Professional Documents
Culture Documents
Howto Cisco External Web Authentication (EN)
Uploaded by
karthikkumarkanniyappanOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Howto Cisco External Web Authentication (EN)
Uploaded by
karthikkumarkanniyappanCopyright:
Available Formats
How to Cisco external web authentication
Bo Nielsen, CCIE #53075 (Sec)
Oktober 2016, V1.00
How to Cisco external web authentication
Overview
The principle is that the user connects to a wireless network, and the network must be open. An
open network with captive portal always starts with providing access to the network with an IP
address, and in this phase DNS implicitly allowed. The principle is to make an http-redirect at the
first http-request, and here the WLC will spoof the original destination IP address, and the browser
think that it communicates with the requested web page.
Redirect http on Cisco WLC is either to a local web page or to an external web page.
In both cases the web page must guide the user's web browser to send the login credentials to the
virtual interface (1.1.1.1). When login is delivered as https and the authentication may be made
locally from WLC itself or via a RADIUS. With RADIUS the login can be approved by Windows AD.
The process of external web authentication is illustrated here:
WLC DNS Web Auth
10.100.200.78
DNS for www.dr.dk
http://www.dr.dk
Redirect = http://10.100.200.78/guest/cisco.php
Get = http://10.100.200.78/guest/cisco.php
Login page (skin)
URL=http://10.100.200.78/guest/cisco.php? Aruba Clearpass Win-AD
Switch_url=https://1.1.1.1/login.html
Submit login
https://1.1.1.1/login.html
RADIUS LDAP
LDAPS
PAP
Success page
www.dr.dk
http://www.dr.dk
For authentication via RADIUS the Cisco WLC by default uses PAP and can be set to either PAP, CHAP
or MD5-CHAP under Security -> General.
Bo Nielsen, CCIE #53075 (Sec) Side 1
How to Cisco external web authentication
Aruba Clearpass
An overview of the service rule, enforcement policy and enforcement profile is:
Authentication source
Windows AD
NAS-Port-Type = Wireless-802.11
Service-Type = Login-User
WLC Service Authentication method
(NAD) ”CWA-WLAN-service” PAP
Enforcement policy
”CWA-WLAN-enforcement”
RADIUS:IETF
Enforcement profile
Session-Timeout =
”CWA-WLAN-profile”
3600
The enforcement profile uses the attribute Session-Timeout to set the timer for the session.
The session time is stored on the Cisco WLC after successful authentication.
In this example the session-timeout is set to 1 hour (3600s), and the user is approved for 1 hour.
When reaching 1 hour the captive portal is displayed again, and the user must re-enter their login.
In practice the session timeout can be set to a higher value than 1 hour.
On Aruba Clearpass the configuration tasks are:
1. Authentication source from Windows AD.
2. Enforcement profile
3. Enforcement policy to set the session timeout
4. Service rule with authentication source, authentication method and enforcement policy
Bo Nielsen, CCIE #53075 (Sec) Side 2
How to Cisco external web authentication
Enforcement profile
Configuration -> Enforcement -> Profiles
Enforcement policy
Configuration -> Enforcement -> Policies
Bo Nielsen, CCIE #53075 (Sec) Side 3
How to Cisco external web authentication
Service rule
Configuration -> Services
Bo Nielsen, CCIE #53075 (Sec) Side 4
How to Cisco external web authentication
External web page on Aruba Clearpass
Configuration -> Pages - Web Logins
It is very important to select The controller will send the IP to submit credentials.
Bo Nielsen, CCIE #53075 (Sec) Side 5
How to Cisco external web authentication
Cisco Wireless LAN Controller
Start by checking that the Cisco WLC uses PAP.
Controller -> General
Next verification is that the installed certificate for Web Auth has the common name set to 1.1.1.1 or
the certificate has the SAN field set to 1.1.1.1 as an IP address.
Security -> Web Auth -> Certificate
In this example I have used a certificate from an internal PKI, and it can be used for testing purpose
only because the external users have not installed the root certificate from the internal PKI. In
practice a public certificate should be used for example from Verisign, GoDaddy, DigiCert etc.
Bo Nielsen, CCIE #53075 (Sec) Side 6
How to Cisco external web authentication
Radius
Security -> RADIUS -> Authentication
In this example the Aruba Clearpass is the radius of the IP address 10,100,200.78.
Note: The name of the SSID can not be used as a condition for a service rule on Aruba Clearpass, and
this is because the Cisco WLC sends the index number of the SSID. If SSID index should be included in
a service rule, then Auth Called Station ID Type must be changed to a type where the SSID index is
included in RADIUS-request.
Security -> RADIUS -> Accounting
Access Control Lists
Security -> Access Control Lists - Access Control Lists
The ACL gives access to the website on Aruba Clearpass and DHCP. DNS is allowed by the WLC.
Bo Nielsen, CCIE #53075 (Sec) Side 7
How to Cisco external web authentication
WLAN
In this example it is a setup with the SSID name Ford, and the management interface is used for WiFi
clients and they obtain their IP address from this interface.
General
Security (open SSID), Layer 2
Security (Web Auth), Layer 3
Pre Authentication ACL restricts traffic to Aruba Clearpass until the user is authenticated.
Bo Nielsen, CCIE #53075 (Sec) Side 8
How to Cisco external web authentication
Security (Radius), AAA Servers
Advanced
It is important to select the Allow AAA Override. This causes the session-timeout from RADIUS to
become the active session timer. If overide not selected, the value for Session Timeout on the Cisco
WLC (here 600) sets the session-timeout. For an open SSID the NAC State must be set to None.
Redirect af https
By default on Cisco WLC the redirect for https is disabled. You can enable https redirect with:
config network web-auth https-redirect enable
If selected there will always be a certificate warning because the DNS name in the URL does not
match with the Cisco WLC certificate for Web Auth (default CN = 1.1.1.1).
Bo Nielsen, CCIE #53075 (Sec) Side 9
How to Cisco external web authentication
Verification
Before approval
Bo Nielsen, CCIE #53075 (Sec) Side 10
How to Cisco external web authentication
After approval
Bo Nielsen, CCIE #53075 (Sec) Side 11
You might also like
- Progress 2008Document124 pagesProgress 2008The Dispatch100% (2)
- It NotesDocument5 pagesIt Notessimran.patilNo ratings yet
- Loan Term Sheet - 20 - 12 - 42Document21 pagesLoan Term Sheet - 20 - 12 - 42Md riyaj ali KhanNo ratings yet
- Zenith GRP ReportDocument90 pagesZenith GRP ReportMarriagr - MAF KnitsNo ratings yet
- U.S. Food & Drug Administration 10903 New Hampshire Avenue: Silver Spring, MD 20993Document7 pagesU.S. Food & Drug Administration 10903 New Hampshire Avenue: Silver Spring, MD 20993api-237132031No ratings yet
- Agoda Hotels in Puncak Best Price Guarantee!Document1 pageAgoda Hotels in Puncak Best Price Guarantee!Alvina drNo ratings yet
- OpenSAP Sf7-1 Week 1 Unit 1 Trends PresentationDocument15 pagesOpenSAP Sf7-1 Week 1 Unit 1 Trends PresentationJOSEPH REYESNo ratings yet
- What's New in Artificial Lift?: World OilDocument2 pagesWhat's New in Artificial Lift?: World OilViorica SîrghiiNo ratings yet
- 2000-05 The Computer Paper - Ontario EditionDocument143 pages2000-05 The Computer Paper - Ontario Editionthecomputerpaper0% (1)
- Shrimantee Roy - ResumeDocument3 pagesShrimantee Roy - ResumeShrimantee RoyNo ratings yet
- En FS 8.1.2 Deploy BookDocument99 pagesEn FS 8.1.2 Deploy BookRodolfo TobiasNo ratings yet
- CV-Amit KumarDocument4 pagesCV-Amit KumarAmit KumarNo ratings yet
- 1 PDFsam 270120 BM PDFDocument243 pages1 PDFsam 270120 BM PDFSomenath PaulNo ratings yet
- Linksys PAP2 Configuration For Sipgate (UK)Document3 pagesLinksys PAP2 Configuration For Sipgate (UK)emsquared100% (3)
- Constructed Wetlands: Technology For Removing Drug Concentration From WaterDocument12 pagesConstructed Wetlands: Technology For Removing Drug Concentration From WaterIJAERS JOURNALNo ratings yet
- Sharad Finial 6Document67 pagesSharad Finial 6diptanshu gaikwadNo ratings yet
- Intern ReportDocument51 pagesIntern ReportHarsh PandeyNo ratings yet
- Clash of The TitansDocument6 pagesClash of The TitansSteven SchafersmanNo ratings yet
- Ip Telephony & NGN: IrisetDocument74 pagesIp Telephony & NGN: IrisetPankaj kumarNo ratings yet
- Peter Giese, J. Behrmann (Auth.), P. Giese, J. Behrmann (Eds.) - Active Continental Margins - Present and Past-Springer-Verlag Berlin Heidelberg (1994)Document249 pagesPeter Giese, J. Behrmann (Auth.), P. Giese, J. Behrmann (Eds.) - Active Continental Margins - Present and Past-Springer-Verlag Berlin Heidelberg (1994)KHIRI KHALFNo ratings yet
- Equi Valencia S Comando S Cisco Hua We IDocument77 pagesEqui Valencia S Comando S Cisco Hua We IMILTONBARRERANo ratings yet
- STD X - Chapter - 6 Natural Vegetation NotesDocument8 pagesSTD X - Chapter - 6 Natural Vegetation NotesRuchira Sanket KaleNo ratings yet
- AxtriaDocument3 pagesAxtriaTarang Gupta0% (1)
- ошибкаDocument8 pagesошибкаMukhtar ZakirovNo ratings yet
- Details Main ConentsDocument23 pagesDetails Main Conentsnemo lioNo ratings yet
- Technical Manual Goodman GMVC8Document24 pagesTechnical Manual Goodman GMVC8ed wNo ratings yet
- Oct 2019 Sebring Meals On Wheels NewsletterDocument6 pagesOct 2019 Sebring Meals On Wheels NewsletterPamela McCabeNo ratings yet
- Steps To Setup Instance Synchronization Between Two Successfactors Instances - SAP BlogsDocument6 pagesSteps To Setup Instance Synchronization Between Two Successfactors Instances - SAP BlogsgauravNo ratings yet
- PorterDocument2 pagesPorterJasonHrvyNo ratings yet
- CVvephancong GVHDCTTTapdung HK212Document6 pagesCVvephancong GVHDCTTTapdung HK212TRÍ ĐỖ MINHNo ratings yet
- A BERT Encoding With Recurrent Neural Network and Long-Short Term Memory For Breast Cancer Image Classification - 1-s2.0-S2772662223000176-MainDocument15 pagesA BERT Encoding With Recurrent Neural Network and Long-Short Term Memory For Breast Cancer Image Classification - 1-s2.0-S2772662223000176-MainSrinitish SrinivasanNo ratings yet
- EndorsementLetter PDFDocument2 pagesEndorsementLetter PDFZubairAhmedNo ratings yet
- Free Gprs Settings For Idea..Document28 pagesFree Gprs Settings For Idea..aghakhan1988No ratings yet
- Thanks For Your Order!: Billing Information Payment Details Receipt DetailsDocument1 pageThanks For Your Order!: Billing Information Payment Details Receipt DetailslbhsinhaNo ratings yet
- Oxiinc PDFDocument2 pagesOxiinc PDFChandan kumar singhNo ratings yet
- Itinerary SatishDocument3 pagesItinerary SatishGreetsNo ratings yet
- Exhibit HQI0023a - P Witness Statement of MR Luke Ashford - 0Document8 pagesExhibit HQI0023a - P Witness Statement of MR Luke Ashford - 0Michael SmithNo ratings yet
- UNAVCO July08 Yellowstone Wasatch AlaskaDocument23 pagesUNAVCO July08 Yellowstone Wasatch AlaskaLina Xiomara SierraNo ratings yet
- The Upstate Shopper Is Now Available at All Bi-Lo StoresDocument16 pagesThe Upstate Shopper Is Now Available at All Bi-Lo StoresCoolerAds100% (2)
- New York City Will Create New Agency To Cope With Migrant SurgeDocument1 pageNew York City Will Create New Agency To Cope With Migrant Surgeedwinbramosmac.comNo ratings yet
- Line Interactive UPS System - Battery Backup - KstarDocument5 pagesLine Interactive UPS System - Battery Backup - KstarViduranga BandaraNo ratings yet
- Airteltigo Sms Bundle Code - Google SearchDocument1 pageAirteltigo Sms Bundle Code - Google SearchAbigail BrownNo ratings yet
- Netezza OBIEEDocument10 pagesNetezza OBIEErahulmod5828No ratings yet
- Newlightmyanmar 04 01 2024Document15 pagesNewlightmyanmar 04 01 2024NickyNo ratings yet
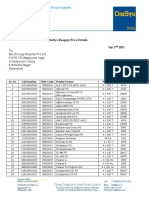
- Diasys Price Details For Bhrungi Hospital HyderabadDocument4 pagesDiasys Price Details For Bhrungi Hospital HyderabadSandeep BellapuNo ratings yet
- Brookfield More Solutions To Sticky ProblemsDocument39 pagesBrookfield More Solutions To Sticky ProblemsbobgallowayNo ratings yet
- 800 Gigacenter Ordering Guide: April 2017Document28 pages800 Gigacenter Ordering Guide: April 2017Antwan JosephNo ratings yet
- AA-7000 Series: Shimadzu Atomic Absorption SpectrophotometersDocument28 pagesAA-7000 Series: Shimadzu Atomic Absorption Spectrophotometersosklav100% (1)
- ACP 1703 Ax 1703 CM-0821: Fieldbus Interface Ring (3x FO, 1x El.)Document16 pagesACP 1703 Ax 1703 CM-0821: Fieldbus Interface Ring (3x FO, 1x El.)savijolaNo ratings yet
- Catalogue Maclev Access FloorDocument32 pagesCatalogue Maclev Access FloorJayz JDKNo ratings yet
- Solaris Root Password RecoveryDocument3 pagesSolaris Root Password RecoveryMirza Jubayar TopuNo ratings yet
- Akkaya Katalog EN 2019Document66 pagesAkkaya Katalog EN 2019Juan MendozaNo ratings yet
- PO 4600062173 SDBiosensorHealthcarePvtLtdDocument7 pagesPO 4600062173 SDBiosensorHealthcarePvtLtdChinna ThambiNo ratings yet
- Cold AisleDocument20 pagesCold Aisleyogesh chandrayanNo ratings yet
- SLC 5/01™ and SLC 5/02™ Modular Processors: Installation InstructionsDocument56 pagesSLC 5/01™ and SLC 5/02™ Modular Processors: Installation InstructionsRoman ArangoNo ratings yet
- SOP To Be Adopted by FPOsDocument12 pagesSOP To Be Adopted by FPOssampathsamudralaNo ratings yet
- Real Number NCERT Exemplar Hand Written SolutionsDocument7 pagesReal Number NCERT Exemplar Hand Written SolutionsSaksham Khushwaha 4G GNNo ratings yet
- Recen RC A11 Pro Catalog - OptDocument7 pagesRecen RC A11 Pro Catalog - OptINFO TOP SKYNo ratings yet
- PeopleLink InstaVC Data SheetDocument3 pagesPeopleLink InstaVC Data SheetTelepresence Options100% (1)
- Central Web Authentication On The WLC and ISE Configuration Example - CiscoDocument17 pagesCentral Web Authentication On The WLC and ISE Configuration Example - CiscoCiscostuffNo ratings yet
- FortiOS 7.0.0 New Features GuideDocument694 pagesFortiOS 7.0.0 New Features GuideHansNo ratings yet
- Carrier Grade Captive Portal at Hotspot - Koeln: Ivan AndricDocument26 pagesCarrier Grade Captive Portal at Hotspot - Koeln: Ivan AndricDavid GasparyanNo ratings yet
- Aruba Instant On: Deployment GuideDocument30 pagesAruba Instant On: Deployment GuideMochamad FarizNo ratings yet
- Access Control - Cisco MerakiDocument12 pagesAccess Control - Cisco MerakiJean Jacques BelyNo ratings yet
- Ruijie Reyee-Hotel Solution Cookbook (V1.0)Document77 pagesRuijie Reyee-Hotel Solution Cookbook (V1.0)juragan.it100% (1)
- Configuring A Guest Splash Page ProfileDocument8 pagesConfiguring A Guest Splash Page Profiledev KumarNo ratings yet
- Controller ArubaDocument54 pagesController ArubaRudinHariantoNo ratings yet
- ISE Wired PoC Prescriptive Guide v.5Document133 pagesISE Wired PoC Prescriptive Guide v.5shadab umairNo ratings yet
- Palo Alto Networks - Premium.pcnse - by.VCEplus.163qDocument96 pagesPalo Alto Networks - Premium.pcnse - by.VCEplus.163qWess WessNo ratings yet
- Advanced Troubleshooting R6 - I - Alcatel-Lucent EnterpriseDocument416 pagesAdvanced Troubleshooting R6 - I - Alcatel-Lucent EnterprisejghiNo ratings yet
- Setting Up A Temporary Guest WiFi UserDocument7 pagesSetting Up A Temporary Guest WiFi UserVitor TapadasNo ratings yet
- Barracuda Web Filter 310Document200 pagesBarracuda Web Filter 310Neil AlphonsoNo ratings yet
- WP 80211 AttacksDocument46 pagesWP 80211 AttacksTalhaAftabNo ratings yet
- Nse6 FWF-6.4Document18 pagesNse6 FWF-6.4crgonzalezfloresNo ratings yet
- Krumm20Heller20 20del20inicienso20a20la20osmoterapiaDocument3,157 pagesKrumm20Heller20 20del20inicienso20a20la20osmoterapiaEddyWillamisNo ratings yet
- Wi-Fi Jamming Using Raspberry Pi: ISSN: 1314-3395 (On-Line Version) Url: Http://acadpubl - Eu/hub Special IssueDocument8 pagesWi-Fi Jamming Using Raspberry Pi: ISSN: 1314-3395 (On-Line Version) Url: Http://acadpubl - Eu/hub Special IssueSarangNo ratings yet
- New Captive PDFDocument24 pagesNew Captive PDFCharbel AvognonNo ratings yet
- Setup GatewayDocument34 pagesSetup GatewaytaticuioNo ratings yet
- Captive Portal Facebook AuthenticationDocument18 pagesCaptive Portal Facebook AuthenticationSantiago RemacheNo ratings yet
- UXI Use Cases - Vertical WiseDocument10 pagesUXI Use Cases - Vertical Wiseapc666No ratings yet
- ExtremeControl With WiNG 5.8Document42 pagesExtremeControl With WiNG 5.8manelnaboNo ratings yet
- 1 Peplink Balance DatasheetDocument4 pages1 Peplink Balance DatasheetMarcelMinotelliNo ratings yet
- 203 Lab GuideDocument17 pages203 Lab GuidezarandijaNo ratings yet
- Quick Inst Alla Tion Guid E: Wl-EdhowaDocument155 pagesQuick Inst Alla Tion Guid E: Wl-EdhowaDomenicoNo ratings yet
- Checkpoint: Exam 156-215.80Document210 pagesCheckpoint: Exam 156-215.80awdNo ratings yet
- 9035051-02-Rev00 ExtremeWireless v10.21.03.0010 RelNotesDocument38 pages9035051-02-Rev00 ExtremeWireless v10.21.03.0010 RelNotesdoru.aero4738No ratings yet
- Easy Hotspot DocumentationDocument23 pagesEasy Hotspot DocumentationMelvin Asadon DalaNo ratings yet
- Day in The Life of A Packet: PAN-OS Packet Flow Sequence PAN-OS 6.1Document14 pagesDay in The Life of A Packet: PAN-OS Packet Flow Sequence PAN-OS 6.1Dede RizkiNo ratings yet
- Ezmaster Installation Guide - 1027Document18 pagesEzmaster Installation Guide - 1027hendraNo ratings yet
- Connect Mikrotik Routerboard 751u To Radiusdesk BasicDocument7 pagesConnect Mikrotik Routerboard 751u To Radiusdesk BasicOneRobNo ratings yet