Professional Documents
Culture Documents
Amenu Rheman A10031291S219
Amenu Rheman A10031291S219
Uploaded by
Jai SharmaCopyright:
Available Formats
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5820)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1093)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (845)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (897)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (540)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (348)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (822)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (401)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Foundations of Software TestingDocument722 pagesFoundations of Software TestingJai SharmaNo ratings yet
- Saveetha School of Engineering Saveetha Institute of Medical and Technical Sciences M.E Computer Science and Engineering Programme Regulation 2016Document1 pageSaveetha School of Engineering Saveetha Institute of Medical and Technical Sciences M.E Computer Science and Engineering Programme Regulation 2016Jai SharmaNo ratings yet
- Projection of Constraint Based On Clustering: Jai Sharma. K, Chandra Mouliswara Reddy. PDocument4 pagesProjection of Constraint Based On Clustering: Jai Sharma. K, Chandra Mouliswara Reddy. PJai SharmaNo ratings yet
- Sampling Which Provides For A Known Non Zero Chance of Selection IsDocument7 pagesSampling Which Provides For A Known Non Zero Chance of Selection IsJai SharmaNo ratings yet
- Unit-1 NotesDocument73 pagesUnit-1 NotesJai SharmaNo ratings yet
- List of AWCs in Tamil Nadu PDFDocument1,833 pagesList of AWCs in Tamil Nadu PDFJai Sharma0% (1)
- SMART Product Drivers 12 and Smart Ink 5: Basic Installation and Administration GuideDocument32 pagesSMART Product Drivers 12 and Smart Ink 5: Basic Installation and Administration GuideJai SharmaNo ratings yet
- Privacy Characterization and Quantification in Data PublishingDocument1 pagePrivacy Characterization and Quantification in Data PublishingJai SharmaNo ratings yet
- Cse41-Internet of Things - SyllabusDocument2 pagesCse41-Internet of Things - SyllabusJai SharmaNo ratings yet
- B.E CSE Full Time Curriculam-2010 PDFDocument135 pagesB.E CSE Full Time Curriculam-2010 PDFJai SharmaNo ratings yet
- Unix Commands Part 2Document37 pagesUnix Commands Part 2Jai SharmaNo ratings yet
- XML Unit 2 NotesDocument24 pagesXML Unit 2 NotesJai SharmaNo ratings yet
- Unit - I Web Fundamentals 1.1 History of WebDocument50 pagesUnit - I Web Fundamentals 1.1 History of WebJai SharmaNo ratings yet
- TN Apartment Ownership Rules 1997Document3 pagesTN Apartment Ownership Rules 1997Jai Sharma100% (1)
- CS006 C Programming 3 0 2 4Document2 pagesCS006 C Programming 3 0 2 4Jai SharmaNo ratings yet
- Meghdoot ManualDocument5 pagesMeghdoot ManualJai SharmaNo ratings yet
- SHAR Permission LetterDocument2 pagesSHAR Permission LetterJai Sharma100% (2)
- STPIDocument2 pagesSTPIJai SharmaNo ratings yet
- Shell Scripting NotesDocument17 pagesShell Scripting NotesJai SharmaNo ratings yet
- TECHSOSYSDocument16 pagesTECHSOSYSJai SharmaNo ratings yet
- cs2029 Adt1 QBDocument2 pagescs2029 Adt1 QBJai SharmaNo ratings yet
- CS2029Document6 pagesCS2029Jai SharmaNo ratings yet
- GKM College of Engineering and Technology Chennai - 63 Department of Information TechnologyDocument2 pagesGKM College of Engineering and Technology Chennai - 63 Department of Information TechnologyJai SharmaNo ratings yet
- CP7101 Design and Management of Computer Networks Important and Model Question PaperDocument1 pageCP7101 Design and Management of Computer Networks Important and Model Question PaperJai SharmaNo ratings yet
Amenu Rheman A10031291S219
Amenu Rheman A10031291S219
Uploaded by
Jai SharmaOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Amenu Rheman A10031291S219
Amenu Rheman A10031291S219
Uploaded by
Jai SharmaCopyright:
Available Formats
International Journal of Engineering and Advanced Technology (IJEAT)
ISSN: 2249 – 8958, Volume-9, Issue-1S2, December 2019
Data Collateral in Cloud Enumerate using AES
under Heroku Cloud
Mohamed Ameen Ur Rehman, K. Jaisharma, D. Mahalakshmi
To make these dossiers set to safe the heroku scaffold is
Abstract: Before some years the dossier gets stored using the used which makes the use of the personal content of the
hardware devices with the sufficient amount of emporium. As of individual from the pirated person.
the technology gets improved the emporium can be done in the To make it secure the various contrivances has been
nebula without the need of the external devices. But the dossier involved but these contrivances when compared to one
which is gets stored in the nebula that gets fetched by the third-
something else there is some drawbacks which leads there is
party affiliates. So, to make the system much secured and safety
new technique has been proposed in this paper. The paper shows some back end of opening to access the dossier set. To make
the use of the herokucloud. The herokucloud act as a separate it more secured a specialized method has been takes place
nebulascaffold and the AES contrivance has been used to secure which is the AES. This contrivance is tested in various
the dossier in the nebula. This technique has been used in scaffold which is act as barrier to prevent the dossier
various web developing application. They can be used for various collecting from the pirated persons. Hackers feels difficult to
collateral maintains of dossier in the anamnesis allocation fetching the dossier from the set because of using the
groove. The main aim of the system is to make secured of the contrivance which is much protective and use of
nebuladossier. herokuscaffold which is provides a linear groove.
Each online section has the particular website in which the
Keywords: Dossier, Nebula, Heroku, Contrivance
major content has been declared in the public mode which is
much visible to the customers about the industries. The
I. INTRODUCTION
design of the web can be taking place in two parts of the
In the recent survey nearly 90% of the people using digital section one is the front end and the back end. The front end
technology. They are living in the digital world. The is the people visiting the web design and can bale to
personal dossier of each individual they get upload into the interface with the website. The back end is the coding part
social website and in the Google accounts. The dossier section they design and in which basis the web could be
which is get upload can be gets easily accessed by the third- operate. The dossier in the nebula can be takes place from
party affiliate. Nebula enumerate is the main technique any location from any part of the world without the loss of
which act as the pillar for this digital process. The nebula single set of dossiers. To full fill the customers’ satisfaction
enumerate can be done only in the presence of the internet. and free from fear of theft the personal dossier this nebula
Dossier that can be searched by the individual is stored in scaffold act as safe guard from preventing the use of the set
the nebula it acts as extended scaffold with huge anamnesis information. Set which is get upload can be gets easily
space. This technique can be demonstrate by the example in accessed by the third-party affiliate. Nebula enumerate is the
the online there are various application are available each main technique which acts as the pillar for this digital
have the unique requirements and needs when we download process. The nebula enumerate can be done only in the
and enter into the applications they can ask several personal presence of the internet. The emporium capacity of the
dossier and the acceptance of the terms and the condition if dossier can be in vast extent, fetching of dossier is not easy.
we want to use this app we need to performs this conditions. For each dossier the password is provided to make the
Dossier emporium in the nebula can be differentiating into dossier more confidential and secured. The common
private groove, public groove and the intermediate groove. division of these three grooves is safer by using the
The private groove that contains the dossier of each herokuscaffold and the AES contrivance, Here the dossier is
individual person in a separate location groove of the in encrypted form preventing fetching from the pirated
nebula. The public groove which contains the details of the person.
affiliates in the web groove that can be easily accessed by
anyone. The third groove is the intermediate groove in II. LITERATURE SURVEY
which it can be used in the corporate and in the industries.
Prashant Rewagadet., al., proposed users can be increases
day by day and the vast numbers of nebula position gets
occupied by the users. Due to the increase of the users the
dossier accumulation can be much high so the issues of
collateral maintenance are arising. To make the information
Revised Manuscript Received December 10, 2019.
Mohamed Ameen Ur Rehman, Department of Computer Science and much confidential, secured. So, the increase in the
Engineering, Saveetha School of Engineering, Saveetha Institute of technology hackers fetches the information in some sort of
Medical and Technical Sciences. theft method. To avoid this some research has been took
K. Jaisharma, Department of Computer Science and Engineering,
Saveetha School of Engineering, Saveetha Institute of Medical and place and then they finally get a solution to avoid the
Technical Sciences. fetching of dossier by the pirated person.
D. Mahalakshmi, Department of Computer Science and Engineering,
Saveetha School of Engineering, Saveetha Institute of Medical and
Technical Sciences.
Retrieval Number: A10031291S219/2019©BEIESP Published By:
DOI:10.35940/ijeat.A1003.1291S219 Blue Eyes Intelligence Engineering
1 & Sciences Publication
Data Collateral in Cloud Enumerate using AES under Heroku Cloud
The private latchkey has been generated for each particular party. The dossier can be directly sent through the
contaminated dossier set. The dossier can be secured within retainer without changing in any format and the minimum of
the latchkey. In this paper they proposed the use of the collateral in the dossier allocation groove and in the sharing
secured latchkey which is the differential man wave precinct. This dossier theft can be reduced by the providing
latchkey which is combined with the AES. This latchkey is the dossier in the encrypted and decrypted form. So the
more secured even when the technical or the hacker’s team dossier which is get transferred from the sender affiliate the
try to break the latchkey, the dossier is get surrounded by dossier is encrypted and the content of the dossier is not able
the latchkey of fire wall. So, the fetching of the dossier is to read by the human it is machine format so the hackers
difficult. When they find the latchkey there is the something who fetched the dossier from the retainer they can’t able to
else inner latchkey which can be changing every period of get the content in the file it is of useless file when the
time. So, the dossier fetching is not possible in this method. dossier gets received by the receiver node they can bale to
The dossier collateral is getting differentiate into three decrypted the file then the original content of the file gets
different categories which can be separated depends upon retrieved. By using this method, the dossier becomes much
the efficient of collateral maintained. The vast emporium secured and efficient and it is in collaborated with the AES
area can be properly maintained by applying the contrivance contrivance [4].
in the nebulascaffold for the effective and proper maintains Gaurav Rajet., al., proposed today’s world facing the
of dossier [1]. collateral issues in the digital environment. Before some
K. M. Akhil et., al., proposed the worlds technology gets years if we need to theft the dossier from the one person,
developed dossier sharing took place in the nebula via the they directly go to them and secretly stoles the dossier file.
dossier transfer medium. The dossier can be allocated in the But now as technology gets improved the dossier gathering
segments of partition in the nebula. Each and every dossier is much easy, they can fetch from the one place with
can be arranged in the proper space with the named groove. someback-end code. The code can be created in the web
The groove can be designed with the efficient amount of retainer and it particularly maintains the retainer the sharing
dossier emporium. As the technology increases at the same of the dossier between the two nodes. This collateral lack is
time there are some drawbacks is too getting increases is the gets avoided by the use of the use of the incorruption. The
hacking of the personal dossier of the individual in the incorruption can be undergoing into some several types
dossier emporium groove. The hacking can be taking place which is the 64 bit it can allocate the anamnesis size same as
because of the lack of the collateral emporium of the of that and the 128 bit of anamnesis it gets allocated same to
information. The popularity and the use of the nebula that and the 256 bit anamnesis. Based upon this size the
increases the collateral is gets decreased due to the dossier can be encrypted to the particular anamnesis sort [5].
maintenance. At the time of dossier sharing the information Vishwanath S et., al., proposed method we use the unique
can be hacked. From the web retainer by finding the IP contrivance to maintain the collateral in the online dossier
address of the particular retainer and the dossier can be transfer. Here it uses the two mainly based contrivances
easily hacked. In this paper they manly say about the which can maintain the dossier in confidential manner. The
information collateral in the set that can be act as barrier to dossier is encrypted in the sender node groove. The
the third party who can accessing the dossier in the required incorruption of the dossier can be involved in two different
and the sufficient anamnesis [2]. steps one is the proper upload of the dossier in the nebula
Nivedita Shimbreet., al., proposed most of the business and the other one is the proper download of the dossier file
people are using the nebula type of dossier sharing from on from the nebula. The proper which denotes the avoid the
to something else. They did not care about the location and missing of the setup files and the packages in the files sets.
the emporium and the long-distance communication. When The dossier which is gets encrypted to particular anamnesis
the dossier is get transferred from the retainer to retainer size before uploading into the nebula and the dossier is get
communication by knowing the retainer IP address the decrypted after downloading from the nebula. The dossier
others affiliates can easily fetches the dossier. The dossier transferring gets safe between the two medium grooves.
which is much confidential but it gets shared by the other During the incorruption and elucidation, the specific tool
affiliates. This situation is getting arises due to the lack of latchkey has been provided. After done both the process we
the collateral maintenance in the system architecture. The want to login to the latchkey it acts as the password for the
system can be monitored by the web developing affiliates at secured dossier section [6].
the time of transferring the dossier the signal is generated in Shivaraj kumar Hiremathet., al., proposed nebula sharing
the serial monitor that shows some dossier is get transfer is not only involved the dossier files transfer in also involves
from one node to the something else node. In this paper they the sharing of the money from the one account to the
proposed about the collateral maintenance of the dossier something else account. To make it much secured in this
sharing through the internet. The hash code is provided money transferring here much and more corporate are
which is act as collateral guard for the dossier sharing in involved in sharing of the money through the online
which the dossier can be secured in the both transfer and the payment. The payment can be done in the retainer.
receiver end. The both node affiliates have to log on to the To avoid the theft of the dossier and the money involves a
hash code so that the files gets opened [3]. scheme of ATP accessing of third party it makes secured
Niteen Survet., al., proposed the previous method they say from the dossier accessing by
about the collateral issues in the dossier emporium nebula. an unknown affiliate.
This paper also presents the dossier gets easily fetches by
the some of the people who needs the dossier from the
Retrieval Number: A10031291S219/2019©BEIESP Published By:
DOI:10.35940/ijeat.A1003.1291S219 Blue Eyes Intelligence Engineering
2 & Sciences Publication
International Journal of Engineering and Advanced Technology (IJEAT)
ISSN: 2249 – 8958, Volume-9, Issue-1S2, December 2019
In this paper they proposed the involve of the AES third party due to the lack of collateral management in the
contrivance and the hash code detection. They can be done system. The collateral can be increased by the use of the
along with the dossier transfer where the incorruption has technique AES contrivance. Dossier file from the nebula.
been made and the receiver groove the dossier gets The proper which denotes avoid the missing of the setup
decrypted after that the verification code has been sent to the files and the packages in the files sets. The dossier which is
required section. After that applying latchkey they can be gets encrypted to particular anamnesis size before uploading
easily logged on to the file. After that file can be easily gets into the nebula and the dossier is get decrypted after
read by the users and gets safe of fetching the dossier [7]. downloading from the nebula. The dossier transferring gets
Amit R. Gadekaret., al., proposed current situation the safe between the two medium grooves. This contrivance can
companies who having the own nebulas are Google, IBM be used to safeguard the dossier files from the unknown
etc., They are the major distributing of nebula emporium to party. They generate a latchkey when the affiliate uploads
the many clients in the world wide. The dossier can be the details in the public precinct. When the other can wants
segregated by using the dossier mining technology in which to view the details, they needed to login with the latchkey
the separation of the dossier can be done in the nebula. On which is being used by the other affiliates [8].
the time of this process the dossier can be hacked by the
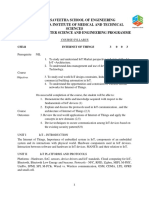
Fig. 1 Cloud data storage using AES algorithm
Shivaraj kumar Hiremathet., al., proposed simple terms contrivance to prevent the dossier theft from the something
we can clearly says that the nebula enumerate is the else retainer and the special technique is that it can clearly
emporium of the dossier set of the one user with the large shows that retainer id and their location from where the
amount of anamnesis allocation. They anamnesis can be dossier is being fetched. This collateral system can generate
provided to each affiliate as in the range of the giga bytes. a latchkey to unlock the file. The latchkey can be changed
The anamnesis bytes can be declared in technical terms. The periodically at every instances of time so that the dossier
users want to upload the dossier in the nebula set after hacking is difficult. The several nebula scaffolds offer these
uploading the dossier the contact between the dossier and features to the corporate companies. In future this system
the individual affiliate who upload the code is cleared. On has been implemented in all over the world [10].
the upcoming times the process can be took by the nebula
services. So, there is some lack of collateral in the dossier III. REVIEW IN DATA COLLATERAL IN CLOUD
management system. The collateral can be increased by the ENUMERATE USING AES UNDER HEROKU
use of the ATP which is the accessing of the third party and CLOUD
the AES and the hash code segment. In which the dossier
The main aim of this paper is the dossier collateral in the
can be provided by the customers are accessed by them and
nebula system. They clearly show that the current problems
the receiver so there is no theft in the dossier. Verification
which are facing in the nebula emporium. The main thing is
has been made in the particular time of elucidation. By using
that the dossier hacking. The dossier which is get upload in
this dossier theft is reduced and the information are in the
the nebula the person is get isolated from the information.
safe position. This system has been first implemented by the
So, there is the lack of the dossier collateral in the nebula
Amazon web service in dealing the windows technology [9].
system. To avoid these collateral issues here we clearly
Nagasai Lohithaet., al., proposed about the collateral of
show that the solution to be put forward. The use of the
the dossier in the nebula management system. In the current
heroku nebula scaffold which act as spate collateral part in
hacking world, it is difficult to safe guard once private
the nebula system and the information in the nebula can be
information. The hacking has been done from the one
retainer to something else retainer through the latchkey of
the main retainer. To protect the information in this paper
they propose AES and the effective cyber detecting
Retrieval Number: A10031291S219/2019©BEIESP Published By:
DOI:10.35940/ijeat.A1003.1291S219 Blue Eyes Intelligence Engineering
3 & Sciences Publication
Data Collateral in Cloud Enumerate using AES under Heroku Cloud
maintained safely by the use of the AES contrivance in 3. “Enhancing Distributed Dossier Emporium Collateral for Nebula
Enumerate Using TPA and AES Contrivance” by Nivedita Shimbre
which it provides a collateral layer of the dossier file. The
Dept. of Inf. Technol., MIT Coll. of Eng., Pune, India in 2015.
dossier is encrypted and then it provides a collateral 4. “Framework for client side AES incorruption technique in nebula
latchkey to the file which makes the use of the dossier file enumerate” by Niteen Surv Pimpri Chinchwad College of Engineering,
from the third party accessing over the retainer. So, the Pune, India in 2015
5. “Enhancement of collateral mechanism for confidential dossier using
efficiency of the dossier is gets increased.
AES-128, 192 and 256bit incorruption in nebula” by Gaurav Raj
Research Scholar, PTU, Jalandhar, ASET- CSE, Amity University,
IV. RESULT Noida, India in 2016
6. “Enhancing the dossier collateral in Nebula by implementing hybrid
(Rsa & Aes) incorruption contrivance” by Vishwanath S Mahalle
Department of Computer Science & Engineering Shri Sant Gajanan
Maharaj College of Engineering, Shegaon, Maharashtra, India in 2014.
7. “A novel dossier auditing approach to achieve dossier privacy and
dossier integrity in nebulaenumerate” by Shivaraj kumar Hiremath
Department of ISE, SKSVM Agadi College of Engg. & Tech,
Laxmeshwar, Indiain 2018.
8. “Nebula Collateral and Emporium Space Management using DCA
Crypt” by Amit R. Gadekar
Dept. of Computer Engg, SITRC, Nashik, India in 2018.
9. “Ensuring Nebula Dossier Collateral using Public Auditing with
Privacy Preserving” by Shivaraj kumar Hiremath Dept. of ISE,
SKSVMA College of Engineering & Tech., Lakshmeshwar, India in
2018.
10. “Secure Dossier Emporium in Nebula Using Cryptographic
Contrivances” by Nagasai Lohitha Kodumru Dept. of Computer
Science & Engineering, Amrita School of Engineering, Bengaluru,
India in 2018.
11. S.V. Manikanthan, T.Padmapriya, “A Secured Multi-Level Key
Management Technique for Intensified Wireless Sensor Network”,
International Journal of Recent Technology and Engineering, Vol. 7,
issue6s2, 2019. https://www.ijrte.org/wp-
content/uploads/papers/v7i6s2/F10720476S219.pdf
12. Fageeri S., Alhussian H., Jadid S., Abdalla I.E.E., Mohamed A.O.A.,
Hussain A. (2019). Association Rules-Based Cancer Data Analysis Of
Khartoum Centre For Radiation And Isotopes. Journal of
Computational and Theoretical Nanoscience. Vol 16. 05-Jun. Page
2289-2293
Fig. 2 comparison graph of AES algorithm
Where x axis is the size of the file and y axis is the time
taken in the seconds the above graph is comparison between
AES and modified AES while we doing the test the
modified is significantly better than unmodified AES.
Fig. 3 Home Page
REFERENCES
1. “Use of Digital Signature with Diffie Hellman Latchkey Exchange and
AES Incorruption Contrivance to Enhance Dossier Collateral in Nebula
Enumerate”, by Prashant Rewagad 2013 International Conference on
Communication Systems and Network Technologies.
2. “Enhanced nebula dossier collateral using AES contrivance” by K. M.
Akhil ,M Praveen Kumar Department of Computer Science, Amrita
University, Mysuru, India in 2018.
Retrieval Number: A10031291S219/2019©BEIESP Published By:
DOI:10.35940/ijeat.A1003.1291S219 Blue Eyes Intelligence Engineering
4 & Sciences Publication
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5820)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1093)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (845)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (897)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (540)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (348)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (822)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (401)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Foundations of Software TestingDocument722 pagesFoundations of Software TestingJai SharmaNo ratings yet
- Saveetha School of Engineering Saveetha Institute of Medical and Technical Sciences M.E Computer Science and Engineering Programme Regulation 2016Document1 pageSaveetha School of Engineering Saveetha Institute of Medical and Technical Sciences M.E Computer Science and Engineering Programme Regulation 2016Jai SharmaNo ratings yet
- Projection of Constraint Based On Clustering: Jai Sharma. K, Chandra Mouliswara Reddy. PDocument4 pagesProjection of Constraint Based On Clustering: Jai Sharma. K, Chandra Mouliswara Reddy. PJai SharmaNo ratings yet
- Sampling Which Provides For A Known Non Zero Chance of Selection IsDocument7 pagesSampling Which Provides For A Known Non Zero Chance of Selection IsJai SharmaNo ratings yet
- Unit-1 NotesDocument73 pagesUnit-1 NotesJai SharmaNo ratings yet
- List of AWCs in Tamil Nadu PDFDocument1,833 pagesList of AWCs in Tamil Nadu PDFJai Sharma0% (1)
- SMART Product Drivers 12 and Smart Ink 5: Basic Installation and Administration GuideDocument32 pagesSMART Product Drivers 12 and Smart Ink 5: Basic Installation and Administration GuideJai SharmaNo ratings yet
- Privacy Characterization and Quantification in Data PublishingDocument1 pagePrivacy Characterization and Quantification in Data PublishingJai SharmaNo ratings yet
- Cse41-Internet of Things - SyllabusDocument2 pagesCse41-Internet of Things - SyllabusJai SharmaNo ratings yet
- B.E CSE Full Time Curriculam-2010 PDFDocument135 pagesB.E CSE Full Time Curriculam-2010 PDFJai SharmaNo ratings yet
- Unix Commands Part 2Document37 pagesUnix Commands Part 2Jai SharmaNo ratings yet
- XML Unit 2 NotesDocument24 pagesXML Unit 2 NotesJai SharmaNo ratings yet
- Unit - I Web Fundamentals 1.1 History of WebDocument50 pagesUnit - I Web Fundamentals 1.1 History of WebJai SharmaNo ratings yet
- TN Apartment Ownership Rules 1997Document3 pagesTN Apartment Ownership Rules 1997Jai Sharma100% (1)
- CS006 C Programming 3 0 2 4Document2 pagesCS006 C Programming 3 0 2 4Jai SharmaNo ratings yet
- Meghdoot ManualDocument5 pagesMeghdoot ManualJai SharmaNo ratings yet
- SHAR Permission LetterDocument2 pagesSHAR Permission LetterJai Sharma100% (2)
- STPIDocument2 pagesSTPIJai SharmaNo ratings yet
- Shell Scripting NotesDocument17 pagesShell Scripting NotesJai SharmaNo ratings yet
- TECHSOSYSDocument16 pagesTECHSOSYSJai SharmaNo ratings yet
- cs2029 Adt1 QBDocument2 pagescs2029 Adt1 QBJai SharmaNo ratings yet
- CS2029Document6 pagesCS2029Jai SharmaNo ratings yet
- GKM College of Engineering and Technology Chennai - 63 Department of Information TechnologyDocument2 pagesGKM College of Engineering and Technology Chennai - 63 Department of Information TechnologyJai SharmaNo ratings yet
- CP7101 Design and Management of Computer Networks Important and Model Question PaperDocument1 pageCP7101 Design and Management of Computer Networks Important and Model Question PaperJai SharmaNo ratings yet