclosureAvi KinetNo ratings yet
- BP Oracle11g Bkup Recovery RMAN EQL SnapshotsDocument42 pagesBP Oracle11g Bkup Recovery RMAN EQL Snapshotsmfs coreNo ratings yet
- rp4vm Dsa Gii Ordering and Licensing Guide 2Document22 pagesrp4vm Dsa Gii Ordering and Licensing Guide 2Delrish F.No ratings yet
- Clearpass GibimbaDocument84 pagesClearpass GibimbaRafael GomesNo ratings yet
- Design Guide - OpenShift 4.12 On Dell Intel InfrastructureDocument49 pagesDesign Guide - OpenShift 4.12 On Dell Intel InfrastructureWSNo ratings yet
- Common Dell Emc Poweredge Cyber Resilient SecurityDocument32 pagesCommon Dell Emc Poweredge Cyber Resilient Securityarchar001No ratings yet
- Pvaul 124t SpecsDocument2 pagesPvaul 124t Specsrosco825No ratings yet
- PowerProtect DD - Data Domain Field Component Replacement-DD6400Document175 pagesPowerProtect DD - Data Domain Field Component Replacement-DD6400Ra YuthNo ratings yet
- Documentum Foundation Classes 7.2 Release NotesDocument26 pagesDocumentum Foundation Classes 7.2 Release Notesandres humberto villamizar veraNo ratings yet
- DCPP 2 7 en UsDocument33 pagesDCPP 2 7 en UsmyfarlockNo ratings yet
- Config Guide Ddos ProtectionDocument100 pagesConfig Guide Ddos ProtectionNelsonbohrNo ratings yet
- Docu98680 - DD OS, PowerProtect DDMC, and PowerProtect DDVE 6.1.2.70 Release NotesDocument66 pagesDocu98680 - DD OS, PowerProtect DDMC, and PowerProtect DDVE 6.1.2.70 Release Notesjerome PerrigueyNo ratings yet
- R740 Tech GuideDocument80 pagesR740 Tech GuideRendy AjisokoNo ratings yet
- PowerVault - 5012 Deployment-Preparing For Hardware InstallationDocument132 pagesPowerVault - 5012 Deployment-Preparing For Hardware InstallationSantosh SharmaNo ratings yet
- Infrastructure Guide CDP Private CloudDocument22 pagesInfrastructure Guide CDP Private CloudDouglas LeongNo ratings yet
- CyberSense For Dell PowerProtect Cyber Recovery 1656644381Document12 pagesCyberSense For Dell PowerProtect Cyber Recovery 1656644381Marcelo MafraNo ratings yet
- SG 248451Document540 pagesSG 248451Marcelo MafraNo ratings yet
- ACG Users GuideDocument50 pagesACG Users GuideMarcelo MafraNo ratings yet
- Financial Services Industry Lens: AWS Well-Architected FrameworkDocument46 pagesFinancial Services Industry Lens: AWS Well-Architected FrameworkMarcelo MafraNo ratings yet
- External ERP Integration With SalesforceDocument1 pageExternal ERP Integration With SalesforceMarcelo Mafra100% (1)
- Service Provisioning With SalesforceDocument1 pageService Provisioning With SalesforceMarcelo MafraNo ratings yet
- AHD Series Quick Setup GuideDocument2 pagesAHD Series Quick Setup GuideNIRCIDA MARGARITA NIRCIDA MARGARITA PEREZ/DE LOS SANTOSNo ratings yet
- The Complete Guide To Adobe Illustrator ToolsDocument21 pagesThe Complete Guide To Adobe Illustrator ToolsSophia Zhang100% (1)
- PLSQL 5 2 PracticeDocument5 pagesPLSQL 5 2 PracticeANONYMOUSHELPINGOTHERSNo ratings yet
- LogDocument16 pagesLogMila AsgarNo ratings yet
- Comprog Fundamentals Oblcbl Module 2nd 2022 2023 JavaDocument65 pagesComprog Fundamentals Oblcbl Module 2nd 2022 2023 JavaEuphiemia SamonteNo ratings yet
- SkyViper StreamingGPSDrone V2450GPS InstructionsDocument4 pagesSkyViper StreamingGPSDrone V2450GPS InstructionsozbxhhgcrpgsqzoswrNo ratings yet
- Crowdstrike Support OfferingsDocument4 pagesCrowdstrike Support OfferingsRemicheNo ratings yet
- Ehealth Cloud Security Challenges A Survey PDFDocument16 pagesEhealth Cloud Security Challenges A Survey PDFfardzlyNo ratings yet
- Wespeaker A Research and Production Oriented SpeakDocument6 pagesWespeaker A Research and Production Oriented Speakomar.sayedNo ratings yet
- PESTPP Workshop Based On GV WorkshopDocument27 pagesPESTPP Workshop Based On GV WorkshopfredNo ratings yet
- DIVAR IP 6000 R2 Technical Service Note enUS 22866053259Document4 pagesDIVAR IP 6000 R2 Technical Service Note enUS 22866053259Vương NhânNo ratings yet
- Citrix Education Learning JourneyDocument15 pagesCitrix Education Learning JourneyrameshgmorayNo ratings yet
- Existing System:: Vehicle Insurance Management System Is A Web-Based Application Implemented UsingDocument2 pagesExisting System:: Vehicle Insurance Management System Is A Web-Based Application Implemented Usingranajana pawarNo ratings yet
- Pythonlearn 01 IntroDocument43 pagesPythonlearn 01 IntroPadmavathi GuddappaNo ratings yet
- Quikr SrsDocument23 pagesQuikr Srsvijaysai nuniNo ratings yet
- DG Agent For Windows 7.9.x Supported Environments by Release May 2023 (DG Customer Confidential)Document3 pagesDG Agent For Windows 7.9.x Supported Environments by Release May 2023 (DG Customer Confidential)Eddie ChuNo ratings yet
- Well Modeling and Artificial Lift Design - Doc - 2022Document4 pagesWell Modeling and Artificial Lift Design - Doc - 2022ĐẠT TRẦNNo ratings yet
- آٹھواں آسماں بھی نیلا ہےDocument154 pagesآٹھواں آسماں بھی نیلا ہےMohsin Hassas MohsinNo ratings yet
- 60-1512-01 Data SheetDocument24 pages60-1512-01 Data SheetMohamed TawfikNo ratings yet
- The Yii FrameworkDocument28 pagesThe Yii FrameworkAndrew FryNo ratings yet
- Class-9 IT-WSDocument4 pagesClass-9 IT-WSGauri MittalNo ratings yet
- BI Implementation StepsDocument2 pagesBI Implementation StepsavinashNo ratings yet
- Southern Mindanao Institute of Technology, Inc.: Summary of References Per SubjectDocument13 pagesSouthern Mindanao Institute of Technology, Inc.: Summary of References Per Subjectjaneth mombayNo ratings yet
- CS8711-Cloud Computing Lab PDFDocument95 pagesCS8711-Cloud Computing Lab PDFTJS CSE HODNo ratings yet
- COMANDOSDocument13 pagesCOMANDOSLiaNo ratings yet
- Define and Understand The Term Information SystemsDocument16 pagesDefine and Understand The Term Information SystemsTrishna TrishnaNo ratings yet
- Vmware Telco Cloud Automation 2301 Release Notes - 2Document11 pagesVmware Telco Cloud Automation 2301 Release Notes - 2abitaloveNo ratings yet
- Introduction To Cloud Computing: Mohamed Rahal ENIT 2018Document99 pagesIntroduction To Cloud Computing: Mohamed Rahal ENIT 2018Nouradin Hassan DararNo ratings yet
- QR Code RRL (International)Document4 pagesQR Code RRL (International)Jamie Faith AlingigNo ratings yet
- Rexx 1Document10 pagesRexx 1AtthulaiNo ratings yet
- The Internet Con: How to Seize the Means of ComputationFrom EverandThe Internet Con: How to Seize the Means of ComputationRating: 5 out of 5 stars5/5 (6)
- Defensive Cyber Mastery: Expert Strategies for Unbeatable Personal and Business SecurityFrom EverandDefensive Cyber Mastery: Expert Strategies for Unbeatable Personal and Business SecurityRating: 5 out of 5 stars5/5 (1)
- Laws of UX: Using Psychology to Design Better Products & ServicesFrom EverandLaws of UX: Using Psychology to Design Better Products & ServicesRating: 5 out of 5 stars5/5 (9)
- Social Media Marketing 2024, 2025: Build Your Business, Skyrocket in Passive Income, Stop Working a 9-5 Lifestyle, True Online Working from HomeFrom EverandSocial Media Marketing 2024, 2025: Build Your Business, Skyrocket in Passive Income, Stop Working a 9-5 Lifestyle, True Online Working from HomeNo ratings yet
- Evaluation of Some Websites that Offer Virtual Phone Numbers for SMS Reception and Websites to Obtain Virtual Debit/Credit Cards for Online Accounts VerificationsFrom EverandEvaluation of Some Websites that Offer Virtual Phone Numbers for SMS Reception and Websites to Obtain Virtual Debit/Credit Cards for Online Accounts VerificationsRating: 5 out of 5 stars5/5 (1)
- Grokking Algorithms: An illustrated guide for programmers and other curious peopleFrom EverandGrokking Algorithms: An illustrated guide for programmers and other curious peopleRating: 4 out of 5 stars4/5 (16)
- The Designer’s Guide to Figma: Master Prototyping, Collaboration, Handoff, and WorkflowFrom EverandThe Designer’s Guide to Figma: Master Prototyping, Collaboration, Handoff, and WorkflowNo ratings yet
- Practical Industrial Cybersecurity: ICS, Industry 4.0, and IIoTFrom EverandPractical Industrial Cybersecurity: ICS, Industry 4.0, and IIoTNo ratings yet
- The Digital Marketing Handbook: A Step-By-Step Guide to Creating Websites That SellFrom EverandThe Digital Marketing Handbook: A Step-By-Step Guide to Creating Websites That SellRating: 5 out of 5 stars5/5 (6)
- The YouTube Formula: How Anyone Can Unlock the Algorithm to Drive Views, Build an Audience, and Grow RevenueFrom EverandThe YouTube Formula: How Anyone Can Unlock the Algorithm to Drive Views, Build an Audience, and Grow RevenueRating: 5 out of 5 stars5/5 (33)
- React.js Design Patterns: Learn how to build scalable React apps with ease (English Edition)From EverandReact.js Design Patterns: Learn how to build scalable React apps with ease (English Edition)No ratings yet
- More Porn - Faster!: 50 Tips & Tools for Faster and More Efficient Porn BrowsingFrom EverandMore Porn - Faster!: 50 Tips & Tools for Faster and More Efficient Porn BrowsingRating: 3.5 out of 5 stars3.5/5 (24)
- Tor Darknet Bundle (5 in 1): Master the Art of InvisibilityFrom EverandTor Darknet Bundle (5 in 1): Master the Art of InvisibilityRating: 4.5 out of 5 stars4.5/5 (5)
- The Ultimate LinkedIn Sales Guide: How to Use Digital and Social Selling to Turn LinkedIn into a Lead, Sales and Revenue Generating MachineFrom EverandThe Ultimate LinkedIn Sales Guide: How to Use Digital and Social Selling to Turn LinkedIn into a Lead, Sales and Revenue Generating MachineNo ratings yet
- TikTok Algorithms 2024 $15,000/Month Guide To Escape Your Job And Build an Successful Social Media Marketing Business From Home Using Your Personal Account, Branding, SEO, InfluencerFrom EverandTikTok Algorithms 2024 $15,000/Month Guide To Escape Your Job And Build an Successful Social Media Marketing Business From Home Using Your Personal Account, Branding, SEO, InfluencerRating: 4 out of 5 stars4/5 (4)
- Branding: What You Need to Know About Building a Personal Brand and Growing Your Small Business Using Social Media Marketing and Offline Guerrilla TacticsFrom EverandBranding: What You Need to Know About Building a Personal Brand and Growing Your Small Business Using Social Media Marketing and Offline Guerrilla TacticsRating: 5 out of 5 stars5/5 (32)
- How to Do Nothing: Resisting the Attention EconomyFrom EverandHow to Do Nothing: Resisting the Attention EconomyRating: 4 out of 5 stars4/5 (421)
- The Wires of War: Technology and the Global Struggle for PowerFrom EverandThe Wires of War: Technology and the Global Struggle for PowerRating: 4 out of 5 stars4/5 (34)
- Ultimate Guide to YouTube for BusinessFrom EverandUltimate Guide to YouTube for BusinessRating: 5 out of 5 stars5/5 (1)