Professional Documents
Culture Documents
Assignment 1 Cns
Assignment 1 Cns
Uploaded by
sbasha22000 ratings0% found this document useful (0 votes)
3 views1 pageThis document outlines an assignment on cryptography and network security. It contains 6 questions covering topics such as the X.800 security services, network security models, Euler's theorem, the Hill cipher, cryptanalytic attacks, transposition techniques, Feistel encryption and decryption, block cipher design principles, cipher feedback mode, conventional vs public-key encryption, and using public-key cryptosystems for authentication and secrecy. The student is asked to explain, state, illustrate, discuss, compare, and provide sketches for their responses.
Original Description:
rvr assignment cns
Original Title
assignment_1_cns
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThis document outlines an assignment on cryptography and network security. It contains 6 questions covering topics such as the X.800 security services, network security models, Euler's theorem, the Hill cipher, cryptanalytic attacks, transposition techniques, Feistel encryption and decryption, block cipher design principles, cipher feedback mode, conventional vs public-key encryption, and using public-key cryptosystems for authentication and secrecy. The student is asked to explain, state, illustrate, discuss, compare, and provide sketches for their responses.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
3 views1 pageAssignment 1 Cns
Assignment 1 Cns
Uploaded by
sbasha2200This document outlines an assignment on cryptography and network security. It contains 6 questions covering topics such as the X.800 security services, network security models, Euler's theorem, the Hill cipher, cryptanalytic attacks, transposition techniques, Feistel encryption and decryption, block cipher design principles, cipher feedback mode, conventional vs public-key encryption, and using public-key cryptosystems for authentication and secrecy. The student is asked to explain, state, illustrate, discuss, compare, and provide sketches for their responses.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 1
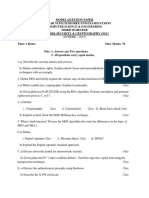
CRYPTOGRAPHY AND NETWORK SECURITY
Assignment-I
1 a) List and explain the X.800 Security Services. 3M
b) With a neat sketch explain the model for network security. 3M
2 a) State and Prove Euler’s Theorem. 3M
b) Encrypt the message “meet me at the usual place at ten rather than 3M
eight o clock” using the Hill cipher with the key 7 3
25
Show your calculations and the result.
3 a) List and explain the various types of Cryptanalytic Attacks. 3M
b) Illustrate Transposition techniques with suitable examples. 3M
4 With a neat sketch explain Fiestel Encryption and Decryption 6M
process.
5 a) Write about the block cipher design Principles. 3M
b) Discuss in detail about Cipher Feedback Mode. 3M
6 a) Compare and Contrast Convention Encryption and Public-Key 3M
Encryption.
b) With a neat sketch explain Public-key Cryptosystem to provide 3M
authentication and secrecy.
You might also like
- Mca 501 Computer Security: Each Question Carries 3 MarksDocument2 pagesMca 501 Computer Security: Each Question Carries 3 MarksToby ThomasNo ratings yet
- Information Assurance & Network Security: B.E. (Computer Engineering) Seventh Semester (CBS)Document2 pagesInformation Assurance & Network Security: B.E. (Computer Engineering) Seventh Semester (CBS)YashaswiNo ratings yet
- Is 23-24 Question PaperDocument1 pageIs 23-24 Question PaperkdchavanNo ratings yet
- Cryptography Model Question Paper Mca 5th SemDocument4 pagesCryptography Model Question Paper Mca 5th SemSanthosh B Acharya100% (1)
- NS Summer 16Document1 pageNS Summer 1624210134No ratings yet
- Unit - IDocument22 pagesUnit - IKishan KumarNo ratings yet
- University QuestionsDocument24 pagesUniversity QuestionsVasantha KumariNo ratings yet
- Assignment 2 Network SecurityDocument3 pagesAssignment 2 Network SecurityLouise ChristineNo ratings yet
- Cryptography and Network Security Dec 2023Document1 pageCryptography and Network Security Dec 2023sahithinayudu1No ratings yet
- CS8792 REJINPAUlDocument2 pagesCS8792 REJINPAUlprathipp364No ratings yet
- University QuestionsDocument24 pagesUniversity QuestionsVasantha KumariNo ratings yet
- Model Question Paper Two Year M.Tech Degree End Examinations Computer Science & Engineering Third Semester Network Security & Cryptography (NSC)Document1 pageModel Question Paper Two Year M.Tech Degree End Examinations Computer Science & Engineering Third Semester Network Security & Cryptography (NSC)api-279049687No ratings yet
- Gujarat Technological UniversityDocument2 pagesGujarat Technological Universityneeraj sharmaNo ratings yet
- CNS S2023-3161606Document2 pagesCNS S2023-3161606Archi JariwalaNo ratings yet
- 21-22 - I-Sem - Iv-Cse-Cns QBDocument12 pages21-22 - I-Sem - Iv-Cse-Cns QBSrimanth ReddyNo ratings yet
- CNS Question Bank For CIA 1Document3 pagesCNS Question Bank For CIA 1aswinsee796No ratings yet
- Gujarat Technological UniversityDocument1 pageGujarat Technological Universityyicef37689No ratings yet
- CNS Assignment - I DBATUDocument2 pagesCNS Assignment - I DBATUTere WadilNo ratings yet
- CP 7043 Cryptography Network SecurityDocument4 pagesCP 7043 Cryptography Network SecurityMegha SrivastavaNo ratings yet
- QP10 CNS QPDocument2 pagesQP10 CNS QPreshmapdscemailboxNo ratings yet
- 6.CNS Unit Wise Question BankDocument2 pages6.CNS Unit Wise Question BankRajNo ratings yet
- Css-Question BankDocument3 pagesCss-Question BankPranay NandiwadekarNo ratings yet
- Cs 8792 - Cryptography and Network SecurityDocument2 pagesCs 8792 - Cryptography and Network SecurityBHUVANESHWARNo ratings yet
- CS8792-Cryptography and Network Security QBDocument12 pagesCS8792-Cryptography and Network Security QBlavanyaraju4985No ratings yet
- CSE-ND-2020-CS 8792-Cryptography and Network Security-488165205-CS8792 CRYPTOGRAPHY AND NETWORK SECURITYDocument3 pagesCSE-ND-2020-CS 8792-Cryptography and Network Security-488165205-CS8792 CRYPTOGRAPHY AND NETWORK SECURITYBalakumar. CNo ratings yet
- Crypto Question BankDocument2 pagesCrypto Question Bankjohnabrahim1010No ratings yet
- Data Communication Networks Nec 702B PDFDocument2 pagesData Communication Networks Nec 702B PDFomenderNo ratings yet
- IET DAVV Be - Com - It-A - Apr - 2011Document19 pagesIET DAVV Be - Com - It-A - Apr - 2011jainam dudeNo ratings yet
- Internet Security October 2008Document1 pageInternet Security October 2008Neelesh SrinivasanNo ratings yet
- Embedded Systems: B. Tech VI Semester Supplementary Examinations, April - 2017Document59 pagesEmbedded Systems: B. Tech VI Semester Supplementary Examinations, April - 2017LAKKANABOINA LAKSHMANARAONo ratings yet
- MCQ - Cryptography BasicsDocument8 pagesMCQ - Cryptography Basicsvikes singh100% (1)
- Most Important Questions (5 Marks) : 11. Explain The Difference Between Streams and Block CiphersDocument2 pagesMost Important Questions (5 Marks) : 11. Explain The Difference Between Streams and Block CiphersShubham KumarNo ratings yet
- Nis Pyq 22620Document2 pagesNis Pyq 22620yashkale195No ratings yet
- Cryptpgrahy Simp TieDocument3 pagesCryptpgrahy Simp TieArshiya BegumNo ratings yet
- CNS W2023-3161606Document2 pagesCNS W2023-3161606Archi JariwalaNo ratings yet
- CCS 3402 Comp Security and Cryptography 2Document3 pagesCCS 3402 Comp Security and Cryptography 2shinsokingNo ratings yet
- Crypto QB Module 1, 2Document3 pagesCrypto QB Module 1, 2Nitish100% (2)
- Mid Sem CNS FAQDocument3 pagesMid Sem CNS FAQmayurikasoni0No ratings yet
- 07TE762Document2 pages07TE762Shiva ShankarNo ratings yet
- CRYPTOGAPHYDocument4 pagesCRYPTOGAPHYVivek ShuklaNo ratings yet
- Final 06Document2 pagesFinal 06Moudi MouhamadouNo ratings yet
- CSS Total Question BankDocument5 pagesCSS Total Question BankYOURDADNo ratings yet
- 01 TERM-1 NotesDocument14 pages01 TERM-1 Notesprajwol neupaneNo ratings yet
- Gujarat Technological UniversityDocument2 pagesGujarat Technological UniversityShweta JhaNo ratings yet
- 2023 Summer Question Paper (Msbte Study Resources)Document4 pages2023 Summer Question Paper (Msbte Study Resources)Adibhai 007 OfficialNo ratings yet
- RT 41051102018Document4 pagesRT 41051102018Mr.V. PrabhakarNo ratings yet
- CNS Question BankDocument3 pagesCNS Question BankNitya JaniNo ratings yet
- QP16 Network SecurityDocument2 pagesQP16 Network SecurityreshmapdscemailboxNo ratings yet
- Questionbank CryptoDocument4 pagesQuestionbank CryptoSantoshNo ratings yet
- ICS 3201 - Computer Security and Cryptography - January 2022Document4 pagesICS 3201 - Computer Security and Cryptography - January 2022nyamosiyegoNo ratings yet
- CNS 2017Document4 pagesCNS 2017Dr-Samson ChepuriNo ratings yet
- Be Summer 2022Document2 pagesBe Summer 2022Jenish LathiyaNo ratings yet
- (CS6701 PTCS6701)Document3 pages(CS6701 PTCS6701)Russian CarxgameNo ratings yet
- Gtu Computer 3170720 Winter 2022Document1 pageGtu Computer 3170720 Winter 2022Farhan MansuriNo ratings yet
- Cns ModelExamQuestionPaper2012Document2 pagesCns ModelExamQuestionPaper2012Rohith CsNo ratings yet
- CSS Paper 2nd YearDocument1 pageCSS Paper 2nd YearlalitmguptaamuNo ratings yet
- Gtu Computer 3170720 Summer 2022Document2 pagesGtu Computer 3170720 Summer 2022Farhan MansuriNo ratings yet
- (WWW - Entrance-Exam - Net) - DOEACC B Level-Network Management & Information Security Sample Paper 1Document2 pages(WWW - Entrance-Exam - Net) - DOEACC B Level-Network Management & Information Security Sample Paper 1DEBLEENA VIJAYNo ratings yet
- Assignment III Cryptography and Network Security (CSE324)Document1 pageAssignment III Cryptography and Network Security (CSE324)Sai HarishNo ratings yet